Vulnerabilities > CVE-2018-7600 - Improper Input Validation vulnerability in multiple products
Attack vector
NETWORK Attack complexity
LOW Privileges required
NONE Confidentiality impact
HIGH Integrity impact
HIGH Availability impact
HIGH Summary
Drupal before 7.58, 8.x before 8.3.9, 8.4.x before 8.4.6, and 8.5.x before 8.5.1 allows remote attackers to execute arbitrary code because of an issue affecting multiple subsystems with default or common module configurations.
Vulnerable Configurations
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Buffer Overflow via Environment Variables This attack pattern involves causing a buffer overflow through manipulation of environment variables. Once the attacker finds that they can modify an environment variable, they may try to overflow associated buffers. This attack leverages implicit trust often placed in environment variables.
- Server Side Include (SSI) Injection An attacker can use Server Side Include (SSI) Injection to send code to a web application that then gets executed by the web server. Doing so enables the attacker to achieve similar results to Cross Site Scripting, viz., arbitrary code execution and information disclosure, albeit on a more limited scale, since the SSI directives are nowhere near as powerful as a full-fledged scripting language. Nonetheless, the attacker can conveniently gain access to sensitive files, such as password files, and execute shell commands.
- Cross Zone Scripting An attacker is able to cause a victim to load content into their web-browser that bypasses security zone controls and gain access to increased privileges to execute scripting code or other web objects such as unsigned ActiveX controls or applets. This is a privilege elevation attack targeted at zone-based web-browser security. In a zone-based model, pages belong to one of a set of zones corresponding to the level of privilege assigned to that page. Pages in an untrusted zone would have a lesser level of access to the system and/or be restricted in the types of executable content it was allowed to invoke. In a cross-zone scripting attack, a page that should be assigned to a less privileged zone is granted the privileges of a more trusted zone. This can be accomplished by exploiting bugs in the browser, exploiting incorrect configuration in the zone controls, through a cross-site scripting attack that causes the attackers' content to be treated as coming from a more trusted page, or by leveraging some piece of system functionality that is accessible from both the trusted and less trusted zone. This attack differs from "Restful Privilege Escalation" in that the latter correlates to the inadequate securing of RESTful access methods (such as HTTP DELETE) on the server, while cross-zone scripting attacks the concept of security zones as implemented by a browser.
- Cross Site Scripting through Log Files An attacker may leverage a system weakness where logs are susceptible to log injection to insert scripts into the system's logs. If these logs are later viewed by an administrator through a thin administrative interface and the log data is not properly HTML encoded before being written to the page, the attackers' scripts stored in the log will be executed in the administrative interface with potentially serious consequences. This attack pattern is really a combination of two other attack patterns: log injection and stored cross site scripting.
- Command Line Execution through SQL Injection An attacker uses standard SQL injection methods to inject data into the command line for execution. This could be done directly through misuse of directives such as MSSQL_xp_cmdshell or indirectly through injection of data into the database that would be interpreted as shell commands. Sometime later, an unscrupulous backend application (or could be part of the functionality of the same application) fetches the injected data stored in the database and uses this data as command line arguments without performing proper validation. The malicious data escapes that data plane by spawning new commands to be executed on the host.
