Security News > 2021 > November > Palo Alto Warns of Zero-Day Bug in Firewalls Using GlobalProtect Portal VPN
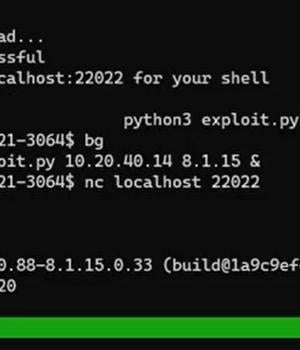
A new zero-day vulnerability has been disclosed in Palo Alto Networks GlobalProtect VPN that could be abused by an unauthenticated network-based attacker to execute arbitrary code on affected devices with root user privileges.
Successful exploitation of the flaw necessitates that the attacker strings it with a technique known as HTTP smuggling to achieve remote code execution on the VPN installations, not to mention have network access to the device on the GlobalProtect service default port 443.
"A memory corruption vulnerability exists in Palo Alto Networks GlobalProtect portal and gateway interfaces that enables an unauthenticated network-based attacker to disrupt system processes and potentially execute arbitrary code with root privileges," Palo Alto Networks said in an independent advisory.
"The attacker must have network access to the GlobalProtect interface to exploit this issue."
In light of the fact that VPN devices are lucrative targets for malicious actors, it's highly recommended that users move quickly to patch the vulnerability.
As a workaround, Palo Alto Networks is advising affected organizations to enable threat signatures for identifiers 91820 and 91855 on traffic destined for GlobalProtect portal and gateway interfaces to prevent any potential attacks against CVE-2021-3064.
News URL
https://thehackernews.com/2021/11/palo-alto-warns-of-zero-day-bug-in.html
Related news
- SonicWall firewall exploit lets hackers hijack VPN sessions, patch now (source)
- Fortinet warns of new zero-day exploited to hijack firewalls (source)
- Mysterious Palo Alto firewall reboots? You're not alone (source)
- SonicWall firewalls now under attack: Patch ASAP or risk intrusion via your SSL VPN (source)
- Palo Alto firewalls under attack as miscreants chain flaws for root access (source)
- Attackers are chaining flaws to breach Palo Alto Networks firewalls (source)
- Palo Alto Networks tags new firewall bug as exploited in attacks (source)
Related Vulnerability
| DATE | CVE | VULNERABILITY TITLE | RISK |
|---|---|---|---|
| 2021-11-10 | CVE-2021-3064 | Out-of-bounds Write vulnerability in Paloaltonetworks Pan-Os A memory corruption vulnerability exists in Palo Alto Networks GlobalProtect portal and gateway interfaces that enables an unauthenticated network-based attacker to disrupt system processes and potentially execute arbitrary code with root privileges. | 9.8 |