Security News

No attacks possible, but enough issues to cause concern Messaging giant WeChat uses a network protocol that the app's developers modified – and by doing so introduced security weaknesses,...

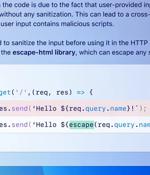
CISA and the FBI urged tech companies to review their software and eliminate cross-site scripting (XSS) vulnerabilities before shipping. [...]

CISA and the FBI urged software companies on Wednesday to review their products and eliminate path OS command injection vulnerabilities before shipping. "OS command injection vulnerabilities arise when manufacturers fail to properly validate and sanitize user input when constructing commands to execute on the underlying OS," today's joint advisory explains.

Red Shield VPN, which is focused on providing its services to Russian users, claims it received a note from Apple that says its VPN was removed from the Russian App Store. The email, which the VPN operator shared on X, says Cupertino had to remove the app from the App Store in Russia since the software did not "Conform with all local laws." This is after the Kremlin had apparently spent years trying technological approaches to block the use of the VPN. "Apple's actions, motivated by a desire to retain revenue from the Russian market, actively support an authoritarian regime," Red Shield said in a statement.

CISA and the FBI urged software companies today to review their products and eliminate path traversal security vulnerabilities before shipping. Attackers can exploit path traversal vulnerabilities to create or overwrite critical files used to execute code or bypass security mechanisms like authentication.

Your profile can be used to present content that appears more relevant based on your possible interests, such as by adapting the order in which content is shown to you, so that it is even easier for you to find content that matches your interests. Content presented to you on this service can be based on your content personalisation profiles, which can reflect your activity on this or other services, possible interests and personal aspects.

AI hallucinates software packages and devs download them – even if potentially poisoned with malware
According to Bar Lanyado, security researcher at Lasso Security, one of the businesses fooled by AI into incorporating the package is Alibaba, which at the time of writing still includes a pip command to download the Python package huggingface-cli in its GraphTranslator installation instructions. Lanyado did so to explore whether these kinds of hallucinated software packages - package names invented by generative AI models, presumably during project development - persist over time and to test whether invented package names could be co-opted and used to distribute malicious code by writing actual packages that use the names of code dreamed up by AIs.

CISA and the FBI urged executives of technology manufacturing companies to prompt formal reviews of their organizations' software and implement mitigations to eliminate SQL injection security vulnerabilities before shipping.In SQL injection attacks, threat actors "Inject" maliciously crafted SQL queries into input fields or parameters used in database queries, exploiting vulnerabilities in the application's security to execute unintended SQL commands, such as exfiltrating, manipulating, or deleting sensitive data stored in the database.
GitHub on Wednesday announced that it's making available a feature called code scanning autofix in public beta for all Advanced Security customers to provide targeted recommendations in an effort...

The White House Office of the National Cyber Director urged tech companies today to switch to memory-safe programming languages, such as Rust, to improve software security by reducing the number of memory safety vulnerabilities. Such vulnerabilities are coding errors or weaknesses within software that can lead to memory management issues when memory can be accessed, written, allocated, or deallocated.