Vulnerabilities > CVE-2018-4878 - Use After Free vulnerability in multiple products
Attack vector
NETWORK Attack complexity
LOW Privileges required
NONE Confidentiality impact
HIGH Integrity impact
HIGH Availability impact
HIGH Summary
A use-after-free vulnerability was discovered in Adobe Flash Player before 28.0.0.161. This vulnerability occurs due to a dangling pointer in the Primetime SDK related to media player handling of listener objects. A successful attack can lead to arbitrary code execution. This was exploited in the wild in January and February 2018.
Vulnerable Configurations
Common Weakness Enumeration (CWE)
Exploit-Db
description Adobe Flash < 28.0.0.161 - Use-After-Free. CVE-2018-4878. Remote exploit for Multiple platform file exploits/multiple/remote/44412.py id EDB-ID:44412 last seen 2018-05-24 modified 2018-04-06 platform multiple port published 2018-04-06 reporter Exploit-DB source https://www.exploit-db.com/download/44412/ title Adobe Flash < 28.0.0.161 - Use-After-Free type remote description Flash ActiveX 28.0.0.137 - Code Execution (2). CVE-2018-4878. Local exploit for Windows platform id EDB-ID:44745 last seen 2018-05-24 modified 2016-02-13 published 2016-02-13 reporter Exploit-DB source https://www.exploit-db.com/download/44745/ title Flash ActiveX 28.0.0.137 - Code Execution (2) description Flash ActiveX 28.0.0.137 - Code Execution (1). CVE-2018-4878. Local exploit for Windows platform id EDB-ID:44744 last seen 2018-05-24 modified 2016-02-16 published 2016-02-16 reporter Exploit-DB source https://www.exploit-db.com/download/44744/ title Flash ActiveX 28.0.0.137 - Code Execution (1)
Nessus
NASL family Gentoo Local Security Checks NASL id GENTOO_GLSA-201803-08.NASL description The remote host is affected by the vulnerability described in GLSA-201803-08 (Adobe Flash Player: Multiple vulnerabilities) Multiple vulnerabilities have been discovered in Adobe Flash Player. Please review the CVE identifiers referenced below for details. Impact : A remote attacker could possibly execute arbitrary code with the privileges of the process or bypass security restrictions. Workaround : There is no known workaround at this time. last seen 2020-06-01 modified 2020-06-02 plugin id 108434 published 2018-03-19 reporter This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/108434 title GLSA-201803-08 : Adobe Flash Player: Multiple vulnerabilities (Underminer) code # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from Gentoo Linux Security Advisory GLSA 201803-08. # # The advisory text is Copyright (C) 2001-2018 Gentoo Foundation, Inc. # and licensed under the Creative Commons - Attribution / Share Alike # license. See http://creativecommons.org/licenses/by-sa/3.0/ # include("compat.inc"); if (description) { script_id(108434); script_version("1.4"); script_cvs_date("Date: 2019/04/05 23:25:06"); script_cve_id("CVE-2018-4871", "CVE-2018-4877", "CVE-2018-4878", "CVE-2018-4919", "CVE-2018-4920"); script_xref(name:"GLSA", value:"201803-08"); script_name(english:"GLSA-201803-08 : Adobe Flash Player: Multiple vulnerabilities (Underminer)"); script_summary(english:"Checks for updated package(s) in /var/db/pkg"); script_set_attribute( attribute:"synopsis", value: "The remote Gentoo host is missing one or more security-related patches." ); script_set_attribute( attribute:"description", value: "The remote host is affected by the vulnerability described in GLSA-201803-08 (Adobe Flash Player: Multiple vulnerabilities) Multiple vulnerabilities have been discovered in Adobe Flash Player. Please review the CVE identifiers referenced below for details. Impact : A remote attacker could possibly execute arbitrary code with the privileges of the process or bypass security restrictions. Workaround : There is no known workaround at this time." ); script_set_attribute( attribute:"see_also", value:"https://security.gentoo.org/glsa/201803-08" ); script_set_attribute( attribute:"solution", value: "All Adobe Flash Player users should upgrade to the latest version: # emerge --sync # emerge --ask --oneshot --verbose '>=www-plugins/adobe-flash-29.0.0.113'" ); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:H/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:H/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploited_by_malware", value:"true"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:gentoo:linux:adobe-flash"); script_set_attribute(attribute:"cpe", value:"cpe:/o:gentoo:linux"); script_set_attribute(attribute:"patch_publication_date", value:"2018/03/19"); script_set_attribute(attribute:"in_the_news", value:"true"); script_set_attribute(attribute:"plugin_publication_date", value:"2018/03/19"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"Gentoo Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/Gentoo/release", "Host/Gentoo/qpkg-list"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("qpkg.