Security News

That GitHub repo an interviewer wants you to work on could be malware Palo Alto Networks' Unit 42 has detailed a pair of job market hacking schemes linked to state-sponsored actors in North Korea:...

Months of work reveals how this tricky malware family targets... the financial services sector A brand-new macOS malware strain from North Korean state-sponsored hackers has been spotted in the wild.…

The North Korea-linked nation-state group called BlueNoroff has been attributed to a previously undocumented macOS malware strain dubbed ObjCShellz. Jamf Threat Labs, which disclosed details of the malware, said it's used as part of the RustBucket malware campaign, which came to light earlier this year.

As much as $7 billion in cryptocurrency has been illicitly laundered through cross-chain crime, with the North Korea-linked Lazarus Group linked to the theft of roughly $900 million of those...

South Korea's National Intelligence Service has warned North Korea is attacking its shipbuilding sector. "Security recently reported that North Korea has targeted our shipbuilding companies to strengthen its naval military power," explained [PDF] the intelligence agency, via machine translation.
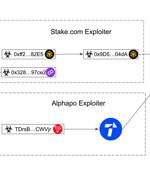
The North Korea-affiliated Lazarus Group has stolen nearly $240 million in cryptocurrency since June 2023, marking a significant escalation of its hacks. According to multiple reports from Certik, Elliptic, and ZachXBT, the infamous hacking group is said to be suspected behind the theft of $31 million in digital assets from the CoinEx exchange on September 12, 2023.

Lazarus Group, the infamous cryptocurrency thieves backed by North Korea, may try to liquidate a stash of stolen Bitcoin worth more than $40 million, according to the FBI. In an alert issued on Tuesday, agents said they tracked the purloined cryptocurrency over the past 24 hours. Most recently, on June 22 Lazarus Group stole $60 million in virtual currency from Alphapo, which processes payments for gambling services.

A hacking unit of North Korea's Reconnaissance General Bureau was linked to the JumpCloud breach after the attackers made an operational security mistake, inadvertently exposing their real-world IP addresses. While North Korean state hackers are known for using commercial VPN services to mask their IP addresses and actual locations, during the JumpCloud attack, the VPNs they were using failed and exposed their location in Pyongyang while connecting to a victim's network.

A North Korean satellite allegedly designed for reconnaissance was not viable for its alleged intended purpose, according to South Korea's military on Wednesday. North Korea attempted to put the satellite into orbit on May 31, but it instead plunged into the sea soon after it was launched.

North Korea has created a fake version of South Korea's largest internet portal, Naver, in a large scale phishing attempt, Seoul's National Intelligence Service said on Wednesday. NIS has asked the Korea Internet & Security Agency to shut down the now inaccessible phishing site.