Security News

The email your manager received and forwarded to you was something completely innocent, such as a potential customer asking a few questions. The innocent pretext disappeared and the real phishing email became visible.

The North Korea-linked threat actor known as Kimsuky (aka Black Banshee, Emerald Sleet, or Springtail) has been observed shifting its tactics, leveraging Compiled HTML Help (CHM) files as vectors...

Cybersecurity researchers have discovered a new malware campaign that leverages bogus Google Sites pages and HTML smuggling to distribute a commercial malware called AZORult in order to facilitate...

Valve has reportedly fixed an HTML injection flaw in Counter-Strike 2 that was heavily abused today to inject images into games and obtain other players' IP addresses. While initially thought to be a more severe Cross Site Scripting flaw, which allows JavaScript code to be executed in a client, the bug was determined only to be an HTML injection flaw, allowing the injection of images.

Google is notifying Gmail users that the webmail's Basic HTML view will be deprecated in January 2024, and users will require modern browsers to continue using the service. The basic HTML view is a stripped-down version of Gmail that does not offer users chat, spell checking, keyboard shortcuts, adding or importing contacts, setting custom "From" addresses, or using rich text formatting.

A Chinese nation-state group has been observed targeting Foreign Affairs ministries and embassies in Europe using HTML smuggling techniques to deliver the PlugX remote access trojan on compromised systems. "The campaign uses new delivery methods to deploy a new variant of PlugX, an implant commonly associated with a wide variety of Chinese threat actors," Check Point said.

Dll attachments as the main focus when cyberattacks arise, but there may be another type of highly used malicious file to be aware of. According to findings from IT security company Barracuda Networks, HTML attachments are being employed by adversaries the most when it comes to cyberattacks and 21% of all HTML attachments scanned by the company were found to be malicious.

HTML files remain one of the most popular attachments used in phishing attacks for the first four months of 2022, showing that the technique remains effective against antispam engines and works well on the victims themselves. The phishing forms, redirection mechanisms, and data-stealing elements in HTML attachments are typically implemented using various methods, ranging from simple redirects to obfuscating JavaScript to hide phishing forms.
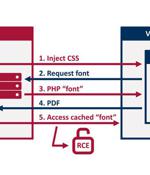
Researchers have disclosed an unpatched security vulnerability in "Dompdf," a PHP-based HTML to PDF converter, that, if successfully exploited, could lead to remote code execution in certain configurations. In other words, the flaw allows a malicious party to upload font files with a.php extension to the web server, which can then be activated by using an XSS vulnerability to inject HTML into a web page before it's rendered as a PDF. This meant that the attacker could potentially navigate to the uploaded.

Threat actors are increasingly banking on the technique of HTML smuggling in phishing campaigns as a means to gain initial access and deploy an array of threats, including banking malware, remote administration trojans, and ransomware payloads. HTML smuggling is an approach that allows an attacker to "Smuggle" first-stage droppers, often encoded malicious scripts embedded within specially-crafted HTML attachment or web pages, on a victim machine by taking advantage of basic features in HTML5 and JavaScript rather than exploiting a vulnerability or a design flaw in modern web browsers.