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); if (!get_kb_item("Host/Gentoo/release")) audit(AUDIT_OS_NOT, "Gentoo"); if (!get_kb_item("Host/Gentoo/qpkg-list")) audit(AUDIT_PACKAGE_LIST_MISSING); flag = 0; if (qpkg_check(package:"www-plugins/adobe-flash", unaffected:make_list("ge 29.0.0.113"), vulnerable:make_list("lt 29.0.0.113"))) flag++; if (flag) { if (report_verbosity > 0) security_hole(port:0, extra:qpkg_report_get()); else security_hole(0); exit(0); } else { tested = qpkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "Adobe Flash Player"); }NASL family Red Hat Local Security Checks NASL id REDHAT-RHSA-2018-0285.NASL description An update for flash-plugin is now available for Red Hat Enterprise Linux 6 Supplementary. Red Hat Product Security has rated this update as having a security impact of Critical. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. The flash-plugin package contains a Mozilla Firefox compatible Adobe Flash Player web browser plug-in. This update upgrades Flash Player to version 28.0.0.161. Security Fix(es) : * This update fixes multiple vulnerabilities in Adobe Flash Player. These vulnerabilities, detailed in the Adobe Security Bulletin listed in the References section, could allow an attacker to create a specially crafted SWF file that would cause flash-plugin to crash, execute arbitrary code, or disclose sensitive information when the victim loaded a page containing the malicious SWF content. (CVE-2018-4877, CVE-2018-4878) last seen 2020-06-01 modified 2020-06-02 plugin id 106671 published 2018-02-08 reporter This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/106671 title RHEL 6 : flash-plugin (RHSA-2018:0285) (Underminer) code # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from Red Hat Security Advisory RHSA-2018:0285. The text # itself is copyright (C) Red Hat, Inc. # include("compat.inc"); if (description) { script_id(106671); script_version("3.14"); script_cvs_date("Date: 2019/10/24 15:35:44"); script_cve_id("CVE-2018-4877", "CVE-2018-4878"); script_xref(name:"RHSA", value:"2018:0285"); script_name(english:"RHEL 6 : flash-plugin (RHSA-2018:0285) (Underminer)"); script_summary(english:"Checks the rpm output for the updated package"); script_set_attribute( attribute:"synopsis", value:"The remote Red Hat host is missing a security update." ); script_set_attribute( attribute:"description", value: "An update for flash-plugin is now available for Red Hat Enterprise Linux 6 Supplementary. Red Hat Product Security has rated this update as having a security impact of Critical. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. The flash-plugin package contains a Mozilla Firefox compatible Adobe Flash Player web browser plug-in. This update upgrades Flash Player to version 28.0.0.161. Security Fix(es) : * This update fixes multiple vulnerabilities in Adobe Flash Player. These vulnerabilities, detailed in the Adobe Security Bulletin listed in the References section, could allow an attacker to create a specially crafted SWF file that would cause flash-plugin to crash, execute arbitrary code, or disclose sensitive information when the victim loaded a page containing the malicious SWF content. (CVE-2018-4877, CVE-2018-4878)" ); script_set_attribute( attribute:"see_also", value:"https://helpx.adobe.com/security/products/flash-player/apsb18-03.html" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/errata/RHSA-2018:0285" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2018-4877" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2018-4878" ); script_set_attribute( attribute:"solution", value:"Update the affected flash-plugin package." ); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:H/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:H/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploited_by_malware", value:"true"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:flash-plugin"); script_set_attribute(attribute:"cpe", value:"cpe:/o:redhat:enterprise_linux:6"); script_set_attribute(attribute:"vuln_publication_date", value:"2018/02/06"); script_set_attribute(attribute:"patch_publication_date", value:"2018/02/07"); script_set_attribute(attribute:"plugin_publication_date", value:"2018/02/08"); script_set_attribute(attribute:"in_the_news", value:"true"); script_set_attribute(attribute:"generated_plugin", value:"current"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"Red Hat Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/RedHat/release", "Host/RedHat/rpm-list", "Host/cpu"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("misc_func.inc"); include("rpm.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); release = get_kb_item("Host/RedHat/release"); if (isnull(release) || "Red Hat" >!< release) audit(AUDIT_OS_NOT, "Red Hat"); os_ver = pregmatch(pattern: "Red Hat Enterprise Linux.