Security News

Microsoft sets multi-factor authentication as default for all Azure AD customers. In a new blog post, the company revealed that it's adding multi-factor authentication as the default security setting for existing Azure customers who haven't changed that setting on their own.

Microsoft has released a workaround for a zero-day flaw that was initially flagged in April and that attackers already have used to target organizations in Russia and Tibet, researchers said. The remote control execution flaw, tracked as CVE-2022-3019, is associated with the Microsoft Support Diagnostic Tool, which, ironically, itself collects information about bugs in the company's products and reports to Microsoft Support.

An advanced persistent threat actor aligned with Chinese state interests has been observed weaponizing the new zero-day flaw in Microsoft Office to achieve code execution on affected systems. "TA413 CN APT spotted exploiting the Follina zero-day using URLs to deliver ZIP archives which contain Word Documents that use the technique," enterprise security firm Proofpoint said in a tweet.

Microsoft has whipped out the rebranding team once more, and chosen the name "Entra" as a catch-all for the company's identity and access capabilities. Sadly nothing to do with the sometimes-missed Encarta, the encyclopaedia launched by Microsoft back in the 1990s and eventually killed off in the first decade of the twenty-first century, Entra is not so much about squinting at postage stamp-sized bits of video and more about Azure Active Directory and Cloud Infrastructure Entitlement Management.

Microsoft on Monday published guidance for a newly discovered zero-day security flaw in its Office productivity suite that could be exploited to achieve code execution on affected systems. Microsoft Office versions Office 2013, Office 2016, Office 2019, and Office 2021, as well as Professional Plus editions, are impacted.

Microsoft has shared mitigation measures to block attacks exploiting a newly discovered Microsoft Office zero-day flaw abused in the wild to execute malicious code remotely. The bug is a Microsoft Windows Support Diagnostic Tool remote code execution vulnerability reported by crazyman of the Shadow Chaser Group.

Infosec researchers have idenitied a zero-day code execution vulnerability in Microsoft's ubiquitous Office software. Dubbed "Follina", the vulnerability has been floating around for a while and uses Office functionality to retrieve a HTML file which in turn makes use of the Microsoft Support Diagnostic Tool to run some code.

A zero-day vulnerability in Microsoft Office allows adversaries to run malicious code on targeted systems via a flaw a remote Word template feature. Noted security researcher Kevin Beaumont dubbed the vulnerability "Follina", explaining the zero day code references the Italy-based area code of Follina - 0438.Beaumont said the flaw is abusing the remote template feature in Microsoft Word and is not dependent on a typical macro-based exploit path, common within Office-based attacks.

Security researchers have discovered a new Microsoft Office zero-day vulnerability that is being used in attacks to execute malicious PowerShell commands via Microsoft Diagnostic Tool simply by opening a Word document.The vulnerability, which has yet to receive a tracking number and is referred to by the infosec community as 'Follina,' is leveraged using malicious Word documents that execute PowerShell commands via the MSDT. This new Follina zero-day opens the door to a new critical attack vector leveraging Microsoft Office programs as it works without elevated privileges, bypasses Windows Defender detection, and does not need macro code to be enabled to execute binaries or scripts.
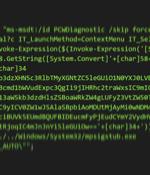
Cybersecurity researchers are calling attention to a zero-day flaw in Microsoft Office that could be abused to achieve arbitrary code execution on affected Windows systems. According to security researcher Kevin Beaumont, who dubbed the flaw "Follina," the maldoc leverages Word's remote template feature to fetch an HTML file from a server, which then makes use of the "Ms-msdt://" URI scheme to run the malicious payload. MSDT is short for Microsoft Support Diagnostics Tool, a utility that's used to troubleshoot and collect diagnostic data for analysis by support professionals to resolve a problem.