Vulnerabilities > CVE-2015-1433 - Cross-site Scripting vulnerability in multiple products
Attack vector
NETWORK Attack complexity
MEDIUM Privileges required
NONE Confidentiality impact
NONE Integrity impact
PARTIAL Availability impact
NONE Summary
program/lib/Roundcube/rcube_washtml.php in Roundcube before 1.0.5 does not properly quote strings, which allows remote attackers to conduct cross-site scripting (XSS) attacks via the style attribute in an email.
Vulnerable Configurations
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Cross Site Scripting through Log Files An attacker may leverage a system weakness where logs are susceptible to log injection to insert scripts into the system's logs. If these logs are later viewed by an administrator through a thin administrative interface and the log data is not properly HTML encoded before being written to the page, the attackers' scripts stored in the log will be executed in the administrative interface with potentially serious consequences. This attack pattern is really a combination of two other attack patterns: log injection and stored cross site scripting.
- Embedding Scripts in Non-Script Elements This attack is a form of Cross-Site Scripting (XSS) where malicious scripts are embedded in elements that are not expected to host scripts such as image tags (<img>), comments in XML documents (< !-CDATA->), etc. These tags may not be subject to the same input validation, output validation, and other content filtering and checking routines, so this can create an opportunity for an attacker to tunnel through the application's elements and launch a XSS attack through other elements. As with all remote attacks, it is important to differentiate the ability to launch an attack (such as probing an internal network for unpatched servers) and the ability of the remote attacker to collect and interpret the output of said attack.
- Embedding Scripts within Scripts An attack of this type exploits a programs' vulnerabilities that are brought on by allowing remote hosts to execute scripts. The attacker leverages this capability to execute scripts to execute his/her own script by embedding it within other scripts that the target software is likely to execute. The attacker must have the ability to inject script into script that is likely to be executed. If this is done, then the attacker can potentially launch a variety of probes and attacks against the web server's local environment, in many cases the so-called DMZ, back end resources the web server can communicate with, and other hosts. With the proliferation of intermediaries, such as Web App Firewalls, network devices, and even printers having JVMs and Web servers, there are many locales where an attacker can inject malicious scripts. Since this attack pattern defines scripts within scripts, there are likely privileges to execute said attack on the host. Of course, these attacks are not solely limited to the server side, client side scripts like Ajax and client side JavaScript can contain malicious scripts as well. In general all that is required is for there to be sufficient privileges to execute a script, but not protected against writing.
- Cross-Site Scripting in Error Pages An attacker distributes a link (or possibly some other query structure) with a request to a third party web server that is malformed and also contains a block of exploit code in order to have the exploit become live code in the resulting error page. When the third party web server receives the crafted request and notes the error it then creates an error message that echoes the malformed message, including the exploit. Doing this converts the exploit portion of the message into to valid language elements that are executed by the viewing browser. When a victim executes the query provided by the attacker the infected error message error message is returned including the exploit code which then runs in the victim's browser. XSS can result in execution of code as well as data leakage (e.g. session cookies can be sent to the attacker). This type of attack is especially dangerous since the exploit appears to come from the third party web server, who the victim may trust and hence be more vulnerable to deception.
- Cross-Site Scripting Using Alternate Syntax The attacker uses alternate forms of keywords or commands that result in the same action as the primary form but which may not be caught by filters. For example, many keywords are processed in a case insensitive manner. If the site's web filtering algorithm does not convert all tags into a consistent case before the comparison with forbidden keywords it is possible to bypass filters (e.g., incomplete black lists) by using an alternate case structure. For example, the "script" tag using the alternate forms of "Script" or "ScRiPt" may bypass filters where "script" is the only form tested. Other variants using different syntax representations are also possible as well as using pollution meta-characters or entities that are eventually ignored by the rendering engine. The attack can result in the execution of otherwise prohibited functionality.