*release ([0-9]+(\.[0-9]+)?)", string:release); if (isnull(os_ver)) audit(AUDIT_UNKNOWN_APP_VER, "Red Hat"); os_ver = os_ver[1]; if (! preg(pattern:"^6([^0-9]|$)", string:os_ver)) audit(AUDIT_OS_NOT, "Red Hat 6.x", "Red Hat " + os_ver); if (!get_kb_item("Host/RedHat/rpm-list")) audit(AUDIT_PACKAGE_LIST_MISSING); cpu = get_kb_item("Host/cpu"); if (isnull(cpu)) audit(AUDIT_UNKNOWN_ARCH); if ("x86_64" >!< cpu && cpu !~ "^i[3-6]86$" && "s390" >!< cpu) audit(AUDIT_LOCAL_CHECKS_NOT_IMPLEMENTED, "Red Hat", cpu); yum_updateinfo = get_kb_item("Host/RedHat/yum-updateinfo"); if (!empty_or_null(yum_updateinfo)) { rhsa = "RHSA-2018:0285"; yum_report = redhat_generate_yum_updateinfo_report(rhsa:rhsa); if (!empty_or_null(yum_report)) { security_report_v4( port : 0, severity : SECURITY_HOLE, extra : yum_report ); exit(0); } else { audit_message = "affected by Red Hat security advisory " + rhsa; audit(AUDIT_OS_NOT, audit_message); } } else { flag = 0; if (rpm_check(release:"RHEL6", reference:"flash-plugin-28.0.0.161-1.el6_9")) flag++; if (flag) { flash_plugin_caveat = '\n' + 'NOTE: This vulnerability check only applies to RedHat released\n' + 'versions of the flash-plugin package. This check does not apply to\n' + 'Adobe released versions of the flash-plugin package, which are\n' + 'versioned similarly and cause collisions in detection.\n\n' + 'If you are certain you are running the Adobe released package of\n' + 'flash-plugin and are running a version of it equal or higher to the\n' + 'RedHat version listed above then you can consider this a false\n' + 'positive.\n'; security_report_v4( port : 0, severity : SECURITY_HOLE, extra : rpm_report_get() + redhat_report_package_caveat() + flash_plugin_caveat ); exit(0); } else { tested = pkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "flash-plugin"); } }NASL family FreeBSD Local Security Checks NASL id FREEBSD_PKG_756A86310B8411E8A9866451062F0F7A.NASL description Adobe reports : - This update resolves use-after-free vulnerabilities that could lead to remote code execution (CVE-2018-4877, CVE-2018-4878). last seen 2020-06-01 modified 2020-06-02 plugin id 106649 published 2018-02-07 reporter This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/106649 title FreeBSD : Flash Player -- multiple vulnerabilities (756a8631-0b84-11e8-a986-6451062f0f7a) (Underminer) code # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from the FreeBSD VuXML database : # # Copyright 2003-2018 Jacques Vidrine and contributors # # Redistribution and use in source (VuXML) and 'compiled' forms (SGML, # HTML, PDF, PostScript, RTF and so forth) with or without modification, # are permitted provided that the following conditions are met: # 1. Redistributions of source code (VuXML) must retain the above # copyright notice, this list of conditions and the following # disclaimer as the first lines of this file unmodified. # 2. Redistributions in compiled form (transformed to other DTDs, # published online in any format, converted to PDF, PostScript, # RTF and other formats) must reproduce the above copyright # notice, this list of conditions and the following disclaimer # in the documentation and/or other materials provided with the # distribution. # # THIS DOCUMENTATION IS PROVIDED BY THE AUTHOR AND CONTRIBUTORS "AS IS" # AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, # THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR # PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE AUTHOR OR CONTRIBUTORS # BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, # OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT # OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR # BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, # WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE # OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS DOCUMENTATION, # EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE. # include("compat.inc"); if (description) { script_id(106649); script_version("3.9"); script_cvs_date("Date: 2019/04/05 23:25:06"); script_cve_id("CVE-2018-4877", "CVE-2018-4878"); script_name(english:"FreeBSD : Flash Player -- multiple vulnerabilities (756a8631-0b84-11e8-a986-6451062f0f7a) (Underminer)"); script_summary(english:"Checks for updated package in pkg_info output"); script_set_attribute( attribute:"synopsis", value:"The remote FreeBSD host is missing a security-related update." ); script_set_attribute( attribute:"description", value: "Adobe reports : - This update resolves use-after-free vulnerabilities that could lead to remote code execution (CVE-2018-4877, CVE-2018-4878)." ); script_set_attribute( attribute:"see_also", value:"https://helpx.adobe.com/security/products/flash-player/apsa18-01.html" ); script_set_attribute( attribute:"see_also", value:"https://helpx.adobe.com/security/products/flash-player/apsb18-03.html" ); # https://vuxml.freebsd.org/freebsd/756a8631-0b84-11e8-a986-6451062f0f7a.html script_set_attribute( attribute:"see_also", value:"http://www.nessus.org/u?20175c41" ); script_set_attribute(attribute:"solution", value:"Update the affected package."