Security News > 2023 > June > Iranian Hackers Using POWERSTAR Backdoor in Targeted Espionage Attacks
Charming Kitten, the nation-state actor affiliated with Iran's Islamic Revolutionary Guard Corps, has been attributed to a bespoke spear-phishing campaign that delivers an updated version of a fully-featured PowerShell backdoor called POWERSTAR. "There have been improved operational security measures placed in the malware to make it more difficult to analyze and collect intelligence," Volexity researchers Ankur Saini and Charlie Gardner said in a report published this week.
Recent intrusions orchestrated by Charming Kitten have made use of other implants such as PowerLess and BellaCiao, suggesting that the group is utilizing an array of espionage tools at its disposal to realize its strategic objectives.
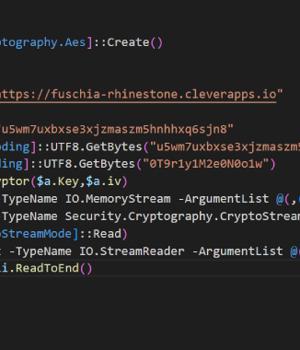
Volexity, which detected a rudimentary variant of POWERSTAR in 2021 distributed by a malicious macro embedded in DOCM file, said the May 2023 attack wave leverages an LNK file inside a password-protected RAR file to download the backdoor from Backblaze, while also taking steps to hinder analysis.
"With POWERSTAR, Charming Kitten sought to limit the risk of exposing their malware to analysis and detection by delivering the decryption method separately from the initial code and never writing it to disk," the researchers said.
"The general phishing playbook used by Charming Kitten and the overall purpose of POWERSTAR remain consistent," the researchers said.
"The references to persistence mechanisms and executable payloads within the POWERSTAR Cleanup module strongly suggests a broader set of tools used by Charming Kitten to conduct malware-enabled espionage."
News URL
https://thehackernews.com/2023/06/iranian-hackers-charming-kitten-utilize.html
Related news
- Hackers Deploy Python Backdoor in Palo Alto Zero-Day Attack (source)
- Iranian hackers pose as journalists to push backdoor malware (source)
- Hackers Exploiting Popular Document Publishing Sites for Phishing Attacks (source)
- Hackers Hijack GitHub Accounts in Supply Chain Attack Affecting Top-gg and Others (source)
- US sanctions APT31 hackers behind critical infrastructure attacks (source)
- Microsoft still unsure how hackers stole MSA key in 2023 Exchange attack (source)
- XZ Utils Supply Chain Attack: A Threat Actor Spent Two Years to Implement a Linux Backdoor (source)
- Iranian MuddyWater Hackers Adopt New C2 Tool 'DarkBeatC2' in Latest Campaign (source)
- TA558 Hackers Weaponize Images for Wide-Scale Malware Attacks (source)
- Russian APT Deploys New 'Kapeka' Backdoor in Eastern European Attacks (source)