Security News
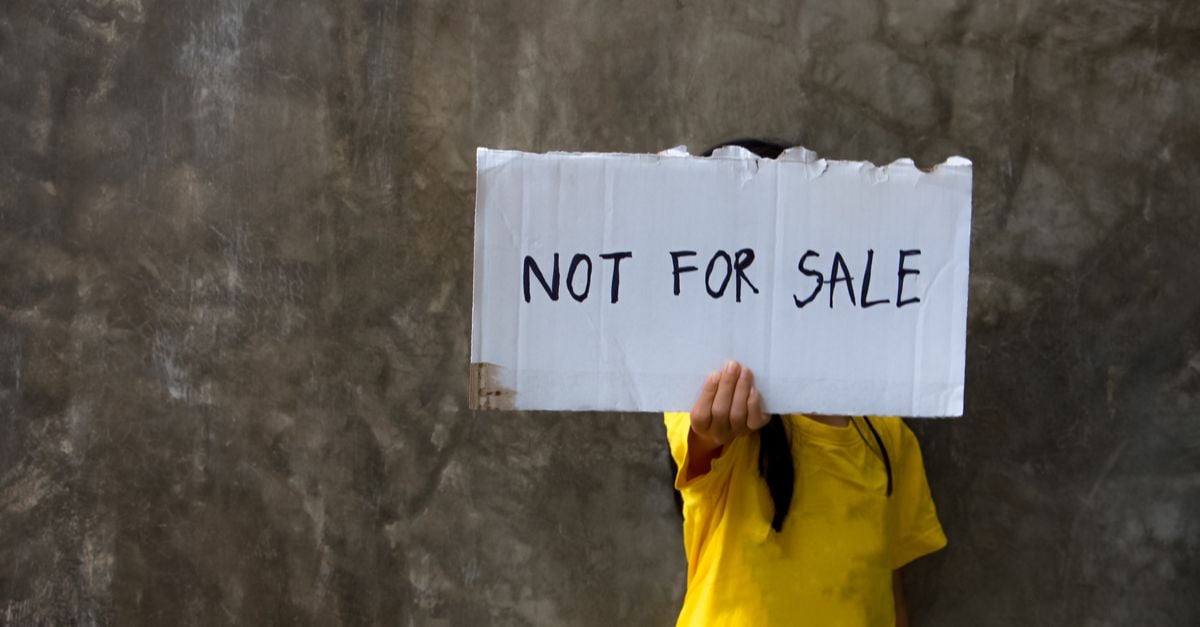
On Monday, the FBI's online crime division - the Internet Crime Complaint Center - issued a warning that human traffickers are increasingly using online platforms, including popular social media and dating platforms, to recruit and to advertise sex trafficking victims. Human trafficking victims are beaten, starved, deceived, and forced into sex work or agricultural, domestic, restaurant, or factory jobs with little to no pay.

Baltimore, MD-based ZeroFOX has raised $74 million in a new funding round led by Intel Capital and including existing vendors NEA, Highland Capital Partners, Redline Capital Management, Hercules Capital and Core Capital. ZeroFOX delivers an AI-powered platform that protects users and brands from social media-sourced threats.

Those two forces are, one, individual social media users and, second, the engagement algorithms used by social media platforms. Social media algorithms can be used to magnify a troll's message and promote the re-sharing of a message that appeals to a niche corner of a social media platform.

TikTok, a mobile video app popular with teens, was vulnerable to SMS spoofing attacks that could have led to the extraction of private information, according to infosec researchers. If the user clicked that malicious link, the attacker could access the user's TikTok account and, so Check Point said, manipulate its content by deleting videos, uploading new videos and making private or "Hidden" videos public.

Give us free instant messaging for our smartphones, and faster than you can say "Viral kitten video," we're collectively part of a mass surveillance nightmare. Or just give in and download the popular - and free - ToTok social messaging app.

Twitter Funds Team to Develop an Open and Decentralized Standard for Social Media read more

Twitter co-founder Jack Dorsey is funding research aimed at changing the way information circulates on social media -- with the goal of combating online violence, hate and disinformation. read more

A special episode dedicated to social media culture!

Most people nowadays are quite aware that hiring managers put their social media postings under a microscope, a new survey finds.

The EU's top court ruled that platforms like Facebook can be ordered to proactively seek out and delete all copies of illegal content.