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:H/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:H/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploited_by_malware", value:"true"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:freebsd:freebsd:linux-flashplayer"); script_set_attribute(attribute:"cpe", value:"cpe:/o:freebsd:freebsd"); script_set_attribute(attribute:"vuln_publication_date", value:"2018/01/31"); script_set_attribute(attribute:"patch_publication_date", value:"2018/02/06"); script_set_attribute(attribute:"in_the_news", value:"true"); script_set_attribute(attribute:"plugin_publication_date", value:"2018/02/07"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"FreeBSD Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/FreeBSD/release", "Host/FreeBSD/pkg_info"); exit(0); } include("audit.inc"); include("freebsd_package.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); if (!get_kb_item("Host/FreeBSD/release")) audit(AUDIT_OS_NOT, "FreeBSD"); if (!get_kb_item("Host/FreeBSD/pkg_info")) audit(AUDIT_PACKAGE_LIST_MISSING); flag = 0; if (pkg_test(save_report:TRUE, pkg:"linux-flashplayer<28.0.0.161")) flag++; if (flag) { if (report_verbosity > 0) security_hole(port:0, extra:pkg_report_get()); else security_hole(0); exit(0); } else audit(AUDIT_HOST_NOT, "affected");NASL family MacOS X Local Security Checks NASL id MACOSX_FLASH_PLAYER_APSA18-01.NASL description The version of Adobe Flash Player installed on the remote macOS or Mac OS X host is equal or prior to version 28.0.0.137. It is, therefore, affected by a remote code execution vulnerability. last seen 2020-06-01 modified 2020-06-02 plugin id 106607 published 2018-02-05 reporter This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/106607 title Adobe Flash Player for Mac <= 28.0.0.137 Use-after-free Remote Code Execution (APSA18-01) (APSB18-03) code # # (C) Tenable Network Security, Inc. # include("compat.inc"); if (description) { script_id(106607); script_version("1.9"); script_cvs_date("Date: 2019/11/08"); script_cve_id("CVE-2018-4877", "CVE-2018-4878"); script_bugtraq_id(102893, 102930); script_name(english:"Adobe Flash Player for Mac <= 28.0.0.137 Use-after-free Remote Code Execution (APSA18-01) (APSB18-03)"); script_summary(english:"Checks the version of Flash Player."); script_set_attribute(attribute:"synopsis", value: "The remote macOS or Mac OSX host has a browser plugin installed that is affected by a remote code execution vulnerability."); script_set_attribute(attribute:"description", value: "The version of Adobe Flash Player installed on the remote macOS or Mac OS X host is equal or prior to version 28.0.0.137. It is, therefore, affected by a remote code execution vulnerability."); script_set_attribute(attribute:"see_also", value:"https://helpx.adobe.com/security/products/flash-player/apsa18-01.html"); script_set_attribute(attribute:"see_also", value:"https://helpx.adobe.com/security/products/flash-player/apsb18-03.html"); script_set_attribute(attribute:"solution", value: "Upgrade to Adobe Flash Player version 28.0.0.161 or later."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:H/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:H/RL:O/RC:C"); script_set_attribute(attribute:"cvss_score_source", value:"CVE-2018-4877"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploited_by_malware", value:"true"); script_set_attribute(attribute:"vuln_publication_date", value:"2018/02/01"); script_set_attribute(attribute:"patch_publication_date", value:"2018/02/01"); script_set_attribute(attribute:"plugin_publication_date", value:"2018/02/05"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"cpe:/a:adobe:flash_player"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_family(english:"MacOS X Local Security Checks"); script_copyright(english:"This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_dependencies("macosx_flash_player_installed.nasl"); script_require_keys("MacOSX/Flash_Player/Version"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("misc_func.inc"); version = get_kb_item_or_exit("MacOSX/Flash_Player/Version"); path = get_kb_item_or_exit("MacOSX/Flash_Player/Path"); cutoff_version = "28.0.0.137"; fix = "28.0.0.161"; # We're checking for versions less than or equal to the cutoff! if (ver_compare(ver:version, fix:cutoff_version, strict:FALSE) <= 0) { report = '\n Path : ' + path + '\n Installed version : ' + version + '\n Fixed version : ' + fix + '\n'; security_report_v4(severity:SECURITY_HOLE, port:0, extra:report); } else audit(AUDIT_INST_PATH_NOT_VULN, "Flash Player for Mac", version, path);NASL family Windows : Microsoft Bulletins NASL