Security News

Google's Chrome 115 has a new feature that allows users to use Windows Mica material, a design element that enhances user personalization. Mica is a distinctive design feature that doesn't just stay opaque but fuses with the user's desktop theme and wallpaper.

Non-executable files containing malware were rarely shared, and could easily and automatically be identified if you tried to share one by mistake because they lacked the tell-tale starting bytes of a typical program file. Firstly, numerous malware families sneakily store at least some of their own needed data as added information in the personal part of such files, so that trying to bowdlerise, redact or rewrite the sensitive, "Unsharable" parts of the file causes the malware to stop working, or to behave differently.

Cybersecurity researchers have uncovered a privilege escalation vulnerability in Google Cloud that could enable malicious actors tamper with application images and infect users, leading to supply chain attacks. The issue, dubbed Bad.Build, is rooted in the Google Cloud Build service, according to cloud security firm Orca, which discovered and reported the issue.

A critical design flaw in the Google Cloud Build service discovered by cloud security firm Orca Security can let attackers escalate privileges, providing them with almost nearly-full and unauthorized access to Google Artifact Registry code repositories. Dubbed Bad.Build, this flaw could enable the threat actors to impersonate the service account for the Google Cloud Build managed continuous integration and delivery service to run API calls against the artifact registry and take control over application images.

A criminal crew with a history of deploying malware to harvest credentials from Amazon Web Services accounts may expand its attention to organizations using Microsoft Azure and Google Cloud Platform. The crooks used to target primarily AWS users, and now seem to be looking for ways into Azure and Google Cloud accounts.

Review your recent Gmail access, browser sign-in history and Google account activity to make sure no one other than you has used your account. SEE: Discover how to regain access to your Google account.
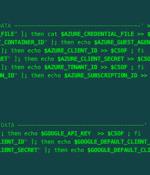
A malicious actor has been linked to a cloud credential stealing campaign in June 2023 that's focused on Azure and Google Cloud Platform services, marking the adversary's expansion in targeting beyond Amazon Web Services. They also overlap with an ongoing TeamTNT campaign disclosed by Aqua called Silentbob that leverages misconfigured cloud services to drop malware as part of what's said to be a testing effort, while also linking SCARLETEEL attacks to the threat actor, citing infrastructure commonalities.

Google is fighting back against the constant invasion of malware on Google Play by requiring all new developer accounts registering as an organization to provide a valid D-U-N-S number before submitting apps. Typically, malicious apps on Google Play are submitted for review without dangerous code or payloads, which are then fetched later via an update in the post-installation phase.

Find out how Google Cloud approaches AI data, what privacy measures your business should keep in mind when it comes to generative AI and how to make a machine learning application "Unlearn" someone's data. Google Cloud approaches using personal data in AI products by covering such data under the existing Google Cloud Platform Agreement.

Research and development: Google uses information to improve our services and to develop new products, features and technologies that benefit our users and the public. We use publicly available information to help train Google's AI models and build products and features like Google Translate, Bard, and Cloud AI capabilities.