Security News > 2022 > September > New Malware Families Found Targeting VMware ESXi Hypervisors
Threat actors have been found deploying never-before-seen post-compromise implants in VMware's virtualization software to seize control of infected systems and evade detection.
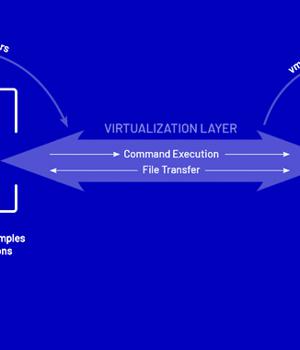
Google's Mandiant threat intelligence division referred to it as a "Novel malware ecosystem" that impacts VMware ESXi, Linux vCenter servers, and Windows virtual machines, allowing attackers to maintain persistent access to the hypervisor as well as execute arbitrary commands.
The hyperjacking attacks, per the cybersecurity vendor, involved the use of malicious vSphere Installation Bundles to sneak in two implants, dubbed VIRTUALPITA and VIRTUALPIE, on the ESXi hypervisors.
"This malware differs in that it supports remaining both persistent and covert, which is consistent with the goals of larger threat actors and APT groups who target strategic institutions with the intention of dwelling undetected for some time," VMware disclosed.
Also uncovered is a malware sample called VIRTUALGATE in Windows guest virtual machines, which is a C-based utility program that executes an embedded payload capable of using VMware's virtual machine communication interface sockets to run commands on a guest virtual machine from a hypervisor host.
Mandiant also warned that the campaign's techniques to get around traditional security controls by exploiting virtualization software represent a new attack surface that's likely to be picked up by other hacker groups.
News URL
https://thehackernews.com/2022/09/new-malware-families-found-targeting.html