id SMB_NT_MS18_FEB_4074595.NASL description The remote Windows host is missing security update KB4074595. It is, therefore, affected by multiple remote code execution vulnerabilities in Adobe Flash Player. last seen 2020-06-01 modified 2020-06-02 plugin id 106655 published 2018-02-07 reporter This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/106655 title KB4074595: Security update for Adobe Flash Player (February 2018) code # # (C) Tenable Network Security, Inc. # include("compat.inc"); if (description) { script_id(106655); script_version("1.7"); script_cvs_date("Date: 2019/11/08"); script_cve_id("CVE-2018-4877", "CVE-2018-4878"); script_bugtraq_id(102893, 102930); script_xref(name:"MSKB", value:"4074595"); script_xref(name:"MSFT", value:"MS18-4074595"); script_name(english:"KB4074595: Security update for Adobe Flash Player (February 2018)"); script_summary(english:"Checks the version of the ActiveX control."); script_set_attribute(attribute:"synopsis", value: "The remote Windows host has a browser plugin installed that is affected by multiple vulnerabilities."); script_set_attribute(attribute:"description", value: "The remote Windows host is missing security update KB4074595. It is, therefore, affected by multiple remote code execution vulnerabilities in Adobe Flash Player."); script_set_attribute(attribute:"see_also", value:"https://helpx.adobe.com/security/products/flash-player/apsa18-01.html"); script_set_attribute(attribute:"see_also", value:"https://helpx.adobe.com/security/products/flash-player/apsb18-03.html"); # https://support.microsoft.com/en-us/help/4074595/security-update-for-adobe-flash-player script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?9e60077b"); script_set_attribute(attribute:"solution", value: "Microsoft has released KB4074595 to address this issue."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:H/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:H/RL:O/RC:C"); script_set_attribute(attribute:"cvss_score_source", value:"CVE-2018-4877"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploited_by_malware", value:"true"); script_set_attribute(attribute:"vuln_publication_date", value:"2018/02/01"); script_set_attribute(attribute:"patch_publication_date", value:"2018/02/06"); script_set_attribute(attribute:"plugin_publication_date", value:"2018/02/07"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"cpe:/a:adobe:flash_player"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_family(english:"Windows : Microsoft Bulletins"); script_copyright(english:"This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_dependencies("smb_hotfixes.nasl", "ms_bulletin_checks_possible.nasl"); script_require_keys("SMB/MS_Bulletin_Checks/Possible"); script_require_ports(139, 445, "Host/patch_management_checks"); exit(0); } include("audit.inc"); include("smb_func.inc"); include("smb_hotfixes.inc"); include("smb_hotfixes_fcheck.inc"); include("smb_activex_func.inc"); get_kb_item_or_exit("SMB/MS_Bulletin_Checks/Possible"); bulletin = "MS18-02"; kbs = make_list('4074595'); if (get_kb_item("Host/patch_management_checks")) hotfix_check_3rd_party(bulletin:bulletin, kbs:kbs, severity:SECURITY_HOLE); get_kb_item_or_exit("SMB/Registry/Enumerated"); get_kb_item_or_exit("SMB/WindowsVersion", exit_code:1); if (hotfix_check_sp_range(win8:'0', win81:'0', win10:'0') <= 0) audit(AUDIT_OS_SP_NOT_VULN); if (hotfix_check_server_core() == 1) audit(AUDIT_WIN_SERVER_CORE); productname = get_kb_item_or_exit("SMB/ProductName", exit_code:1); if ("Windows 8" >< productname && "Windows 8.1" >!< productname) audit(AUDIT_OS_SP_NOT_VULN); if (activex_init() != ACX_OK) audit(AUDIT_FN_FAIL, "activex_init"); # Adobe Flash Player CLSID clsid = '{D27CDB6E-AE6D-11cf-96B8-444553540000}'; file = activex_get_filename(clsid:clsid); if (isnull(file)) { activex_end(); audit(AUDIT_FN_FAIL, "activex_get_filename", "NULL"); } if (!file) { activex_end(); audit(AUDIT_ACTIVEX_NOT_FOUND, clsid); } # Get its version. version = activex_get_fileversion(clsid:clsid); if (!version) { activex_end(); audit(AUDIT_VER_FAIL, file); } info = ''; iver = split(version, sep:'.', keep:FALSE); for (i=0; i<max_index(iver); i++) iver[i] = int(iver[i]); iver = join(iver, sep:"."); # all <= 28.0.0.137 fix = FALSE; if(ver_compare(ver:iver, fix:"28.0.0.137", strict:FALSE) <= 0) fix = "28.0.0.161"; if ( (report_paranoia > 1 || activex_get_killbit(clsid:clsid) == 0) && fix ) { info = '\n Path : ' + file + '\n Installed version : ' + version + '\n Fixed version : ' + fix + '\n'; } port = kb_smb_transport(); if (info != '') { if (report_paranoia > 1) { report = info + '\n' + 'Note, though, that Nessus did not check whether the kill bit was\n' + "set for the control's CLSID because of the Report Paranoia setting" + '\n' + 'in effect when this scan was run.\n'; } else { report = info + '\n' + 'Moreover, its kill bit is not set so it is accessible via Internet\n' + 'Explorer.