Vulnerabilities > CVE-2018-0101 - Double Free vulnerability in Cisco Adaptive Security Appliance Software
Summary
A vulnerability in the Secure Sockets Layer (SSL) VPN functionality of the Cisco Adaptive Security Appliance (ASA) Software could allow an unauthenticated, remote attacker to cause a reload of the affected system or to remotely execute code. The vulnerability is due to an attempt to double free a region of memory when the webvpn feature is enabled on the Cisco ASA device. An attacker could exploit this vulnerability by sending multiple, crafted XML packets to a webvpn-configured interface on the affected system. An exploit could allow the attacker to execute arbitrary code and obtain full control of the system, or cause a reload of the affected device. This vulnerability affects Cisco ASA Software that is running on the following Cisco products: 3000 Series Industrial Security Appliance (ISA), ASA 5500 Series Adaptive Security Appliances, ASA 5500-X Series Next-Generation Firewalls, ASA Services Module for Cisco Catalyst 6500 Series Switches and Cisco 7600 Series Routers, ASA 1000V Cloud Firewall, Adaptive Security Virtual Appliance (ASAv), Firepower 2100 Series Security Appliance, Firepower 4110 Security Appliance, Firepower 9300 ASA Security Module, Firepower Threat Defense Software (FTD). Cisco Bug IDs: CSCvg35618.
Vulnerable Configurations
Common Weakness Enumeration (CWE)
Exploit-Db
| description | Cisco ASA - Crash PoC. CVE-2018-0101. Dos exploit for Hardware platform |
| file | exploits/hardware/dos/43986.py |
| id | EDB-ID:43986 |
| last seen | 2018-02-07 |
| modified | 2018-02-07 |
| platform | hardware |
| port | |
| published | 2018-02-07 |
| reporter | Exploit-DB |
| source | https://www.exploit-db.com/download/43986/ |
| title | Cisco ASA - Crash PoC |
| type | dos |
Nessus
NASL family CISCO NASL id CISCO-SA-20180129-ASA1.NASL description According to its self-reported version the Cisco Adaptive Security Appliance (ASA) software running on the remote device is affected by a denial of service vulnerability which could allow an unauthenticated, remote attacker to cause a reload of the affected system or to remotely execute code. last seen 2020-04-30 modified 2018-01-30 plugin id 106484 published 2018-01-30 reporter This script is Copyright (C) 2018-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/106484 title Cisco ASA Remote Code Execution and Denial of Service Vulnerability (cisco-sa-20180129-asa1) code #TRUSTED 13bb29d3f8b98864fffa7f0696794654b3a579b249de03535ee427d8569c3ef56ace70bb73d04f0d18643f72c45794a2b4cf547243663f229be17d1d77b8ea4d3f651d92d8b2324fe7826e8b6113d370ead744d25884187b1a372fbb7aebc330af5bf7835f1c4ba6891afe578ed00c0e74b5b7dd90290295da4c0dba568fd292268975dbf720a618f193958e9628964e5cdcc826fdae4840bcf68e5ed18c37e400919428df4ff6d1d9d6d8b4bf9ec9222e2d7d90bfb1e0df1a9d5afad6d779f8639bc78d25d8446cd6a0d43edd6a15b2af728b8dad7dbcee933c2b2507d81c0e861da36ad43d5146670d6f9b9520aaaead36bc426bd70c7afb3bd0f1cccb285814fec24400a772b98100ee97052e281bdbcbf7be49a12d5770256e8d49950e2eee0d9cafbda47bc83e5d878d8e766f89464966fe1be4f1a5596cbd6001413ab2c31dc9dda46b9e3448b0f3dc362d8c48805b605aad37245590d87d2d654dcda3d0b8d8dbe376cc52214ae353aabfd707df996efd183f2213152816a5ee8643551eaf4d57c5680bc71802b542f97716c465515837e6df00ad30ac47bbb3c53686ee750eb9af25d68b65d9123d332043cd58e1f99afbe4bfa05bdcfb18dbf01c72965b90c5f066ff86007550748df6643327a8808d1a7f56220a88269d41a4f12dbe03a7203b32f27120c5383c66bc74ef2530af4a1a9275cb807f81316f91d643 # # (C) Tenable Network Security, Inc. # include("compat.inc"); if (description) { script_id(106484); script_version("1.21"); script_set_attribute(attribute:"plugin_modification_date", value:"2020/04/27"); script_cve_id("CVE-2018-0101"); script_xref(name:"CISCO-BUG-ID", value:"CSCvg35618"); script_xref(name:"CISCO-BUG-ID", value:"CSCvh79732"); script_xref(name:"CISCO-BUG-ID", value:"CSCvh81737"); script_xref(name:"CISCO-BUG-ID", value:"CSCvh81870"); script_xref(name:"CISCO-SA", value:"cisco-sa-20180129-asa1"); script_xref(name:"IAVA", value:"0001-A-0011"); script_name(english:"Cisco