Security News > 2022 > August > New Evil PLC Attack Weaponizes PLCs to Breach OT and Enterprise Networks
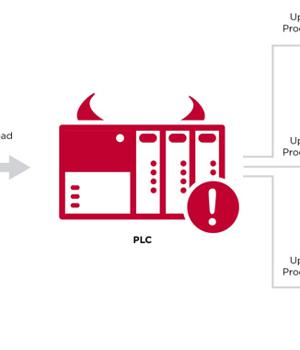
With the Evil PLC attack, the controller acts as a means to an end, permitting the threat actor to breach a workstation, access to all the other PLCs on the network, and even tamper with the controller logic.
Put differently, the idea is to "Use the PLC as a pivot point to attack the engineers who program and diagnose it and gain deeper access to the OT network," the researchers said.
The whole sequence plays out as follows: An opportunistic adversary deliberately induces a malfunction on an internet-exposed PLC, an action that prompts an unsuspecting engineer to connect to the infected PLC using the engineering workstation software as a troubleshooting tool.
"The fact that the PLC stores additional types of data that are used by the engineering software and not the PLC itself" creates a scenario wherein the unused data stored on the PLC can be modified to manipulate the engineering software, the researchers pointed out.
In an alternative theoretical attack scenario, the Evil PLC method can also be used as honeypots to lure threat actors into connecting to a decoy PLC, leading to a compromise of the attacker's machine.
To mitigate such attacks, it's recommended to limit physical and network access to PLCs to authorized engineers and operators, enforce authentication mechanisms to validate the engineering station, monitor OT network traffic for anomalous activity, and apply patches in a timely fashion.
News URL
https://thehackernews.com/2022/08/new-evil-plc-attack-weaponizes-plcs-to.html