Security News

A North Korea-linked threat actor known for its cyber espionage operations has gradually expanded into financially-motivated attacks that involve the deployment of ransomware, setting it apart from other nation-state hacking groups linked to the country. "APT45 is a long-running, moderately sophisticated North Korean cyber operator that has carried out espionage campaigns as early as 2009," researchers Taylor Long, Jeff Johnson, Alice Revelli, Fred Plan, and Michael Barnhart said.

A likely China-linked state-sponsored threat actor has been linked to a cyber espionage campaign targeting government, academic, technology, and diplomatic organizations in Taiwan between November...

Cyber espionage groups associated with China have been linked to a long-running campaign that has infiltrated several telecom operators located in a single Asian country at least since 2021. "The...

Chinese state-sponsored actors have been targeting a government agency since at least March 2023 in a cyberespionage campaign that researchers track as Crimson Palace. According to a report from cybersecurity company Sophos, the campaign relied on new malware variants and three different activity clusters that indicate a coordinated attack.
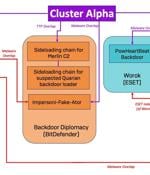
An unnamed high-profile government organization in Southeast Asia emerged as the target of a "complex, long-running" Chinese state-sponsored cyber espionage operation codenamed Crimson Palace....

Your profile can be used to present content that appears more relevant based on your possible interests, such as by adapting the order in which content is shown to you, so that it is even easier for you to find content that matches your interests. Content presented to you on this service can be based on your content personalisation profiles, which can reflect your activity on this or other services, possible interests and personal aspects.

A previously undocumented cyber espionage-focused threat actor named LilacSquid has been linked to targeted attacks spanning various sectors in the United States (U.S.), Europe, and Asia as part...

Microsoft has published a "Cyber Signals" report sharing new information about the hacking group Storm-0539 and a sharp rise in gift card theft as we approach the Memorial Day holiday in the United States. The FBI previously warned about Storm-0539's activities earlier this month, highlighting the threat group's advanced techniques in conducting gift card theft and fraud, stating that their tactics resemble state-sponsored hackers and sophisticated cyberespionage actors.

Microsoft has revealed that North Korea-linked state-sponsored cyber actors has begun to use artificial intelligence (AI) to make its operations more effective and efficient. "They are learning to...

Two China-linked advanced persistent threat (APT) groups have been observed targeting entities and member countries affiliated with the Association of Southeast Asian Nations (ASEAN) as part of a...