\n'; } replace_kb_item(name:"SMB/Missing/"+bulletin, value:TRUE); hotfix_add_report(bulletin:'MS18-02', kb:'4074595', report); security_report_v4(severity:SECURITY_HOLE, port:port, extra:hotfix_get_report()); } else audit(AUDIT_HOST_NOT, 'affected');NASL family Windows NASL id FLASH_PLAYER_APSA18-01.NASL description The version of Adobe Flash Player installed on the remote Windows host is equal or prior to version 28.0.0.137. It is, therefore, affected by a use-after-free vulnerability that allows arbitrary code execution. last seen 2020-06-01 modified 2020-06-02 plugin id 106606 published 2018-02-05 reporter This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/106606 title Adobe Flash Player <= 28.0.0.137 Use-after-free Remote Code Execution (APSA18-01) (APSB18-03) code # # (C) Tenable Network Security, Inc. # include("compat.inc"); if (description) { script_id(106606); script_version("1.9"); script_cvs_date("Date: 2019/11/08"); script_cve_id("CVE-2018-4877", "CVE-2018-4878"); script_bugtraq_id(102893, 102930); script_name(english:"Adobe Flash Player <= 28.0.0.137 Use-after-free Remote Code Execution (APSA18-01) (APSB18-03)"); script_summary(english:"Checks the version of Flash Player."); script_set_attribute(attribute:"synopsis", value: "The remote Windows host has a browser plugin installed that is affected by a remote code execution vulnerability."); script_set_attribute(attribute:"description", value: "The version of Adobe Flash Player installed on the remote Windows host is equal or prior to version 28.0.0.137. It is, therefore, affected by a use-after-free vulnerability that allows arbitrary code execution."); script_set_attribute(attribute:"see_also", value:"https://helpx.adobe.com/security/products/flash-player/apsa18-01.html"); script_set_attribute(attribute:"see_also", value:"https://helpx.adobe.com/security/products/flash-player/apsb18-03.html"); # http://helpx.adobe.com/flash-player/kb/archived-flash-player-versions.html script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?0cb17c10"); script_set_attribute(attribute:"solution", value: "Upgrade to Adobe Flash Player version 28.0.0.161 or later."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:H/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:H/RL:O/RC:C"); script_set_attribute(attribute:"cvss_score_source", value:"CVE-2018-4877"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploited_by_malware", value:"true"); script_set_attribute(attribute:"vuln_publication_date", value:"2018/02/01"); script_set_attribute(attribute:"patch_publication_date", value:"2018/02/01"); script_set_attribute(attribute:"plugin_publication_date", value:"2018/02/05"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"cpe:/a:adobe:flash_player"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_family(english:"Windows"); script_copyright(english:"This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_dependencies("flash_player_installed.nasl"); script_require_keys("SMB/Flash_Player/installed"); exit(0); } include("global_settings.inc"); include("misc_func.inc"); get_kb_item_or_exit("SMB/Flash_Player/installed"); # Identify vulnerable versions. info = ""; variants = make_list( "Plugin", "ActiveX", "Chrome", "Chrome_Pepper" ); cutoff_version = "28.0.0.137"; fix = "28.0.0.161"; # we're checking for versions less than *or equal to* the cutoff! foreach variant (variants) { vers = get_kb_list("SMB/Flash_Player/"+variant+"/Version/*"); files = get_kb_list("SMB/Flash_Player/"+variant+"/File/*"); if (isnull(vers) || isnull(files)) continue; foreach key (keys(vers)) { ver = vers[key]; if (isnull(ver)) continue; # vuln <= 28.0.0.137 if (ver_compare(ver:ver, fix:cutoff_version, strict:FALSE) <= 0) { num = key - ("SMB/Flash_Player/"+variant+"/Version/"); file = files["SMB/Flash_Player/"+variant+"/File/"+num]; if (variant == "Plugin") { info += '\n Product : Browser plugin (for Firefox / Netscape / Opera)'; } else if (variant == "ActiveX") { info += '\n Product : ActiveX control (for Internet Explorer)'; } else if ("Chrome" >< variant) { info += '\n Product : Browser plugin (for Google Chrome)'; if (variant == "Chrome") fix = "Upgrade to a version of Google Chrome running Flash Player 28.0.0.161"; } info += '\n Path : ' + file + '\n Installed version : ' + ver; if (variant == "Chrome_Pepper") info += '\n Fixed version : '+fix+' (Chrome PepperFlash)'; else if (!isnull(fix)) info += '\n Fixed version : '+fix; info += '\n'; } } } if (info) { port = get_kb_item("SMB/transport"); if (!port) port = 445; if (report_verbosity > 0) security_hole(port:port, extra:info); else security_hole(port); } else { if (thorough_tests) exit(0, 'No vulnerable versions of Adobe Flash Player were found.'); else exit(1, 'Google Chrome\'s built-in Flash Player may not have been detected because the \'Perform thorough tests\' setting was not enabled.'); }
