Security News

Multiple zero-day vulnerabilities named 'BitForge' in the implementation of widely used cryptographic protocols like GG-18, GG-20, and Lindell 17 affected popular cryptocurrency wallet providers, including Coinbase, ZenGo, Binance, and many more. Today, the analysts publicly disclosed BitForge in the "Small Leaks, Billions Of Dollars: Practical Cryptographic Exploits That Undermine Leading Crypto Wallets" BlackHat presentation, by which time Coinbase and ZenGo have applied fixes to address the problem.

Sophos released new findings on CryptoRom scams—a subset of pig butchering schemes designed to trick users of dating apps into making fake cryptocurrency investments. Since May, Sophos X-Ops has...

Blockchain analysts blame the North Korean Lazarus hacking group for a recent attack on payment processing platform Alphapo where the attackers stole almost $60 million in crypto. [...]
A new malware family called Realst has become the latest to target Apple macOS systems, with a third of the samples already designed to infect macOS 14 Sonoma, the upcoming major release of the operating system. Written in the Rust programming language, the malware is distributed in the form of bogus blockchain games and is capable of "Emptying crypto wallets and stealing stored password and browser data" from both Windows and macOS machines.

A new Mac malware named "Realst" is being used in a massive campaign targeting Apple computers, with some of its latest variants including support for macOS 14 Sonoma, which is still in development. In reality, the game installers infect devices with information-stealing malware, such as RedLine Stealer on Windows and Realst on macOS. This type of malware will steal data from the victim's web browsers and cryptocurrency wallet apps and send them back to the threat actors.

A new Mac malware named "Realst" is being used in a massive campaign targeting Apple computers, with some of its latest variants including support for macOS 14 Sonoma, which is still in development. The malware, first discovered by security researcher iamdeadlyz, is distributed to both Windows and macOS users in the form of fake blockchain games using names such as Brawl Earth, WildWorld, Dawnland, Destruction, Evolion, Pearl, Olymp of Reptiles, and SaintLegend.

Hive is widely believed to be affiliated with the Conti ransomware group, joining a list of other groups associated with former Conti operators, including Royal, Black Basta, and Quantum. Hive, like other RaaS providers, wrote a ransomware encryptor, created a dark web domain, advertised their services to affiliates and forums, and then allowed users to purchase a license to configure a ransomware payload and receive extortion funds.

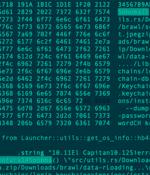
A new fileless attack dubbed PyLoose has been observed striking cloud workloads with the goal of delivering a cryptocurrency miner, new findings from Wiz reveal. "The attack consists of Python code that loads an XMRig Miner directly into memory using memfd, a known Linux fileless technique," security researchers Avigayil Mechtinger, Oren Ofer, and Itamar Gilad said.

An unknown cryptocurrency exchange located in Japan was the target of a new attack earlier this month to deploy an Apple macOS backdoor called JokerSpy. Elastic Security Labs, which is monitoring the intrusion set under the name REF9134, said the attack led to the installation of Swiftbelt, a Swift-based enumeration tool inspired by an open-source utility called SeatBelt.

Internet-facing Linux systems and Internet of Things devices are being targeted as part of a new campaign designed to illicitly mine cryptocurrency. "The threat actors behind the attack use a backdoor that deploys a wide array of tools and components such as rootkits and an IRC bot to steal device resources for mining operations," Microsoft threat intelligence researcher Rotem Sde-Or said.