ASA Remote Code Execution and Denial of Service Vulnerability (cisco-sa-20180129-asa1)"); script_summary(english:"Checks the ASA version."); script_set_attribute(attribute:"synopsis", value: "The remote device is missing a vendor-supplied security patch."); script_set_attribute(attribute:"description", value: "According to its self-reported version the Cisco Adaptive Security Appliance (ASA) software running on the remote device is affected by a denial of service vulnerability which could allow an unauthenticated, remote attacker to cause a reload of the affected system or to remotely execute code."); # https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180129-asa1 script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?118d2746"); script_set_attribute(attribute:"solution", value: "Upgrade to the relevant fixed version referenced in Cisco security advisory cisco-sa-20180129-asa1."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:POC/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:P/RL:O/RC:C"); script_set_attribute(attribute:"cvss_score_source", value:"CVE-2018-0101"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"vuln_publication_date", value:"2018/01/29"); script_set_attribute(attribute:"patch_publication_date", value:"2018/01/29"); script_set_attribute(attribute:"plugin_publication_date", value:"2018/01/30"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"cpe:/a:cisco:adaptive_security_appliance_software"); script_set_attribute(attribute:"potential_vulnerability", value:"true"); script_set_attribute(attribute:"stig_severity", value:"I"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_family(english:"CISCO"); script_copyright(english:"This script is Copyright (C) 2018-2020 and is owned by Tenable, Inc. or an Affiliate thereof."); script_dependencies("ssh_get_info.nasl", "os_fingerprint.nasl"); script_require_keys("Host/Cisco/ASA", "Host/Cisco/ASA/model", "Settings/ParanoidReport"); exit(0); } include("audit.inc"); include("cisco_workarounds.inc"); include("ccf.inc"); product_info = cisco::get_product_info(name:"Cisco Adaptive Security Appliance (ASA) Software"); if (report_paranoia < 2) audit(AUDIT_PARANOID); if ( product_info.model !~ '^1000V' && # 1000V product_info.model !~ '^55[0-9][0-9]($|[^0-9])' && # 5500 & 5500-X product_info.model !~ '^65[0-9][0-9]($|[^0-9])' && # 6500 product_info.model !~ '^76[0-9][0-9]($|[^0-9])' && # 7600 product_info.model !~ '^93[0-9][0-9]($|[^0-9])' && # Firepower 9300 ASA product_info.model !~ '^411[0-9]($|[^0-9])' && # Firepower 4110 SA product_info.model !~ '^41[245][0-9]($|[^0-9])' && # Firepower 4120/4140/4150 SA product_info.model !~ '^21[0-9][0-9]($|[^0-9])' && # Firepower 2100 SSA product_info.model !~ '^30[0-9][0-9]($|[^0-9])' && # ISA 3000 product_info.model != 'v' # ASAv ) audit(AUDIT_HOST_NOT, "an affected Cisco ASA product"); vuln_ranges = [ {'min_ver' : '0.0', 'fix_ver' : '9.1(7.23)'}, {'min_ver' : '9.2', 'fix_ver' : '9.2(4.27)'}, {'min_ver' : '9.3', 'fix_ver' : '9.4(4.16)'}, {'min_ver' : '9.5', 'fix_ver' : '9.6(4.3)'}, {'min_ver' : '9.7', 'fix_ver' : '9.7(1.21)'}, {'min_ver' : '9.8', 'fix_ver' : '9.8(2.20)'}, {'min_ver' : '9.9', 'fix_ver' : '9.9(1.2)'} ]; workarounds = make_list( CISCO_WORKAROUNDS['ASA_HTTP_Server'], CISCO_WORKAROUNDS['IKEv2_enabled'], CISCO_WORKAROUNDS['aaa_auth_listener'], CISCO_WORKAROUNDS['CA_Server'], CISCO_WORKAROUNDS['mdm_proxy'], CISCO_WORKAROUNDS['ssl_vpn'], CISCO_WORKAROUNDS['proxy_bypass'], CISCO_WORKAROUNDS['mus'], CISCO_WORKAROUNDS['rest_api'] ); workaround_params = { "check_anyconnect" : 1, "check_no_shutdown" : 1 }; reporting = make_array( 'port' , 0, 'severity' , SECURITY_HOLE, 