Security News > 2024 > April > Hackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
2024-04-17 10:23
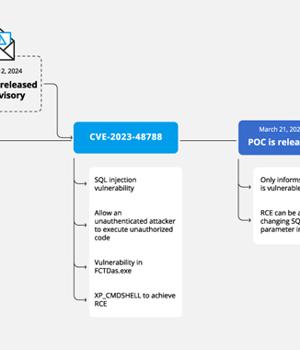
Cybersecurity researchers have discovered a new campaign that's exploiting a recently disclosed security flaw in Fortinet FortiClient EMS devices to deliver ScreenConnect and Metasploit Powerfun payloads. The activity entails the exploitation of CVE-2023-48788 (CVSS score: 9.3), a critical SQL injection flaw that could permit an unauthenticated attacker to execute unauthorized code or
News URL
https://thehackernews.com/2024/04/hackers-exploit-fortinet-flaw-deploy.html
Related news
- Hackers exploit WordPress plugin flaw to infect 3,300 sites with malware (source)
- Magnet Goblin Hacker Group Leveraging 1-Day Exploits to Deploy Nerbian RAT (source)
- Hackers exploit Windows SmartScreen flaw to drop DarkGate malware (source)
- Hackers exploit Aiohttp bug to find vulnerable networks (source)
- Exploit released for Fortinet RCE bug used in attacks, patch now (source)
- Hackers exploit Ray framework flaw to breach servers, hijack resources (source)
- Hackers Exploit Magento Bug to Steal Payment Data from E-commerce Websites (source)
- Hackers Exploit OpenMetadata Flaws to Mine Crypto on Kubernetes (source)
- Microsoft: APT28 hackers exploit Windows flaw reported by NSA (source)
- Microsoft: APT28 hackers exploit Windows flaw reported by NSA (source)
Related Vulnerability
| DATE | CVE | VULNERABILITY TITLE | RISK |
|---|---|---|---|
| 2024-03-12 | CVE-2023-48788 | SQL Injection vulnerability in Fortinet Forticlient Enterprise Management Server A improper neutralization of special elements used in an sql command ('sql injection') in Fortinet FortiClientEMS version 7.2.0 through 7.2.2, FortiClientEMS 7.0.1 through 7.0.10 allows attacker to execute unauthorized code or commands via specially crafted packets. | 9.8 |