Security News

Cybersecurity researchers are warning of suspected exploitation of a recently disclosed critical security flaw in the Apache ActiveMQ open-source message broker service that could result in remote...

Over three thousand internet-exposed Apache ActiveMQ servers are vulnerable to a recently disclosed critical remote code execution vulnerability. Apache ActiveMQ is a scalable open-source message broker that fosters communication between clients and servers, supporting Java and various cross-language clients and many protocols, including AMQP, MQTT, OpenWire, and STOMP. Thanks to the project's support for a diverse set of secure authentication and authorization mechanisms, it is widely used in enterprise environments where systems communicate without direct connectivity.

The U.S. Cybersecurity and Infrastructure Security Agency has added to its catalog of known exploited vulnerabilities a critical-severity issue tracked as CVE-2023-33246 that affects Apache's RocketMQ distributed messaging and streaming platform. CISA is warning federal agencies that they should patch the CVE-2023-33246 vulnerability for Apache RocketMQ installations on their systems by September 27.
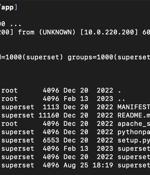
Patches have been released to address two new security vulnerabilities in Apache SuperSet that could be exploited by an attacker to gain remote code execution on affected systems. Outside of these weaknesses, the latest version of Superset also remediates a separate improper REST API permission issue that allows for low-privilege users to carry out server-side request forgery attacks.

Recently disclosed security flaws impacting Juniper firewalls, Openfire, and Apache RocketMQ servers have come under active exploitation in the wild, according to multiple reports. "This flaw allows an unauthorized user to exploit the unauthenticated Openfire Setup Environment within an established Openfire configuration," cloud security firm Aqua said.

Misconfigured and poorly secured Apache Tomcat servers are being targeted as part of a new campaign designed to deliver the Mirai botnet malware and cryptocurrency miners. The findings come...

Multiple security flaws have been disclosed in Apache OpenMeetings, a web conferencing solution, that could be potentially exploited by malicious actors to seize control of admin accounts and run malicious code on susceptible servers. "The acquired admin privileges can further be leveraged to exploit another vulnerability allowing attackers to execute arbitrary code on the Apache OpenMeetings server."

A financially motivated threat actor is actively scouring the internet for unprotected Apache NiFi instances to covertly install a cryptocurrency miner and facilitate lateral movement. "The attack script is not saved to the system. The attack scripts are kept in memory only."

If you're running an Apache NiFi instance exposed on the internet and you have not secured access to it, the underlying host may already be covertly cryptomining on someone else's behalf. "Routers make bad cryptomining servers. Cryptomining may be what they end up doing if the lateral movement doesn't get them anywhere."

The U.S. Cybersecurity and Infrastructure Security Agency has added three flaws to the Known Exploited Vulnerabilities catalog, based on evidence of active exploitation. The second flaw to be added to the KEV catalog is CVE-2021-45046, a remote code execution affecting the Apache Log4j2 logging library that came to light in December 2021.