Nessus
NASL family Debian Local Security Checks NASL id DEBIAN_DLA-613.NASL description Multiple CSRF and XSS issues allow remote attackers to hijack the authentication and execute roundcube operations without the consent of the user. In some cases, this could result in data loss or data theft. CVE-2014-9587 Multiple cross-site request forgery (CSRF) vulnerabilities in allow remote attackers to hijack the authentication of unspecified victims via unknown vectors, related to (1) address book operations or the (2) ACL or (3) Managesieve plugins. CVE-2015-1433 Incorrect quotation logic during sanitization of style HTML attribute allows remote attackers to execute arbitrary JavaScript code on the user last seen 2020-03-17 modified 2016-09-09 plugin id 93385 published 2016-09-09 reporter This script is Copyright (C) 2016-2020 Tenable Network Security, Inc. source https://www.tenable.com/plugins/nessus/93385 title Debian DLA-613-1 : roundcube security update NASL family Fedora Local Security Checks NASL id FEDORA_2015-1761.NASL description Cross-site scripting vulnerability has been fixed in Roundcube 1.0.5 version. http://roundcube.net/news/2015/01/24/security-update-1.0.5/ http://trac.roundcube.net/wiki/Changelog#RELEASE1.0.5 http://trac.roundcube.net/ticket/1490227 CVE request: http://www.openwall.com/lists/oss-security/2015/01/31/3 Note that Tenable Network Security has extracted the preceding description block directly from the Fedora security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2015-02-16 plugin id 81362 published 2015-02-16 reporter This script is Copyright (C) 2015-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/81362 title Fedora 20 : roundcubemail-1.0.5-1.fc20 (2015-1761) NASL family SuSE Local Security Checks NASL id OPENSUSE-2015-148.NASL description roundcubemail was updated to version 1.0.5 to fix one security issue. This security issue was fixed : - CVE-2015-1433: program/lib/Roundcube/rcube_washtml.php in Roundcube before 1.0.5 did not properly quote strings, which allowed remote attackers to conduct cross-site scripting (XSS) attacks via the style attribute in an email (bnc#915789). Various non-security bugs were resolved in this update. Please see the changes file for details. last seen 2020-06-05 modified 2015-02-16 plugin id 81373 published 2015-02-16 reporter This script is Copyright (C) 2015-2020 Tenable Network Security, Inc. source https://www.tenable.com/plugins/nessus/81373 title openSUSE Security Update : roundcubemail (openSUSE-2015-148) NASL family Fedora Local Security Checks NASL id FEDORA_2015-1772.NASL description Cross-site scripting vulnerability has been fixed in Roundcube 1.0.5 version. http://roundcube.net/news/2015/01/24/security-update-1.0.5/ http://trac.roundcube.net/wiki/Changelog#RELEASE1.0.5 http://trac.roundcube.net/ticket/1490227 CVE request: http://www.openwall.com/lists/oss-security/2015/01/31/3 Note that Tenable Network Security has extracted the preceding description block directly from the Fedora security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2015-02-16 plugin id 81364 published 2015-02-16 reporter This script is Copyright (C) 2015-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/81364 title Fedora 21 : roundcubemail-1.0.5-1.fc21 (2015-1772)
Seebug
| bulletinFamily | exploit |
