Security News > 2023 > September > Nearly 12,000 Juniper Firewalls Found Vulnerable to Recently Disclosed RCE Vulnerability
New research has found that close to 12,000 internet-exposed Juniper firewall devices are vulnerable to a recently disclosed remote code execution flaw.
VulnCheck, which discovered a new exploit for CVE-2023-36845, said it could be exploited by an "Unauthenticated and remote attacker to execute arbitrary code on Juniper firewalls without creating a file on the system."
A subsequent proof-of-concept exploit devised by watchTowr combined CVE-2023-36846 and CVE-2023-36845 to upload a PHP file containing malicious shellcode and achieve code execution.
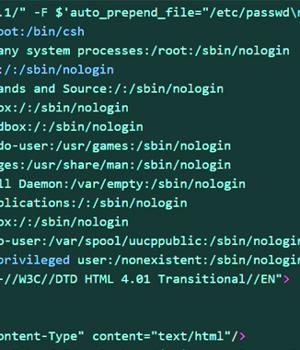
Arbitrary code execution is then achieved by leveraging PHP's auto prepend file and allow url include options in conjunction with the data:// protocol wrapper.
"Anyone who has an unpatched Juniper firewall should examine it for signs of compromise."
Juniper has since disclosed that it's not aware of a successful exploit against its customers, but warned that it has detected exploitation attempts in the wild, making it imperative that users apply the necessary fixes to mitigate potential threats.
News URL
https://thehackernews.com/2023/09/over-12000-juniper-firewalls-found.html
Related Vulnerability
| DATE | CVE | VULNERABILITY TITLE | RISK |
|---|---|---|---|
| 2023-08-17 | CVE-2023-36846 | Missing Authentication for Critical Function vulnerability in Juniper Junos A Missing Authentication for Critical Function vulnerability in Juniper Networks Junos OS on SRX Series allows an unauthenticated, network-based attacker to cause limited impact to the file system integrity. With a specific request to user.php that doesn't require authentication an attacker is able to upload arbitrary files via J-Web, leading to a loss of integrity for a certain part of the file system, which may allow chaining to other vulnerabilities. This issue affects Juniper Networks Junos OS on SRX Series: * All versions prior to 20.4R3-S8; * 21.1 versions 21.1R1 and later; * 21.2 versions prior to 21.2R3-S6; * 21.3 versions prior to 21.3R3-S5; * 21.4 versions prior to 21.4R3-S5; * 22.1 versions prior to 22.1R3-S3; * 22.2 versions prior to 22.2R3-S2; * 22.3 versions prior to 22.3R2-S2, 22.3R3; * 22.4 versions prior to 22.4R2-S1, 22.4R3. | 5.3 |
| 2023-08-17 | CVE-2023-36845 | Unspecified vulnerability in Juniper Junos A PHP External Variable Modification vulnerability in J-Web of Juniper Networks Junos OS on EX Series and SRX Series allows an unauthenticated, network-based attacker to remotely execute code. Using a crafted request which sets the variable PHPRC an attacker is able to modify the PHP execution environment allowing the injection und execution of code. This issue affects Juniper Networks Junos OS on EX Series and SRX Series: * All versions prior to 20.4R3-S9; * 21.1 versions 21.1R1 and later; * 21.2 versions prior to 21.2R3-S7; * 21.3 versions prior to 21.3R3-S5; * 21.4 versions prior to 21.4R3-S5; * 22.1 versions prior to 22.1R3-S4; * 22.2 versions prior to 22.2R3-S2; * 22.3 versions prior to 22.3R2-S2, 22.3R3-S1; * 22.4 versions prior to 22.4R2-S1, 22.4R3; * 23.2 versions prior to 23.2R1-S1, 23.2R2. | 9.8 |