'version' , product_info['version'], 'bug_id' , "CSCvg35618, CSCvh79732, CSCvh81737, and CSCvh81870" ); cisco::check_and_report(product_info:product_info, workarounds:workarounds, workaround_params:workaround_params, reporting:reporting, vuln_ranges:vuln_ranges);NASL family CISCO NASL id CISCO_ASA_CVE-2018-0101_DOS.NASL description The Cisco Adaptive Security Appliance (ASA) software running on the remote device is affected by a remote code execution vulnerability due to an issue with allocating and freeing memory when processing a malicious XML payload. An unauthenticated, remote attacker can exploit the issue to cause a reload of the affected system or to remotely execute code. last seen 2020-06-01 modified 2020-06-02 plugin id 107004 published 2018-02-26 reporter This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/107004 title Cisco ASA Remote Code Execution and Denial of Service Vulnerability (cisco-sa-20180129-asa1) (destructive check) NASL family CISCO NASL id CISCO-SA-20180129-ASA1-FTD.NASL description According to its version, the Cisco Firepower Threat Defense (FTD) software installed on the remote host is affected by a vulnerability in the XML parser that can allow a remote, unauthenticated attacker to execute arbitrary code. last seen 2020-06-01 modified 2020-06-02 plugin id 106630 published 2018-02-06 reporter This script is Copyright (C) 2018-2019 Tenable Network Security, Inc. source https://www.tenable.com/plugins/nessus/106630 title Cisco Firepower Threat Defense (FTD) Adaptive Security Appliance Remote Code Execution and Denial of Service Vulnerability (cisco-sa-20180129-asa1)
Packetstorm
| data source | https://packetstormsecurity.com/files/download/146296/ciscoasa-dos.txt |
| id | PACKETSTORM:146296 |
| last seen | 2018-02-08 |
| published | 2018-02-07 |
| reporter | Sean Dillon |
| source | https://packetstormsecurity.com/files/146296/Cisco-ASA-Crash-Proof-Of-Concept.html |
| title | Cisco ASA Crash Proof Of Concept |
Seebug
| bulletinFamily | exploit |
| description | ### Summary A vulnerability in the Secure Sockets Layer (SSL) VPN functionality of the Cisco Adaptive Security Appliance (ASA) Software could allow an unauthenticated, remote attacker to cause a reload of the affected system or to remotely execute code. The vulnerability is due to an attempt to double free a region of memory when the webvpn feature is enabled on the Cisco ASA device. An attacker could exploit this vulnerability by sending multiple, crafted XML packets to a webvpn-configured interface on the affected system. An exploit could allow the attacker to execute arbitrary code and obtain full control of the system, or cause a reload of the affected device. Cisco has released software updates that address this vulnerability. There are no workarounds that address this vulnerability. This advisory is available at the following link: https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180129-asa1 ### Affected Products #### Vulnerable Products This vulnerability affects Cisco ASA Software that is running on the following Cisco products: * 3000 Series Industrial Security Appliance (ISA) * ASA 5500 Series Adaptive Security Appliances * ASA 5500-X Series Next-Generation Firewalls * ASA Services Module for Cisco Catalyst 6500 Series Switches and Cisco 7600 Series Routers * ASA 1000V Cloud Firewall * Adaptive Security Virtual Appliance (ASAv) * Firepower 2100 Series Security Appliance * Firepower 4110 Security Appliance * Firepower 9300 ASA Security Module * Firepower Threat Defense Software (FTD) ### ASA Software This vulnerability affects devices that are running a vulnerable release of Cisco ASA Software where the webvpn feature is enabled. In addition to webvpn being globally configured there must be one enabled interface via the enable <if_name> in the configuration. To determine whether webvpn is enabled for at least one interface, administrators