D2sec
name Drupal 7 SA-CORE-2018-002 RCE url http://www.d2sec.com/exploits/drupal_7_sa-core-2018-002_rce.html name Drupal 8 SA-CORE-2018-002 RCE url http://www.d2sec.com/exploits/drupal_8_sa-core-2018-002_rce.html
Exploit-Db
description Drupal < 8.3.9 / < 8.4.6 / < 8.5.1 - 'Drupalgeddon2' Remote Code Execution (PoC). CVE-2018-7600. Webapps exploit for PHP platform file exploits/php/webapps/44448.py id EDB-ID:44448 last seen 2018-05-24 modified 2018-04-13 platform php port published 2018-04-13 reporter Exploit-DB source https://www.exploit-db.com/download/44448/ title Drupal < 8.3.9 / < 8.4.6 / < 8.5.1 - 'Drupalgeddon2' Remote Code Execution (PoC) type webapps description Drupal < 7.58 / < 8.3.9 / < 8.4.6 / < 8.5.1 - 'Drupalgeddon2' Remote Code Execution. CVE-2018-7600. Webapps exploit for PHP platform file exploits/php/webapps/44449.rb id EDB-ID:44449 last seen 2018-05-24 modified 2018-04-13 platform php port 80 published 2018-04-13 reporter Exploit-DB source https://www.exploit-db.com/download/44449/ title Drupal < 7.58 / < 8.3.9 / < 8.4.6 / < 8.5.1 - 'Drupalgeddon2' Remote Code Execution type webapps description Drupal < 8.3.9 / < 8.4.6 / < 8.5.1 - 'Drupalgeddon2' Remote Code Execution (Metasploit). CVE-2018-7600. Remote exploit for PHP platform. Tags: Metas... file exploits/php/remote/44482.rb id EDB-ID:44482 last seen 2018-05-24 modified 2018-04-17 platform php port 80 published 2018-04-17 reporter Exploit-DB source https://www.exploit-db.com/download/44482/ title Drupal < 8.3.9 / < 8.4.6 / < 8.5.1 - 'Drupalgeddon2' Remote Code Execution (Metasploit) type remote
Metasploit
| description | This module exploits a Drupal property injection in the Forms API. Drupal 6.x, < 7.58, 8.2.x, < 8.3.9, < 8.4.6, and < 8.5.1 are vulnerable. |
| id | MSF:EXPLOIT/UNIX/WEBAPP/DRUPAL_DRUPALGEDDON2 |
| last seen | 2020-06-12 |
| modified | 2020-02-19 |
| published | 2018-04-13 |
| references |
|
| reporter | Rapid7 |
| source | https://github.com/rapid7/metasploit-framework/blob/master//modules/exploits/unix/webapp/drupal_drupalgeddon2.rb |
| title | Drupal Drupalgeddon 2 Forms API Property Injection |
Nessus
NASL family FreeBSD Local Security Checks NASL id FREEBSD_PKG_A9E466E8414411E8A29200E04C1EA73D.NASL description Drupal Security Team reports : CVE-2018-7600: Drupal before 7.58, 8.x before 8.3.9, 8.4.x before 8.4.6, and 8.5.x before 8.5.1 allows remote attackers to execute arbitrary code because of an issue affecting multiple subsystems with default or common module configurations. last seen 2020-03-31 modified 2018-04-16 plugin id 109055 published 2018-04-16 reporter This script is Copyright (C) 2018-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/109055 title FreeBSD : drupal -- Drupal Core - Multiple Vulnerabilities (a9e466e8-4144-11e8-a292-00e04c1ea73d) (Drupalgeddon 2) NASL family Fedora Local Security Checks NASL id FEDORA_2018-906BA26B4D.NASL description - [8.4.6](https://www.drupal.org/project/drupal/releases/8 .4.6) - [SA-CORE-2018-002 (CVE-2018-7600)](https://www.drupal.org/SA-CORE-2018-002 ) - [8.4.5](https://www.drupal.org/project/drupal/releases/8 .4.5) - [SA-CORE-2018-001 (CVE-2017-6926 / CVE-2017-6927 / CVE-2017-6930 / CVE-2017-6931)](https://www.drupal.org/SA-CORE-2018-001) - [8.4.4](https://www.drupal.org/project/drupal/releases/8 .4.4) - [8.4.3](https://www.drupal.org/project/drupal/releases/8 .4.3) - [8.4.2](https://www.drupal.org/project/drupal/releases/8 .4.2) - [8.4.1](https://www.drupal.org/project/drupal/releases/8 .4.1) - [8.4.0](https://www.drupal.org/project/drupal/releases/8 .4.0) - [8.4.0-rc2](https://www.drupal.org/project/drupal/releas es/8.4.0-rc2) - [8.4.0-rc1](https://www.drupal.org/project/drupal/releas es/8.4.0-rc1) - [8.4.0-beta1](https://www.drupal.org/project/drupal/rele ases/8.4.0-beta1) - [8.4.0-alpha1](https://www.drupal.org/project/drupal/rel eases/8.4.0-alpha1) Note that Tenable Network Security has extracted the preceding description block directly from the Fedora update system website. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2019-01-03 plugin id 120615 published 2019-01-03 reporter This script is Copyright (C) 2019-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/120615 title Fedora 28 : drupal8 (2018-906ba26b4d) (Drupalgeddon 2) NASL family Debian Local Security Checks NASL id DEBIAN_DLA-1325.NASL description Jasper Mattsson found a remote code execution vulnerability in the Drupal content management system. This potentially allows attackers to exploit multiple attack vectors on a Drupal site, which could result in the site being completely compromised. For further information please refer to the official upstream advisory at https://www.drupal.org/sa-core-2018-002. For Debian 7 last seen 2020-03-17 modified 2018-03-29 plugin id 108695 published 2018-03-29 reporter This script is Copyright (C) 2018-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/108695 title Debian DLA-1325-1 : drupal7 security update (Drupalgeddon 2) NASL family CGI abuses NASL id DRUPAL_8_5_1.NASL description According to its self-reported version, the instance of Drupal running on the remote web server is 7.x prior to 7.58, 8.3.x prior to 8.3.9, 8.4.x prior to 8.4.6, or 8.5.x prior to 8.5.1. It is, therefore, affected by a remote code execution vulnerability. Note that Nessus has not tested for these issues but has instead relied only on the application last seen 2020-06-01 modified 2020-06-02 plugin id 108688 published 2018-03-28 reporter This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/108688 title Drupal 7.x < 7.58 / 8.3.x < 8.3.9 / 8.4.x < 8.4.6 / 8.5.x < 8.5.1 Remote Code Execution Vulnerability (SA-CORE-2018-002) NASL family Fedora Local Security Checks NASL id FEDORA_2018-922CC2FBAA.NASL description - [8.3.9](https://www.drupal.org/project/drupal/releases/8 .3.9) - [SA-CORE-2018-002 (CVE-2018-7600)](https://www.drupal.org/SA-CORE-2018-002 ) - [8.3.8](https://www.drupal.org/project/drupal/releases/8 .3.8) - [SA-CORE-2018-001 (CVE-2017-6926 / CVE-2017-6927 / CVE-2017-6930 / CVE-2017-6931)](https://www.drupal.org/SA-CORE-2018-001) Note that Tenable Network Security has extracted the preceding description block directly from the Fedora update system website. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2018-04-24 plugin id 109288 published 2018-04-24 reporter This script is Copyright (C) 2018-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/109288 title Fedora 26 : drupal8 (2018-922cc2fbaa) (Drupalgeddon 2) NASL family Debian Local Security Checks NASL id DEBIAN_DSA-4156.NASL description A remote code execution vulnerability has been found in Drupal, a fully-featured content management framework. For additional information, please refer to the upstream advisory at https://www.drupal.org/sa-core-2018-002 last seen 2020-03-30 modified 2018-03-29 plugin id 108698 published 2018-03-29 reporter This script is Copyright (C) 2018-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/108698 title Debian DSA-4156-1 : drupal7 - security update (Drupalgeddon 2)
Packetstorm
data source https://packetstormsecurity.com/files/download/147392/drupal_drupalgeddon2.rb.txt id PACKETSTORM:147392 last seen 2018-04-27 published 2018-04-26 reporter FireFart source https://packetstormsecurity.com/files/147392/Drupal-Drupalgeddon-2-Forms-API-Property-Injection.html title Drupal Drupalgeddon 2 Forms API Property Injection data source https://packetstormsecurity.com/files/download/147181/drupalgeddon2poc-exec.txt id PACKETSTORM:147181 last seen 2018-04-14 published 2018-04-13 reporter Vitalii Rudnykh source https://packetstormsecurity.com/files/147181/Drupal-Drupalgeddon2-Remote-Code-Execution.html title Drupal Drupalgeddon2 Remote Code Execution data source https://packetstormsecurity.com/files/download/147182/drupalgeddon2poc2-exec.txt id PACKETSTORM:147182 last seen 2018-04-14 published 2018-04-13 reporter Hans Topo source https://packetstormsecurity.com/files/147182/Drupal-Drupalgeddon2-Remote-Code-Execution-Ruby-Port.html title Drupal Drupalgeddon2 Remote Code Execution Ruby Port data source https://packetstormsecurity.com/files/download/147247/drupalgeddon2-exec.rb.txt id PACKETSTORM:147247 last seen 2018-04-19 published 2018-04-17 reporter Vitalii Rudnykh source https://packetstormsecurity.com/files/147247/Drupalgeddon2-Drupal-Remote-Code-Execution.html title Drupalgeddon2 Drupal Remote Code Execution
Saint
| bid | 103534 |
| description | Drupal Form API command execution |
| id | web_cms_drupal |
| title | drupal_form_api |
| type | remote |
Seebug
| bulletinFamily | exploit |
| description | Two weeks ago, a highly critical (21/25 NIST rank) vulnerability, nicknamed Drupalgeddon 2 (SA-CORE-2018-002 / CVE-2018-7600), was disclosed by the Drupal security team. This vulnerability allowed an unauthenticated attacker to perform remote code execution on default or common Drupal installations. Drupal is an open-source content management system (CMS) that is used by more than one million sites around the world (including governments, e-retail, enterprise organizations, financial institutions and more), all of which are vulnerable unless patched. Until now details of the vulnerability were not available to the public, however, Check Point Research can now expand upon this vulnerability and reveal exactly how it works. In brief, Drupal had insufficient input sanitation on Form API (FAPI) AJAX requests. As a result, this enabled an attacker to potentially inject a malicious payload into the internal form structure. This would have caused Drupal to execute it without user authentication. By exploiting this vulnerability an attacker would have been able to carry out a full site takeover of any Drupal customer. The vulnerability existed on all Drupal versions from 6 to 8, though has since been patched