Security News > 2021 > October > Iranian Hackers Abuse Dropbox in Cyberattacks Against Aerospace and Telecom Firms
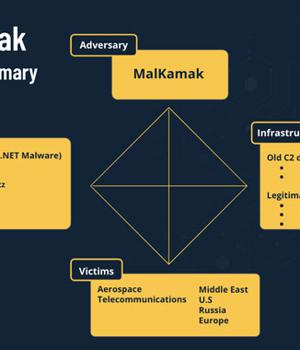
Details have emerged about a new cyber espionage campaign directed against the aerospace and telecommunications industries, primarily in the Middle East, with the goal of stealing sensitive information about critical assets, organizations' infrastructure, and technology while remaining in the dark and successfully evading security solutions.
"The ShellClient RAT has been under ongoing development since at least 2018, with several iterations that introduced new functionalities, while it evaded antivirus tools and managed to remain undetected and publicly unknown," researchers Tom Fakterman, Daniel Frank, Chen Erlich, and Assaf Dahan said in a technical deep dive published today.
Investigation into the attribution of the cyber-attacks has also yielded an entirely new Iranian threat actor named MalKamak that has been operating since around the same time period and has eluded discovery and analysis thus far, with possible connections to other Iranian state-sponsored APT threat actors such as Chafer APT and Agrius APT, the latter of which was found posing as ransomware operators in an effort to conceal the origin of a series of data-wiping hacks against Israeli entities.
The Dropbox storage contains three folders, each storing information about the infected machines, the commands to be executed by the ShellClient RAT, and the results of those commands.
"Every two seconds, the victim machine checks the commands folder, retrieves files that represent commands, parses their content, then deletes them from the remote folder and enables them for execution," the researchers said.
The aforementioned modus operandi mirrors a tactic adopted by another threat actor called IndigoZebra, which was uncovered as relying on Dropbox API to store commands in a victim-specific sub-folder that's retrieved by the malware prior to execution.
News URL
http://feedproxy.google.com/~r/TheHackersNews/~3/CWLIwnoeDJI/iranian-hackers-abuse-dropbox-in.html
Related news
- FBI seeks help to unmask Salt Typhoon hackers behind telecom breaches (source)
- SK Telecom cyberattack: Free SIM replacements for 25 million customers (source)
- France ties Russian APT28 hackers to 12 cyberattacks on French orgs (source)
- Iranian Hackers Maintain 2-Year Access to Middle East CNI via VPN Flaws and Malware (source)
- Nova Scotia Power confirms hackers stole customer data in cyberattack (source)
- Czech Republic Blames China-Linked APT31 Hackers for 2022 Cyberattack (source)
- Iranian Hacker Pleads Guilty in $19 Million Robbinhood Ransomware Attack on Baltimore (source)
- ConnectWise breached in cyberattack linked to nation-state hackers (source)