Security News

Once they've identified a tempting asset to exploit, attackers employ techniques to find a vulnerability. Some attackers use tried-and-true methods, but the most creative in the group find ways to exploit systems through unexpected vectors.

The Plus Addons for Elementor plugin for WordPress has a critical security vulnerability that attackers can exploit to quickly, easily and remotely take over a website. "If you are using The Plus Addons for Elementor plugin, we strongly recommend that you deactivate and remove the plugin completely until this vulnerability is patched," researchers said.

Maza, a place online for fraudsters and extorters to connect to pull off their operations, has been breached by an unknown attacker, in just the latest in a series of attacks targeting elite Russian-language cybercrime forums. These forums are where threat actors can go to access ransomware-as-a-service tools, launder stolen money and even get advice on how to improve their crimes, Flashpoint vice president Thomas Hofmann explained to Threatpost.

It's notable for its unusual sophistication, according to researchers, evidenced by its multiple modules. The code is specifically taking aim at the Oracle MICROS Restaurant Enterprise Series 3700 POS - a management software suite used by hundreds of thousands of bars, restaurants, hotels and other hospitality establishments worldwide, according to ESET. The attacks have mainly been in the U.S., researchers said - though the initial infection vector is unknown.
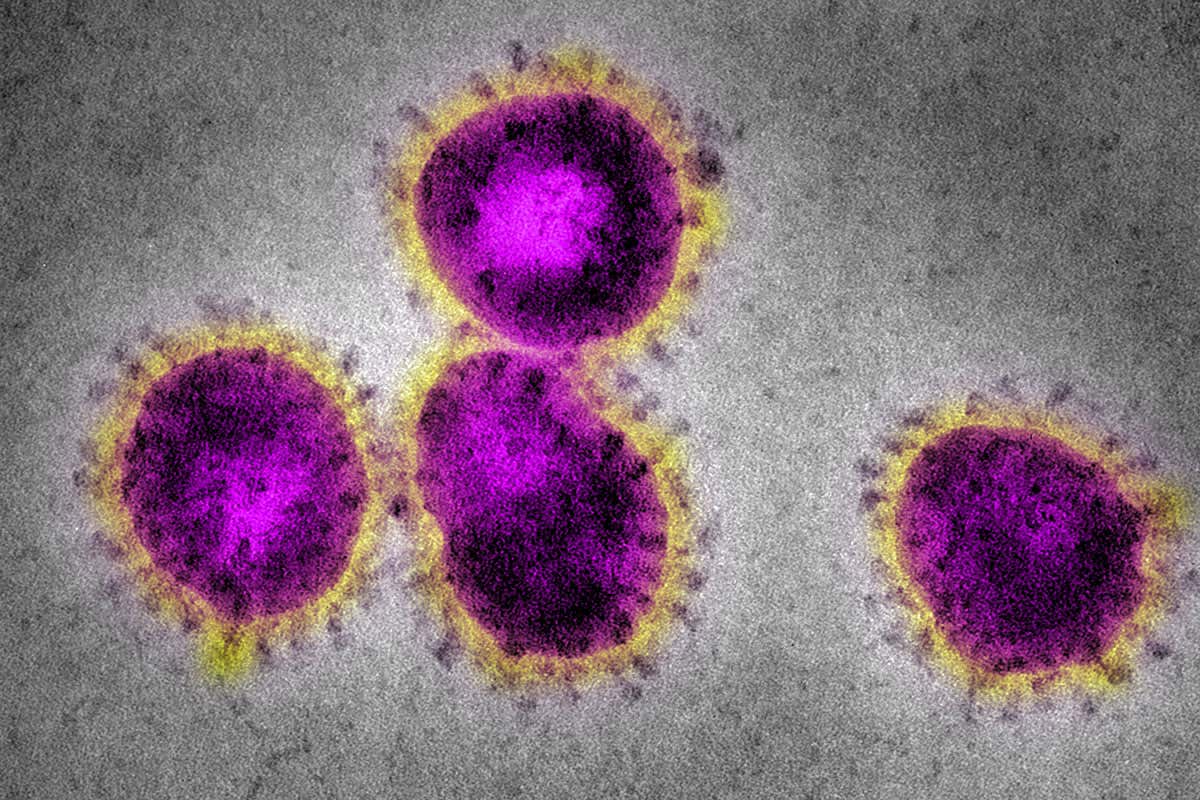
Cyberattackers have reached a peak of sending 1.5 million malicious emails per day related to the COVID-19 pandemic over the course of the last three months, according to new research. "We saw a rise in unwanted emails containing embedded URLs using the keywords of 'COVID' or 'corona,' from negligible values in January 2020 to over half a million blocked per day the end-of-March onwards," he wrote in the post.

Legitimate-looking links from OneDrive, Google Drive, iCloud, and Dropbox slip by standard security measures. Bad actors have added a new snare to their bag of social engineering tricks- malicious OneDrive, Google Drive, iCloud, and Dropbox links.

Across the board, malicious cyber-activity was down partly as a result of hectic holiday schedules and vacations with fewer employees around to interact with malicious activity. This decrease in activity also tracks to the heightened malicious activity Nuspire researchers saw at the beginning of 2019.

Remote attackers can easily compromise the device and pivot to move laterally through the LAN or WAN.

Attivo Networks surveyed more than 450 cybersecurity professionals and executives globally to gain insights into detection trends, top threat concerns, attack surface concerns, and what’s on their...

XM Cyber's Adi Ashkenazy on the Latest TrendsAre cyberattackers working on ways to counter artificial intelligence-augmented security? And will the bad guys ever use AI-driven attacks? Adi...