Security News > 2021 > October > Researchers Discover UEFI Bootkit Targeting Windows Computers Since 2012
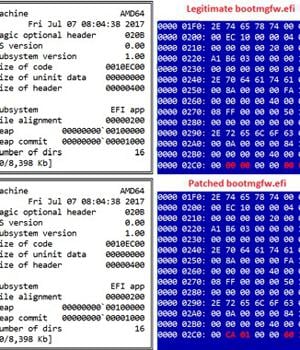
Cybersecurity researchers on Tuesday revealed details of a previously undocumented UEFI bootkit that has been put to use by threat actors to backdoor Windows systems as early as 2012 by modifying a legitimate Windows Boot Manager binary to achieve persistence, once again demonstrating how technology meant to secure the environment prior to loading the operating system is increasingly becoming a "Tempting target."
Slovak cybersecurity firm ESET codenamed the new malware "ESPecter" for its ability to persist on the EFI System Partition, in addition to circumventing Microsoft Windows Driver Signature Enforcement to load its own unsigned driver that can be used to facilitate espionage activities such as document theft, keylogging, and screen monitoring by periodically capturing screenshots.
"ESPecter shows that threat actors are relying not only on UEFI firmware implants when it comes to pre-OS persistence and, despite the existing security mechanisms like UEFI Secure Boot, invest their time into creating malware that would be easily blocked by such mechanisms, if enabled and configured correctly," ESET researchers Martin Smolár and Anton Cherepanov said in a technical write-up published Tuesday.
The development marks the fourth time real-world cases of UEFI malware have been discovered so far, following LoJax, MosaicRegressor, and most recently FinFisher, the last of which was found leveraging the same method of compromise to persist on the ESP in the form of a patched Windows Boot Manager.
"By patching the Windows Boot Manager, attackers achieve execution in the early stages of the system boot process, before the operating system is fully loaded," the researchers said.
"Even though Secure Boot stands in the way of executing untrusted UEFI binaries from the ESP, over the last few years we have been witness to various UEFI firmware vulnerabilities affecting thousands of devices that allow disabling or bypassing Secure Boot," the researchers noted.
News URL
http://feedproxy.google.com/~r/TheHackersNews/~3/Az0020v418M/researchers-discover-uefi-bootkit.html