Security News > 2022 > September > Serious Security: Browser-in-the-browser attacks – watch out for windows that aren’t!
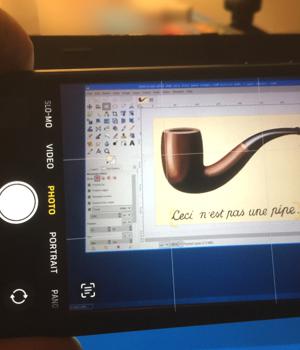
The idea of a BitB attack is to create what looks like a popup browser window that was generated securely by the browser itself, but that is actually nothing more than a web page that was rendered in an existing browser window.
You'd have to admit that the resulting visual content looks exactly like a standalone browser window, even though it's actually a web page inside another browser window.
Of course, if you click on an app screenshot inside a photo browser, you're at very little risk, because the clicks or taps simply won't do what you expect - indeed, you may end up editing or scribbling lines on the image instead. But when it comes to a browser-in-the-browser "Artwork attack" instead, misdirected clicks or taps in a simulated window can be dangerous, because you're still in an active browser window, where JavaScript is in play, and where links still work.
Worse still, any JavaScript running in the active browser window can simulate some of the expected behaviour of a genuine browser popup window in order to add realism, such as dragging it, resizing it, and more.
Browser-in-the-Browser windows aren't real browser windows.
A real browser window will behave independently, so you can move it outside and beyond the original browser window.
News URL
Related news
- WinRAR flaw bypasses Windows Mark of the Web security alerts (source)
- New TCESB Malware Found in Active Attacks Exploiting ESET Security Scanner (source)
- Microsoft: Windows 'inetpub' folder created by security fix, don’t delete (source)
- Don't delete that mystery empty folder. Windows put it there as a security fix (source)
- Browser extensions make nearly every employee a potential attack vector (source)
- Windows NTLM vulnerability exploited in multiple attack campaigns (CVE-2025-24054) (source)
- Windows NTLM hash leak flaw exploited in phishing attacks on governments (source)
- Three Reasons Why the Browser is Best for Stopping Phishing Attacks (source)
- Linux 'io_uring' security blindspot allows stealthy rootkit attacks (source)
- Windows "inetpub" security fix can be abused to block future updates (source)