Security News > 2023 > May > N. Korean Lazarus Group Targets Microsoft IIS Servers to Deploy Espionage Malware
The infamous Lazarus Group actor has been targeting vulnerable versions of Microsoft Internet Information Services servers as an initial breach route to deploy malware on targeted systems.
The findings come from the AhnLab Security Emergency response Center, which detailed the advanced persistent threat's continued abuse of DLL side-loading techniques to deploy malware.
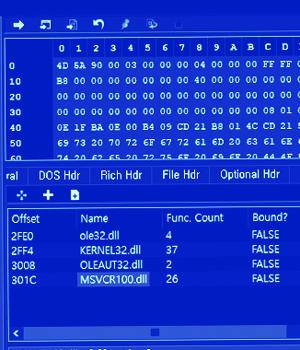
"The threat actor places a malicious DLL in the same folder path as a normal application via the Windows IIS web server process, w3wp.exe," ASEC explained.
DLL side-loading, similar to DLL search-order hijacking, refers to the proxy execution of a rogue DLL via a benign binary planted in the same directory.
"In particular, since the threat group primarily utilizes the DLL side-loading technique during their initial infiltrations, companies should proactively monitor abnormal process execution relationships and take preemptive measures to prevent the threat group from carrying out activities such as information exfiltration and lateral movement," ASEC said.
The Lazarus Group and its various clusters are believed to be operated by the Technical Reconnaissance Bureau, which oversees North Korea's development of offensive cyber tactics and tools.
News URL
https://thehackernews.com/2023/05/n-korean-lazarus-group-targets.html
Related news
- Microsoft fixes auth issues on Windows Server, Windows 11 24H2 (source)
- Fake Microsoft Office add-in tools push malware via SourceForge (source)
- Police detains Smokeloader malware customers, seizes servers (source)
- Microsoft: Windows Server 2025 restarts break connectivity on some DCs (source)
- Microsoft fixes Windows Server 2025 blue screen, install issues (source)
- Oh, cool. Microsoft melts bug that froze Server 2025 Remote Desktop sessions (source)
- Microsoft pitches pay-to-patch reboot reduction subscription for Windows Server 2025 (source)
- Microsoft: Windows Server hotpatching to require subscription (source)
- Microsoft: April updates cause Windows Server auth issues (source)
- Microsoft Fixes 78 Flaws, 5 Zero-Days Exploited; CVSS 10 Bug Impacts Azure DevOps Server (source)