Security News > 2022 > December > Ransomware Hackers Using New Way to Bypass MS Exchange ProxyNotShell Mitigations
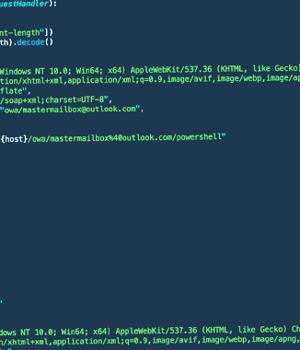
Threat actors affiliated with a ransomware strain known as Play are leveraging a never-before-seen exploit chain that bypasses blocking rules for ProxyNotShell flaws in Microsoft Exchange Server to achieve remote code execution through Outlook Web Access.
"The new exploit method bypasses URL rewrite mitigations for the Autodiscover endpoint," CrowdStrike researchers Brian Pitchford, Erik Iker, and Nicolas Zilio said in a technical write-up published Tuesday.
Play ransomware, which first surfaced in June 2022, has been revealed to adopt many tactics employed by other ransomware families such as Hive and Nokoyawa, the latter of which upgraded to Rust in September 2022.
The cybersecurity company's investigations into several Play ransomware intrusions found that initial access to the target environments was not achieved by directly exploiting CVE-2022-41040, but rather through the OWA endpoint.
CrowdStrike further noted that a proof-of-concept Python script discovered and leaked by Huntress Labs researcher Dray Agha last week may have been put to use by the Play ransomware actors for initial access.
"Organizations should apply the November 8, 2022 patches for Exchange to prevent exploitation since the URL rewrite mitigations for ProxyNotShell are not effective against this exploit method," the researchers said.
News URL
https://thehackernews.com/2022/12/ransomware-hackers-using-new-way-to.html
Related news
- Update VMware Tools for Windows Now: High-Severity Flaw Lets Hackers Bypass Authentication (source)
- Hackers exploit WordPress plugin auth bypass hours after disclosure (source)
- US indicts Black Kingdom ransomware admin for Microsoft Exchange attacks (source)
- U.S. Charges Yemeni Hacker Behind Black Kingdom Ransomware Targeting 1,500 Systems (source)
- New "Bring Your Own Installer" EDR bypass used in ransomware attack (source)
Related Vulnerability
| DATE | CVE | VULNERABILITY TITLE | RISK |
|---|---|---|---|
| 2022-10-03 | CVE-2022-41040 | Server-Side Request Forgery (SSRF) vulnerability in Microsoft Exchange Server 2013/2016/2019 Microsoft Exchange Server Elevation of Privilege Vulnerability | 0.0 |