Security News > 2023 > March > Researchers Shed Light on CatB Ransomware's Evasion Techniques
The threat actors behind the CatB ransomware operation have been observed using a technique called DLL search order hijacking to evade detection and launch the payload. CatB, also referred to as CatB99 and Baxtoy, emerged late last year and is said to be an "Evolution or direct rebrand" of another ransomware strain known as Pandora based on code-level similarities.
It's worth noting that the use of Pandora has been attributed to Bronze Starlight, a China-based threat actor that's known to employ short-lived ransomware families as a ruse to likely conceal its true objectives.
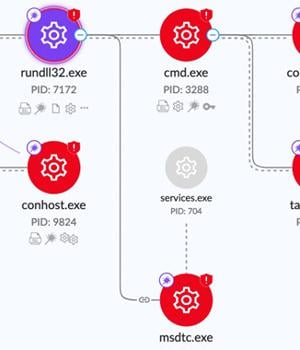
One of the key defining characteristics of CatB is its reliance on DLL hijacking via a legitimate service called Microsoft Distributed Transaction Coordinator to extract and launch the ransomware payload. "Upon execution, CatB payloads rely on DLL search order hijacking to drop and load the malicious payload," SentinelOne researcher Jim Walter said in a report published last week.
"The [MSDTC] configurations changed are the name of the account under which the service should run, which is changed from Network Service to Local System, and the service start option, which is changed from Demand start to Auto start for persistency if a restart occurs," Minerva Labs researcher Natalie Zargarov explained in a previous analysis.
One striking aspect of the ransomware is its absence of a ransom note.
"CatB joins a long line of ransomware families that embrace semi-novel techniques and atypical behaviors such as appending notes to the head of files," Walter said.
News URL
https://thehackernews.com/2023/03/researchers-shed-light-on-catb.html