Packetstorm
| data source | https://packetstormsecurity.com/files/download/147041/flashp0c.py.txt |
| id | PACKETSTORM:147041 |
| last seen | 2018-04-05 |
| published | 2018-04-04 |
| reporter | SyFi |
| source | https://packetstormsecurity.com/files/147041/Adobe-Flash-28.0.0.137-Remote-Code-Execution.html |
| title | Adobe Flash 28.0.0.137 Remote Code Execution |
Redhat
| advisories |
| ||||
| rpms | flash-plugin-0:28.0.0.161-1.el6_9 |
Seebug
| bulletinFamily | exploit |
| description | ### EXECUTIVE SUMMARY The 1st of February, Adobe published an advisory concerning a Flash vulnerability (CVE-2018-4878). This vulnerability is a use after free that allows Remote Code Execute through a malformed Flash object. Additionally KISA (Korean CERT) published an [advisory](https://www.krcert.or.kr/data/secNoticeView.do?bulletin_writing_sequence=26998) about a Flash 0-day used in the wild. Talos identified that an attacker exploited this vulnerability with a Flash object embedded in a Microsoft Excel document. By opening the document, the exploit was executed in order to download an additional payload from a compromised website. We identified that the downloaded payload is the well-known Remote Administration Tool named ROKRAT. We already extensively spoke about this RAT on several articles in this blog: [here](http://blog.talosintelligence.com/2018/01/korea-in-crosshairs.html), [here](http://blog.talosintelligence.com/2017/11/ROKRAT-Reloaded.html), [here](http://blog.talosintelligence.com/2017/04/introducing-rokrat.html) and [here](http://blog.talosintelligence.com/2017/02/korean-maldoc.html). It is particularity used with cloud platforms in order to exfiltrate documents and manage infected systems. ### FLASH 0-DAY: CVE-2018-4878 The campaign started by a malicious Microsoft Excel sheet: 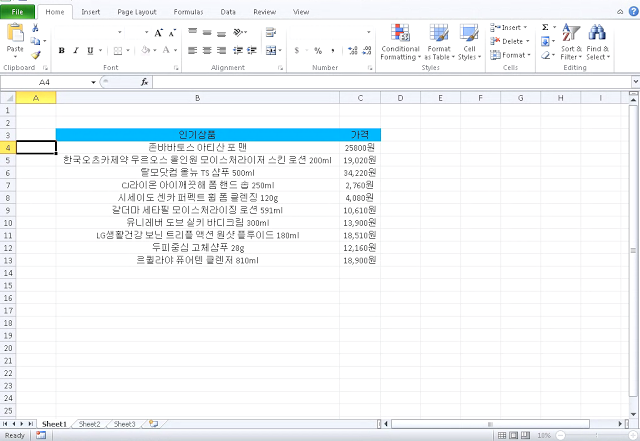 This malicious document contains an ActiveX object. This object is a SWF file (Flash). The CVE-2018-4878 use after free vulnerability is used in order to download an additional payload from a compromised web server. This payload is a shellcode loaded in memory and executed. We identified Flash exploits from November 2017. Here is the exploit workflow: 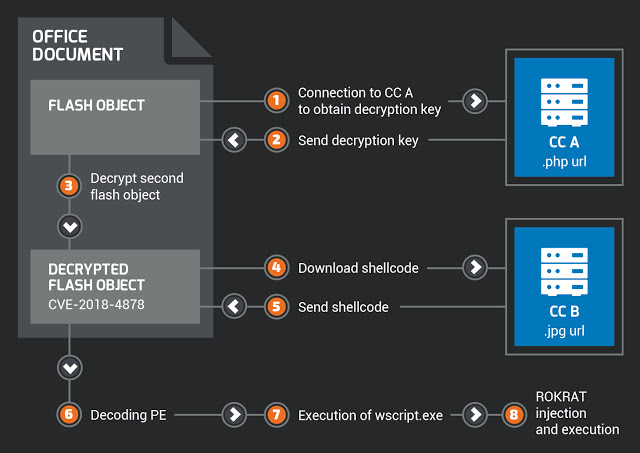 ### CC & ROKRAT PAYLOAD As explained previously, the purpose of the exploit is to download and execute an additional payload on the Internet. Here are some URLs where this additional payload was downloaded: * hxxp://www[.]1588-2040[.]co[.]kr/conf/product_old.jpg * hxxp://www[.]1588-2040[.]co[.]kr/design/m/images/image/image.php * hxxp://www[.]korea-tax[.]info/main/local.php * hxxp://www[.]dylboiler[.]co[.]kr/admincenter/files/board/4/manager.php All these URLs are compromised websites located in South Korea. We identified that several of these URLs hosted a shellcode used to unpack and execute a ROKRAT variant. Here is the PDB of this sample: ``` d:\HighSchool\version 13\2ndBD\T+M\T+M\Result\DocPrint.pdb ``` It's the same PDB that was previously identified during our investigations. The exploit was used to drop ROKRAT on compromised systems. One of the ROKRAT samples identified used a naming reference to Hancom Secure AnySign. It is a reference to a legitimate application developed by Hancom Secure for PKI & authentication mechanisms. It is a software application used to protect user data and is massively used in South Korea. ### CONCLUSION Group 123 have now joined some of the criminal elite with this latest payload of ROKRAT. They have used an Adobe Flash 0-day which was outside of their previous capabilities - they did use exploits in previous campaigns but never a net new exploit as they have done now. This change represents a major shift in Group 123s maturity level, we can now confidentially assess Group 123 has a highly skilled, highly motivated and highly sophisticated group. Whilst Talos do not have any victim information related to this campaign we suspect the victim has been a very specific and high value target. Utilizing a brand new exploit, previously not seen in the wild, displays they were very determined to ensure their attack worked. In January 2018 we produced a write up '[Korea In The Crosshair](http://blog.talosintelligence.com/2018/01/korea-in-crosshairs.html)' detailing the campaigns previously carried out by Group 123. In this write up we explained this would not be the last time we witness attacks from this threat actor and that we would expect them to continue to evolve. Within a few weeks we have witnessed the evolution of Group 123 and we will continue to monitor the threat landscape for this group. ### COVERAGE Additional ways our customers can detect and block this threat are listed below. 