Vulnerabilities > CVE-2018-9844 - Cross-site Scripting vulnerability in Iptanus Wordpress File Upload
Attack vector
NETWORK Attack complexity
LOW Privileges required
NONE Confidentiality impact
LOW Integrity impact
LOW Availability impact
NONE Summary
The Iptanus WordPress File Upload plugin before 4.3.4 for WordPress mishandles Settings attributes, leading to XSS.
Vulnerable Configurations
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Cross Site Scripting through Log Files An attacker may leverage a system weakness where logs are susceptible to log injection to insert scripts into the system's logs. If these logs are later viewed by an administrator through a thin administrative interface and the log data is not properly HTML encoded before being written to the page, the attackers' scripts stored in the log will be executed in the administrative interface with potentially serious consequences. This attack pattern is really a combination of two other attack patterns: log injection and stored cross site scripting.
- Embedding Scripts in Non-Script Elements This attack is a form of Cross-Site Scripting (XSS) where malicious scripts are embedded in elements that are not expected to host scripts such as image tags (<img>), comments in XML documents (< !-CDATA->), etc. These tags may not be subject to the same input validation, output validation, and other content filtering and checking routines, so this can create an opportunity for an attacker to tunnel through the application's elements and launch a XSS attack through other elements. As with all remote attacks, it is important to differentiate the ability to launch an attack (such as probing an internal network for unpatched servers) and the ability of the remote attacker to collect and interpret the output of said attack.
- Embedding Scripts within Scripts An attack of this type exploits a programs' vulnerabilities that are brought on by allowing remote hosts to execute scripts. The attacker leverages this capability to execute scripts to execute his/her own script by embedding it within other scripts that the target software is likely to execute. The attacker must have the ability to inject script into script that is likely to be executed. If this is done, then the attacker can potentially launch a variety of probes and attacks against the web server's local environment, in many cases the so-called DMZ, back end resources the web server can communicate with, and other hosts. With the proliferation of intermediaries, such as Web App Firewalls, network devices, and even printers having JVMs and Web servers, there are many locales where an attacker can inject malicious scripts. Since this attack pattern defines scripts within scripts, there are likely privileges to execute said attack on the host. Of course, these attacks are not solely limited to the server side, client side scripts like Ajax and client side JavaScript can contain malicious scripts as well. In general all that is required is for there to be sufficient privileges to execute a script, but not protected against writing.
- Cross-Site Scripting in Error Pages An attacker distributes a link (or possibly some other query structure) with a request to a third party web server that is malformed and also contains a block of exploit code in order to have the exploit become live code in the resulting error page. When the third party web server receives the crafted request and notes the error it then creates an error message that echoes the malformed message, including the exploit. Doing this converts the exploit portion of the message into to valid language elements that are executed by the viewing browser. When a victim executes the query provided by the attacker the infected error message error message is returned including the exploit code which then runs in the victim's browser. XSS can result in execution of code as well as data leakage (e.g. session cookies can be sent to the attacker). This type of attack is especially dangerous since the exploit appears to come from the third party web server, who the victim may trust and hence be more vulnerable to deception.
- Cross-Site Scripting Using Alternate Syntax The attacker uses alternate forms of keywords or commands that result in the same action as the primary form but which may not be caught by filters. For example, many keywords are processed in a case insensitive manner. If the site's web filtering algorithm does not convert all tags into a consistent case before the comparison with forbidden keywords it is possible to bypass filters (e.g., incomplete black lists) by using an alternate case structure. For example, the "script" tag using the alternate forms of "Script" or "ScRiPt" may bypass filters where "script" is the only form tested. Other variants using different syntax representations are also possible as well as using pollution meta-characters or entities that are eventually ignored by the rendering engine. The attack can result in the execution of otherwise prohibited functionality.