to those who manually update their site. In this document we will showcase real life attack scenarios around an out-of-the-box installation of Drupal’s flagship product, Drupal 8. ### Technical Details #### The Vulnerability To provide some background, Drupal’s Form API was introduced in Drupal 6 and allowed alteration of the form data during the form rendering process. This revolutionized the way markup processing was done. In Drupal 7 the Form API was generalized to what is now known as “Renderable Arrays”. This extended API is used to represent the structure of most of the UI elements in Drupal, such as pages, blocks, nodes and more. Renderable arrays contain metadata that is used in the rendering process. These renderable arrays are a key-value structure in which the property keys start with a hash sign (#). Please see below for an example: ``` [ ‘#type’ => ‘markup’, ‘#markup’ => ‘<em>some text</em>’, ‘#prefix’ => ‘<div>’, ‘#suffix’ => ‘</div>’ ] ``` #### Drupal’s Patch The patch that Drupal published adds a single class called RequestSanitizer with a stripDangerousValues method that unsets all the items in an input array for keys that start with a hash sign. This method sanitizes input data in `$_GET`, `$_POST` & `$_COOKIES` during the very early stages of Drupal’s bootstrap (immediately after loading the site configurations). We assume that one of the reasons that the patch was done in this way was to make it harder to find and exploit the vulnerability. #### Finding an Attack Vector Because of the above we focused on forms that are exposed to anonymous users. There are a few of those forms available, one of which is the user registration form. This form contains multiple fields, as can be seen in the screenshot below. 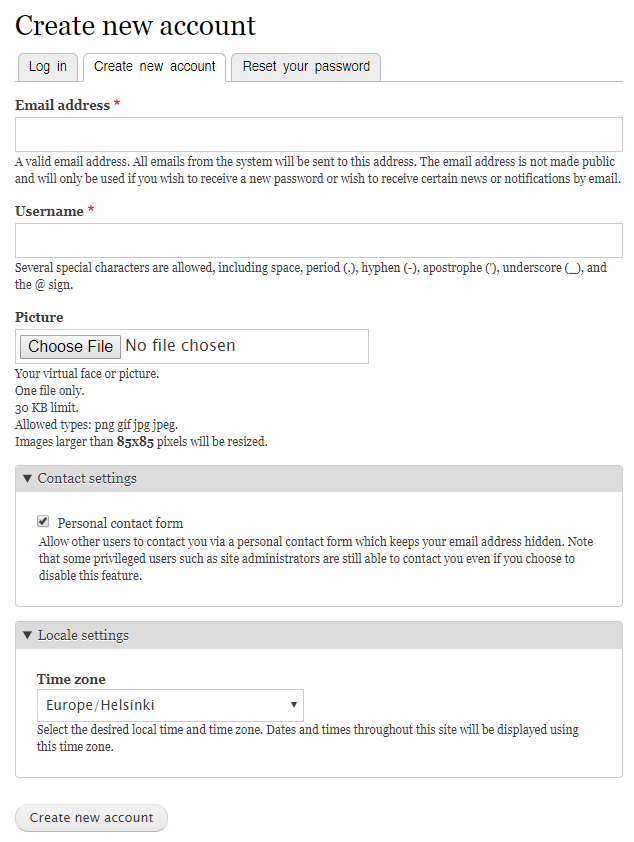 Figure 1: The Drupal registration form. We knew that we needed to inject a renderable array somewhere in the form structure, we just had to find out where. As it happens, the “Email address” field does not sanitize the type of input that it receives. This allowed us to inject an array to the form array structure (as the value of the email field). 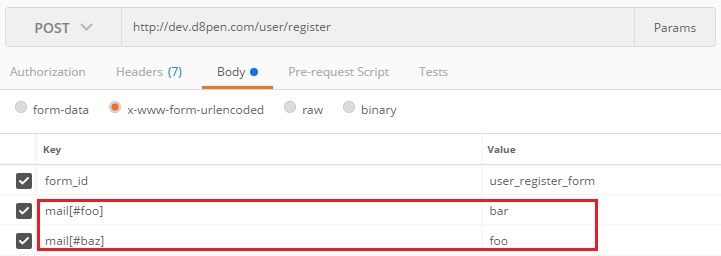 Figure 2: Injecting our renderable array into the mail input of the registration form.  Figure 3: Example of injected form renderable array. Now all we needed was for Drupal to render our injected array. Since Drupal treats our injected array as a value and not as an element, we needed to trick Drupal into rendering it. The situations in which Drupal renders arrays are as follows: 1. Page load 2. Drupal AJAX API – i.e. when a user fills an AJAX form, a request is made to Drupal which renders an HTML markup and updates the form. After investigating possible attack vectors surrounding the above functionalities, because of the post-submission rendering process and the way Drupal implements it, we came to the conclusion that an AJAX API call is our best option to leverage an attack. As part of the user registration form, the “Picture” field uses Drupal’s AJAX API to upload a picture into the server and replace it with a thumbnail of the uploaded image. 