Security News > 2021 > November > Critical Root RCE Bug Affects Multiple Netgear SOHO Router Models
Networking equipment company Netgear has released yet another round of patches to remediate a high-severity remote code execution vulnerability affecting multiple routers that could be exploited by remote attackers to take control of an affected system.
Because of its ubiquitous nature, UPnP is used by a wide variety of devices, including personal computers, networking equipment, video game consoles and internet of things devices.
Specifically, the vulnerability stems from the fact that the UPnP daemon accepts unauthenticated HTTP SUBSCRIBE and UNSUBSCRIBE requests - which are event notification alerts that devices use to receive notifications from other devices when certain configuration changes, such as media sharing, happen.
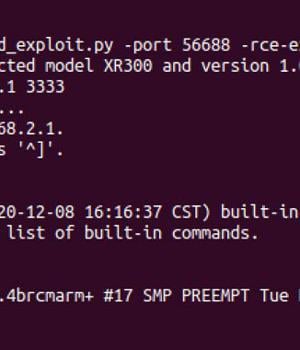
According to GRIMM security researcher Adam Nichols, there exists a memory stack overflow bug in the code that handles the UNSUBSCRIBE requests, which enables an adversary to send a specially crafted HTTP request and run malicious code on the affected device, including resetting the administrator password and delivering arbitrary payloads.
"Since the UPnP daemon runs as root, the highest privileged user in Linux environments, the code executed on behalf of the attacker will be run as root as well," Nichols said.
"With root access on a device, an attacker can read and modify all traffic that is passed through the device."
News URL
https://thehackernews.com/2021/11/critical-root-rce-bug-affects-multiple.html
Related news
- Critical RCE bug in 92,000 D-Link NAS devices now exploited in attacks (source)
- HPE Aruba Networking fixes four critical RCE flaws in ArubaOS (source)
- Four Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks (source)
- Over 50,000 Tinyproxy servers vulnerable to critical RCE flaw (source)
- PoC exploit released for RCE zero-day in D-Link EXO AX4800 routers (source)
- Critical Git vulnerability allows RCE when cloning repositories with submodules (CVE-2024-32002) (source)