Security News > 2023 > July > PicassoLoader Malware Used in Ongoing Attacks on Ukraine and Poland
Government entities, military organizations, and civilian users in Ukraine and Poland have been targeted as part of a series of campaigns designed to steal sensitive data and gain persistent remote access to the infected systems.
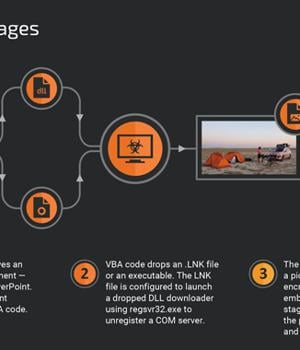
The intrusion set, which stretches from April 2022 to July 2023, leverages phishing lures and decoy documents to deploy a downloader malware called PicassoLoader, which acts as a conduit to launch Cobalt Strike Beacon and njRAT. "The attacks used a multistage infection chain initiated with malicious Microsoft Office documents, most commonly using Microsoft Excel and PowerPoint file formats," Cisco Talos researcher Vanja Svajcer said in a new report.
It's worth noting that a subset of these attacks has already been documented over the past year by Ukraine's Computer Emergency Response Team and Fortinet FortiGuard Labs, one of which employed macro-laden PowerPoint documents to deliver Agent Tesla malware in July 2022.
The infection chains aim to convince victims to enable macros, with the VBA macro engineered to drop a DLL downloader known as PicassoLoader that subsequently reaches out to an attacker-controlled site to fetch the next-stage payload, a legitimate image file that embeds the final malware.
The disclosure comes as CERT-UA detailed a number of phishing operations distributing the SmokeLoader malware as well as a smishing attack designed to gain unauthorized control of targets' Telegram accounts.
Last month, CERT-UA disclosed a cyber espionage campaign aimed at state organizations and media representatives in Ukraine that makes use of email and instant messengers to distribute files, which, when launched, results in the execution of a PowerShell script called LONEPAGE to fetch next-stage browser stealer and keylogger payloads.
News URL
https://thehackernews.com/2023/07/picassoloader-malware-used-in-ongoing.html
Related news
- DarkGate Malware Exploited Recently Patched Microsoft Flaw in Zero-Day Attack (source)
- From Deepfakes to Malware: AI's Expanding Role in Cyber Attacks (source)
- New BunnyLoader Malware Variant Surfaces with Modular Attack Features (source)
- Over 100 US and EU orgs targeted in StrelaStealer malware attacks (source)
- The Biggest Takeaways from Recent Malware Attacks (source)
- Critical Flaws Leave 92,000 D-Link NAS Devices Vulnerable to Malware Attacks (source)
- Microsoft fixes two Windows zero-days exploited in malware attacks (source)
- TA558 Hackers Weaponize Images for Wide-Scale Malware Attacks (source)
- OfflRouter Malware Evades Detection in Ukraine for Almost a Decade (source)
- CoralRaider attacks use CDN cache to push info-stealer malware (source)