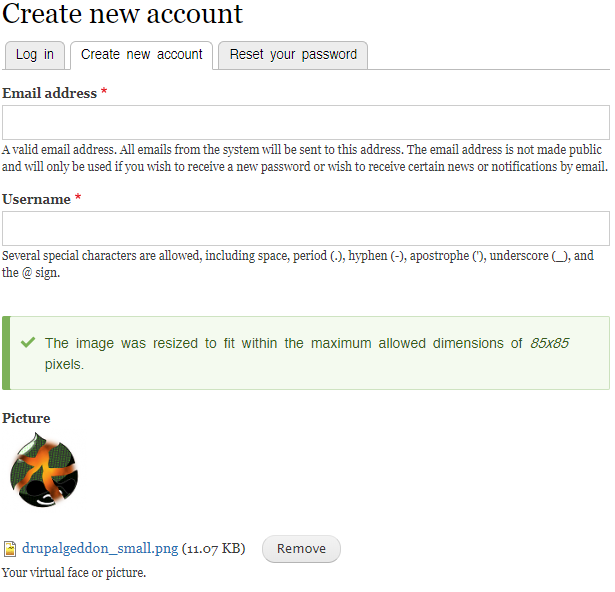 Figure 4: Form used to upload a picture using AJAX API. Diving into the AJAX file upload callback revealed that it uses a GET parameter to locate the part of the form that needs to be updated in the client. 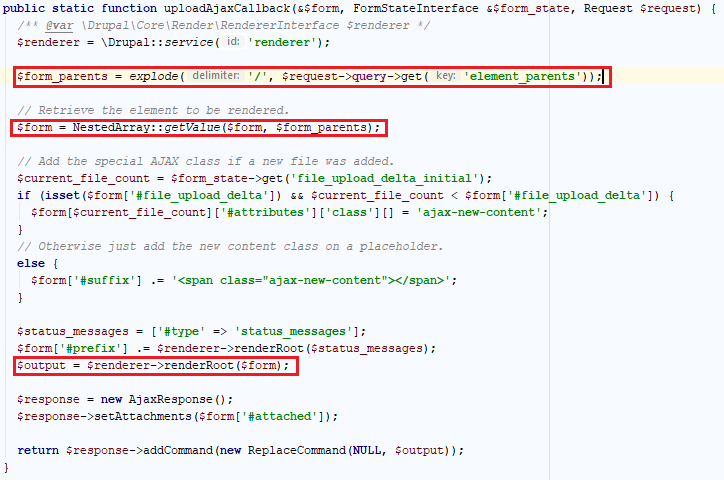 Figure 5: The AJAX ‘upload file’ callback function code. After pointing element_parents to the part of the form that contained our injected array, Drupal successfully rendered it. #### Weaponizing Drupalgeddon 2 Now, all we had to do is to inject a malicious render array that uses one of Drupal’s rendering callback to execute code on the system. There were several properties we could have injected: * #access_callback * Used by Drupal to determine whether or not the current user has access to an element. * #pre_render * Manipulates the render array before rendering. * #lazy_builder * Used to add elements in the very end of the rendering process. * #post_render * Receives the result of the rendering process and adds wrappers around it. For our POC to work, we chose the #lazy_builder element as the one being injected into the mail array. Combined with the AJAX API callback functionality, we could direct Drupal to render our malicious array. This allowed us to take control over the administrator’s account, install a malicious backdoor module and finally execute arbitrary commands on the server. 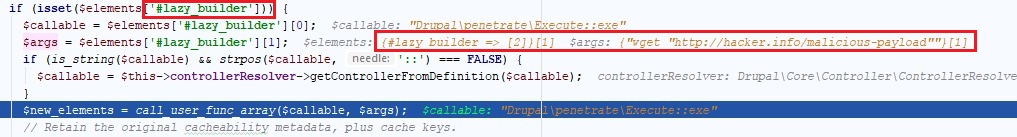 Figure 6: injecting malicious command into one of Drupal’s rendering callbacks. 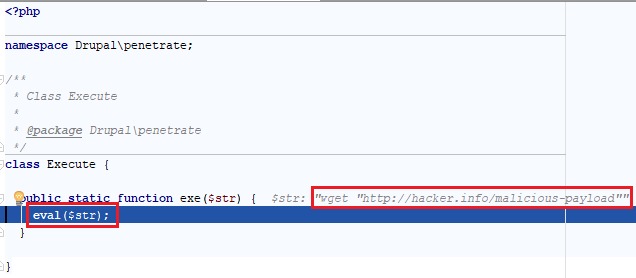 Figure 7: Successfully executing shell commands using the malicious module. ### Conclusion After seeing earlier publications on Twitter and several security blogs, it was apparent that there was much confusion among the community regarding this vulnerability announcement, with some even doubting the severity of it. As a result, we considered it worthwhile to looking deeper into. The research however was challenging as we were starting from a very large attack surface since the patch blurred the real attack vectors. To expedite our findings, we were fortunate to be joined by experts in the Drupal platform. The final results highlight how easy it is for organization to be exposed through no fault of their own, but rather through the third party platforms they use every day. |
| id | SSV:97207 |
| last seen | 2018-06-08 |
| modified | 2018-03-30 |
| published | 2018-03-30 |
| reporter | Knownsec |
| title | Drupal core Remote Code Execution(CVE-2018-7600) (Drupalgeddon2) |
The Hacker News
id THN:8E5D44939B2B2FF0156F7FF2D4802857 last seen 2018-04-26 modified 2018-04-26 published 2018-04-25 reporter Mohit Kumar source https://thehackernews.com/2018/04/drupal-vulnerability-exploit.html title Third Critical Drupal Flaw Discovered—Patch Your Sites Immediately id THN:F03064A70C65D9BD62A8F5898BA276D2 last seen 2018-04-18 modified 2018-04-18 published 2018-04-17 reporter Mohit Kumar source https://thehackernews.com/2018/04/drupal-cryptocurrency-hacking.html title Hackers Exploiting Drupal Vulnerability to Inject Cryptocurrency Miners id THN:8D76D821D51DF9AAAAF1C9D1FA8CA0C5 last seen 2018-06-05 modified 2018-06-05 published 2018-06-05 reporter Swati Khandelwal source https://thehackernews.com/2018/06/drupalgeddon2-exploit.html title Over 115,000 Drupal Sites Still Vulnerable to Drupalgeddon2 Exploit id