can use the show running-config webvpn command at the CLI and verify that the command returns at least one enable <if_name> line. The following example shows the output of the command for a device that is running Cisco ASA Software and has WebVPN enabled on the Outside interface. ``` ciscoasa# show running-config webvpn webvpn enable Outside ``` The customer can also use the show asp table socket command and look for an SSL and a DTLS listen socket on TCP port 443. An SSL and DTLS listen socket on TCP port 443 must be present in order for the vulnerability to be exploited. The following example shows the output of the command for a device that has SSL and DTLS listen sockets on TCP port 443: ``` ciscoasa# show asp table socket Protocol Socket State Local Address Foreign Address SSL 00005898 LISTEN 10.48.66.202:8443 0.0.0.0:* TCP 00009718 LISTEN 10.48.66.202:23 0.0.0.0:* TCP 0000e708 LISTEN 10.48.66.202:22 0.0.0.0:* SSL 00011cc8 LISTEN 10.48.66.202:443 0.0.0.0:* DTLS 000172f8 LISTEN 10.48.66.202:443 0.0.0.0:* ``` ### Determining the ASA Running Software Release To determine whether a vulnerable version of Cisco ASA Software is running on a device, administrators can use the show version command in the CLI. The following example shows the output of the command for a device that is running Cisco ASA Software Release 9.2(1): ``` ciscoasa# show version | include Version Cisco Adaptive Security Appliance Software Version 9.2(1) Device Manager Version 7.4(1) ``` Customers who use Cisco Adaptive Security Device Manager (ASDM) to manage devices can locate the software release in the table that appears in the login window or the upper-left corner of the Cisco ASDM window. ### FTD Software This vulnerability applies to the FTD 6.2.2 software release, which was the first to support the Remote Access VPN feature. This release contains both Firepower and ASA code. Review Firepower Threat Defense Devices in the Cisco Firepower Compatibility Guide for additional information. ### Determining the Running FTD Software Release Administrators can use the show version command at the CLI to determine the FTD release. In this example, the device is running software release 6.2.2. ``` > show version ---------------------[ ftd ]--------------------- Model : Cisco ASA5525-X Threat Defense (75) Version 6.2.2 (Build 362) UUID : 2849ba3c-ecb8-11e6-98ca-b9fc2975893c Rules update version : 2017-03-15-001-vrt VDB version : 279 ---------------------------------------------------- ``` ### Products Confirmed Not Vulnerable No other Cisco products are currently known to be affected by this vulnerability. ### Workarounds There are no workarounds that address this vulnerability. ### Fixed Software Cisco has released free software updates that address the vulnerability described in this advisory. Customers may only install and expect support for software versions and feature sets for which they have purchased a license. By installing, downloading, accessing, or otherwise using such software upgrades, customers agree to follow the terms of the Cisco software license: http://www.cisco.com/en/US/docs/general/warranty/English/EU1KEN_.html Additionally, customers may only download software for which they have a valid license, procured from Cisco directly, or through a Cisco authorized reseller or partner. In most cases this will be a maintenance upgrade to software that was previously purchased. Free security software updates do not entitle customers to a new software license, additional software feature sets, or major revision upgrades. When considering software upgrades, customers are advised to regularly consult the advisories for Cisco products, which are available from the Cisco Security Advisories and Alerts page, to determine exposure and a complete upgrade solution. In all cases, customers should ensure that the devices to upgrade contain