Security News > 2023 > October

Misconception #1: GitHub Actions security only means using SCA, SAST tools in CI/CD. When people think about GitHub Actions security, their first thought is about adding security tools, like SCA and SAST tools, in the CI/CD pipeline. GitHub Actions security also extends to securing the CI/CD servers on which GitHub Actions run.

FraudGPT is the evil counterpart to ChatGPT. Criminals use it to target businesses with phishing emails and scams with speed and accuracy like never before. The AI can be prompted to create the most realistic phishing emails, perfected down to a business' tone and artistic style, and encourage victims to hand over sensitive information, such as bank information or corporate login details.

Cybercriminals launched approximately 7.9 million DDoS attacks in 1H 2023, representing a 31% year-over-year increase, according to NETSCOUT. Global events like the Russia-Ukraine war and NATO bids have driven recent DDoS attack growth. In 2023, Sweden experienced a similar onslaught around its NATO bid, culminating with a 500 Gbps DDoS attack in May. Overall, ideologically motivated DDoS attacks have targeted the United States, Ukraine, Finland, Sweden, Russia, and multiple other countries.

Online fraud is a pervasive and constantly evolving threat that affects individuals and organizations worldwide. In this Help Net Security round-up, cybersecurity experts talk about online fraud and damaging effects it has on individuals and organizations.

Ciphertex strengthens data security with SecureNAS CX-160KSSD-X. The SecureNAS CX-160KSSD-X storage unit is powered by an Intel Xeon D processor and supports up to sixteen hot-swappable 2.5″ SSDs and two internal 2.5″ SSDs and can store up to 490TB, while improving security and endurance. Librem 11 tablet sets new standard for privacy and security with Linux-based PureOS. Purism introduced the new Librem 11 tablet running secure PureBoot and Linux kernel-based PureOS. Librem 11 is made for individuals, organizations, government agencies, law enforcement agencies, and businesses that need security and privacy with powerful portability.
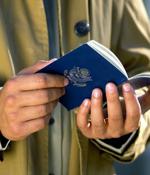
Last week the internet was abuzz with talk that Singapore's commercial Changi airport was no longer going to require passports for clearance at immigration. The news came through as Singapore passed its Immigration Amendment Bill which, among other things, enables the use of end-to-end biometric clearance at airports and checkpoints, beginning in the first half of 2024.

Infosec in brief Progress Software, maker of the mass-exploited MOVEit document transfer tool, is back in the news with more must-apply security patches, this time for another file-handling product: WS FTP. We're told this software's ad hoc transfer module and WS FTP's server management interface were found to have eight vulnerabilities, with CVSS severity scores ranging from 5.3 all the way to 10 out of 10. At their most severe, all versions of WS FTP Server prior to 8.7.4 and 8.8.2 are vulnerable to a.NET deserialization attack from a pre-authenticated attacker.

Amazon mistakenly sent out purchase confirmation emails for Hotels.com, Google Play, and Mastercard gift cards to customers, making many worried their accounts were compromised. The emails were sent out last night, with customers reporting receiving three separate emails from Amazon Prime for each alleged gift card purchase.

The LostTrust ransomware operation is believed to be a rebrand of MetaEncryptor, utilizing almost identical data leak sites and encryptors. MetaEncryptor is a ransomware operation that is believed to have launched in August 2022, amassing twelve victims on their data leak site through July 2023, after which no new victims were added to the site.

Using standard hardware, the researchers demonstrated that executing the Marvin Attack within just a couple of hours is possible, proving its practicality. The Marvin Attack does not have a corresponding CVE despite highlighting a fundamental flaw in RSA decryption, mainly how padding errors are managed, due to the variety and complexity of individual implementations.