Security News

RMM software developer TeamViewer says a Russian state-sponsored hacking group known as Midnight Blizzard is believed to be behind a breach of their corporate network this week. TeamViewer says they believe their internal corporate network, not their production environment, was breached on Wednesday, June 26, using an employee's credentials.

The U.S. indicted Russian national Amin Timovich Stigal for his alleged role in cyberattacks targeting Ukrainian government computer networks in an operation from the Russian foreign military intelligence agency prior to invading the country. The announcement from the Department of Justice says that in January 2022 Stigal and members of the GRU used a U.S.-based company to distribute the WhisperGate pseudo-ransomware to systems at dozens of Ukrainian government entities to destroy data.

A 22-year-old Russian national has been indicted in the U.S. for his alleged role in staging destructive cyber attacks against Ukraine and its allies in the days leading to Russia's full-blown...

Russian organizations have been targeted by a cybercrime gang called ExCobalt using a previously unknown Golang-based backdoor known as GoRed. "ExCobalt focuses on cyber espionage and includes...

The Treasury Department's Office of Foreign Assets Control has sanctioned twelve Kaspersky Lab executives for operating in the technology sector of Russia. These sanctions came after the Biden administration announced yesterday the ban of sales and software updates for Kaspersky antivirus software in the USA, which started in July, over potential cybersecurity risks to national security.

State-sponsored actors with ties to Russia have been linked to targeted cyber attacks aimed at French diplomatic entities, the country's information security agency ANSSI said in an advisory. The...

Your profile can be used to present content that appears more relevant based on your possible interests, such as by adapting the order in which content is shown to you, so that it is even easier for you to find content that matches your interests. Content presented to you on this service can be based on your content personalisation profiles, which can reflect your activity on this or other services, possible interests and personal aspects.
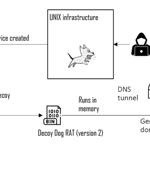
Russian organizations are at the receiving end of cyber attacks that have been found to deliver a Windows version of a malware called Decoy Dog. Cybersecurity company Positive Technologies is...

The Russian GRU-backed threat actor APT28 has been attributed as behind a series of campaigns targeting networks across Europe with the HeadLace malware and credential-harvesting web pages. APT28,...

A 31-year-old Russian national named Evgeniy Doroshenko has been indicted for wire and computer fraud in the United States for allegedly acting as an "Initial access broker" from February 2019 to May 2024. An initial access broker is a threat actor who breaches corporate networks and then sells that access to other threat actors, who commonly use the access to conduct data theft or ransomware attacks.