Security News

Let's begin with a thought-provoking question: among a credit card number, a social security number, and an Electronic Health Record (EHR), which commands the highest price on a dark web forum? ...

Ransomware attacks have become a significant and pervasive threat in the ever-evolving realm of cybersecurity. Among the various iterations of ransomware, one trend that has gained prominence is...

Threat intelligence refers to gathering, processing, and analyzing cyber threats, along with proactive defensive measures aimed at strengthening security. It enables organizations to gain a...

Threat actors can take advantage of Amazon Web Services Security Token Service (AWS STS) as a way to infiltrate cloud accounts and conduct follow-on attacks. The service enables threat actors to...

Compromising the browser is a high-return target for adversaries. Browser extensions, which are small software modules that are added to the browser and can enhance browsing experiences, have...

A previously undocumented threat actor has been linked to a cyber attack targeting an aerospace organization in the U.S. as part of what's suspected to be a cyber espionage mission. The BlackBerry...

Enterprises' increasing digital reliance has fueled an array of cybersecurity threats. One rapidly growing area is information-stealing malware known as infostealers, which is malicious software designed to steal data.

The U.S. Department of Justice (DOJ) and the FBI recently collaborated in a multinational operation to dismantle the notorious Qakbot malware and botnet. While the operation was successful in...
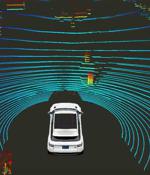
The Select Committee on the Chinese Communist Party, spearheaded by US representative and committee chairman Mike Gallagher, penned a letter to secretaries Gina Raimondo, Lloyd Austin, and Janet Yellen requesting an investigation of Chinese LiDAR manufacturers and the appropriateness of sanctions on those entities. "LiDAR is a critical technology used in autonomous systems and robotics but is currently not subject to US export controls or government procurement restrictions, which raises several concerns," reads the letter.

This article describes why threat actors target web apps and highlights the value of continuous monitoring in securing modern web apps. One of the key attractions of web apps from a hacker's perspective is how easy they are to target.