Security News

In today's digital world, where connectivity is rules all, endpoints serve as the gateway to a business’s digital kingdom. And because of this, endpoints are one of hackers' favorite targets. ...
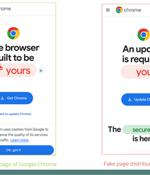
Fake browser updates are being used to push a previously undocumented Android malware called Brokewell. "Brokewell is a typical modern banking malware equipped with both data-stealing and...

Palo Alto Networks has shared remediation guidance for a recently disclosed critical security flaw impacting PAN-OS that has come under active exploitation. The vulnerability, tracked...

Healthcare service provider Kaiser Permanente disclosed a data security incident that may impact 13.4 million people in the United States. "Kaiser Permanente has determined that certain online technologies, previously installed on its websites and mobile applications, may have transmitted personal information to third-party vendors Google, Microsoft Bing, and X when members and patients accessed its websites or mobile applications" - Kaiser Permanente.

Your profile can be used to present content that appears more relevant based on your possible interests, such as by adapting the order in which content is shown to you, so that it is even easier for you to find content that matches your interests. Content presented to you on this service can be based on your content personalisation profiles, which can reflect your activity on this or other services, possible interests and personal aspects.

Threat actors are attempting to actively exploit a critical security flaw in the WP‑Automatic plugin for WordPress that could allow site takeovers. The shortcoming, tracked as CVE-2024-27956,...

Your profile can be used to present content that appears more relevant based on your possible interests, such as by adapting the order in which content is shown to you, so that it is even easier for you to find content that matches your interests. Content presented to you on this service can be based on your content personalisation profiles, which can reflect your activity on this or other services, possible interests and personal aspects.

These practices reveal a significant gap between recommended security practices and actual user behavior, highlighting how weak password habits and password reuse significantly heighten cybersecurity risks and identity theft. Despite 60% of users claiming they feel confident in identifying a phishing attack and 68% feeling prepared to identify and mitigate AI-enhanced cyberattacks, many respondents still resort to risky password management methods.

LSA Whisperer consists of open-source tools designed to interact with authentication packages through their unique messaging protocols. "Many authentication packages generally support their internal APIs, known as package calls, and relatively few are documented or used outside of Microsoft. I wanted to document as many of these calls as possible and implement a tool for interacting with them so we could identify which would provide value for red team assessments," Evan McBroom, Senior Software Engineer at SpecterOps, told Help Net Security.

Following the past few years of economic turbulence, merger and acquisition activity is on the rise in 2024, with several acquisition deals being announced in the first few months of the year valued at billions of dollars. With the surge of AI adoption, companies must not only reevaluate AI's role in identifying top prospects but also assess and resolve security risks that may lie hidden within their networks and the companies they are merging or acquiring.