Security News > 2025 > March > Critical Ingress NGINX Controller Vulnerability Allows RCE Without Authentication
2025-03-24 18:55
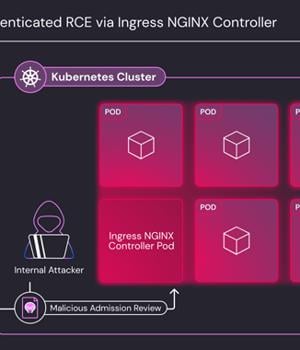
A set of five critical security shortcomings have been disclosed in the Ingress NGINX Controller for Kubernetes that could result in unauthenticated remote code execution, putting over 6,500 clusters at immediate risk by exposing the component to the public internet. The vulnerabilities (CVE-2025-24513, CVE-2025-24514, CVE-2025-1097, CVE-2025-1098, and CVE-2025-1974 ), assigned a CVSS score of
News URL
https://thehackernews.com/2025/03/critical-ingress-nginx-controller.html
#authentication #critical #nginx #RCE #vulnerability #CVE-2025-24513 #CVE-2025-1098 #CVE-2025-1097 #CVE-2025-1974 #CVE-2025-24514
Related news
- Gladinet’s Triofox and CentreStack Under Active Exploitation via Critical RCE Vulnerability (source)
- Critical Commvault RCE vulnerability fixed, PoC available (CVE-2025-34028) (source)
- CISA Warns of CentreStack's Hard-Coded MachineKey Vulnerability Enabling RCE Attacks (source)
- Critical Apache Roller Vulnerability (CVSS 10.0) Enables Unauthorized Session Persistence (source)
- Critical Erlang/OTP SSH Vulnerability (CVSS 10.0) Allows Unauthenticated Code Execution (source)
- Critical Erlang/OTP SSH pre-auth RCE is 'Surprisingly Easy' to exploit, patch now (source)
- Critical Erlang/OTP SSH RCE bug now has public exploits, patch now (source)
- Critical Langflow RCE flaw exploited to hack AI app servers (source)
- SysAid Patches 4 Critical Flaws Enabling Pre-Auth RCE in On-Premise Version (source)
- Unpatched critical bugs in Versa Concerto lead to auth bypass, RCE (source)