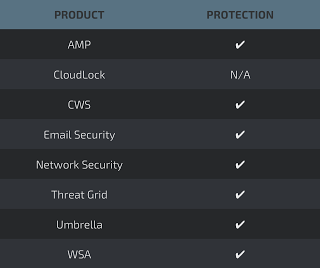 Advanced Malware Protection ([AMP](https://www.cisco.com/c/en/us/products/security/advanced-malware-protection)) is ideally suited to prevent the execution of the malware used by these threat actors. [CWS](https://www.cisco.com/c/en/us/products/security/cloud-web-security/index.html) or [WSA](https://www.cisco.com/c/en/us/products/security/web-security-appliance/index.html) web scanning prevents access to malicious websites and detects malware used in these attacks. [Email Security](https://www.cisco.com/c/en/us/products/security/email-security-appliance/index.html) can block malicious emails sent by threat actors as part of their campaign. Network Security appliances such as [NGFW](https://www.cisco.com/c/en/us/products/security/firewalls/index.html), [NGIPS](https://www.cisco.com/c/en/us/products/security/intrusion-prevention-system-ips/index.html), and [Meraki MX](https://meraki.cisco.com/products/appliances) can detect malicious activity associated with this threat. [AMP Threat Grid](https://www.cisco.com/c/en/us/solutions/enterprise-networks/amp-threat-grid/index.html) helps identify malicious binaries and build protection into all Cisco Security products. [Umbrella](https://umbrella.cisco.com/), our secure internet gateway (SIG), blocks users from connecting to malicious domains, IPs, and URLs, whether users are on or off the corporate network. Open Source Snort Subscriber Rule Set customers can stay up to date by downloading the latest rule pack available for purchase on [Snort.org](https://www.snort.org/products). ### IOCS Flash exploits: fec71b8479f3a416fa58580ae76a8c731c2294c24663c601a1267e0e5c2678a0 3b1395f620e428c5f68c6497a2338da0c4f749feb64e8f12e4c5b1288cc57a1c ROKRAT sample: E1546323dc746ed2f7a5c973dcecc79b014b68bdd8a6230239283b4f775f4bbd URL: hxxp://www[.]1588-2040[.]co[.]kr/conf/product_old.jpg hxxp://www[.]1588-2040[.]co[.]kr/design/m/images/image/image.php hxxp://www[.]korea-tax[.]info/main/local.php hxxp://www[.]dylboiler[.]co[.]kr/admincenter/files/board/4/manager.php |
| id | SSV:97136 |
| last seen | 2018-02-23 |
| modified | 2018-02-23 |
| published | 2018-02-23 |
| reporter | Root |
| source | https://www.seebug.org/vuldb/ssvid-97136 |
| title | Adobe Flash Player Use After Free Remote Code Execution Vulnerability(CVE-2018-4878) |
The Hacker News
| id | THN:3BC4F7FE3170D82B2C8328638552D1D3 |
| last seen | 2018-02-02 |
| modified | 2018-02-02 |
| published | 2018-02-01 |
| reporter | Mohit Kumar |
| source | https://thehackernews.com/2018/02/flash-zero-day-exploit.html |
| title | (Unpatched) Adobe Flash Player Zero-Day Exploit Spotted in the Wild |
Related news
References
- http://blog.talosintelligence.com/2018/02/group-123-goes-wild.html
- http://www.securityfocus.com/bid/102893
- http://www.securitytracker.com/id/1040318
- https://access.redhat.com/errata/RHSA-2018:0285
- https://blog.morphisec.com/flash-exploit-cve-2018-4878-spotted-in-the-wild-massive-malspam-campaign
- https://github.com/InQuest/malware-samples/tree/master/CVE-2018-4878-Adobe-Flash-DRM-UAF-0day
- https://github.com/vysec/CVE-2018-4878
- https://helpx.adobe.com/security/products/flash-player/apsb18-03.html
- https://securingtomorrow.mcafee.com/mcafee-labs/hackers-bypassed-adobe-flash-protection-mechanism/
- https://threatpost.com/adobe-flash-player-zero-day-spotted-in-the-wild/129742/
- https://www.darkreading.com/threat-intelligence/adobe-flash-vulnerability-reappears-in-malicious-word-files/d/d-id/1331139
- https://www.exploit-db.com/exploits/44412/
- https://www.fireeye.com/blog/threat-research/2018/02/attacks-leveraging-adobe-zero-day.html
- https://www.trendmicro.com/vinfo/us/security/news/vulnerabilities-and-exploits/north-korean-hackers-allegedly-exploit-adobe-flash-player-vulnerability-cve-2018-4878-against-south-korean-targets
- http://blog.talosintelligence.com/2018/02/group-123-goes-wild.html
- https://www.trendmicro.com/vinfo/us/security/news/vulnerabilities-and-exploits/north-korean-hackers-allegedly-exploit-adobe-flash-player-vulnerability-cve-2018-4878-against-south-korean-targets
- https://www.fireeye.com/blog/threat-research/2018/02/attacks-leveraging-adobe-zero-day.html
- https://www.exploit-db.com/exploits/44412/
- https://www.darkreading.com/threat-intelligence/adobe-flash-vulnerability-reappears-in-malicious-word-files/d/d-id/1331139
- https://threatpost.com/adobe-flash-player-zero-day-spotted-in-the-wild/129742/
- https://securingtomorrow.mcafee.com/mcafee-labs/hackers-bypassed-adobe-flash-protection-mechanism/
- https://helpx.adobe.com/security/products/flash-player/apsb18-03.html
- https://github.com/vysec/CVE-2018-4878
- https://github.com/InQuest/malware-samples/tree/master/CVE-2018-4878-Adobe-Flash-DRM-UAF-0day
- https://blog.morphisec.com/flash-exploit-cve-2018-4878-spotted-in-the-wild-massive-malspam-campaign
- https://access.redhat.com/errata/RHSA-2018:0285
- http://www.securitytracker.com/id/1040318
- http://www.securityfocus.com/bid/102893