Security News > 2022 > September > Researchers Uncover Covert Attack Campaign Targeting Military Contractors
A new covert attack campaign singled out multiple military and weapons contractor companies with spear-phishing emails to trigger a multi-stage infection process designed to deploy an unknown payload on compromised machines.
"The attack was carried out starting in late summer 2022 targeting at least two high-profile military contractor companies," Den Iuzvyk, Tim Peck, and Oleg Kolesnikov said in an analysis.
Infection chains begin with a phishing mail with a ZIP archive attachment containing a shortcut file that claims to be a PDF document about "Company & Benefits," which is then used to retrieve a stager - an initial binary that's used to download the desired malware - from a remote server.
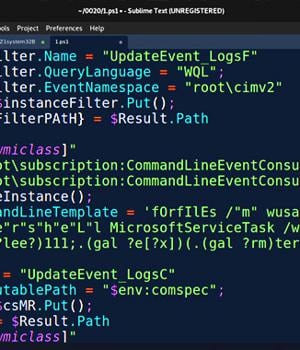
This PowerShell stager sets the stage for a "Robust chain of stagers" that progresses through seven more steps, when the final PowerShell script executes a remote payload "Header.png" hosted on a server named "Terma[.]app.".
"While we were able to download and analyze the header.png file, we were not able to decode it as we believe the campaign was completed and our theory is that the file was replaced in order to prevent further analysis," the researchers explained.
Should all these checks pass, the PowerShell stager proceeds to disable logging, add Windows Defender exclusions for LNK, RAR, and EXE files, and establish persistence via a scheduled task or Windows Registry modifications.
News URL
https://thehackernews.com/2022/09/researchers-uncover-covert-attack.html
Related news
- Russian hackers attack Western military mission using malicious drive (source)
- Researchers Demonstrate How MCP Prompt Injection Can Be Used for Both Attack and Defense (source)
- Researchers Expose New Intel CPU Flaws Enabling Memory Leaks and Spectre v2 Attacks (source)
- Researchers Expose PWA JavaScript Attack That Redirects Users to Adult Scam Apps (source)