THN:B0F0C0035DAAFA1EC62F15464A80677E last seen 2018-04-14 modified 2018-04-14 published 2018-04-13 reporter Swati Khandelwal source https://thehackernews.com/2018/04/drupal-rce-exploit-code.html title Hackers Have Started Exploiting Drupal RCE Exploit Released Yesterday id THN:F8EDB5227B5DA0E4B49064C2972A193D last seen 2018-04-26 modified 2018-04-26 published 2018-04-26 reporter Swati Khandelwal source https://thehackernews.com/2018/04/drupalgeddon3-exploit-code.html title Release of PoC Exploit for New Drupal Flaw Once Again Puts Sites Under Attack
Related news
- Crypto Me0wing attacks: Kitty cashes in on Monero (source)
- Hackers Exploiting Drupal Vulnerability to Inject Cryptocurrency Miners (source)
- Drupal Sites Targeted With Backdoors, Miners in Drupalgeddon2 Attacks (source)
- Drupalgeddon: Critical Flaw Exposes Million Drupal Websites to Attacks (source)
- Muhstik Botnet Targeting Redis Servers Using Recently Disclosed Vulnerability (source)
References
- http://www.securityfocus.com/bid/103534
- http://www.securityfocus.com/bid/103534
- http://www.securitytracker.com/id/1040598
- http://www.securitytracker.com/id/1040598
- https://badpackets.net/over-100000-drupal-websites-vulnerable-to-drupalgeddon-2-cve-2018-7600/
- https://badpackets.net/over-100000-drupal-websites-vulnerable-to-drupalgeddon-2-cve-2018-7600/
- https://blog.appsecco.com/remote-code-execution-with-drupal-core-sa-core-2018-002-95e6ecc0c714
- https://blog.appsecco.com/remote-code-execution-with-drupal-core-sa-core-2018-002-95e6ecc0c714
- https://github.com/a2u/CVE-2018-7600
- https://github.com/a2u/CVE-2018-7600
- https://github.com/g0rx/CVE-2018-7600-Drupal-RCE
- https://github.com/g0rx/CVE-2018-7600-Drupal-RCE
- https://greysec.net/showthread.php?tid=2912&pid=10561
- https://greysec.net/showthread.php?tid=2912&pid=10561
- https://groups.drupal.org/security/faq-2018-002
- https://groups.drupal.org/security/faq-2018-002
- https://lists.debian.org/debian-lts-announce/2018/03/msg00028.html
- https://lists.debian.org/debian-lts-announce/2018/03/msg00028.html
- https://research.checkpoint.com/uncovering-drupalgeddon-2/
- https://research.checkpoint.com/uncovering-drupalgeddon-2/
- https://twitter.com/arancaytar/status/979090719003627521
- https://twitter.com/arancaytar/status/979090719003627521
- https://twitter.com/RicterZ/status/979567469726613504
- https://twitter.com/RicterZ/status/979567469726613504
- https://twitter.com/RicterZ/status/984495201354854401
- https://twitter.com/RicterZ/status/984495201354854401
- https://www.debian.org/security/2018/dsa-4156
- https://www.debian.org/security/2018/dsa-4156
- https://www.drupal.org/sa-core-2018-002
- https://www.drupal.org/sa-core-2018-002
- https://www.exploit-db.com/exploits/44448/
- https://www.exploit-db.com/exploits/44448/
- https://www.exploit-db.com/exploits/44449/
- https://www.exploit-db.com/exploits/44449/
- https://www.exploit-db.com/exploits/44482/
- https://www.exploit-db.com/exploits/44482/
- https://www.synology.com/support/security/Synology_SA_18_17
- https://www.synology.com/support/security/Synology_SA_18_17
- https://www.tenable.com/blog/critical-drupal-core-vulnerability-what-you-need-to-know
- https://www.tenable.com/blog/critical-drupal-core-vulnerability-what-you-need-to-know