sufficient memory and confirm that current hardware and software configurations will continue to be supported properly by the new release. If the information is not clear, customers are advised to contact the Cisco Technical Assistance Center (TAC) or their contracted maintenance providers. ### Customers Without Service Contracts Customers who purchase directly from Cisco but do not hold a Cisco service contract and customers who make purchases through third-party vendors but are unsuccessful in obtaining fixed software through their point of sale should obtain upgrades by contacting the Cisco TAC: http://www.cisco.com/en/US/support/tsd_cisco_worldwide_contacts.html Customers should have the product serial number available and be prepared to provide the URL of this advisory as evidence of entitlement to a free upgrade. ### Fixed Releases In the following tables, the left column lists major releases of Cisco ASA Software. The right column indicates whether a major release is affected by the vulnerability described in this advisory and the first release that includes the fix for this vulnerability. Customers should upgrade to an appropriate release as indicated in this section. 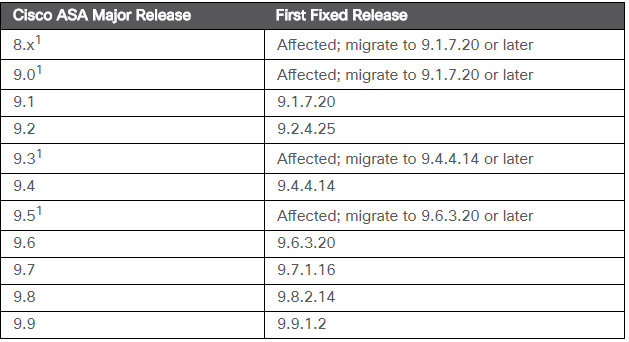 ASA Software releases prior to 9.1, including all 8.x releases, and ASA releases 9.3 and 9.5 have reached End of Software Maintenance. Customers should migrate to a supported release. ### FTD Software In the following table, the left column lists major releases of Cisco FTD Software. The right column indicates whether a major release is affected by the vulnerability described in this advisory and the first release that includes the fix for this vulnerability. Customers should upgrade to an appropriate release as indicated in this section. 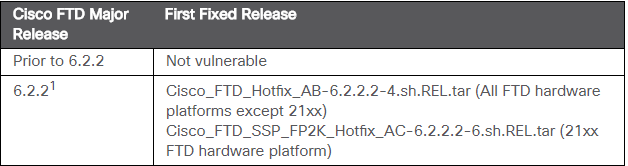 The Remote Access VPN feature was not supported on FTD until 6.2.2. Exploitation and Public Announcements The Cisco Product Security Incident Response Team (PSIRT) is aware of public knowledge of the vulnerability that is described in this advisory. Cisco PSIRT is not aware of any malicious use of the vulnerability described in this advisory. ### Source Cisco would like to thank Cedric Halbronn from the NCC Group for finding and reporting this vulnerability. ### IDS Signatures ``` # IDS signatures for https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180129-asa1: alert udp any any -> any 500 (msg:"FOX-SRT - Suspicious - Possible Fragmented Cisco IKE/isakmp Packet HeapSpray (CVE-2018-0101)"; flow:to_server; content:"|84|"; offset:16; depth:1; content:"|02 08 |"; distance:1; within:2; fast_pattern; byte_test:4,>,5000,4,relative; byte_test:2,>,5000,10,relative; byte_extract:4,36,fragment_match; byte_test:4,=,fragment_match,52,relative; byte_test:4,=,fragment_match,136,relative; byte_test:4,=,fragment_match,236,relative; threshold:type limit, track by_dst, count 1, seconds 600; classtype:attempted-admin; sid:21002339; rev:4;) alert udp any any -> any 500 (msg:"FOX-SRT - Exploit - Possible Shellcode in Cisco IKE/isakmp - tcp/CONNECT/"; content:"tcp/CONNECT/"; fast_pattern:only; threshold:type limit, track by_src, count 1, seconds 600; priority:1; classtype:attempted-admin; sid:21002340; rev:2;) ``` |
| id | SSV:97119 |
| last seen | 2018-02-07 |
| modified | 2018-01-31 |
| published | 2018-01-31 |
| reporter | Root |
| source | https://www.seebug.org/vuldb/ssvid-97119 |
| title | Cisco Adaptive Security Appliance Remote Code Execution and Denial of Service Vulnerability |
Related news
References
- https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180129-asa1
- http://www.securitytracker.com/id/1040292
- http://www.securityfocus.com/bid/102845
- https://icanthackit.wordpress.com/2018/01/30/thoughts-on-the-handling-cve-2018-0101-cisco-bug-cscvg35618/
- https://pastebin.com/YrBcG2Ln
- https://www.exploit-db.com/exploits/43986/