Security News
Networking equipment company Netgear has released yet another round of patches to remediate a high-severity remote code execution vulnerability affecting multiple routers that could be exploited by remote attackers to take control of an affected system. Because of its ubiquitous nature, UPnP is used by a wide variety of devices, including personal computers, networking equipment, video game consoles and internet of things devices.

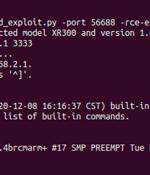
Newly surfaced malware that is difficult to detect and written in Google's open-source programming language has the potential to exploit millions of routers and IoT devices, researchers have found. This feature may be the reason why it's caught on with malware developers in the last few years, since it also makes it easier for attackers to spread malware on multiple operating systems, Caspi wrote.

As of Monday night, Facebook had crawled back from what may have been its longest blackout ever and apologized for the mass outage that left billions of users locked out of Facebook, Instagram, WhatsApp, Messenger and Oculus VR for about six hours. When it comes to gauging Facebook's worst blackout ever, accounts vary: CNBC reported that Monday's outage was the longest downtime that Facebook has experienced since 2008, when a bug knocked its site offline for about a day, affecting some 80 million users.

Networking equipment company Netgear has released patches to remediate a high-severity remote code execution vulnerability affecting multiple routers that could be exploited by remote attackers to take control of an affected system. Traced as CVE-2021-40847, the security weakness impacts the following models -.

Netgear has fixed a high severity remote code execution vulnerability found in the Circle parental control service, which runs with root permissions on almost a dozen modern Small Offices/Home Offices Netgear routers. While one would expect the attack vector exposed by Circle security flaw would be removed after the service is stopped, the Circle update daemon containing the bug is enabled by default and it can be exploited even if the service is disabled.

Latvian network equipment manufacturer MikroTik has shared details on customers can secure and clean routers enslaved by the massive Mēris DDoS botnet over the summer. "As far as we have seen, these attacks use the same routers that were compromised in 2018, when MikroTik RouterOS had a vulnerability, that was quickly patched," a MicroTik spokesperson told BleepingComputer.

A denial-of-service vulnerability affecting SDKs for Realtek chipsets used in 65 vendors' IoT devices has been incorporated into a son-of-Mirai botnet, according to new research. Warning that the vuln had been included in Dark.IoT's botnet "Less than a week" after it was publicly disclosed, Radware said: "This vulnerability was recently disclosed by IoT Inspectors Research Lab on August 16th and impacts IoT devices manufactured by 65 vendors relying on the Realtek chipsets and SDK.".

A critical vulnerability in Cisco Small Business Routers will not be patched by the networking equipment giant, since the devices reached end-of-life in 2019. "The Cisco Small Business RV110W, RV130, RV130W, and RV215W Routers have entered the end-of-life process. Customers are encouraged to migrate to the Cisco Small Business RV132W, RV160, or RV160W Routers."

A critical security vulnerability in Cisco Small Business Routers allows remote code execution and denial of service. The bug is one of six addressed by Cisco this week; it also issued an advisory for the critical BlackBerry QNX-2021-001 vulnerability unveiled earlier this week, which affects multiple vendors, well beyond Cisco.

In a security advisory published on Wednesday, Cisco said that a critical vulnerability in Universal Plug-and-Play service of multiple small business VPN routers will not be patched because the devices have reached end-of-life. "The Cisco Small Business RV110W, RV130, RV130W, and RV215W Routers have entered the end-of-life process."