| description | RoundCube Webmail is a foreign use of a wide an open source php e-mail system, the meaning is still quite large. roundcube webmail official website: <https://roundcube.net/>, download the latest version. /program/lib/Roundcube/rcube_washtml.php this file is actually a rich text filter class class rcube_washtml it. roundcube is the use of this class for rich text filter. First probably look, I know this class feature: 1. Use the DOM to change the HTML to do parsing, remove all tags, corresponding to the attribute key and value. 2. The use of the white list, and only keep the allowed tags and attributes. 3. According to the preserved tags, attributes, keys and values, spliced into the filtered HTML output. In fact, from this process I see a safety hazard. I used to own wrote a rich text class, the class of the first two points of the process and this class is the same, but the third point, I was the results are also saved as a DOM object, and then converted into HTML output. The two have what difference? A large different point is that roundcube to HTML splicing, the splicing process if not handled properly the quotes, it is easy to lead to the attribute“value”beyond the quoted range, into a new“attribute”, such as onerror in. Well, we saw 246 the line, `else if ($key == 'style' && ($style = $this->wash_style($value))) { $quot = strpos($style, '"') !== false ? "'" : '"'; $t .= 'style=' . $quot . $style . $quot; }` When the property name is the style, then the value of the incoming wash_style function. This function, as the name implies is to filter the css used, then the return value of the`$style `stitching to the final HTML in:`$t .= 'style=' . $quot . $style . $quot;` `$quote `is a quotation mark,`$style `put into quotation marks. The`$quote `is before a word is defined, when the`$style `in single quotes,`$quote `is a double quotation mark, when the`$style `in double-quotes,`$quote `is in single quotation marks. But if`$style`, two quotation marks are there? Certainly will cause the quotation marks are closed, then the back will be able to write the other attributes. There's some trouble with the analysis I will not write, the last of my payload is: `<img src="data:xxx1" style=aaa:'"/onerror=alert(1)//' >` We see that style in the middle there is a single quotation mark and double quotation marks, because there are, so choose a single quotation mark as the outside of the closing quotation marks. And because I also have single quotes, so the front of the single quotes closure, and lead to the back of the content overflow, onerror become a new attribute, and finally lead to stored XSS in. After the class the processed HTML into this, chrome the latest version directly triggered without interaction `<!-- html ignored --><!-- body ignored --><img src="data:xxx1" style='aaa: '\"/onerror=alert(1)//" />` Test, directly send a text containing the above POC in the mail, roundcube opens the message can be triggered: 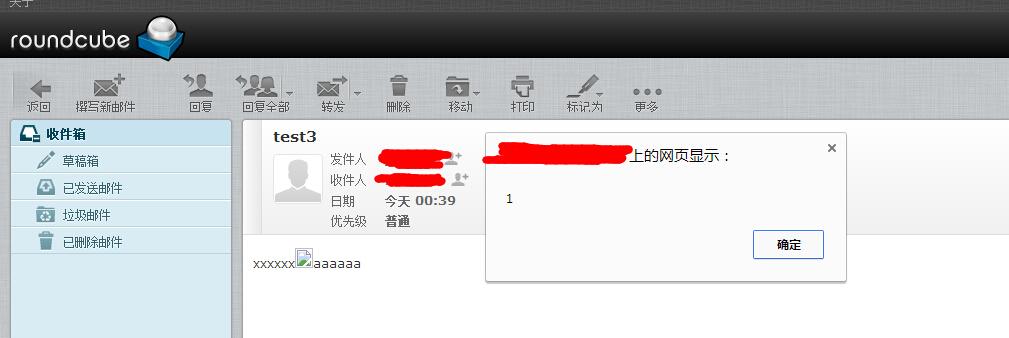  |
| id | SSV:92792 |
| last seen | 2017-11-19 |
| modified | 2017-03-16 |
| published | 2017-03-16 |
| reporter | Root |
| title | RoundCube Webmail mail <1.0.5 body stored XSS(CVE-2015-1433) |
References
- http://lists.fedoraproject.org/pipermail/package-announce/2015-February/149877.html
- http://lists.opensuse.org/opensuse-updates/2015-02/msg00064.html
- http://roundcube.net/news/2015/01/24/security-update-1.0.5/
- http://trac.roundcube.net/changeset/786aa0725/github
- http://trac.roundcube.net/ticket/1490227
- http://www.openwall.com/lists/oss-security/2015/01/31/3
- http://www.openwall.com/lists/oss-security/2015/01/31/6
- http://www.securityfocus.com/bid/72401