Security News

A US court has rejected spyware vendor NSO Group's motion to dismiss a lawsuit filed by Apple that alleges the developer violated computer fraud and other laws by infecting customers' iDevices with its surveillance software. Apple sued NSO, developer of the notorious Pegasus spyware, back in November 2021 and asked the court to permanently ban NSO from using any Apple software, services, or devices.

Cybercrime gangs like the notorious Lazarus group and spyware vendors like Israel's NSO should be considered cyber mercenaries - and become the subject of a concerted international response - according to a Monday report from Delhi-based think tank Observer Research Foundation. Author Fitri Bintang Timur argued the term mercenary applies because, as amendments to the Geneva Convention put it, mercenaries are "An entity having the motivation to gain financial or material compensation in return for their willingness to fight for the recruiter's country."

The iPhone belonging to Galina Timchenko, a prominent Russian journalist and critic of the government, was compromised with NSO Group's Pegasus spyware, a new collaborative investigation from Access Now and the Citizen Lab has revealed. The Washington Post reported that the Russian government is not a client of NSO Group, citing an unnamed person familiar with the company's operations.

Spyware maker NSO Group has a new ringleader, as the notorious biz seeks to revamp its image amid new reports that the company's Pegasus malware is targeting yet more human rights advocates and journalists. The new owner is a Luxembourg-based holding firm called Dufresne Holdings controlled by NSO co-founder Omri Lavie, according to the report.
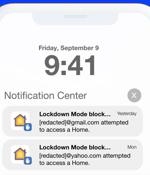
Israeli spyware maker NSO Group deployed at least three novel "Zero-click" exploits against iPhones in 2022 to infiltrate defenses erected by Apple and deploy Pegasus, according to the latest findings from Citizen Lab. "NSO Group customers widely deployed at least three iOS 15 and iOS 16 zero-click exploit chains against civil society targets around the world," the interdisciplinary laboratory based at the University of Toronto said.

Pegasus spyware-maker NSO Group announced on Sunday it will reorganize, replacing its CEO and letting go of around 100 workers. A statement from NSO Group reportedly said the reorg, which reduces the size of the company by around 15 percent, "Will examine all aspects of its business, including streamlining its operations to ensure NSO remains one of the world's leading hi-tech cyber intelligence companies, focusing on NATO-member countries."

We forensically confirmed that at least 30 individuals were infected with NSO Group's Pegasus spyware. A sample of the victims was independently analyzed by Amnesty International's Security Lab which confirms the methodology used to determine Pegasus infections.

US security technology provider L3Harris has courted controversial Israeli spyware firm NSO with an aim to buy it, according to reports. The New York Times claims L3Harris in recent months sent a team to Israel to try to smooth passage of the deal, which was made challenging by US president Joe Biden's decision to blacklist NSO following the use of its Pegasus software to crack phones of politicians and campaigners.

The beleaguered Israeli surveillanceware vendor NSO Group this week admitted to the European Union lawmakers that its Pegasus tool was used by at least five countries in the region. The disclosure comes as a special inquiry committee was launched in April 2022 to investigate alleged breaches of E.U. law following revelations that the company's Pegasus spyware is being used to snoop on phones belonging to politicians, diplomats, and civil society members.

NSO Group told European lawmakers this week that "Under 50" customers use its notorious Pegasus spyware, though these customers include "More than five" European Union member states. Generally speaking, a target selected by an NSO customer has their phone or other device infected with hidden spyware via the exploitation of one or more security vulnerabilities.