Security News

Highly targeted phishing campaigns against specific individuals or types of individuals are known as spear phishing. While phishing is generalized in that one phishing email may be sent to millions of people, spear phishing is highly targeted.
Cybersecurity researchers are calling attention to the "democratization" of the phishing ecosystem owing to the emergence of Telegram as an epicenter for cybercrime, enabling threat actors to...

New phishing attacks abuse Microsoft Teams group chat requests to push malicious attachments that install DarkGate malware payloads on victims' systems. The attackers used what looks like a compromised Teams user to send over 1,000 malicious Teams group chat invites, according to AT&T Cybersecurity research.

A widespread Facebook phishing campaign stating, "I can't believe he is gone. I'm gonna miss him so much," leads unsuspecting users to a website that steals your Facebook credentials. The phishing campaign started around a year ago, with Facebook having trouble blocking the posts as they continue to this day.

The threat actor tracked as TA866 has resurfaced after a nine-month hiatus with a new large-volume phishing campaign to deliver known malware families such as WasabiSeed and Screenshotter. The...

The Russia-linked threat actor known as COLDRIVER has been observed evolving its tradecraft to go beyond credential harvesting to deliver its first-ever custom malware written in the Rust...

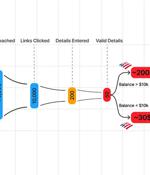
In a seizure warrant application, the U.S. Secret Service sheds light on how threat actors stole $34,000 using fake antivirus renewal subscription emails. The now-executed seizure warrant was submitted by Special Agent Jollif of the United States Secret Service to recover funds stolen in a fake Norton subscription renewal email that led to the threat actor gaining access to a victim's PC and bank account.

This shift in phishing philosophies has also led to a precipitous decline in the use of malicious payloads in phishing emails - presumably to avoid detection from the more capable email security solutions of today. It appears this inherent constraint on scale is now a thing of the past, with the emergence of generative AI effectively flipping the funnel on phishing speed and scale.

The threat actor known as UAC-0050 is leveraging phishing attacks to distribute Remcos RAT using new strategies to evade detection from security software. "The group's weapon of choice is Remcos...

The threat actor referred to as Cloud Atlas has been linked to a set of spear-phishing attacks on Russian enterprises. Targets included a Russian agro-industrial enterprise and a state-owned...