Security News > 2024 > March > New ‘Loop DoS’ attack may impact up to 300,000 online systems
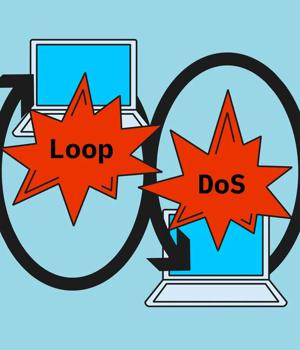
A new denial-of-service attack dubbed 'Loop DoS' targeting application layer protocols can pair network services into an indefinite communication loop that creates large volumes of traffic.
The attack is possible due to a vulnerability, currently tracked as CVE-2024-2169, in the implementation of the UDP protocol, which is susceptible to IP spoofing and does not provide sufficient packet verification.
In total, it is estimated that 300,000 internet hosts are vulnerable to Loop DoS attacks.
Using firewall rules and access-control lists for UDP applications, turning off unnecessary UDP services, and implementing TCP or request validation are also measures that can mitigate the risk of an attack.
New acoustic attack determines keystrokes from typing patterns.
New acoustic attack steals data from keystrokes with 95% accuracy.
News URL
Related news
- New 'Loop DoS' Attack Impacts Hundreds of Thousands of Systems (source)
- Some 300,000 IPs vulnerable to this Loop DoS attack (source)
- Ivanti fixes VPN gateway vulnerability allowing RCE, DoS attacks (source)
- New HTTP/2 Vulnerability Exposes Web Servers to DoS Attacks (source)
- New HTTP/2 DoS attack can crash web servers with a single connection (source)
- Critical 'BatBadBut' Rust Vulnerability Exposes Windows Systems to Attacks (source)
- New Spectre v2 attack impacts Linux systems on Intel CPUs (source)
- Researchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike (source)
Related Vulnerability
| DATE | CVE | VULNERABILITY TITLE | RISK |
|---|---|---|---|
| 2024-03-19 | CVE-2024-2169 | Implementations of UDP application protocol are vulnerable to network loops. | 0.0 |