Security News

Your profile can be used to present content that appears more relevant based on your possible interests, such as by adapting the order in which content is shown to you, so that it is even easier for you to find content that matches your interests. Content presented to you on this service can be based on your content personalisation profiles, which can reflect your activity on this or other services, possible interests and personal aspects.

Last year was challenging for the global market, and the market downturn greatly affected even the historically resilient cybersecurity ecosystem. In this Help Net Security video, Merav Ben Avi, Content Manager at YL Ventures, talks about how the Israeli cybersecurity industry, much like the global one, skyrocketed in 2021 with record-breaking capital and an exceptional number of new startups and unicorns.

Israeli higher education and tech sectors have been targeted as part of a series of destructive cyber attacks that commenced in January 2023 with an aim to deploy previously undocumented wiper malware. "The attacks are characterized by attempts to steal sensitive data, such as personally identifiable information and intellectual property," Palo Alto Networks Unit 42 said in a new report shared with The Hacker News.

Attackers have started using new wiper malware called BiBi-Linux to attack Israeli companies and destroy their data. The Security Joes Incident Response team found the malware during a forensics investigation of a breach within an Israeli company.

A new malware wiper known as BiBi-Linux is being used to destroy data in attacks targeting Linux systems belonging to Israeli companies. The wiper sample discovered by Security Joes also features no obfuscation, packing, or other protective measures, making malware analysts' jobs much easier.

A pro-Hamas hacktivist group has been observed using a new Linux-based wiper malware dubbed BiBi-Linux Wiper, targeting Israeli entities amidst the ongoing Israeli-Hamas war. "This malware is an...

A Gaza-based threat actor has been linked to a series of cyber attacks aimed at Israeli private-sector energy, defense, and telecommunications organizations. Microsoft, which revealed details of...
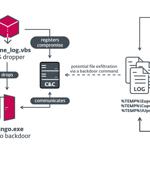
Israeli organizations were targeted as part of two different campaigns orchestrated by the Iranian nation-state actor known as OilRig in 2021 and 2022. The campaigns, dubbed Outer Space and Juicy...
Israeli software maker Insanet has reportedly developed a commercial product called Sherlock that can infect devices via online adverts to snoop on targets and collect data about them for the biz's clients. "Insanet is an Israeli company, which operates with full and absolute obligation to Israeli law and to its strict regulatory directives," the biz reportedly told the newspaper.

The Iranian threat actor known as Agrius is leveraging a new ransomware strain called Moneybird in its attacks targeting Israeli organizations. Agrius, also known as Pink Sandstorm, has a track record of staging destructive data-wiping attacks aimed at Israel under the guise of ransomware infections.