Exploit-Db
| description | WordPress Plugin File Upload 4.3.3 - Stored Cross-Site Scripting (PoC). CVE-2018-9844. Webapps exploit for PHP platform |
| file | exploits/php/webapps/44444.txt |
| id | EDB-ID:44444 |
| last seen | 2018-05-24 |
| modified | 2018-04-10 |
| platform | php |
| port | |
| published | 2018-04-10 |
| reporter | Exploit-DB |
| source | https://www.exploit-db.com/download/44444/ |
| title | WordPress Plugin File Upload 4.3.3 - Stored Cross-Site Scripting (PoC) |
| type | webapps |
Packetstorm
| data source | https://packetstormsecurity.com/files/download/147138/wpfileupload433-xss.txt |
| id | PACKETSTORM:147138 |
| last seen | 2018-04-12 |
| published | 2018-04-10 |
| reporter | ManhNho |
| source | https://packetstormsecurity.com/files/147138/WordPress-File-Upload-4.3.3-Cross-Site-Scripting.html |
| title | WordPress File Upload 4.3.3 Cross Site Scripting |
Seebug
| bulletinFamily | exploit |
| description | ###0x01 漏洞概述 Wordpress的插件WordPress File Upload v4.3.3及其以前版本在管理后台存在一处存储型xss漏洞。攻击者可以通过该漏洞执行js脚本,获取管理员cookie。 漏洞名称:WordPress Plugin File Upload 4.3.3 - Stored Cross-Site Scripting (PoC) 漏洞来源:https://www.exploit-db.com/exploits/44444/ CVE:CVE-2018-9844 影响组件:WordPress Plugin File Upload (https://wordpress.org/plugins/wp-file-upload) 影响版本:<=v4.3.3 ###0x02 漏洞验证 登录admin-panel,安装wp-file-upload插件并激活,打开Wordpress File Upload Control Panel,表单中的wfu_basedir文本框由于过滤不严格,可以直接输入js脚本:  输入 ``` <script>alert(/joke/)</script> ``` 点击“update”按钮: 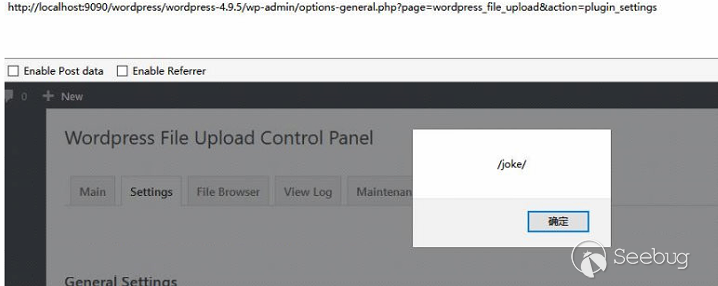 我们看下数据库中插入的值: 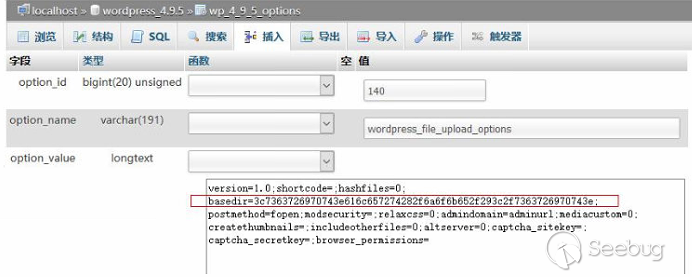 提交的参数进行十六进制编码存储到了数据库: ``` basedir=3c7363726970743e616c657274282f6a6f6b652f293c2f7363726970743e; ``` 解码即为我们上面插入的js脚本。 ###0x03 漏洞分析 通过分析,官网提供的v4.3.4版本及以后版本已经修复了该漏洞,为了分析的方便,直接对比v4.3.3和v4.3.4源码的不同之处: 文件:wfu_admin_settings.php 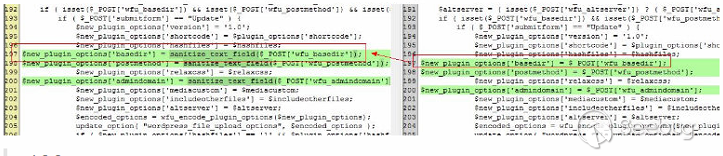 ``` //v4.3.4 $new_plugin_options['basedir']=sanitize_text_field($_POST['wfu_basedir']); //v4.3.3 $new_plugin_options['basedir'] = $_POST['wfu_basedir']; ``` 在v4.3.4中,对输入的POST参数basedir增加了函数sanitize_text_field进行处理,将 < 等符号进行了转义,从而修复了漏洞。 ###0x04 漏洞修复 升级到v4.3.4版本即可。 |
| id | SSV:97249 |
| last seen | 2018-06-26 |
| modified | 2018-04-28 |
| published | 2018-04-28 |
| reporter | My Seebug |
| title | WordPress Plugin File Upload 4.3.3 - Stored Cross-Site Scripting (PoC) |
References
- https://wordpress.org/plugins/wp-file-upload/#developers
- https://wordpress.org/plugins/wp-file-upload/#developers
- https://www.exploit-db.com/exploits/44444/
- https://www.exploit-db.com/exploits/44444/
- https://www.iptanus.com/new-version-4-3-4-of-wordpress-file-upload-plugin/
- https://www.iptanus.com/new-version-4-3-4-of-wordpress-file-upload-plugin/